标签:static substring end 简单 为我 响应 null ram 逆向
环境配置:
Pyhton
Java
dex2jar(将apk反编译成java源码)
jd_gui(源码查看)
jadx
已root的手机或者安卓模拟器
fiddler
分析:
首先我们用fiddler抓包工具对app的登陆进行抓包,这个app抓包需要开启全局代理,不然会抓不到数据。
如果还不会使用全局代理抓包的朋友,可以看下前面一篇文章,里面有详细的抓包教程。
抓包的数据如下:
<ignore_js_op>
我们可以看到有个 token 的参数,有经验的朋友知道,这是服务器后台生成的,而且在发送登陆验证码请求之前并没有其它的数据交换!
<ignore_js_op>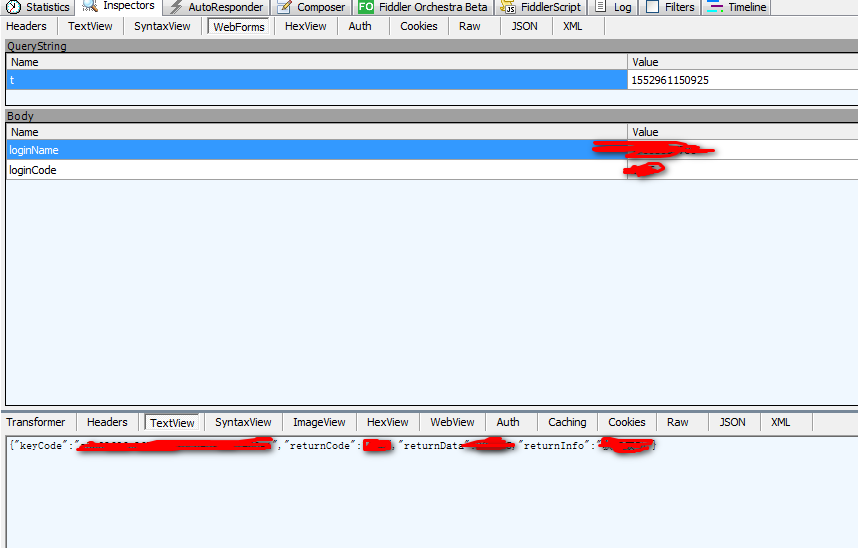
破解过程:
1.将安卓app的后缀更改为可解密的包,并解压
<ignore_js_op>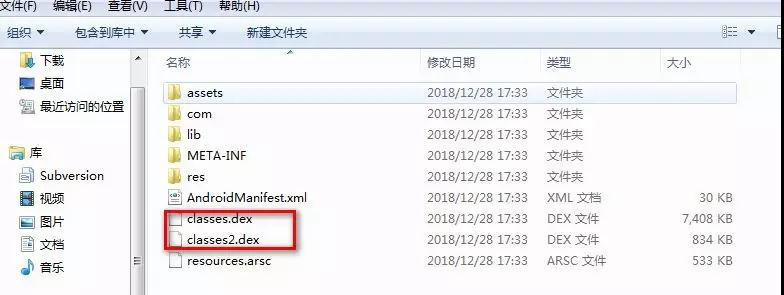
2.将解压后生成的后缀为 .dex 复制到 dex2jar 安装目录中
<ignore_js_op>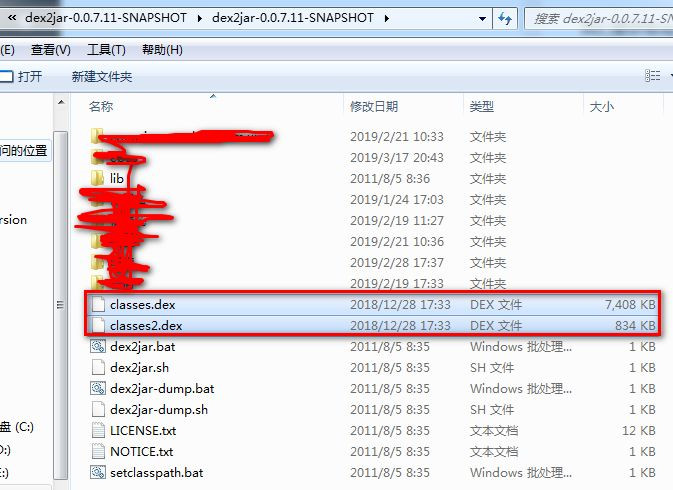
3.DOS命令行进入此文件夹,然后执行命令:dex2jar.bat classes.dex
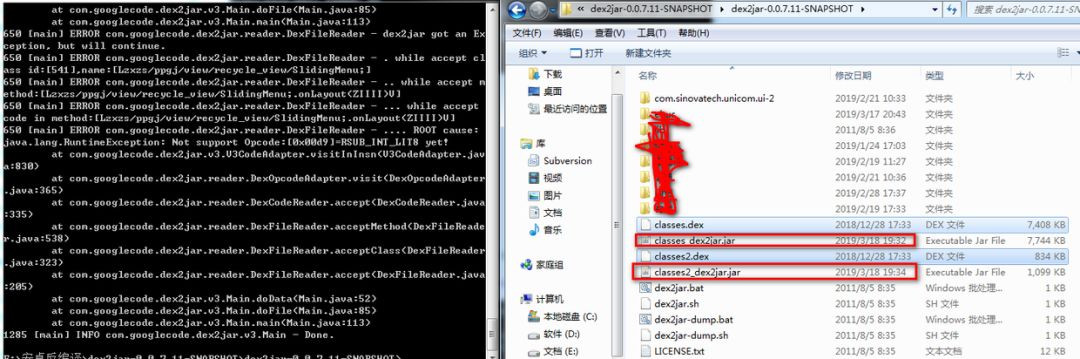
4. 生成.jar文件就是apk的源码了,我们使用 jd_gui 来查看源码 <ignore_js_op>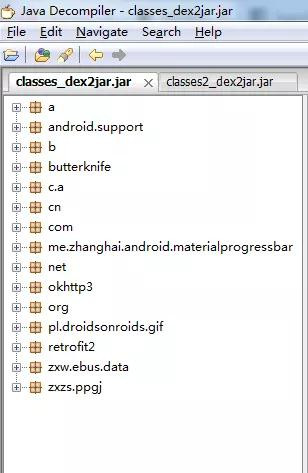
幸运的是这个app并没有加固,有app进行了加固,像腾讯乐固,360加固等等
<ignore_js_op>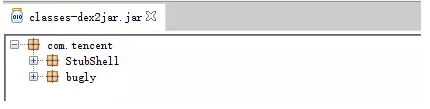
<ignore_js_op>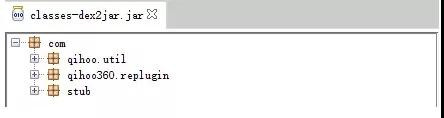
5.第二种反编译的方法是直接使用工具 jadx 打开 .apk 文件
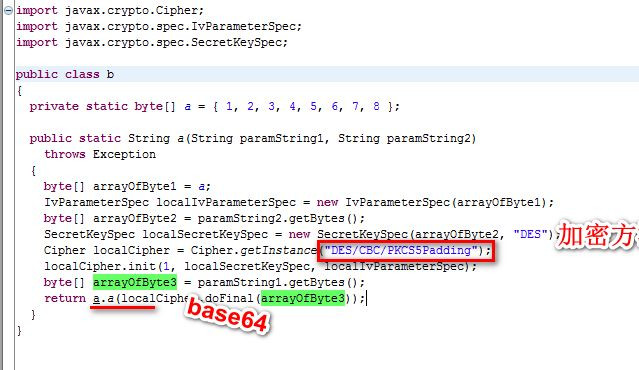
6.根据请求或响应的参数去源码中搜索加密方式
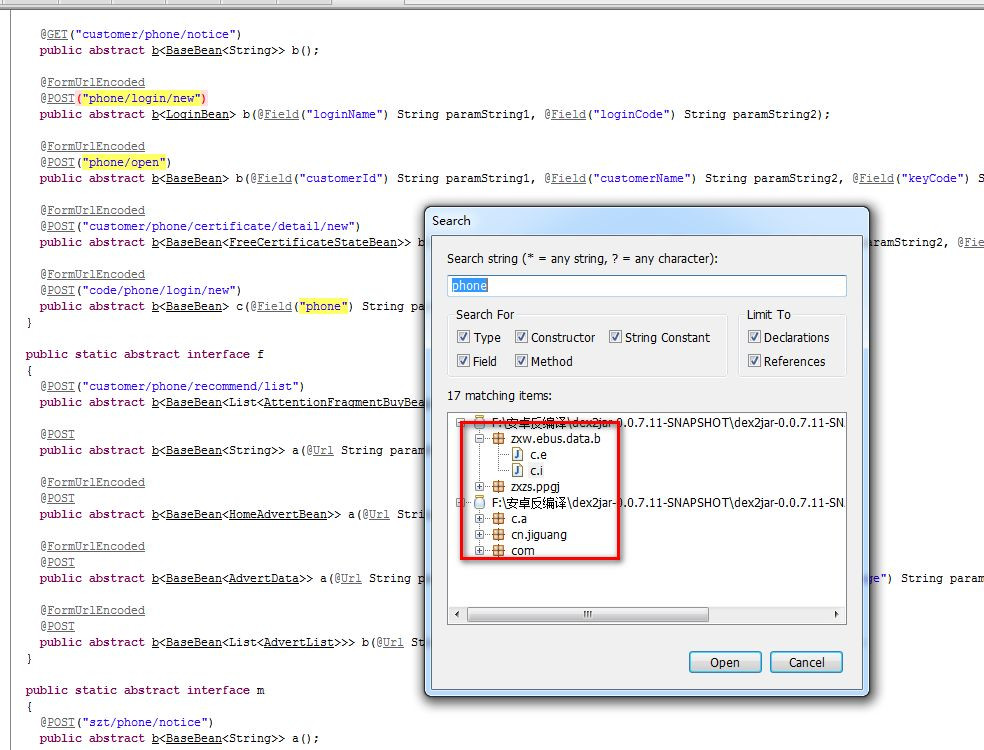
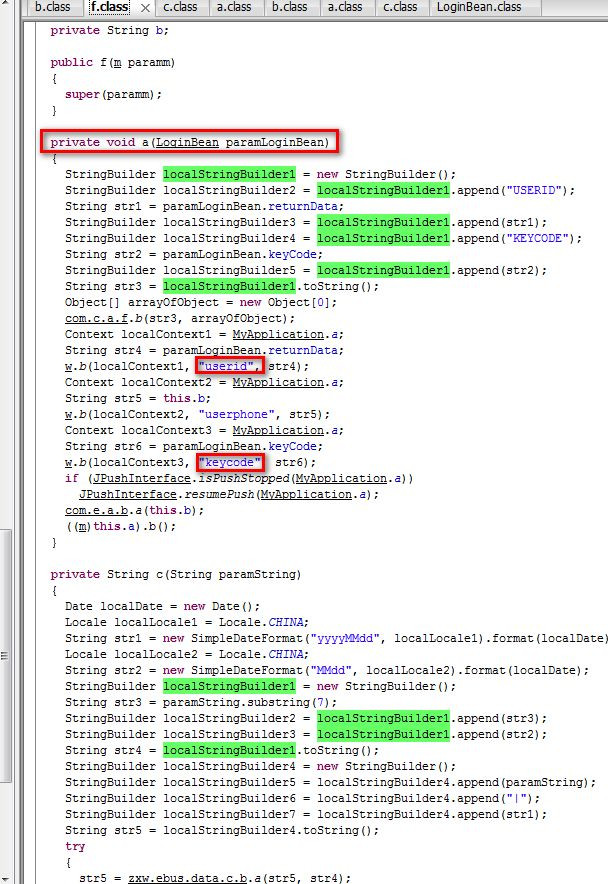
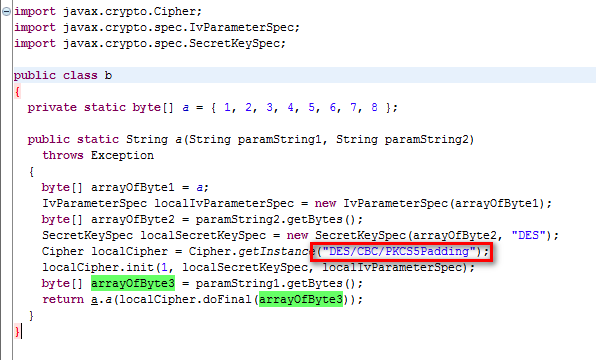
验证我们把源码拷贝出来,分析加密参数
private String c(String paramString)
{
Date localDate = new Date();
Locale localLocale1 = Locale.CHINA;
String str1 = new SimpleDateFormat("yyyyMMdd", localLocale1).format(localDate);
Locale localLocale2 = Locale.CHINA;
String str2 = new SimpleDateFormat("MMdd", localLocale2).format(localDate);
StringBuilder localStringBuilder1 = new StringBuilder();
String str3 = paramString.substring(7);
StringBuilder localStringBuilder2 = localStringBuilder1.append(str3);
StringBuilder localStringBuilder3 = localStringBuilder1.append(str2);
String str4 = localStringBuilder1.toString();
StringBuilder localStringBuilder4 = new StringBuilder();
StringBuilder localStringBuilder5 = localStringBuilder4.append(paramString);
StringBuilder localStringBuilder6 = localStringBuilder4.append("|");
StringBuilder localStringBuilder7 = localStringBuilder4.append(str1);
String str5 = localStringBuilder4.toString();
try
{
str5 = zxw.data.c.b.a(str5, str4);
}
catch (Exception localException)
{
localException.printStackTrace();
str5 = null;
}
return c.a(str5);
}
其中生成了两个参数 str5, str4 传到加密函数。
下面是 str5 的生成代码
String str1 = new SimpleDateFormat("yyyyMMdd", localLocale1).format(localDate);
StringBuilder localStringBuilder4 = new StringBuilder();
StringBuilder localStringBuilder5 = localStringBuilder4.append(paramString);
StringBuilder localStringBuilder6 = localStringBuilder4.append("|");
StringBuilder localStringBuilder7 = localStringBuilder4.append(str1);
String str5 = localStringBuilder4.toString();
str1 = 20190319,也就是今天的日期
str5 = 传过来的参数 + ‘|‘ + ‘20190319‘
那么 str4 呢
String str2 = new SimpleDateFormat("MMdd", localLocale2).format(localDate);
StringBuilder localStringBuilder1 = new StringBuilder();
String str3 = paramString.substring(7);
StringBuilder localStringBuilder2 = localStringBuilder1.append(str3);
StringBuilder localStringBuilder3 = localStringBuilder1.append(str2);
String str4 = localStringBuilder1.toString();
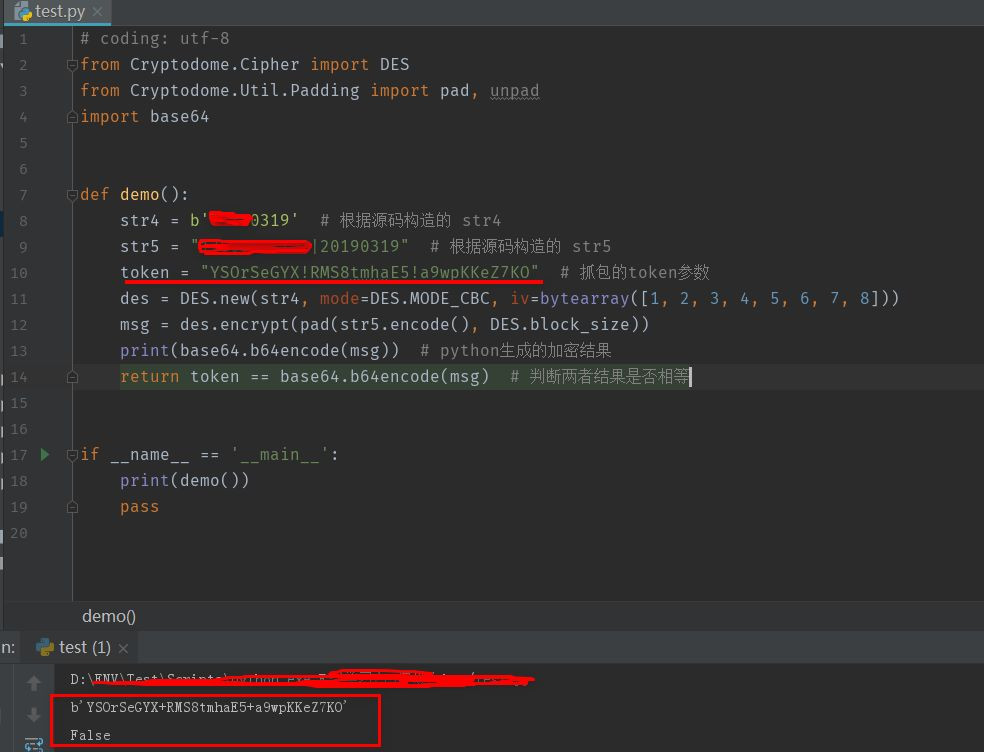
return c.a(str5);
public class c
{
public static String a(String paramString)
{
return paramString.replaceAll("\\+", "!");
}
}
总结
标签:static substring end 简单 为我 响应 null ram 逆向
原文地址:https://www.cnblogs.com/heimaguangzhou/p/11572323.html