标签:3.1 ida 参考 insecure roc 2.3 monit The 手工
一、登陆密码加密认证脚本应用场景日常操作,经常明文指定了MySQL密码来登录MySQL服务,在登录成功之后就会抛出下面的警告:
[root@git-server ~]# mysql -uroot -p‘wujianwei‘
Warning: Using a password on the command line interface can be insecure.
Welcome to the MySQL monitor. Commands end with ; or \g.
Your MySQL connection id is 510
Server version: 5.6.36-log Source distribution
Copyright (c) 2000, 2017, Oracle and/or its affiliates. All rights reserved.
Oracle is a registered trademark of Oracle Corporation and/or its
affiliates. Other names may be trademarks of their respective
owners.
Type ‘help;‘ or ‘\h‘ for help. Type ‘\c‘ to clear the current input statement.
mysql> 对于要求严格的业务生产场景不允许出现Warning的,所以可能需要自己定制一下这个错误的逻辑。
当然如果不需要知道密码,能不能换个方式来做呢,其实也行,在5.6中开始有了loginpath,和Oracle中的钱包的功能差不多,其实就是一种认证,做了授权,你不需要知道这些信息,loginpath就是一道桥梁为你做了认证。
如果你是5.5的版本,没了loginpath,有没有其他的方案来满足需求呢。
有的人可能这个时候开始问,需求是什么?
我们设想一下,命令行的方式中,输入明文密码,那还要密码干嘛,干脆我输入密码的时候你别看,但是history命令里面有啊。
所以这也算是一个风险点的入口,如果因为一些意外的情况登录,那么这种情况就很尴尬了。这是需求一。
还有一种场景,如果我们有大量的MySQL环境,每个环境的DBA账户密码是统一的,但是密码很复杂。我们不能输入明文,那么就输入密码格式,那就意味着交互和手动输入,手动输入简直了,你会发现这种操作真是原始,高级一点,用下keypass或者keepass等,这个是依赖于本地的环境配置。所以需求二的特点就是手工维护密码啰嗦,手工输入密码太原始。
那我们写脚本,但是脚本里面的密码还是可见的,调用的明文密码问题解决了,但是内容中的密码还是可读的。
所以这种情况下,一个很自然的方法就是加密。
其中一种是对密码加密,比如我们得到一个密码加密后的串,在需要调用的时候做一下解密,得到真实的密码。这个过程是在脚本里的逻辑来实现,所以我们得到明文密码的概率要低一些。
另外一类就是对文件加密,比如对整个文件加密,加密之后文件就没法读了。所以加密后的密码又被加密了。对文件加密有shell的方式还有python等语言。
如果要调用脚本的时候,其实就是先解密文件,然后调用解密逻辑,得到真正的密码,然后开启访问的请求。
比如我得到了一个加密后的密码串。调用的解密逻辑是decrypt_passwd,当然这个是可读还可逆的。
base64加密解密站长工具:
https://base64.supfree.net/
[root@git-server ~]# echo wujianwei|base64
d3VqaWFud2VpCg==[root@git-server ~]# echo d3VqaWFud2VpCg==|base64 -d
wujianwei脚本内容如下:
[root@git-server ~]# cat test03.sh
#!/bin/sh
Pass=‘d3VqaWFud2VpCg==‘
sock=/tmp/mysql.sock
function decrypt_passwd
{
tmp_pass=$1
dec_pass=`echo $tmp_pass|base64 -d`
}
decrypt_passwd $Pass
port=$1
#if [ ! -n "$port" ]; then
#echo ‘############################################‘
#echo ‘Please input correct MySQL Port and try again.‘
#echo ‘############################################‘
#ps -ef|grep mysqld|grep -v grep |grep -v mysqld_safe
#exit
#fi
/usr/local/mysql/bin/mysql -uroot -p$dec_pass -P$1 -S$sock通过此脚本登陆MySQL服务,到此处已经实现了脚本密码转换方式登陆MySQL服务
[root@git-server ~]# sh test03.sh.sh 3306
Warning: Using a password on the command line interface can be insecure.
Welcome to the MySQL monitor. Commands end with ; or \g.
Your MySQL connection id is 513
Server version: 5.6.36-log Source distribution
Copyright (c) 2000, 2017, Oracle and/or its affiliates. All rights reserved.
Oracle is a registered trademark of Oracle Corporation and/or its
affiliates. Other names may be trademarks of their respective
owners.
Type ‘help;‘ or ‘\h‘ for help. Type ‘\c‘ to clear the current input statement.
mysql> 参考地址:
http://www.isays.cn/7336.html
gzexe无需安装任何软件是linux自带的功能使用只需要执行命令即可
假如说我们这个脚本名字叫test03.sh
那我们就在linux服务器命令执行gzexe test03.sh即可
[root@git-server ~]# gzexe test03.sh
test03.sh: 51.3%原来的文件就加密了之后会在目录产生一个test03.sh~的文件这个就是原来文件的备份
[root@git-server ~]# ll test03.sh*
-rwxr-xr-x 1 root root 1122 Jul 20 16:57 test03.sh
-rwxr-xr-x 1 root root 587 Jul 20 16:55 test03.sh~发现test03.sh脚本已经变成二进制文件
如下图:
[root@git-server ~]# chmod +x test03.sh
[root@git-server ~]# ll test03.sh
-rwxr-xr-x 1 root root 1128 Jul 20 22:56 test03.sh
[root@git-server ~]# cp test03.sh /usr/local/sbin/登陆MySQL:
[root@git-server ~]# test03.sh 3306
Warning: Using a password on the command line interface can be insecure.
Welcome to the MySQL monitor. Commands end with ; or \g.
Your MySQL connection id is 517
Server version: 5.6.36-log Source distribution
Copyright (c) 2000, 2017, Oracle and/or its affiliates. All rights reserved.
Oracle is a registered trademark of Oracle Corporation and/or its
affiliates. Other names may be trademarks of their respective
owners.
Type ‘help;‘ or ‘\h‘ for help. Type ‘\c‘ to clear the current input statement.
mysql> 假如说我们这个脚本名字叫test03.sh
那我们就执行
gzexe -d test03.sh
原来的文件就加解密了放在目录里面
查看test03.sh内容,事实证明文件内容已经解密了
[root@git-server ~]# cat test03.sh
#!/bin/sh
sock=/tmp/mysql.sock
Pass="d3VqaWFud2VpCg=="
function decrypt_passwd
{
tmp_pass=$1
dec_pass=`echo $tmp_pass|base64 -d`
}
decrypt_passwd $Pass
port=$1
#if [ ! -n "$port" ]; then
#echo ‘############################################‘
#echo ‘Please input correct MySQL Port and try again.‘
#echo ‘############################################‘
#ps -ef|grep mysqld|grep -v grep |grep -v mysqld_safe
#exit
#fi
/usr/local/mysql/bin/mysql -uroot -p$dec_pass -P$1 -S$sockshc是linux的一款加密脚本的插件东西比较安全我们可以利用
shc官网:https://github.com/yanncam/UnSHc
wget -q http://www.datsi.fi.upm.es/~frosal/sources/shc-3.8.9.tgz
tar zxvf shc-3.8.9.tgz
cd shc-3.8.9
make[root@git-server shc-3.8.9]# make
cc -Wall shc.c -o shc
*** Do you want to probe shc with a test script?
*** Please try... make test
[root@git-server shc-3.8.9]# make install
*** Installing shc and shc.1 on /usr/local
*** Do you want to continue? yes
install -c -s shc /usr/local/bin/
install -c -m 644 shc.1 /usr/local/man/man1/
install: target `/usr/local/man/man1/‘ is not a directory: No such file or directory
make: *** [install] Error 1
请创建 mkdir -p /usr/local/man/man1/ ,然后运行make install-e date (指定过期日期)
-m message (指定过期提示的信息)
-f script_name(指定要编译的shell的路径及文件名)
-r Relax security. (可以相同操作系统的不同系统中执行)
-v Verbose compilation(编译的详细情况)
假如说我们这个脚本名字叫test03.sh
那我们就执行
shc -v -f test03.sh
-v 是现实加密过程
-f 后面跟需要加密的文件
[root@git-server ~]# shc -v -f test03.sh
shc shll=sh
shc [-i]=-c
shc [-x]=exec ‘%s‘ "$@"
shc [-l]=
shc opts=
shc: cc test03.sh.x.c -o test03.sh.x
shc: strip test03.sh.x
shc: chmod go-r test03.sh.x
[root@git-server ~]# ll test03.sh*
-rwxr-xr-x 1 root root 598 Jul 20 17:36 test03.sh
-rwx--x--x 1 root root 12376 Jul 20 17:36 test03.sh.x
-rw-r--r-- 1 root root 12805 Jul 20 17:36 test03.sh.x.ctest03.sh.x为二进制文件,赋予执行权限后,可直接执行。更改名字mv test03.sh.x test03.sh
test03.sh.x.c 是c源文件。基本没用,可以删除
[root@git-server ~]# mv test03.sh.x test03.sh
验证文件是否为二进制文件: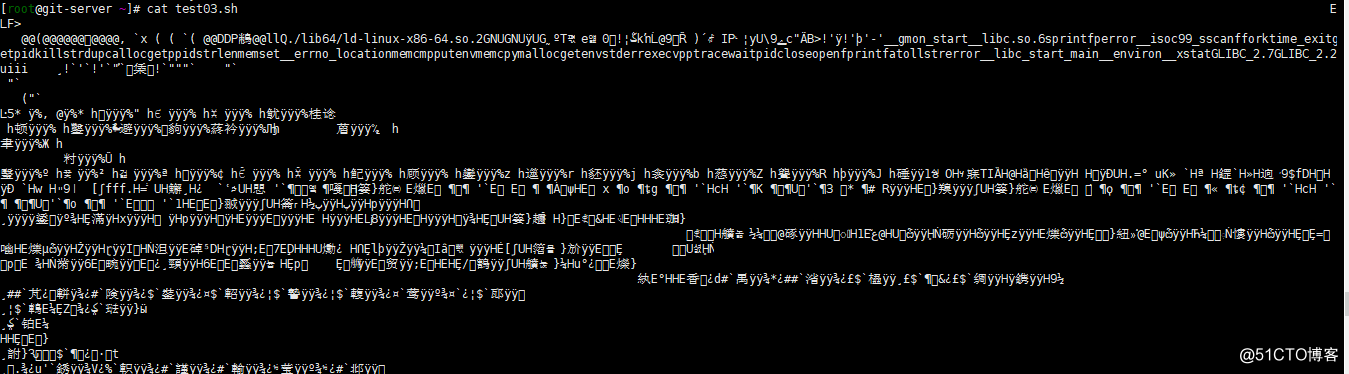
登陆MySQL服务:
[root@git-server ~]# ./test03.sh 3306
Warning: Using a password on the command line interface can be insecure.
Welcome to the MySQL monitor. Commands end with ; or \g.
Your MySQL connection id is 518
Server version: 5.6.36-log Source distribution
Copyright (c) 2000, 2017, Oracle and/or its affiliates. All rights reserved.
Oracle is a registered trademark of Oracle Corporation and/or its
affiliates. Other names may be trademarks of their respective
owners.
Type ‘help;‘ or ‘\h‘ for help. Type ‘\c‘ to clear the current input statement.
mysql> 另shc还提供了一种设定有效执行期限的方法,过期时间,如:
#shc -e 14/09/2016 -m -f test03.sh
选项“-e”指定过期时间,格式为“日/月/年”;选项“-m”指定过期后执行此shell程序的提示信息。
如果在过期后执行,则会有如下提示:
#./test03.sh.x
./test03.sh.x: has expired!(文件已经过期)
使用以上方法要注意,需防止用户更改系统时间,可以通过在程序中加入自动更新系统时间的命令来解决此问题。
利用这个脚本来解密
https://github.com/yanncam/UnSHc
[root@git-server ~]# wget https://github.com/yanncam/UnSHc/archive/master.zip
[root@git-server ~]# unzip master.zip
Archive: master.zip
202e5c200005a1b8e474fbfccfb983a582708da1
creating: UnSHc-master/
inflating: UnSHc-master/README.md
creating: UnSHc-master/latest/
inflating: UnSHc-master/latest/unshc.sh
creating: UnSHc-master/release/
creating: UnSHc-master/release/0.2/
inflating: UnSHc-master/release/0.2/unshc-v0.2.sh
inflating: UnSHc-master/release/0.2/unshc-v0.2b.sh
creating: UnSHc-master/release/0.3/
inflating: UnSHc-master/release/0.3/unshc-v0.3.sh
creating: UnSHc-master/release/0.4/
inflating: UnSHc-master/release/0.4/unshc-v0.4.sh
creating: UnSHc-master/release/0.5/
inflating: UnSHc-master/release/0.5/unshc-v0.5.sh
creating: UnSHc-master/release/0.6/
inflating: UnSHc-master/release/0.6/unshc-v0.6.sh
creating: UnSHc-master/release/0.7/
inflating: UnSHc-master/release/0.7/unshc-v0.7.sh
creating: UnSHc-master/release/0.8/
inflating: UnSHc-master/release/0.8/unshc-v0.8.sh
creating: UnSHc-master/sample/
inflating: UnSHc-master/sample/test.sh
inflating: UnSHc-master/sample/test.sh.x
inflating: UnSHc-master/sample/test.sh.x.c [root@git-server latest]# cd /root/UnSHc-master/latest;
[root@git-server latest]# ./unshc.sh -h
_ _ _____ _ _
| | | | / ___| | | |
| | | |_ __ \ `--.| |_| | ___
| | | | ‘_ \ `--. \ _ |/ __|
| |_| | | | /\__/ / | | | (__
\___/|_| |_\____/\_| |_/\___|
--- UnSHc - The shc decrypter.
--- Version: 0.8
------------------------------
UnSHc is used to decrypt script encrypted with SHc
Original idea from Luiz Octavio Duarte (LOD)
Updated and modernized by Yann CAM
- SHc : [http://www.datsi.fi.upm.es/~frosal/]
- UnSHc : [https://www.asafety.fr/unshc-the-shc-decrypter/]
------------------------------
[*] Usage : ./unshc.sh [OPTIONS] <file.sh.x>
-h | --help : print this help message
-a OFFSET | --arc4 OFFSET : specify the arc4() offset arbitrarily (without 0x prefix)
-d DUMPFILE | --dumpfile DUMPFILE : provide an object dump file (objdump -D script.sh.x > DUMPFILE)
-s STRFILE | --stringfile STRFILE : provide a string dump file (objdump -s script.sh.x > STRFILE)
-o OUTFILE | --outputfile OUTFILE : indicate the output file name
[*] e.g :
./unshc.sh script.sh.x
./unshc.sh script.sh.x -o script_decrypted.sh
./unshc.sh script.sh.x -a 400f9b
./unshc.sh script.sh.x -d /tmp/dumpfile -s /tmp/strfile
./unshc.sh script.sh.x -a 400f9b -d /tmp/dumpfile -s /tmp/strfile -o script_decrypted.sh
[root@git-server latest]# [root@git-server ~]# /root/UnSHc-master/latest/unshc.sh test03.sh
_ _ _____ _ _
| | | | / ___| | | |
| | | |_ __ \ `--.| |_| | ___
| | | | ‘_ \ `--. \ _ |/ __|
| |_| | | | /\__/ / | | | (__
\___/|_| |_\____/\_| |_/\___|
--- UnSHc - The shc decrypter.
--- Version: 0.8
------------------------------
UnSHc is used to decrypt script encrypted with SHc
Original idea from Luiz Octavio Duarte (LOD)
Updated and modernized by Yann CAM
- SHc : [http://www.datsi.fi.upm.es/~frosal/]
- UnSHc : [https://www.asafety.fr/unshc-the-shc-decrypter/]
------------------------------
[*] Input file name to decrypt [test03.sh]
[+] ARC4 address call candidate : [0x400ea0]
[*] Extracting each args address and size for the 14 arc4() calls with address [0x400ea0]...
[0] Working with var address at offset [0x6022e4] (0x2a bytes)
[1] Working with var address at offset [0x6026af] (0x1 bytes)
[2] Working with var address at offset [0x6026b1] (0x8 bytes)
[3] Working with var address at offset [0x6026bb] (0x3 bytes)
[4] Working with var address at offset [0x6027f7] (0xf bytes)
[5] Working with var address at offset [0x602693] (0x1 bytes)
[6] Working with var address at offset [0x60280a] (0x16 bytes)
[7] Working with var address at offset [0x602695] (0x16 bytes)
[8] Working with var address at offset [0x602825] (0x13 bytes)
[9] Working with var address at offset [0x6026b0] (0x1 bytes)
[10] Working with var address at offset [0x602838] (0x1 bytes)
[11] Working with var address at offset [0x60239c] (0x257 bytes)
[12] Working with var address at offset [0x60267d] (0x13 bytes)
[13] Working with var address at offset [0x602668] (0x13 bytes)
[*] Extracting password...
[+] PWD address found : [0x6026e2]
[+] PWD size found : [0x100]
[*] Executing [/tmp/0Kq6m3] to decrypt [test03.sh]
[*] Retrieving initial source code in [test03.sh.sh]
[*] All done!
[root@git-server ~]# [root@git-server ~]# ll test03.sh*
-rwx--x--x 1 root root 12184 Jul 20 23:36 test03.sh
-rw-r--r-- 1 root root 597 Jul 20 23:43 test03.sh.sh
-rw-r--r-- 1 root root 11964 Jul 20 23:36 test03.sh.x.c
[root@git-server ~]# 此时test03.sh.sh 这个文件就是原来的文件
[root@git-server ~]# cat test03.sh.sh
#!/bin/sh
sock=/tmp/mysql.sock
Pass="d3VqaWFud2VpCg=="
function decrypt_passwd
{
tmp_pass=$1
dec_pass=`echo $tmp_pass|base64 -d`
}
decrypt_passwd $Pass
port=$1
#if [ ! -n "$port" ]; then
#echo ‘############################################‘
#echo ‘Please input correct MySQL Port and try again.‘
#echo ‘############################################‘
#ps -ef|grep mysqld|grep -v grep |grep -v mysqld_safe
#exit
#fi
/usr/local/mysql/bin/mysql -uroot -p$dec_pass -P$1 -S$sock到此处MySQL的登陆密码的加密演示完毕。欢迎同学们一起交流学习
标签:3.1 ida 参考 insecure roc 2.3 monit The 手工
原文地址:http://blog.51cto.com/wujianwei/2147903