标签:
The scenario is about Business Secret and our client do worry about data leakage. They want to know whether Suspect copy those data to external hard drive or not. In fact it is not easy for Forensic guys to answer this question. Of course if you copy data from local drive to external drive and then access those files in external drive, there will be some LNK files created.
But if you only copy files and folders from local drive to external drive in Windows, you could not find any "Copy artifacts" in log files or registry...So how do we know if Suspect copy files and folders to external drive or not? As I know that the only way to do this is to monitor and record files and folders manipulation, and you could take a look at logs to see what‘s going on.
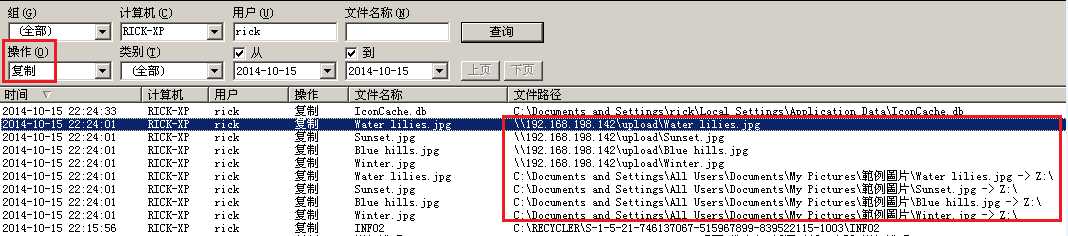
You could use commercial solutions like IP-Guard, etc.

It could also record copy operation to network drive.
There is a free solution called "Windows Explorer Tracker". As you could see that an external usb hard drive plug in at 15:31:15. Its driver letter was "G:" and the volume label was "HD-PNFU3". Then an Excel file "主要服務伺服器密碼一覽表.xls" created in "D:", and we could say that this file may come from "G:", the usb external hard drive. And then some files created in "D:\#1016" in a very short time, so we could say that those files also came from "G:". Let‘s see what happen to that xls file as below:
1. At 15:40:46 that xls file being renamed to "123.xls".
2. At 15:40:59 a LNK file pointed to 123.xls created in "Recent". That means Suspect double click on that xls file and took a look at its content.
3. At 15:45:58 Suspect deleted "123.xls" in "D:\".
By the way, there is a file called "top-secret" created in "G:\" at 15:45:08. That means this file may come from local drives and being copied to usb external hard drive "G:\".
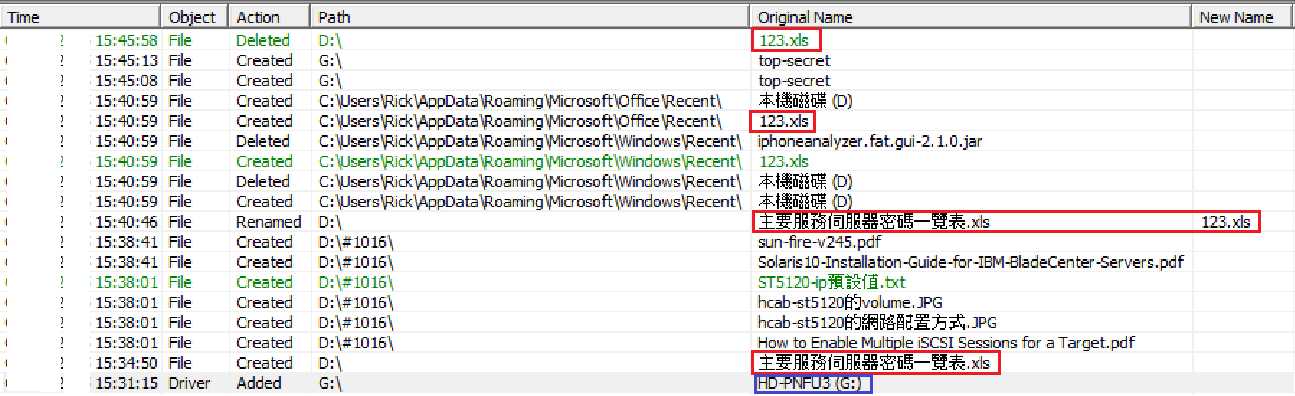
Now we just need to find out where that usb external hard drive is, and search for file "top-secret" and other files as above. Then we could know if Suspect did copy folders and files from local drives to external drives.
Track files and folders manipulation in Windows
标签:
原文地址:http://www.cnblogs.com/pieces0310/p/4925782.html