标签:des style blog http color io os ar strong
A network authentication method is to be implemented using a network authentication device and a user end for authenticating the user end. The network authentication method includes the steps of: configuring the network authentication device to store hardware information associated with unique identification codes of hardware components of the user end; when it is intended to verify identity of the user end, configuring the user end to execute a terminal program stored therein for scanning the hardware components thereof to obtain the identification codes of the hardware components, for establishing a hardware list according to the identification codes thus obtained, and for sending to the network authentication device verification data that is associated with the hardware list; and configuring the network authentication device to verify identity of the user end based on relationship between the verification data received from the user end and the hardware information stored therein.
The present invention relates to a network authentication method and device, more particularly to a network authentication method and device adapted for authenticating a user end using software.
Currently, when a user wants to transfer money at a web bank provided by a banking institution, the user needs to input a unique user identification code (user ID) and a password to access the web bank. The user ID can be obtained using a card reader reading an integrated circuit card issued by the banking institution, or can be a preset code set by the user and certified by the banking institution. After accessing the web bank, the user needs to fill an electronic transfer sheet and to input a transfer password so as to complete the transfer.
Since the user ID, the password and the transfer password may be stolen, a token or an integrated circuit card is used to provide a one-time password (OTP) to be sent to a network server of the web bank for verifying the identity of the user. Further, a token or card reader including its own screen and keys, or a flash drive having public key infrastructure certificate can be used to prevent the user ID and the password from being stolen.
However, due to the variety of web transactions, increasing numbers of web users and web crimes, and continuously progress of criminal techniques, the current verification methods have the following drawbacks.
A network content provider needs to purchase an identity verification device for each user, and the cost of customer service for personalization, distribution and troubleshooting is considerable. Further, it is quite inconvenient to the user that the user needs to have different identity verification devices for different web sites. Moreover, aside from intercepting and stealing the user ID, the password and the transfer password, the hackers also try to manipulate transaction data. Therefore, the network content provider is often forced to change hardware equipments, and the cost for changing the hardware equipments is considerable.
Therefore, an object of the present invention is to provide a network authentication method and device for authenticating a user end using software.
Accordingly, a network authentication method of the present invention is to be implemented using a network authentication device and a user end for authenticating the user end. The user end stores a terminal program and includes a plurality of hardware components each of which has a unique identification code.
The network authentication method comprises the steps of:
a) configuring the network authentication device to store hardware information associated with the identification codes of the hardware components of the user end;
b) when it is intended to verify identity of the user end, configuring the user end to execute the terminal program for scanning the hardware components thereof to obtain the identification codes of the hardware components of the user end, for establishing a hardware list according to the identification codes of the hardware components thus obtained, and for sending to the network authentication device verification data that is associated with the hardware list; and
c) configuring the network authentication device to verify identity of the user end based on relationship between the verification data received from the user end in step b) and the hardware information stored in step a).
Preferably, the network authentication method is to be implemented further using a network server, and step b) includes the sub-steps of:
b1) in response to a login request from the user end for accessing the network server through a first communication channel, configuring the network server to redirect the user end for connecting with the network authentication device through a second communication channel; and
b2) configuring the network authentication device to enable the user end to execute the terminal program.
Preferably, the network authentication method further comprises the steps of:
d) configuring the network authentication device to generate a key according to the hardware information stored therein, and to send the key to the user end and the network server;
e) when the user end intends to conduct an electronic transaction with the network server, configuring the user end to generate a first digital signature corresponding to transaction data of the electronic transaction using the key sent by the network authentication device and to send the transaction data and the first digital signature to the network server, and configuring the network server to generate a second digital signature corresponding to the transaction data received from the user end using the key sent by the network authentication device; and
f) configuring the network server to compare the first digital signature from the user end with the second digital signature generated thereby, and to determine that the transaction data was not tampered during transmission from the user end to the network server when the first digital signature conforms with the second digital signature.
According to another aspect of this invention, a network authentication device is used for authenticating a user end. The user end includes a plurality of hardware components each of which has a unique identification code, and is configured to scan the hardware components thereof to obtain the identification codes of the hardware components, and to establish verification data associated with the identification codes of the hardware components thus obtained.
The network authentication device comprises a database module for storing hardware information associated with the identification codes of the hardware components of the user end, and a verification module for verifying identity of the user end based on relationship between the verification data received from the user end and the hardware information stored in the database module.
Other features and advantages of the present invention will become apparent in the following detailed description of the preferred embodiments with reference to the accompanying drawings, of which:
FIG. 1?is a block diagram illustrating a first preferred embodiment of a network authentication device according to the present invention;
FIG. 2?is a flow chart illustrating a registration procedure of a network authentication method implemented using the network authentication device of the first preferred embodiment according to the present invention;
FIG. 3?is a flow chart illustrating a login procedure of the network authentication method implemented using the network authentication device of the first preferred embodiment;
FIG. 4?is a schematic diagram illustrating the network authentication device implementing the network security authentication method for processing a digital signature;
FIG. 5?is a block diagram illustrating a second preferred embodiment of a network authentication device according to the present invention;
FIG. 6?is a flow chart illustrating a registration procedure of a network authentication method implemented using the network authentication device of the second preferred embodiment according to the present invention;
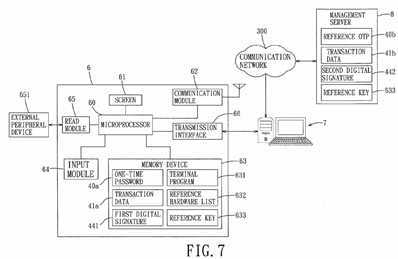
FIG. 7?is a block diagram illustrating the network authentication device of the second preferred embodiment that is configured to implement login and transaction procedures of the network authentication method of the present invention;
FIG. 8?is a flow chart illustrating the login procedure of the network authentication method implemented using the network authentication device of the second preferred embodiment; and
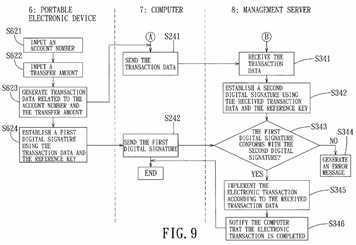
FIG. 9?is a flow chart illustrating the transaction procedure of the network authentication method implemented using the network authentication device of the second preferred embodiment.
DETAILED DESCRIPTION OF THE PREFERRED EMBODIMENTS
Before the present invention is described in greater detail, it should be noted that like elements are denoted by the same reference numerals throughout the disclosure.
Referring to?FIG. 1, the first preferred embodiment of a network authentication device according to the present invention is a verification server?1?operable to cooperate with a plurality of user ends?2?and a network server?3?(e.g., an internet contents provider or ICP) to implement a network authentication method. The verification server?1?includes a database module?10, a control module?11, a verification module?12, and a transmission module?13. For exemplary purposes, the network server?3?may be, but is not limited to, an online game server?3?a, a web bank server?3?b, or any other server that provides a network service requiring identity verification, such as a portal website. The user ends?2?include first, second and third user ends?2?a,?2?b?and2?c?associated with first, second and third users?51,?52?and?53, respectively. The user ends?2?a,?2?b?and?2?c?may be electronic equipment or handheld electronic devices capable of Internet browsing or data communications, such as notebook computers, smart phones, personal digital assistants, etc. Particularly, the user ends?2?are connected to the network server?3?through a first communication channel?300?a?in a communication network?300, and are connected to the verification server?1?through a second communication channel300?b?in the communication network?300?that is separate from the first communication channel?300?a. Accordingly, it is relatively difficult to attack the first and second communication channels?300?a?and?300?b?simultaneously for stealing information associated with the users?51-53. Moreover, the network server?3?is connected to the verification server?1?through a special channel. For example, the online game server?3?a?and the web bank server?3?b?are connected to the verification server?1?through special channels?301?and?302, respectively.
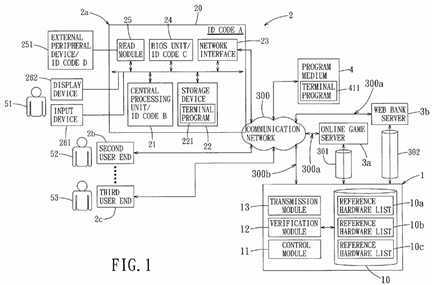
Taking the first user end?2?a?as an example, the first user end?2?a?includes a motherboard?20, a central processing unit?21, a storage device?22, a network interface?23, a basic input/output system (BIOS) unit?24, a read module?25, an external peripheral device?251, an input device?261?and a display device?262. In this embodiment, the motherboard?20, the central processing unit?21?and the BIOS unit?24?have unique identification codes (A), (B) and (C), respectively. Further, the read module?25?is a universal serial bus (USB) interface, and the corresponding external peripheral device?251?is a USB storage device (e.g., a memory card or a USB flash drive) and has a unique identification code (D). In other embodiments, the external peripheral device?251?may be a radio frequency identification (RFID) device or a near field communication (NFC) device. It should be noted that the unique identification code of the network interface?23?may be used for the network authentication method in other embodiments, and hardware components of the first user end?2?a?are also not limited to the disclosure herein.
Since each of the identification codes (A), (B), (C) and (D) of the hardware components (the motherboard?20, the central processing unit?21, the BIOS unit?24?and the external peripheral device?251) of the first user end?2?a?is unique, a combination of the identification codes (A), (B), (C) and (D) is certainly different from a combination of identification codes of hardware components of any one of other user ends?2. Thus, the combination of the identification codes of the first user end?2?a?is like a unique fingerprint of the first user end?2?a, and can be used for verifying the identity of the first user?51. Therefore, it is not possible to use other user ends having different hardware components to verify the identity of the first user?51.
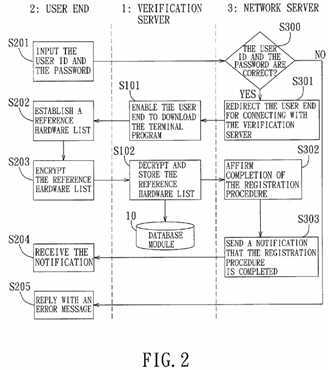
Referring to?FIGS. 1 and 2, the verification server?1?cooperates with the first user end?2?a?and the network server?3?to implement a registration procedure of the network authentication method according to the present invention. The registration procedure of the network authentication method includes the following steps.
In step S201, the first user?51?inputs personal information, a user identification (ID), and a password using the input device261?of the first user end?2?a?at a website provided by the network server?3. The personal information, the user ID, and the password are transmitted to the network server?3?through the first communication channel?300?a. In response to receipt of the personal information, the user ID and the password, the network server?3?is operable to check whether the personal information, the user ID and the password are correct in step S300. If affirmative, the network server?3?is operable to redirect the first user end?2?a?for connecting with the verification server?1?in step S301, so that the verification server?1?is operable to enable the first user end?2?a?to download a terminal program?411?from a program medium?4?in step S101. Otherwise, the network server?3?is operable to send an error message to the first user end?2?a?for displaying on the display device?262?of the first user end?2?a?in step S205.
It should be noted that, although the program medium?4?is an external website separate from the verification server?1?as shown in?FIG. 1?in this embodiment, it may be integrated as a part of the network server?3?or the verification server?1?in other embodiments. Moreover, this invention is not limited to downloading of the terminal program?411?from the network; for example, the program medium?4?may be a compact disc or other data carrier storing the terminal program?411?in practice.
Subsequently, after the first user end?2?a?stores and installs the terminal program?411?in the storage device?22?as a terminal program?221, the first user end?2?a?is operable to execute the terminal program?221, in step S202, for scanning the hardware components of the first user end?2?a?to obtain the identification codes (A)-(D) of the hardware components, and for establishing a reference hardware list?10?a?according to the identification codes of the hardware components thus obtained after the first user?51?inputs the user ID. In step S203, the first user end?2?a?is operable to encrypt the reference hardware list?10?a?with a session key and to directly send the encrypted reference hardware list to the verification server?1through the second communication channel?300?b.
In practice, the terminal program?221?allows the first user?51?to decide whether the external peripheral device?251?is scanned in step S202. Further, when the external peripheral device?251?of the first user end?2?a?does not have a unique identification code, the control module?11?of the verification server?1?is operable to generate a device-assigned identification code, and the transmission module?13?is operable to transmit the device-assigned identification code to the first user end?2?a?for storage in the external peripheral device?251?so as to serve as the identification code of the external peripheral device?251.
After the transmission module?13?of the verification server?1?receives the encrypted reference hardware list from the first user end?2?a, the control module?11?of the verification server?1?is operable, in step S102, to decrypt the encrypted reference hardware list so as to obtain the reference hardware list?10?a, and to store the reference hardware list?10?a?in the database module?10?as hardware information associated with the first user end?2?a. In particular, the reference hardware list?10?a?consists of the user ID associated with the first user?51, and the identification codes (A), (B), (C) and (D) of the hardware components (the motherboard?20, the central processing unit?21, the BIOS unit?24?and the external peripheral device?251) of the first user end?2?a. Similarly, the database module?10?further stores the reference hardware lists?10?band?10?c?corresponding to the second and third user ends?2?b?and?2?c, respectively.
The verification server?1?is further operable to send a notification to the network server?3?after storing the reference hardware list?10?a. Then, in response to the notification from the verification server?1, the network server?3?is operable, in step S302, to affirm that the registration procedure associated with the first user?51?is completed. Finally, the network server?3?is operable, in step S303, to send the first user end?2?a?a notification that the registration procedure is completed, and the first user end?2?a?is operable to receive the notification in step S204.
Referring to?FIGS. 1 and 3, the verification server?1?cooperates with the first user end?2?a?and the network server?3?to implement a login procedure of the network authentication method according to the present invention. The login procedure of the network authentication method includes the following steps.
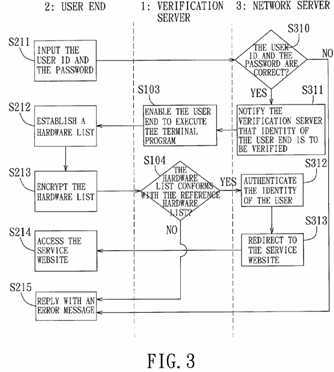
In step S211, the first user?51?inputs the user ID and the password using the input device?261?of the first user end?2?a?at the service website provided by the network server?3, and the first user end?2?a?is operable to transmit the user ID and the password to the network server?3?through the first communication channel?300?a. In step S310, the network server?3?is operable to verify whether the user ID and the password thus received are correct. In particular, the network server?3?is operable to determine whether the user ID and the password inputted in step S211?conform with the user ID and the password provided in the above-mentioned registration procedure. In alternative embodiments, the verification server?1can be configured to verify the user ID and the password associated with the first user?51?instead of the network server?3.
If it is determined that either the user ID or the password is incorrect in step S310, the network server?3?is operable to send an error message to the first user end?2?a?for displaying on the display device?262?of the first user end?2?a?in step S215. If it is determined that both of the user ID and the password are correct in step S310, the network server?3?is operable to notify the verification server?1?that identity of the first user end?2?a?associated with the first user?51?is to be verified in step S311. The network server?3?is further operable to redirect the first user end?2?a?for connecting with the verification server?1through the second communication channel?300?b.
In step S103, the verification server?1?is operable to enable the first user end?2?a?to execute the terminal program?221stored in the storage device?22?of the first user end?2?a. In step S212, the first user end?2?a?is operable to execute the terminal program?221?for scanning the hardware components thereof to obtain the identification codes of the hardware components of the first user end?2?a, and for establishing a hardware list according to the identification codes of the hardware components thus obtained. Then, in step S213, the first user end?2?a?is operable to encrypt the hardware list with the session key, and to send the encrypted hardware list as verification data for verifying identity of the first user end?2a?to the verification server?1?through the second communication channel?300?b.
In step S104, the control module?11?of the verification server?1?is operable to decrypt the verification data from the first user end?2?a?to obtain the hardware list. Then, the verification module?12?of the verification server?1?is operable to compare the hardware list thus obtained with the reference hardware list?10?a?stored in the database module?10?for verifying the identity of the first user?51?associated with the first user end?2?a.
When the hardware list obtained in step S104?does not conform with the reference hardware list?10?a?stored in the database module?10, the verification module?12?is operable to determine that the verification of the first user?51?is unsuccessful and to send the error message to the first user end?2?a. Accordingly, the first user end?2?a?is denied access to the service website provided by the network server?3, and is operable to display the error message on the display device?262?in step S215. On the other hand, when the hardware list conforms with the reference hardware list?10?a, the verification module?12?is operable to determine that the verification of the first user?51?is successful, and to notify the network server?3?of the result of the verification made thereby. Thus, the network server?3?is operable to authenticate the identity of the first user?51?in step S312, and then, to redirect the first user end?2?a?associated with the first user?51?for connecting with the service website provided by the network server?3?in step S313. In step S214, the first user end?2?a?is authorized to access the service website.
After the first user end?2?a?is authorized to access the service website in the login procedure, the verification server?1cooperates with the first user end?2?a?and the network server?3?to further implement the network security authentication method for processing a digital signature when the first user?51?intends to conduct an electronic transaction with the network server?3. The network security authentication method for processing a digital signature will be described in detail below with reference to?FIGS. 1 and 4.
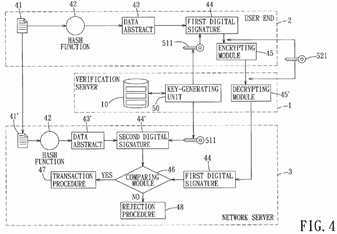
The verification server?1?further includes a key-generating unit?50?and a decrypting module?45′, the terminal program?221includes a hash function?42?and an encrypting module?45, and the network server?3?includes a comparing module?46. The key-generating unit?50?of the verification server?1?is operable to generate a key?511?according to the reference hardware list?10?a?stored in the database module?10. The key?511?is sent to the first user end?2?a?through the second communication channel?300?b?in the communication network?300, and is sent to the network server?3?through the special channel?301(302).
When the first user?51?intends to conduct an electronic transaction with the network server?3?using the first user end?2?a, the first user end?2?a?is operable to generate transaction data?41?related to the electronic transaction and to send the transaction data?41?to the network server?3?through the first communication channel?300?a?in the communication network300. The terminal program?221?of the first user end?2?a?uses the hash function?42?to draw out a data abstract?43?from the transaction data?41, and processes the data abstract?43?into a first digital signature?44?using the key?511?sent by the verification server?1. Then, the encrypting module?45?is operable to encrypt the first digital signature?44?with a session key521, and the encrypted first digital signature is sent to the verification server?1?through the second communication channel300?b. The decrypting module?45′ of the verification server?1?is operable to decrypt the encrypted first digital signature to obtain the first digital signature?44, and then, the first digital signature?44?is sent to the network server?3.
After the network server?3?receives the key?511?from the verification server?1?and the transaction data?41′ from the first user end?2?a, the network server?3?is operable to draw out a data abstract?43′ from the transaction data?41′ using the hash function?42. Then, the network server?3?is operable to process the data abstract?43′ into a second digital signature?44′ using the key?511?sent by the verification server?1. The comparing module?46?of the network server?3?is operable to compare the second digital signature?44′ with the first digital signature?44?generated by the first user end?2?a. When the second digital signature?44′ conforms with the first digital signature?44, the network server?3?is operable to determine that the transaction data?41?was not tampered during transmission from the first user end?2?a?to the network server?3?as the transaction data?41′ through the first communication channel?300?a. Subsequently, the network server?3?is operable to implement a transaction procedure?47?for completing the electronic transaction according to the transaction data?41′. On the other hand, when the second digital signature?44′ does not conform with the first digital signature?44, the network server?3?is operable to determine that the transaction data?41′ was tampered during transmission from the first user end?2a?to the network server so that the data abstract?43′ from the tampered transaction data?41′ is not identical to the data abstract?43?from the original transaction data?41. Thus, the network server?3?is operable to implement a rejection procedure?48?for rejecting the electronic transaction.
In alternative embodiments, the comparing module?46?of the network server?3?can be omitted, and the network server?3?is operable to send the second digital signature?44′ to the verification server?1. Then, the verification server?1?is configured to compare the second digital signature?44′ with the first digital signature?44?instead of the comparing module?46, and to send the comparing result to the network server?3. In response to the comparing result from the verification server?1, the network server?3?is operable to alternatively implement the transaction procedure?47?and the rejection procedure?48.
Referring to?FIG. 5, the second preferred embodiment of a network authentication device according to the present invention is a management server?8?that integrates the functions of the verification server?1?and the network server?3?of the first preferred embodiment. In this embodiment, the user end is a portable electronic device?6, such as a smart phone.
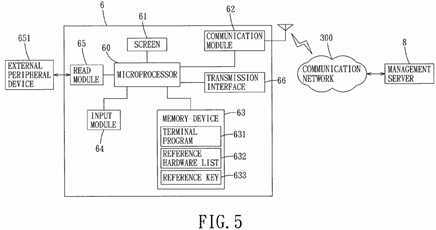
The portable electronic device?6?includes a microprocessor?60, a screen?61, a communication module?62, a transmission interface?66, a memory device?63, an input module?64, and a read module?65. The communication module?62?is operable to communicate with the management server?8?through a communication network?300. The memory device?63?stores a terminal program?631, a reference hardware list?632, and a reference key?633?made from the reference hardware list?632. For instance, the read module?65?is a memory card reader, and an external peripheral device?651?connected thereto is a memory card. The reference hardware list?632?is associated with a combination of the identification codes of the microprocessor?60, the screen?61, the communication module?62, the transmission interface?66, the memory device?63, the input module?64, and/or the external peripheral device?651. While the terminal program?631?is similar to the terminal program?221?in the first preferred embodiment, it is required to input a correct personal identification number (PIN) for executing the terminal program?631?in this embodiment. In other embodiments, the user associated with the portable electronic device?6?only needs to input the PIN upon turning on the portable electronic device?6, and doest not need to input the PIN or a new PIN again for executing the terminal program?631.
Referring to?FIGS. 5 and 6, the management server?8?is operable to cooperate with the portable electronic device?6?to implement a registration procedure of the network authentication method according to the present invention. The registration procedure of the network authentication method includes the following steps.
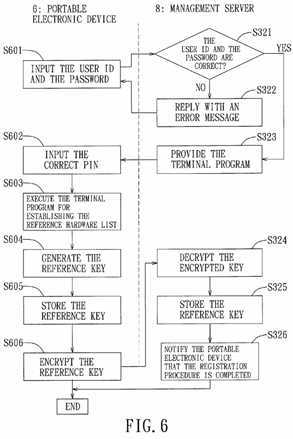
In step S601, after the portable electronic device?6?is connected to the management server?8?using the communication module?62?through the communication network?300, a user associated with the portable electronic device?6?uses the input module?64?of the portable electronic device?6?to input a user identification (ID) and a password at a webs ite provided by the management server?8. In response to receipt of the user ID and the password, the management server?8?is operable to check whether the user ID and the password are correct in step S321. If either the user ID or the password is incorrect, the management server?8?is operable to reply with an error message to the portable electronic device?6?in step S322. On the other hand, if both the user ID and the password are correct, the management server?8?is operable to provide the terminal program?631?to the portable electronic device?6?in step S323.
When the user of the portable electronic device?6?inputs the correct PIN in step S602, the portable electronic device?6?is operable, in step S603, to execute the terminal program?631?for scanning hardware components of the portable electronic device?6?to obtain identification codes of the hardware components, and for establishing and storing the reference hardware list?632. Then, the portable electronic device?6?executes the terminal program?631?for generating the reference key?633?based on the reference hardware list?632?in step S604, and is operable to store the reference key?633?in the memory device?63?in step S605. In step S606, the portable electronic device?6?is operable to encrypt the reference key633?with a session key so as to obtain an encrypted key, and to send the encrypted key to the management server?8. In other embodiments, step S602?may be omitted since the user already inputted the PIN upon turning on the portable electronic device?6.
After receiving the encrypted key from the portable electronic device?6, the management server?8?is operable to decrypt the encrypted key so as to obtain the reference key?633?in step S324, and to store the reference key in step S325. Finally, in step S326, the management server?8?is operable to notify the portable electronic device?6?that the registration procedure is completed.
Referring to?FIG. 7, the portable electronic device?6?is connected to a computer?7?through the transmission interface?66that may be either a cable transmission interface or a wireless transmission interface. The input module?64?of the portable electronic device?6?is a key panel or a touch panel for generating electronic data in responses to an input from the user of the portable electronic device?6. The electronic data is transmitted to the computer?7?through the transmission interface?66, and is subsequently sent to the management server?8?through the communication network?300. In the case of the portable electronic device?6?without the transmission interface?66, the user can use a keyboard of the computer?7?to input the electronic data displayed on the screen?61?of the portable electronic device?6?so as to transmit the electronic data to the management server?8.
Referring to?FIGS. 7 and 8, the management server?8?is operable to cooperate with the portable electronic device?6?and the computer?7?to implement a login procedure of the network authentication method according to the present invention. The login procedure of the network authentication method includes the following steps.
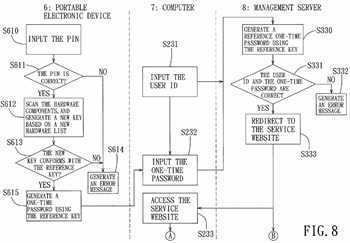
First, the user of the portable electronic device?6?needs to input the PIN in step S610. Then, in step S611, the portable electronic device?6?is operable to determine whether the PIN inputted in step S610?is correct. If it is determined that the PIN is incorrect, the portable electronic device?6?is operable to generate an error message in step S614. If the PIN inputted in step S610?is correct, the portable electronic device?6?is operable, in step S612, to execute the terminal program?631?for scanning the hardware components of the portable electronic device?6?to obtain identification codes of the hardware components, for establishing a new hardware list according to the identification codes thus obtained, and for generating a new key based on the new hardware list?632?thus established. In other embodiments, step S610?and S611?may be omitted, and the portable electronic device?6?is operable to directly implement step S612?when the user wants to use the portable electronic device?6?for accessing the service website provided by the management server?8.
Then, in step S613, the portable electronic device?6?is operable to execute the terminal program?631?for comparing the new key generated in step S612?with the reference key?633?stored in the memory device?63. When the new key does not conform with the reference key?633, it can be determined that the new key was tampered or that the terminal program?631and the reference key?633?were moved to another device, and the flow goes to step S614. When the new key conforms with the reference key?633, it can be determined that the new key and the reference key?633?were generated using the same device and that the terminal program?631?and the reference key?633?were not moved to another device, and the portable electronic device?6?is operable to execute the terminal program?631?for further generating a one-time password (OTP)?40?a?using the reference key?633?in step S615. Then, the OTP?40?a?is transmitted to the computer?7?through the transmission interface?66?of the portable electronic device?6. In the case of the portable electronic device?6?without the transmission interface?66, the user can use the keyboard of the computer?7?to input the OTP?40?a?displayed on the screen61?of the portable electronic device?6?in step S232.
In order to login the service website provided by the management server?8, the user needs to input the user ID using the keyboard of the computer?7?in step S231, and then, the user ID and the OTP?40?a?are sent to the management server?8through the communication network?300.
In step S330, the management server?8?is operable to generate a reference one-time password?40?b?using the reference key?633?stored therein in step S325?of the registration procedure. Upon receiving the user ID and the OTP?40?a?from the computer?7, the management server?8?is operable to compare the OTP?40?a?with the reference OTP?40?b?and to determine whether the user ID is correct in step S331. If the OTP?40?a?does not conform with the reference OTP?40?b?or the user ID is incorrect, the management server?8?is operable to generate an error message in step S332. If the OTP?40?a?conforms with the reference OTP?40?b?and the user ID is correct, the management server?8?is operable to redirect the computer?7?for connecting with the service website provided by the management server?8?in step S333. In step S233, the computer?7?is authorized to access the service website.
After the computer?7?has received authorization to access the service website in the login procedure, the management server?8?cooperates with the portable electronic device?6?and the computer?7?to further implement the network security authentication method for processing a digital signature when the user intends to conduct an electronic transact ion with the management server?8. The network security authentication method for processing a digital signature will be described in detail below with reference to?FIGS. 7 and 9.
For conducting the electronic transaction with the management server?8, the user needs to input a receiving account number in step S621?and to input a transfer amount in step S622?using the input module?64?of the portable electronic device?6. In step S623, the portable electronic device?6?is operable to generate transaction data?41?a?related to the account number and the transfer amount, and to send the transaction data?41?a?to the computer?7?through the transmission interface?66. Further, in step S624, the portable electronic device?6?is operable to execute the terminal program?631?for establishing a first digital signature?441?using the transaction data?41?a?and the reference key?633, and to send the first digital signature?441?to the computer?7?through the transmission interface?66.
In response to receipt of the transaction data?41?a?and the first digital signature?441, the computer?7?is operable to send the transaction data?41?a?and the first digital signature?441?to the management server?8?through the communication network?300?in steps S241?and S242, respectively. It should be noted that, in the case of the portable electronic device?6without the transmission interface?66, the user may use the keyboard of the computer?7?to input the account number and the transfer amount so that the computer?7?is operable to obtain the transaction data?41?a?consisting of the account number and the transfer amount.
The management server?8?is operable to receive transaction data?41?b?corresponding to the transaction data?41?a?from the computer?7?through the communication network?300?in step S341, and then, to establish a second digital signature?442using the received transaction data?41?b?and the reference key?633?in step S342. In step S343, the management server?8is operable to receive the first digital signature?441, and to compare the first digital signature?441?with the second digital signature?442. If the first digital signature?441?does not conform with the second digital signature?442, the management server?8?is operable to determine that the transaction data?41?a?was tampered during transmission and that the received transaction data?41?b?is different from the transaction data?41?a. Therefore, the management server?8?is operable to reject the electronic transaction and to generate an error message in step S344. If the first digital signature?441?conforms with the second digital signature?442, the management server?8?is operable to determine that the received transaction data?41b?is correct and is identical to the transaction data?41?a. Accordingly, the management server?8?is operable to implement the electronic transaction according to the account number and the transfer amount of the received transaction data?41?bin step S345. Finally, in step S346, the management server?8?is operable to notify the computer?7?that the electronic transaction is completed.
In sum, the network authentication method implemented using the network authentication device according to this invention has the following advantages. First, the user end may execute the terminal program for scanning the hardware components of the user end and for establishing the hardware list according to the identification codes of the hardware components thus obtained for subsequent use in authenticating the user. Thus, a network content provider does not need to purchase additional equipment for authentication, and does not need to provide the user with a personalized token, integrated circuit card, USB flash drive, etc. Also, the user does not need to have additional authentication devices for different websites. Further, in the first preferred embodiment, since the user end is connected to the network server through the first communication channel and is connected to the verification server through the second communication channel that is separate from the first communication channel, it is relatively difficult to attack the first and second communication channels simultaneously for stealing and tampering the data sent by the user end.
SRC=https://www.google.com.hk/patents/US20110185181
Network authentication method and device for implementing the same
标签:des style blog http color io os ar strong
原文地址:http://www.cnblogs.com/coryxie/p/3968337.html