标签:
#1 纯属闲的没事干
#2 参考书籍<<程序员密码学>>
1 #coding:utf-8 2 __author__ = ‘Kerne0‘ 3 class AESE(): 4 def __init__(self,blk,key,Nr): 5 self.blk=blk 6 self.key=key 7 self.Nr=Nr 8 self.sbox=( 0x63,0x7c,0x77,0x7b,0xf2,0x6b,0x6f,0xc5,0x30,0x01,0x67,0x2b,0xfe,0xd7,0xab,0x76, 9 0xca,0x82,0xc9,0x7d,0xfa,0x59,0x47,0xf0,0xad,0xd4,0xa2,0xaf,0x9c,0xa4,0x72,0xc0, 10 0xb7,0xfd,0x93,0x26,0x36,0x3f,0xf7,0xcc,0x34,0xa5,0xe5,0xf1,0x71,0xd8,0x31,0x15, 11 0x04,0xc7,0x23,0xc3,0x18,0x96,0x05,0x9a,0x07,0x12,0x80,0xe2,0xeb,0x27,0xb2,0x75, 12 0x09,0x83,0x2c,0x1a,0x1b,0x6e,0x5a,0xa0,0x52,0x3b,0xd6,0xb3,0x29,0xe3,0x2f,0x84, 13 0x53,0xd1,0x00,0xed,0x20,0xfc,0xb1,0x5b,0x6a,0xcb,0xbe,0x39,0x4a,0x4c,0x58,0xcf, 14 0xd0,0xef,0xaa,0xfb,0x43,0x4d,0x33,0x85,0x45,0xf9,0x02,0x7f,0x50,0x3c,0x9f,0xa8, 15 0x51,0xa3,0x40,0x8f,0x92,0x9d,0x38,0xf5,0xbc,0xb6,0xda,0x21,0x10,0xff,0xf3,0xd2, 16 0xcd,0x0c,0x13,0xec,0x5f,0x97,0x44,0x17,0xc4,0xa7,0x7e,0x3d,0x64,0x5d,0x19,0x73, 17 0x60,0x81,0x4f,0xdc,0x22,0x2a,0x90,0x88,0x46,0xee,0xb8,0x14,0xde,0x5e,0x0b,0xdb, 18 0xe0,0x32,0x3a,0x0a,0x49,0x06,0x24,0x5c,0xc2,0xd3,0xac,0x62,0x91,0x95,0xe4,0x79, 19 0xe7,0xc8,0x37,0x6d,0x8d,0xd5,0x4e,0xa9,0x6c,0x56,0xf4,0xea,0x65,0x7a,0xae,0x08, 20 0xba,0x78,0x25,0x2e,0x1c,0xa6,0xb4,0xc6,0xe8,0xdd,0x74,0x1f,0x4b,0xbd,0x8b,0x8a, 21 0x70,0x3e,0xb5,0x66,0x48,0x03,0xf6,0x0e,0x61,0x35,0x57,0xb9,0x86,0xc1,0x1d,0x9e, 22 0xe1,0xf8,0x98,0x11,0x69,0xd9,0x8e,0x94,0x9b,0x1e,0x87,0xe9,0xce,0x55,0x28,0xdf, 23 0x8c,0xa1,0x89,0x0d,0xbf,0xe6,0x42,0x68,0x41,0x99,0x2d,0x0f,0xb0,0x54,0xbb,0x16 ) 24 #xtime process 25 def xtime(self,x): 26 if(x&0x80): 27 return (((x<<1)^0x1b)&0xff) 28 return x<<1 29 #MixColumns: Process the entire block 30 def MixColumns(self): 31 tmp=[0 for t in range(4)] 32 xt=[0 for q in range(4)] 33 n=0 34 for x in range(4): 35 xt[0]=self.xtime(self.blk[n]) 36 xt[1]=self.xtime(self.blk[n+1]) 37 xt[2]=self.xtime(self.blk[n+2]) 38 xt[3]=self.xtime(self.blk[n+3]) 39 tmp[0]=xt[0]^xt[1]^self.blk[n+1]^self.blk[n+2]^self.blk[n+3] 40 tmp[1]=self.blk[n]^xt[1]^xt[2]^self.blk[n+2]^self.blk[n+3] 41 tmp[2]=self.blk[n]^self.blk[n+1]^xt[2]^xt[3]^self.blk[n+3] 42 tmp[3]=xt[0]^self.blk[n]^self.blk[n+1]^self.blk[n+2]^xt[3] 43 self.blk[n]=tmp[0] 44 self.blk[n+1]=tmp[1] 45 self.blk[n+2]=tmp[2] 46 self.blk[n+3]=tmp[3] 47 n=n+4 48 #ShiftRows:Shifts the entire block 49 def ShiftRows(self): 50 #2nd row 51 t=self.blk[1] 52 self.blk[1]=self.blk[5] 53 self.blk[5]=self.blk[9] 54 self.blk[9]=self.blk[13] 55 self.blk[13]=t 56 #3nd row 57 t=self.blk[2] 58 self.blk[2]=self.blk[10] 59 self.blk[10]=t 60 t=self.blk[6] 61 self.blk[6]=self.blk[14] 62 self.blk[14]=t 63 #4nd row 64 t=self.blk[15] 65 self.blk[15]=self.blk[11] 66 self.blk[11]=self.blk[7] 67 self.blk[7]=self.blk[3] 68 self.blk[3]=t 69 #SubBytes 70 def SubBytes(self): 71 for x in range(16): 72 self.blk[x]=self.sbox[self.blk[x]] 73 #AddRoundKey 74 def AddRoundKey(self,key): 75 x=0 76 k=[0 for m in range(16)] 77 for c in range(4): 78 for r in range(4): 79 k[x]=key[r][c] 80 x=x+1 81 for y in range(16): 82 self.blk[y]^=int(k[y]) 83 84 def show(self): 85 for i in range(16): 86 print hex(self.blk[i]) 87 # Schedule a secret key for use. 88 def ScheduleKey(self,w,Nk): 89 Rcon=[0x01,0x02,0x04,0x08,0x10,0x20,0x40,0x80,0x1b,0x36] 90 for r in range(4): 91 for c in range(4): 92 w[0][r][c]=self.key[r+c*4] 93 for i in range(1,self.Nr+1,1):#问题1 94 for j in range(Nk): 95 t=[0 for x in range(4)] 96 for r in range(4): 97 if j : 98 t[r]=w[i][r][j-1] 99 else: 100 t[r]=w[i-1][r][3] 101 if j==0: 102 temp=t[0] 103 for r in range(3): 104 t[r]=self.sbox[t[(r+1)%4]] 105 t[3]=self.sbox[temp] 106 t[0]^=int(Rcon[i-1]) 107 for r in range(4): 108 w[i][r][j]=w[i-1][r][j]^t[r] 109 110 #加密函数 111 def AesEncrypt(self): 112 outkey=[] 113 outkey=[[[0 for col in range(4)] for row in range(4)] for s in range(11)] 114 self.ScheduleKey(outkey,4) 115 self.AddRoundKey(outkey[0]) 116 for x in range(1,self.Nr,1): 117 self.SubBytes() 118 self.ShiftRows() 119 self.MixColumns() 120 self.AddRoundKey(outkey[x]) 121 self.SubBytes() 122 self.ShiftRows() 123 self.AddRoundKey(outkey[10]) 124 print "密文的16进制:" 125 cText="" 126 for i in range(16): 127 xxl=hex(self.blk[i]) 128 cText+=xxl[2:] 129 print cText 130 return blk 131 132 class AESD(): 133 def __init__(self,blk,key,Nr): 134 self.blk=blk 135 self.key=key 136 self.Nr=Nr 137 self.sbox=( 0x63,0x7c,0x77,0x7b,0xf2,0x6b,0x6f,0xc5,0x30,0x01,0x67,0x2b,0xfe,0xd7,0xab,0x76, 138 0xca,0x82,0xc9,0x7d,0xfa,0x59,0x47,0xf0,0xad,0xd4,0xa2,0xaf,0x9c,0xa4,0x72,0xc0, 139 0xb7,0xfd,0x93,0x26,0x36,0x3f,0xf7,0xcc,0x34,0xa5,0xe5,0xf1,0x71,0xd8,0x31,0x15, 140 0x04,0xc7,0x23,0xc3,0x18,0x96,0x05,0x9a,0x07,0x12,0x80,0xe2,0xeb,0x27,0xb2,0x75, 141 0x09,0x83,0x2c,0x1a,0x1b,0x6e,0x5a,0xa0,0x52,0x3b,0xd6,0xb3,0x29,0xe3,0x2f,0x84, 142 0x53,0xd1,0x00,0xed,0x20,0xfc,0xb1,0x5b,0x6a,0xcb,0xbe,0x39,0x4a,0x4c,0x58,0xcf, 143 0xd0,0xef,0xaa,0xfb,0x43,0x4d,0x33,0x85,0x45,0xf9,0x02,0x7f,0x50,0x3c,0x9f,0xa8, 144 0x51,0xa3,0x40,0x8f,0x92,0x9d,0x38,0xf5,0xbc,0xb6,0xda,0x21,0x10,0xff,0xf3,0xd2, 145 0xcd,0x0c,0x13,0xec,0x5f,0x97,0x44,0x17,0xc4,0xa7,0x7e,0x3d,0x64,0x5d,0x19,0x73, 146 0x60,0x81,0x4f,0xdc,0x22,0x2a,0x90,0x88,0x46,0xee,0xb8,0x14,0xde,0x5e,0x0b,0xdb, 147 0xe0,0x32,0x3a,0x0a,0x49,0x06,0x24,0x5c,0xc2,0xd3,0xac,0x62,0x91,0x95,0xe4,0x79, 148 0xe7,0xc8,0x37,0x6d,0x8d,0xd5,0x4e,0xa9,0x6c,0x56,0xf4,0xea,0x65,0x7a,0xae,0x08, 149 0xba,0x78,0x25,0x2e,0x1c,0xa6,0xb4,0xc6,0xe8,0xdd,0x74,0x1f,0x4b,0xbd,0x8b,0x8a, 150 0x70,0x3e,0xb5,0x66,0x48,0x03,0xf6,0x0e,0x61,0x35,0x57,0xb9,0x86,0xc1,0x1d,0x9e, 151 0xe1,0xf8,0x98,0x11,0x69,0xd9,0x8e,0x94,0x9b,0x1e,0x87,0xe9,0xce,0x55,0x28,0xdf, 152 0x8c,0xa1,0x89,0x0d,0xbf,0xe6,0x42,0x68,0x41,0x99,0x2d,0x0f,0xb0,0x54,0xbb,0x16 ) 153 154 def xtime(self,x): 155 if(x&0x80): 156 return (((x<<1)^0x1b)&0xff) 157 return x<<1 158 159 def ReMixColumns(self): 160 tmp=[0 for q in range(4)] 161 xt1=[0 for w in range(4)] 162 xt2=[0 for e in range(4)] 163 xt3=[0 for r in range(4)] 164 n=0 165 for x in range(4): 166 xt1[0]=self.xtime(self.blk[n]) 167 xt1[1]=self.xtime(self.blk[n+1]) 168 xt1[2]=self.xtime(self.blk[n+2]) 169 xt1[3]=self.xtime(self.blk[n+3]) 170 xt2[0]=self.xtime(self.xtime(self.blk[n])) 171 xt2[1]=self.xtime(self.xtime(self.blk[n+1])) 172 xt2[2]=self.xtime(self.xtime(self.blk[n+2])) 173 xt2[3]=self.xtime(self.xtime(self.blk[n+3])) 174 xt3[0]=self.xtime(self.xtime(self.xtime(self.blk[n]))) 175 xt3[1]=self.xtime(self.xtime(self.xtime(self.blk[n+1]))) 176 xt3[2]=self.xtime(self.xtime(self.xtime(self.blk[n+2]))) 177 xt3[3]=self.xtime(self.xtime(self.xtime(self.blk[n+3]))) 178 tmp[0]=xt1[0]^xt2[0]^xt3[0]^ self.blk[n+1]^xt1[1]^xt3[1]^ self.blk[n+2]^xt2[2]^xt3[2]^self.blk[n+3]^xt3[3] 179 tmp[1]=self. blk[n]^xt3[0]^xt1[1]^xt2[1]^xt3[1]^ self.blk[n+2]^xt1[2]^xt3[2]^ self.blk[n+3]^xt2[3]^xt3[3] 180 tmp[2]= self.blk[n]^xt2[0]^xt3[0]^ self.blk[n+1]^xt3[1]^xt1[2]^xt2[2]^xt3[2]^ self.blk[n+3]^xt1[3]^xt3[3] 181 tmp[3]=self. blk[n]^xt1[0]^xt3[0]^self. blk[n+1]^xt2[1]^xt3[1]^ self.blk[n+2]^xt3[2]^xt1[3]^xt2[3]^xt3[3] 182 self.blk[n]=tmp[0] 183 self.blk[n+1]=tmp[1] 184 self.blk[n+2]=tmp[2] 185 self.blk[n+3]=tmp[3] 186 n=n+4 187 188 def ReShiftRows(self): 189 #2nd row 190 t=self.blk[13] 191 self.blk[13]=self.blk[9] 192 self.blk[9]=self.blk[5] 193 self.blk[5]=self.blk[1] 194 self.blk[1]=t 195 #3rd row 196 t=self.blk[2] 197 self.blk[2]=self.blk[10] 198 self.blk[10]=t 199 t=self.blk[6] 200 self.blk[6]=self.blk[14] 201 self.blk[14]=t 202 #4th row 203 t=self.blk[3] 204 self.blk[3]=self.blk[7] 205 self.blk[7]=self.blk[11] 206 self.blk[11]=self.blk[15] 207 self.blk[15]=t 208 209 def ReSubBytes(self): 210 for i in range(16): 211 for j in range(256): 212 if(self.sbox[j]==self.blk[i]): 213 self.blk[i]=j 214 break 215 216 def AddRoundKey(self,key): 217 x=0 218 k=[0 for m in range(16)] 219 for c in range(4): 220 for r in range(4): 221 k[x]=key[r][c] 222 x=x+1 223 for y in range(16): 224 self.blk[y]^=k[y] 225 226 def ScheduleKey(self,w,Nk): 227 Rcon=[0x01,0x02,0x04,0x08,0x10,0x20,0x40,0x80,0x1b,0x36] 228 for r in range(4): 229 for c in range(4): 230 w[0][r][c]=self.key[r+c*4] 231 for i in range(1,self.Nr+1,1): 232 for j in range(Nk): 233 t=[0 for x in range(4)] 234 for r in range(4): 235 if j : 236 t[r]=w[i][r][j-1] 237 else: 238 t[r]=w[i-1][r][3] 239 if j==0: 240 temp=t[0] 241 for r in range(3): 242 t[r]=self.sbox[t[(r+1)%4]] 243 t[3]=self.sbox[temp] 244 t[0]^=int(Rcon[i-1]) 245 for r in range(4): 246 w[i][r][j]=w[i-1][r][j]^t[r] 247 248 def AesDecrpyt(self): 249 outkey=[] 250 outkey=[[[0 for col in range(4)] for row in range(4)] for s in range(11)]#改 251 self.ScheduleKey(outkey,4) 252 self.AddRoundKey(outkey[10]) 253 self.ReShiftRows() 254 self.ReSubBytes() 255 for x in range(self.Nr-1,0,-1): 256 self.AddRoundKey(outkey[x]) 257 self.ReMixColumns()#第二次循环出问题了 258 self.ReShiftRows() 259 self.ReSubBytes() 260 self.AddRoundKey(outkey[0]) 261 print "解密结果:" 262 mText="" 263 for x in range(16): 264 mText+=chr(self.blk[x]) 265 print mText 266 def StringToListN(string): 267 s=[0 for x in range(16)] 268 l=len(string) 269 for x in range(l): 270 s[x]=int(ord(string[x])) 271 return s 272 273 if __name__=="__main__": 274 #加密 275 plainText=raw_input("请输入待加密的字符串:") 276 blk=StringToListN(plainText) 277 skey=raw_input("请输入待加密的秘钥:") 278 key=StringToListN(skey) 279 a=AESE(blk,key,10) 280 rblk=a.AesEncrypt() 281 #解密 282 b=AESD(rblk,key,10) 283 b.AesDecrpyt()
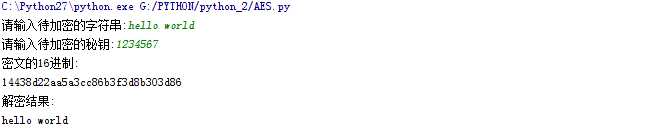
运行结果截图:
标签:
原文地址:http://www.cnblogs.com/Kerne0/p/5067878.html