标签:项目 rect 设置权限 管理 ast mission net bug icon
1. 系统具有角色概念, 部门概念, 且都具有相应不同的权限
2. 用户具有多个角色, 多个部门等关系, 并且能给单个用户指派独有的权限
3. 具有细粒度权限控制到资源的RBAC, 能控制页面, 控制菜单, 控制逻辑, 控制单个操作, 控制到单一数据; 且具有一定的可扩展性
4. 适用于webapi/ mvc / wcf / webservice 混合项目中
5. 设置权限和验证权限易用性高
1. 角色表
2. 部门表
3. 用户表
4. 菜单表
5. 用户表
6. 权限表
7. 用户角色关系表
8. 用户部门关系表
9. 菜单权限关系表
10.用户权限关系表
11.部门权限关系表
12. 权限汇总表
在一般正常的情况下, 大家伙都会有 菜单权限关系, 用户权限关系, 部门权限关系等表, 在此处省去如上几项权限关系表, 将如上权限表做成dll 当插件形式容入到项目中.
权限汇总表描述:
既然将如上所有跟权限有关联的关系表剔除后该如何来设计各种来自不同体系的权限呢? 因此在此权限汇总表中要有字段来定位到, 该条权限是属于什么体系.
因此权限汇总表中出现三个至关重要的字段:
1. PermissionType(权限的类型: 菜单,部门,角色,用户 );
2. PermissionReferenceId(权限类型的引用ID: 当Type为角色时 为角色的ID 以此类推);
3. PermissionAction(权限操作的ID: 每个权限将会划分为一个操作编号ID, 往后会深入讲解)

1 -- 权限汇总表
2 CREATE TABLE `Permission` (
3 `Id` int(11) NOT NULL AUTO_INCREMENT,
4 `PermissionReferenceId` int(11) DEFAULT NULL COMMENT ‘权限引用ID(对应 角色ID, 用户ID, 部门ID)‘,
5 `PermissionAction` int(11) DEFAULT NULL COMMENT ‘权限操作ID(每种资源的操作ID)‘,
6 `PermissionType` int(11) DEFAULT NULL COMMENT ‘权限类型()‘,
7 `CreateTime` datetime DEFAULT ‘1990-01-01 00:00:00‘ COMMENT ‘创建时间‘,
8 `UpdateTime` datetime DEFAULT ‘1990-01-01 00:00:00‘ COMMENT ‘修改时间‘,
9 `IsEnable` bit(1) DEFAULT b‘1‘ COMMENT ‘是否可用‘,
10 PRIMARY KEY (`Id`)
11 ) ENGINE=InnoDB AUTO_INCREMENT=390 DEFAULT CHARSET=utf8 COMMENT=‘权限汇总表‘;

1 -- 部门表
2 CREATE TABLE `AdminMent` (
3 `Id` int(11) NOT NULL AUTO_INCREMENT,
4 `DepartName` varchar(20) DEFAULT NULL COMMENT ‘部门名‘,
5 `Description` varchar(20) DEFAULT NULL COMMENT ‘部门说明‘,
6 `Icon` varchar(20) DEFAULT NULL COMMENT ‘图标‘,
7 `CreateTime` datetime DEFAULT NULL COMMENT ‘创建时间‘,
8 `UpdateTime` datetime DEFAULT NULL COMMENT ‘修改时间‘,
9 `IsEnable` bit(1) DEFAULT b‘1‘ COMMENT ‘是否可用‘,
10 PRIMARY KEY (`Id`)
11 ) ENGINE=InnoDB AUTO_INCREMENT=2 DEFAULT CHARSET=utf8 COMMENT=‘部门表‘;
12
13
14 -- 部门用户关系表
15 CREATE TABLE `AdminMentAdminUsers` (
16 `AdminMent_Id` int(11) NOT NULL,
17 `AdminUser_Id` int(11) NOT NULL,
18 PRIMARY KEY (`AdminMent_Id`,`AdminUser_Id`),
19 KEY `AdminMent_UserCollection_Target` (`AdminUser_Id`)
20 ) ENGINE=MyISAM DEFAULT CHARSET=gbk;
21
22
23 -- 角色表
24 CREATE TABLE `AdminRole` (
25 `Id` int(11) NOT NULL AUTO_INCREMENT,
26 `RoleName` varchar(20) DEFAULT NULL COMMENT ‘角色名‘,
27 `Description` varchar(20) DEFAULT NULL COMMENT ‘角色说明‘,
28 `CreateTime` datetime DEFAULT NULL COMMENT ‘创建时间‘,
29 `UpdateTime` datetime DEFAULT NULL COMMENT ‘修改时间‘,
30 `IsEnable` bit(1) DEFAULT b‘1‘ COMMENT ‘是否可用‘,
31 PRIMARY KEY (`Id`)
32 ) ENGINE=InnoDB AUTO_INCREMENT=4 DEFAULT CHARSET=utf8 COMMENT=‘后台角色表‘;
33
34
35 -- 角色用户关系表
36 CREATE TABLE `AdminRoleAdminUsers` (
37 `AdminRole_Id` int(11) NOT NULL,
38 `AdminUser_Id` int(11) NOT NULL,
39 PRIMARY KEY (`AdminRole_Id`,`AdminUser_Id`),
40 KEY `AdminRole_UserCollection_Target` (`AdminUser_Id`)
41 ) ENGINE=MyISAM DEFAULT CHARSET=gbk;
42
43
44 -- 用户表
45 CREATE TABLE `AdminUser` (
46 `Id` int(11) NOT NULL AUTO_INCREMENT,
47 `UserName` varchar(20) DEFAULT NULL COMMENT ‘后台用户名‘,
48 `Password` varchar(50) DEFAULT NULL COMMENT ‘后台用户密码‘,
49 `Mail` varchar(50) DEFAULT NULL COMMENT ‘用户邮箱‘,
50 `Phone` varchar(20) DEFAULT NULL COMMENT ‘用户手机‘,
51 `Description` varchar(20) DEFAULT NULL COMMENT ‘附加说明‘,
52 `CreateTime` datetime DEFAULT NULL COMMENT ‘创建时间‘,
53 `UpdateTime` datetime DEFAULT NULL COMMENT ‘修改时间‘,
54 `IsEnable` bit(1) DEFAULT b‘1‘ COMMENT ‘是否可用‘,
55 PRIMARY KEY (`Id`)
56 ) ENGINE=InnoDB AUTO_INCREMENT=3 DEFAULT CHARSET=utf8 COMMENT=‘后台用户表‘;
57
58 -- 菜单表
59 CREATE TABLE `AdminMenu` (
60 `Id` int(11) NOT NULL AUTO_INCREMENT,
61 `ParentsID` int(11) DEFAULT NULL COMMENT ‘父菜单ID‘,
62 `MenuName` varchar(20) DEFAULT NULL COMMENT ‘菜单名称‘,
63 `Descriptotion` varchar(20) DEFAULT NULL COMMENT ‘菜单说明‘,
64 `ControllerPermissionName` varchar(20) DEFAULT NULL COMMENT ‘控制器名‘,
65 `ActionPermissionName` varchar(20) DEFAULT NULL COMMENT ‘操作器名‘,
66 `Sort` int(11) DEFAULT NULL COMMENT ‘排序‘,
67 `Icon` varchar(20) DEFAULT NULL COMMENT ‘图标‘,
68 `CreateTime` datetime DEFAULT NULL COMMENT ‘创建时间‘,
69 `UpdateTime` datetime DEFAULT NULL COMMENT ‘修改时间‘,
70 `IsEnable` bit(1) DEFAULT b‘1‘ COMMENT ‘是否可用‘,
71 PRIMARY KEY (`Id`)
72 ) ENGINE=InnoDB AUTO_INCREMENT=32 DEFAULT CHARSET=utf8 COMMENT=‘后台管理菜单表‘;
若要让设置权限和验证权限易用性高, 最好的解决方案则是利用 Attribute 来进行权限的设置.
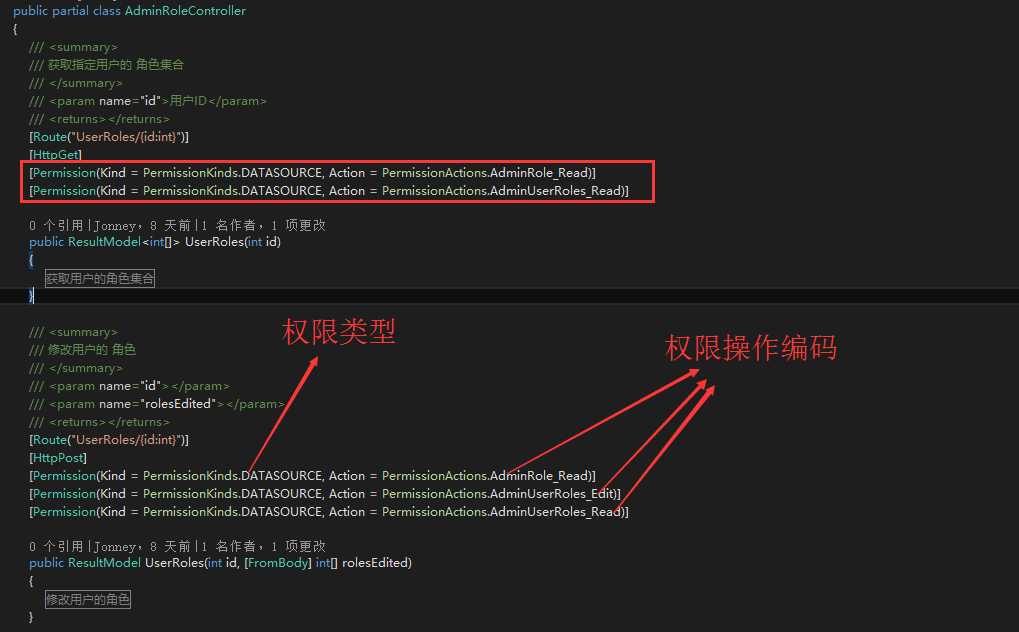
如图:

1 /// <summary> 2 /// 附加权限 3 /// </summary> 4 [AttributeUsage(validOn: AttributeTargets.Class | AttributeTargets.Method, AllowMultiple = true, Inherited = true)] 5 public class PermissionAttribute : Attribute 6 { 7 /// <summary> 8 /// 权限类型 9 /// </summary> 10 public PermissionKinds Kind { get; set; } = PermissionKinds.AllowAnonymous; 11 /// <summary> 12 /// 操作权限 13 /// </summary> 14 public PermissionActions Action { get; set; } = PermissionActions.AllowAnonymous; 15 }
将PermissionKinds 划分为 菜单 和 数据

1 /// <summary> 2 /// 用于标识api接口和mvc访问权限验证类型 3 /// </summary> 4 public enum PermissionKinds : int 5 { 6 /// <summary> 7 /// 匿名 8 /// </summary> 9 AllowAnonymous = 0, 10 /// <summary> 11 /// 菜单 12 /// </summary> 13 MENU = 1, 14 /// <summary> 15 /// 资源操作 16 /// </summary> 17 DATASOURCE = 2 18 }
PermissionActions 则是 标识操作资源的权限编号
例: 用户表: User_Read = 10, User_Edit=11, User_Add=12, User_Delete=13 (当然此处也可以进行扩展如: 搜索用户 User_Search=14)

1 /// <summary> 2 /// 用于标识操作资源的权限动作类型 3 /// </summary> 4 [JsonConverter(typeof(int))] 5 public enum PermissionActions : int 6 { 7 /// <summary> 8 /// 匿名 9 /// </summary> 10 AllowAnonymous = 0, 11 12 13 #region 表:ActionPermission(控制器操作权限表) 权限 14 /// <summary> 15 /// 控制器操作权限表读取权限 16 /// </summary> 17 [PermissionActionDescription("控制器操作权限表", "读取")] 18 ActionPermission_Read = 10, 19 /// <summary> 20 /// 控制器操作权限表修改权限 21 /// </summary> 22 [PermissionActionDescription("控制器操作权限表", "修改")] 23 ActionPermission_Edit = 11, 24 /// <summary> 25 /// 控制器操作权限表添加权限 26 /// </summary> 27 [PermissionActionDescription("控制器操作权限表", "添加")] 28 ActionPermission_Add = 12, 29 /// <summary> 30 /// 控制器操作权限表删除权限 31 /// </summary> 32 [PermissionActionDescription("控制器操作权限表", "删除")] 33 ActionPermission_Delete = 13, 34 #endregion 35 36 #region 表:AdminMent(部门表) 权限 37 /// <summary> 38 /// 部门表读取权限 39 /// </summary> 40 [PermissionActionDescription("部门表", "读取")] 41 AdminMent_Read = 20, 42 /// <summary> 43 /// 部门表修改权限 44 /// </summary> 45 [PermissionActionDescription("部门表", "修改")] 46 AdminMent_Edit = 21, 47 /// <summary> 48 /// 部门表添加权限 49 /// </summary> 50 [PermissionActionDescription("部门表", "添加")] 51 AdminMent_Add = 22, 52 /// <summary> 53 /// 部门表删除权限 54 /// </summary> 55 [PermissionActionDescription("部门表", "删除")] 56 AdminMent_Delete = 23, 57 #endregion 58 59 #region 表:AdminMenu(后台管理菜单表) 权限 60 /// <summary> 61 /// 后台管理菜单表读取权限 62 /// </summary> 63 [PermissionActionDescription("后台管理菜单表", "读取")] 64 AdminMenu_Read = 30, 65 /// <summary> 66 /// 后台管理菜单表修改权限 67 /// </summary> 68 [PermissionActionDescription("后台管理菜单表", "修改")] 69 AdminMenu_Edit = 31, 70 /// <summary> 71 /// 后台管理菜单表添加权限 72 /// </summary> 73 [PermissionActionDescription("后台管理菜单表", "添加")] 74 AdminMenu_Add = 32, 75 /// <summary> 76 /// 后台管理菜单表删除权限 77 /// </summary> 78 [PermissionActionDescription("后台管理菜单表", "删除")] 79 AdminMenu_Delete = 33, 80 #endregion 81 82 #region 表:AdminRole(后台角色表) 权限 83 /// <summary> 84 /// 后台角色表读取权限 85 /// </summary> 86 [PermissionActionDescription("后台角色表", "读取")] 87 AdminRole_Read = 40, 88 /// <summary> 89 /// 后台角色表修改权限 90 /// </summary> 91 [PermissionActionDescription("后台角色表", "修改")] 92 AdminRole_Edit = 41, 93 /// <summary> 94 /// 后台角色表添加权限 95 /// </summary> 96 [PermissionActionDescription("后台角色表", "添加")] 97 AdminRole_Add = 42, 98 /// <summary> 99 /// 后台角色表删除权限 100 /// </summary> 101 [PermissionActionDescription("后台角色表", "删除")] 102 AdminRole_Delete = 43, 103 #endregion 104 105 #region 表:AdminUser(后台用户表) 权限 106 /// <summary> 107 /// 后台用户表读取权限 108 /// </summary> 109 [PermissionActionDescription("后台用户表", "读取")] 110 AdminUser_Read = 50, 111 /// <summary> 112 /// 后台用户表修改权限 113 /// </summary> 114 [PermissionActionDescription("后台用户表", "修改")] 115 AdminUser_Edit = 51, 116 /// <summary> 117 /// 后台用户表添加权限 118 /// </summary> 119 [PermissionActionDescription("后台用户表", "添加")] 120 AdminUser_Add = 52, 121 /// <summary> 122 /// 后台用户表删除权限 123 /// </summary> 124 [PermissionActionDescription("后台用户表", "删除")] 125 AdminUser_Delete = 53, 126 #endregion 127 128 #region 表:AdminUserRoles(后台用户角色表) 权限 129 /// <summary> 130 /// 后台用户角色表读取权限 131 /// </summary> 132 [PermissionActionDescription("后台用户角色表", "读取")] 133 AdminUserRoles_Read = 60, 134 /// <summary> 135 /// 后台用户角色表修改权限 136 /// </summary> 137 [PermissionActionDescription("后台用户角色表", "修改")] 138 AdminUserRoles_Edit = 61, 139 /// <summary> 140 /// 后台用户角色表添加权限 141 /// </summary> 142 [PermissionActionDescription("后台用户角色表", "添加")] 143 AdminUserRoles_Add = 62, 144 /// <summary> 145 /// 后台用户角色表删除权限 146 /// </summary> 147 [PermissionActionDescription("后台用户角色表", "删除")] 148 AdminUserRoles_Delete = 63, 149 #endregion 150 }
至此,我们只需要要将要 进行权限审核验证的方法上进行 permissionattribute 标记即可
附上相应的codesmith 代码生成

1 <%@ CodeTemplate Language="C#" TargetLanguage="C#" Src="" Inherits="" Debug="False" Description="Template description here." ResponseEncoding="UTF-8" %> 2 <%@ Property Name="SourceDatabase" Type="SchemaExplorer.DatabaseSchema" Default="" Description="源数据库" %> 3 <%@ Assembly Name="SchemaExplorer" %> 4 <%@ Assembly Name="System.Data" %> 5 <%@ Assembly Name="mscorlib" %> 6 <%@ Import Namespace="SchemaExplorer" %> 7 <%@ Import Namespace="System.Data" %> 8 <%@ Import Namespace="System.Collections.Generic" %> 9 10 <%@ Assembly Src="..\CommonUtility.cs" %> 11 <%@ Import Namespace="Common" %> 12 13 public enum PermissionActions : int 14 { 15 /// <summary> 16 /// 匿名 17 /// </summary> 18 AllowAnonymous = 0, 19 20 <% 21 int index = 0; 22 foreach(var table in SourceDatabase.Tables){ 23 var tableName = table.GetClassName(); 24 var tableDescription = table.Description; 25 index +=10; 26 var count = index; 27 %> 28 #region 表:<%=tableName %>(<%=tableDescription%>) 权限 29 /// <summary> 30 /// <%=tableDescription%>读取权限 31 /// </summary> 32 [PermissionActionDescription("<%=tableDescription%>","读取")] 33 <%=tableName %>_Read = <%=count++%>, 34 /// <summary> 35 /// <%=tableDescription%>修改权限 36 /// </summary> 37 [PermissionActionDescription("<%=tableDescription%>","修改")] 38 <%=tableName %>_Edit = <%=count++%>, 39 /// <summary> 40 /// <%=tableDescription%>添加权限 41 /// </summary> 42 [PermissionActionDescription("<%=tableDescription%>","添加")] 43 <%=tableName %>_Add = <%=count++%>, 44 /// <summary> 45 /// <%=tableDescription%>删除权限 46 /// </summary> 47 [PermissionActionDescription("<%=tableDescription%>","删除")] 48 <%=tableName %>_Delete = <%=count++%>, 49 #endregion 50 51 <% 52 } 53 %> 54 }
1. 在用户登录时,将用户所在的所有角色组权限, 和部门权限全部查询出来合并,并添加到缓存中.
2. 当用户在访问指定的资源或action方法前 进行验证其是否具有相应权限
实施方案:
1.webapi
新建 Filter 实现 IAuthorizationFilter 接口

1 public Task<HttpResponseMessage> ExecuteAuthorizationFilterAsync(HttpActionContext actionContext, CancellationToken cancellationToken, Func<Task<HttpResponseMessage>> continuation) 2 { 3 var permissions_on_action = actionContext.ActionDescriptor.GetCustomAttributes<PermissionAttribute>().ToList(); 4 5 bool isAnonymous = actionContext.ActionDescriptor.GetCustomAttributes<AllowAnonymousAttribute>().Count() > 0 6 || permissions_on_action.Any(a => a.Action == PermissionActions.AllowAnonymous) 7 ; 8 9 if (isAnonymous) 10 return continuation.Invoke(); 11 else 12 { 13 //该 操作所需要的所有权限 14 var action_needs_permissions = permissions_on_action.Select(s => s.Action).ToArray(); 15 if (action_needs_permissions.All(a => session.PermissionsArray.Contains(a))) 16 { 17 isAuthor = true; 18 } 19 else if (action_needs_permissions.Count() == 0) 20 { 21 isAuthor = true; 22 } 23 24 25 if (!isAuthor) 26 { 27 var result = new ResultModel(Code.Unauthorized, "没有足够的权限操作资源"); 28 actionContext.Response = new HttpResponseMessage(System.Net.HttpStatusCode.OK) { Content = new StringContent(result.ToJson()) }; 29 } 30 //如果已经登录,则跳过验证 31 return continuation.Invoke(); 32 } 33 }
2. mvc
新建Filter 实现 IAuthorizationFilter 接口

1 public void OnAuthorization(AuthorizationContext filterContext) 2 { 3 //throw new NotImplementedException(); 4 if (filterContext.ActionDescriptor.GetCustomAttributes(typeof(AllowAnonymousAttribute), true).Any()) return; 5 6 var token = HttpContext.Current.Request.Cookies["token_manager"]?.Value; 7 8 ActionNeedsPermissions = filterContext.ActionDescriptor.GetCustomAttributes(typeof(PermissionAttribute), false).Cast<PermissionAttribute>().ToList(); 9 10 if (!token.IsNullOrEmpty()) 11 { 12 var user_session = Redis.FindStore<SysUserSession>(token); 13 if (user_session == null) 14 { 15 if (ActionNeedsPermissions.Any(a => a.Kind == PermissionKinds.MENU && a.Action == PermissionActions.AllowAnonymous)) return; 16 } 17 else 18 { 19 if (ActionNeedsPermissions.Count == 0) return; 20 var action_permissions = ActionNeedsPermissions.Select(s => s.Action).ToList(); 21 if (user_session.PermissionsArray.Intersect(action_permissions).Count() == action_permissions.Count) return; 22 if (ActionNeedsPermissions.Any(a => a.Action == PermissionActions.AllowAnonymous)) return; 23 } 24 } 25 filterContext.Result = new RedirectResult("/Main/Login"); 26 }
.NET 通用高扩展性的细粒度权限管理架构(webApi/Mvc)
标签:项目 rect 设置权限 管理 ast mission net bug icon
原文地址:http://www.cnblogs.com/jonneydong/p/6336889.html