标签:optional nbsp 修改 settings csr OWIN targe most lazy
在Linux下如何根据域名自签发各种SSL证书,这里我们以Apache、Tomcat、Nginx为例。
首先要有openssl工具,如果没有那么使用如下命令安装:
yum install -y openssl openssl-devel
具体修改如下
1 [root@docker02 ~]# vim /etc/pki/tls/openssl.cnf 2 [ req ] 3 ……………… 4 # 将如下配置的注释放开 5 req_extensions = v3_req # The extensions to add to a certificate request 6 ……………… 7 [ v3_req ] 8 9 # Extensions to add to a certificate request 10 11 basicConstraints = CA:FALSE 12 keyUsage = nonRepudiation, digitalSignature, keyEncipherment 13 # 添加如下行 14 subjectAltName = @SubjectAlternativeName 15 16 # 同时增加如下信息 17 [SubjectAlternativeName] 18 DNS.1 = zhangbook.com 19 DNS.2 = *.zhangbook.com
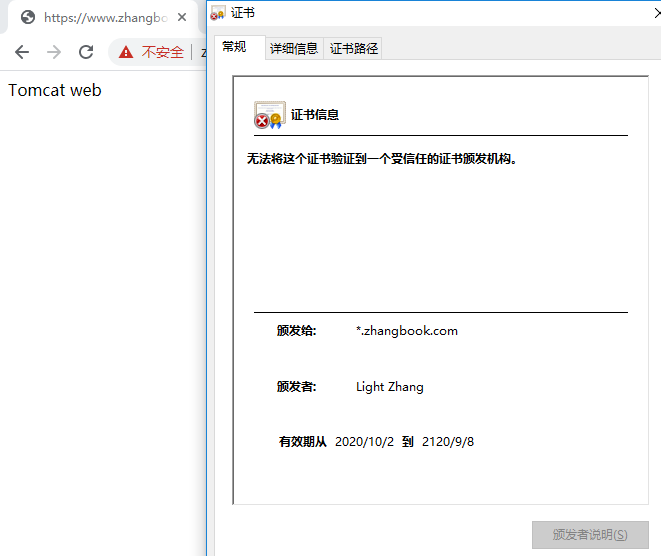
说明:本次我们以 *.zhangbook.com 泛域名为例。
1 [root@docker02 ssl]# pwd 2 /root/software/ssl 3 [root@docker02 ssl]# 4 ## 创建CA私钥 5 [root@docker02 ssl]# openssl genrsa -out CA.key 2048 6 ## 制作CA公钥 7 [root@docker02 ssl]# openssl req -sha256 -new -x509 -days 36500 -key CA.key -out CA.crt -config /etc/pki/tls/openssl.cnf 8 ……………… 9 Country Name (2 letter code) [XX]:CN 10 State or Province Name (full name) []:BJ 11 Locality Name (eg, city) [Default City]:BeiJing 12 Organization Name (eg, company) [Default Company Ltd]:BTC 13 Organizational Unit Name (eg, section) []:MOST 14 Common Name (eg, your name or your server‘s hostname) []:Light Zhang # 这里就是证书上的:颁发者 15 Email Address []:ca@test.com
当然上述的公钥制作方式需要交互式输入信息,如果不想频繁输入,那么可以使用如下命令:
1 ## 免交互式制作CA公钥 2 openssl req -sha256 -new -x509 -days 36500 -key CA.key -out CA.crt -config /etc/pki/tls/openssl.cnf -subj "/C=CN/ST=BJ/L=BeiJing/O=BTC/OU=MOST/CN=Light Zhang/emailAddress=ca@test.com"
subj内容详解:
1 C = Country Name (2 letter code) 2 ST = State or Province Name (full name) 3 L = Locality Name (eg, city) [Default City] 4 O = Organization Name (eg, company) [Default Company Ltd] 5 OU = Organizational Unit Name (eg, section) 6 CN = Common Name (eg, your name or your server‘s hostname) 7 emailAddress = Email Address
此时的的文件有:
1 [root@docker02 ssl]# ll 2 total 32 3 -rw-r--r-- 1 root root 1387 Oct 2 10:25 CA.crt 4 -rw-r--r-- 1 root root 1679 Oct 2 10:04 CA.key
操作步骤为:
具体如下:
1 ### 当前目录 /root/software/ssl 2 # 生成 zhangbook.com.key 密钥 3 openssl genrsa -out zhangbook.com.key 2048 4 # 生成 zhangbook.com.csr 证书签发请求 交互式 5 openssl req -new -sha256 -key zhangbook.com.key -out zhangbook.com.csr -config /etc/pki/tls/openssl.cnf 6 ……………… 7 ##### 产生的交互式内容与填写如下 8 Country Name (2 letter code) [XX]:CN 9 State or Province Name (full name) []:BJ 10 Locality Name (eg, city) [Default City]:BeiJing 11 Organization Name (eg, company) [Default Company Ltd]:BTC 12 Organizational Unit Name (eg, section) []:MOST 13 Common Name (eg, your name or your server‘s hostname) []:*.zhangbook.com # 这里就是证书上的:颁发给 14 Email Address []:ca@test.com 15 16 Please enter the following ‘extra‘ attributes 17 to be sent with your certificate request 18 A challenge password []:123456 19 An optional company name []:BTC 20 ……………… 21 # 生成 zhangbook.com.csr 证书签发请求 非交互式 22 openssl req -new -sha256 -key zhangbook.com.key -out zhangbook.com.csr -config /etc/pki/tls/openssl.cnf -subj "/C=CN/ST=BJ/L=BeiJing/O=BTC/OU=MOST/CN=*.zhangbook.com/emailAddress=ca@test.com"
PS1:上面的Common Name 就是在这步填写 *.zhangbook.com ,表示的就是该证书支持泛域名,common name一定要在SubjectAlternativeName中包含
PS2:进行CA签名获取证书时,需要注意国家、省、单位需要与CA证书相同,否则会报异常
查看签名请求文件信息
openssl req -in zhangbook.com.csr -text
使用自签署的CA,签署zhangbook.com.crt
openssl ca -in zhangbook.com.csr -md sha256 -days 36500 -out zhangbook.com.crt -cert CA.crt -keyfile CA.key -extensions v3_req -config /etc/pki/tls/openssl.cnf
这里证书有效时间为100年。
PS1:即便是你前面是sha256的根证书和sha256的请求文件,如果这里不加 -md sha256,那么默认是按照sha1进行签名的
PS2:在执行时,可能出现如下错误
异常问题1:
1 Using configuration from /etc/pki/tls/openssl.cnf 2 /etc/pki/CA/index.txt: No such file or directory 3 unable to open ‘/etc/pki/CA/index.txt‘ 4 140652962035600:error:02001002:system library:fopen:No such file or directory:bss_file.c:402:fopen(‘/etc/pki/CA/index.txt‘,‘r‘) 5 140652962035600:error:20074002:BIO routines:FILE_CTRL:system lib:bss_file.c:404:
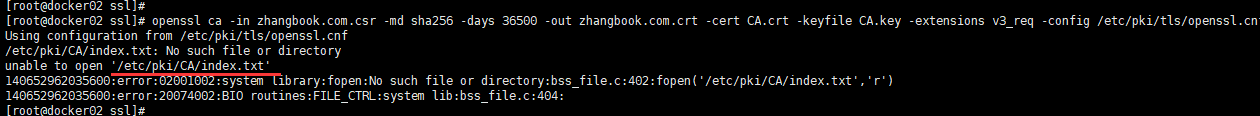
处理:这时我们创建该文件即可
touch /etc/pki/CA/index.txt
异常问题2:
然后我们继续使用 【自签署的CA,签署zhangbook.com.crt】;结果又出现新问题
1 Using configuration from /etc/pki/tls/openssl.cnf 2 /etc/pki/CA/serial: No such file or directory 3 error while loading serial number 4 140087163742096:error:02001002:system library:fopen:No such file or directory:bss_file.c:402:fopen(‘/etc/pki/CA/serial‘,‘r‘) 5 140087163742096:error:20074002:BIO routines:FILE_CTRL:system lib:bss_file.c:404:
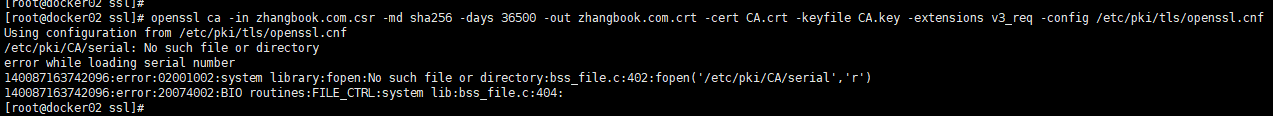
处理:使用如下命令即可。表示:用来跟踪最后一次颁发证书的序列号。
echo "01" > /etc/pki/CA/serial
之后我们再次执行 【自签署的CA,签署zhangbook.com.crt 】 就正常了。详情如下:
1 [root@docker02 ssl]# openssl ca -in zhangbook.com.csr -md sha256 -days 36500 -out zhangbook.com.crt -cert CA.crt -keyfile CA.key -extensions v3_req -config /etc/pki/tls/openssl.cnf 2 Using configuration from /etc/pki/tls/openssl.cnf 3 Check that the request matches the signature 4 Signature ok 5 Certificate Details: 6 Serial Number: 1 (0x1) 7 Validity 8 Not Before: Oct 2 03:42:39 2020 GMT 9 Not After : Sep 8 03:42:39 2120 GMT 10 Subject: 11 countryName = CN 12 stateOrProvinceName = BJ 13 organizationName = BTC 14 organizationalUnitName = MOST 15 commonName = *.zhangbook.com 16 emailAddress = ca@test.com 17 X509v3 extensions: 18 X509v3 Basic Constraints: 19 CA:FALSE 20 X509v3 Key Usage: 21 Digital Signature, Non Repudiation, Key Encipherment 22 X509v3 Subject Alternative Name: 23 DNS:zhangbook.com, DNS:*.zhangbook.com 24 Certificate is to be certified until Sep 8 03:42:39 2120 GMT (36500 days) 25 Sign the certificate? [y/n]:y <== 需要输入的 26 27 28 1 out of 1 certificate requests certified, commit? [y/n]y <== 需要输入的 29 Write out database with 1 new entries 30 Data Base Updated
说明:此时我们再看,/etc/pki/CA/index.txt 和 /etc/pki/CA/serial 文件信息。如下:
1 [root@docker02 ~]# cat /etc/pki/CA/index.txt 2 V 21200908034239Z 01 unknown /C=CN/ST=BJ/O=BTC/OU=MOST/CN=*.zhangbook.com/emailAddress=ca@test.com 3 [root@docker02 ~]# 4 [root@docker02 ~]# cat /etc/pki/CA/serial 5 02
由上可知:域名签署信息已经保存到index.txt文件;并且证书序列serial文件已经更新【从01变为了02】。
PS:
*.zhangbook.com,且已经被记录,因此不能再次被签署。除非删除该记录。查看证书信息
openssl x509 -in zhangbook.com.crt -text
验证签发证书是否有效
1 [root@docker02 ssl]# openssl verify -CAfile CA.crt zhangbook.com.crt 2 zhangbook.com.crt: OK
此时的文件有:
1 [root@docker02 ssl]# ll 2 total 32 3 -rw-r--r-- 1 root root 1387 Oct 2 10:25 CA.crt 4 -rw-r--r-- 1 root root 1679 Oct 2 10:04 CA.key 5 -rw-r--r-- 1 root root 4364 Oct 2 11:42 zhangbook.com.crt 6 -rw-r--r-- 1 root root 1151 Oct 2 10:48 zhangbook.com.csr 7 -rw-r--r-- 1 root root 1679 Oct 2 10:44 zhangbook.com.key
此时我们已经完成自签发证书。
实际工作和生产环境中,可能需要各种各样的证书格式。下面我们将证书转换为常用的其他证书格式。
命令如下:
openssl x509 -in zhangbook.com.crt -out zhangbook.com.pem -outform PEM
利用生成的CA根证书和服务证书的crt 和 key 文件生成 p12 文件
openssl pkcs12 -export -in zhangbook.com.crt -inkey zhangbook.com.key -passin pass:CS2i1QkR -name *.zhangbook.com -chain -CAfile CA.crt -password pass:CS2i1QkR -caname *.zhangbook.com -out zhangbook.com.p12
PS:p12证书的password为CS2i1QkR
查看p12证书信息【keytool命令依赖于Java,因此需要先安装Java】
1 [root@docker02 ssl]# keytool -rfc -list -keystore zhangbook.com.p12 -storetype pkcs12 2 Enter keystore password: <== 输入:CS2i1QkR 3 Keystore type: PKCS12 4 Keystore provider: SunJSSE 5 6 Your keystore contains 1 entry 7 ………………
使用jdk keytool工具进而生成tomcat/jboss端使用的证书文件【需要安装 Java】。
具体如下:
1 [root@docker02 ssl]# keytool -importkeystore -srckeystore zhangbook.com.p12 -srcstoretype PKCS12 -deststoretype JKS -destkeystore zhangbook.com.jks 2 Importing keystore zhangbook.com.p12 to zhangbook.com.jks... 3 Enter destination keystore password: <== 输入 jks 证书的密码,如:CS2i1QkR 4 Re-enter new password: <== 重复输入 jks 证书的密码,如:CS2i1QkR 5 Enter source keystore password: <== 输入 p12 证书的密码,这里是:CS2i1QkR 6 Entry for alias *.zhangbook.com successfully imported. 7 Import command completed: 1 entries successfully imported, 0 entries failed or cancelled 8 9 Warning: 10 The JKS keystore uses a proprietary format. It is recommended to migrate to PKCS12 which is an industry standard format using "keytool -importkeystore -srckeystore zhangbook.com.jks -destkeystore zhangbook.com.jks -deststoretype pkcs12".
PS:p12证书和jks证书的密码相同,防止出现各种异常情况。
具体如下
keytool -export -alias *.zhangbook.com -keystore zhangbook.com.jks -storepass CS2i1QkR -file zhangbook.com.cer
-storepass CS2i1QkR 为jks证书密码
具体如下
keytool -import -alias *.zhangbook.com -keystore cacerts -file zhangbook.com.cer
1 [root@docker02 ssl]# pwd 2 /root/software/ssl 3 [root@docker02 ssl]# 4 [root@docker02 ssl]# ll 5 total 52 6 -rw-r--r-- 1 root root 1018 Oct 2 14:24 cacerts ## jdk 所使用的文件 7 -rw-r--r-- 1 root root 1387 Oct 2 10:25 CA.crt ## CA公钥 8 -rw-r--r-- 1 root root 1679 Oct 2 10:04 CA.key ## CA私钥 9 -rw-r--r-- 1 root root 946 Oct 2 14:21 zhangbook.com.cer ## cer证书 10 -rw-r--r-- 1 root root 4364 Oct 2 11:42 zhangbook.com.crt ## zhangbook.com域名 CA签发公钥 11 -rw-r--r-- 1 root root 1151 Oct 2 10:48 zhangbook.com.csr ## zhangbook.com域名 证书签发请求 12 -rw-r--r-- 1 root root 3303 Oct 2 14:13 zhangbook.com.jks ## jks证书 13 -rw-r--r-- 1 root root 1679 Oct 2 10:44 zhangbook.com.key ## zhangbook.com域名 私钥 14 -rw-r--r-- 1 root root 3716 Oct 2 14:02 zhangbook.com.p12 ## p12格式证书 15 -rw-r--r-- 1 root root 1338 Oct 2 13:56 zhangbook.com.pem ## zhangbook.com域名 PEM文件
修改本地Windows的hosts文件,用于域名解析
1 文件位置:C:\WINDOWS\System32\drivers\etc\hosts 追加如下信息 2 # zhangbook.com 3 172.16.1.32 www.zhangbook.com blog.zhangbook.com auth.zhangbook.com
其中172.16.1.32为测试使用的Linux机器,后面会部署WEB服务。由于自签发的是泛域名证书,因此可以有多个二级域名。
后面访问的时候,既可以使用域名访问,也可以使用IP访问。【推荐】使用域名访问。
1、将Apache httpd用到的证书拷贝到指定目录
1 [root@docker02 ssl]# pwd 2 /root/software/ssl 3 [root@docker02 ssl]# 4 [root@docker02 ssl]# cp -a zhangbook.com.crt zhangbook.com.key zhangbook.com.pem /etc/pki/tls/certs
2、在Linux机器安装httpd服务并添加ssl插件
1 yum install -y httpd 2 yum install -y mod_ssl openssl # 执行后,会增加 /etc/httpd/conf.d/ssl.conf 文件
3、在httpd添加SSL配置
1 [root@docker02 conf.d]# pwd 2 /etc/httpd/conf.d 3 [root@docker02 conf.d]# 4 [root@docker02 conf.d]# vim ssl.conf 5 <VirtualHost _default_:443> 6 # General setup for the virtual host, inherited from global configuration 7 #DocumentRoot "/var/www/html" 8 ……………… 9 # 修改如下3行 10 SSLCertificateFile /etc/pki/tls/certs/zhangbook.com.crt 11 SSLCertificateKeyFile /etc/pki/tls/certs/zhangbook.com.key 12 # 如下行可以注释掉,也可以取消注释 13 #SSLCertificateChainFile /etc/pki/tls/certs/zhangbook.com.pem 14 ……………… 15 </VirtualHost>
4、向VirtualHost的默认目录添加文件
echo "Apache web" > /var/www/html/index.html
5、启动httpd服务
systemctl start httpd
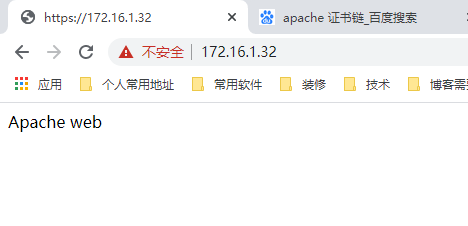
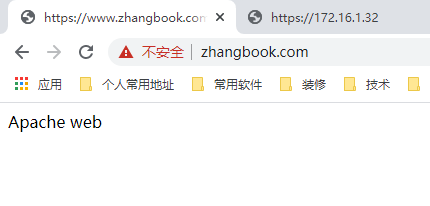
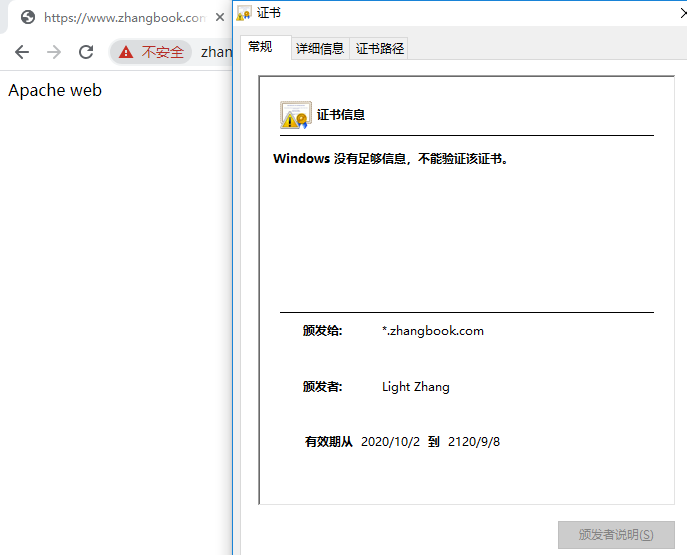
6、浏览器访问
1 https://172.16.1.32/ 2 https://www.zhangbook.com/ 3 https://blog.zhangbook.com 4 https://auth.zhangbook.com
7、验证完毕,停止httpd服务
systemctl stop httpd
1、在Linux机器安装nginx服务
yum install -y nginx
通过 nginx -V 可见,--with-http_ssl_module 已安装。
2、将nginx用到的证书拷贝到指定目录
1 [root@docker02 ssl]# pwd 2 /root/software/ssl 3 [root@docker02 ssl]# 4 [root@docker02 ssl]# cp -a zhangbook.com.key zhangbook.com.crt /etc/nginx/cert
3、在nginx添加SSL配置
1 [root@docker02 nginx]# pwd 2 /etc/nginx 3 [root@docker02 nginx]# 4 [root@docker02 nginx]# vim nginx.conf 5 ……………… 6 server { 7 listen 80; 8 listen [::]:80; 9 server_name www.zhangbook.com blog.zhangbook.com auth.zhangbook.com; 10 return 301 https://$server_name$request_uri; 11 } 12 13 # Settings for a TLS enabled server. 14 server { 15 listen 443 ssl http2 default_server; 16 listen [::]:443 ssl http2 default_server; 17 server_name www.zhangbook.com blog.zhangbook.com auth.zhangbook.com; 18 root /usr/share/nginx/html; 19 20 ssl_certificate "/etc/nginx/cert/zhangbook.com.crt"; 21 ssl_certificate_key "/etc/nginx/cert/zhangbook.com.key"; 22 ssl_session_cache shared:SSL:1m; 23 ssl_session_timeout 10m; 24 ssl_ciphers HIGH:!aNULL:!MD5; 25 ssl_prefer_server_ciphers on; 26 27 # Load configuration files for the default server block. 28 include /etc/nginx/default.d/*.conf; 29 30 location / { 31 index index.html index.htm; 32 } 33 } 34 ………………
4、向WEB站点添加html文件
echo "Nginx web" > /usr/share/nginx/html/index.html
5、启动nginx服务
systemctl start nginx.service
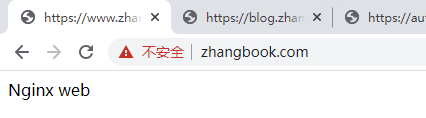
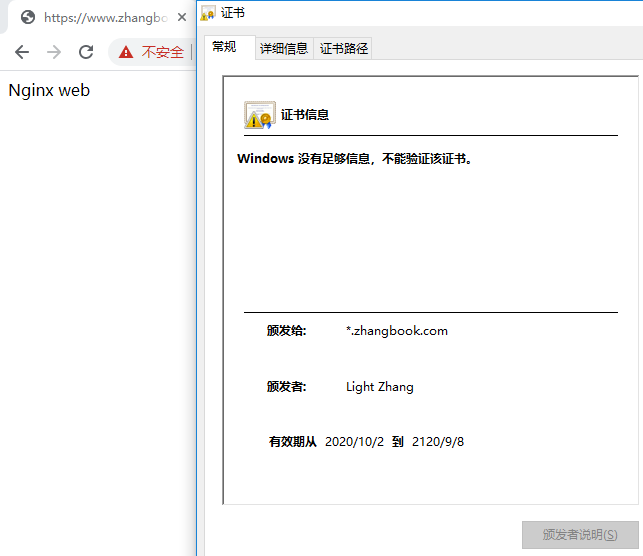
6、浏览器访问
1 https://www.zhangbook.com/ 2 https://blog.zhangbook.com 3 https://auth.zhangbook.com
7、验证完毕,停止nginx服务
systemctl stop nginx
1、下载Tomcat。
1 [root@docker02 App]# pwd 2 /root/App 3 [root@docker02 App]# 4 [root@docker02 App]# wget https://mirrors.bfsu.edu.cn/apache/tomcat/tomcat-8/v8.5.58/bin/apache-tomcat-8.5.58.tar.gz 5 [root@docker02 App]# 6 [root@docker02 App]# tar xf apache-tomcat-8.5.58.tar.gz 7 ### 查看Java版本信息 8 [root@docker02 App]# java -version 9 java version "1.8.0_231" 10 Java(TM) SE Runtime Environment (build 1.8.0_231-b11) 11 Java HotSpot(TM) 64-Bit Server VM (build 25.231-b11, mixed mode) 12 ### 查看Tomcat版本信息 13 [root@docker02 bin]# pwd 14 /root/App/apache-tomcat-8.5.58/bin 15 [root@docker02 bin]# 16 [root@docker02 bin]# ./version.sh 17 ………………
2、将Tomcat用到的证书拷贝到指定目录
1 [root@docker02 ssl]# pwd 2 /root/software/ssl 3 [root@docker02 ssl]# 4 [root@docker02 ssl]# cp -a zhangbook.com.jks /root/App/apache-tomcat-8.5.58/conf/cert/
3、在Tomcat添加SSL配置
1 [root@docker02 conf]# pwd 2 /root/App/apache-tomcat-8.5.58/conf 3 [root@docker02 conf]# 4 [root@docker02 conf]# vim server.xml 5 ……………… 6 <Connector port="80" protocol="HTTP/1.1" 7 connectionTimeout="20000" 8 redirectPort="443" /> 9 ……………… 10 ### 其中Connector标签中的子标签 SSLHostConfig 已去掉 11 <Connector port="443" protocol="org.apache.coyote.http11.Http11NioProtocol" 12 maxThreads="600" SSLEnabled="true" clientAuth="false" keystoreFile="/root/App/apache-tomcat-8.5.58/conf/cert/zhangbook.com.jks" 13 keystorePass="CS2i1QkR" keystoreType="JKS" scheme="https" secure="true" 14 sslProtocol="TLS" compression="on" acceptorThreadCount="2" connectionTimeout="20000"> 15 </Connector> 16 ………………
4、向WEB站点添加html文件
1 [root@docker02 ROOT]# pwd 2 /root/App/apache-tomcat-8.5.58/webapps/ROOT 3 [root@docker02 ROOT]# 4 [root@docker02 ROOT]# echo ‘Tomcat web‘ > index.html
PS:原ROOT目录下的文件已移走。
5、启动Tomcat服务
1 [root@docker02 bin]# pwd 2 /root/App/apache-tomcat-8.5.58/bin 3 [root@docker02 bin]# 4 [root@docker02 bin]# sh startup.sh
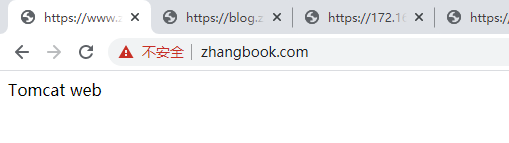
6、浏览器访问
1 https://172.16.1.32/ 2 https://www.zhangbook.com/ 3 https://blog.zhangbook.com 4 https://auth.zhangbook.com
7、验证完毕,停止Tomcat服务
1 [root@docker02 bin]# pwd 2 /root/App/apache-tomcat-8.5.58/bin 3 [root@docker02 bin]# 4 [root@docker02 bin]# sh shutdown.sh
———END———
如果觉得不错就关注下呗 (-^O^-) !
在Linux下如何根据域名自签发OpenSSL证书与常用证书转换
标签:optional nbsp 修改 settings csr OWIN targe most lazy
原文地址:https://www.cnblogs.com/zhanglianghhh/p/13800490.html