标签:tst console wstring define 哈哈 time() jnienv indexof unsigned
安卓逆向脱壳实操app
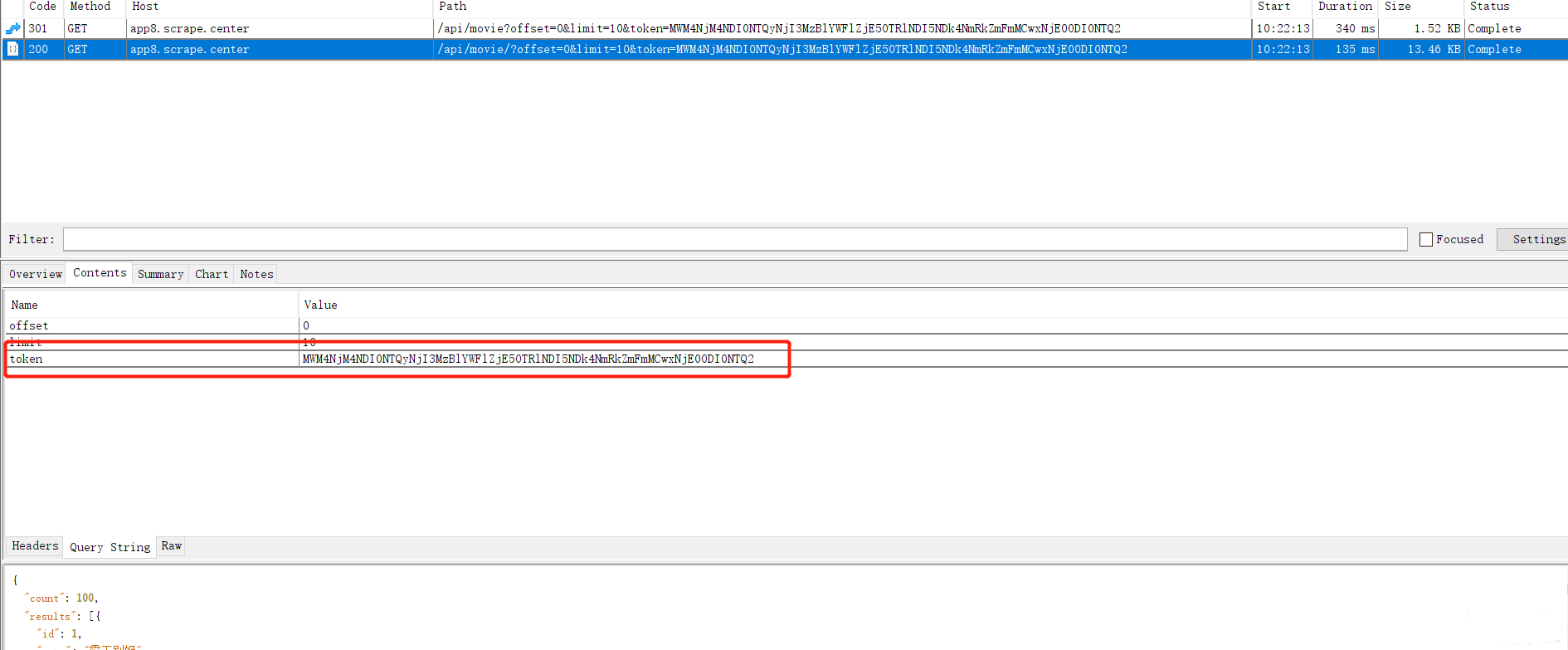
抓包如图所示
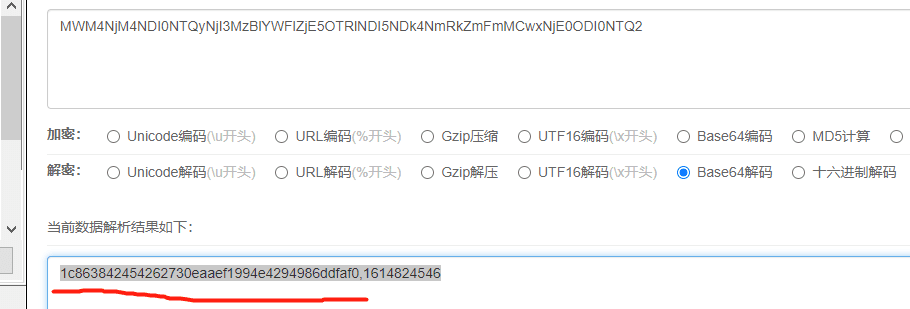
base解码
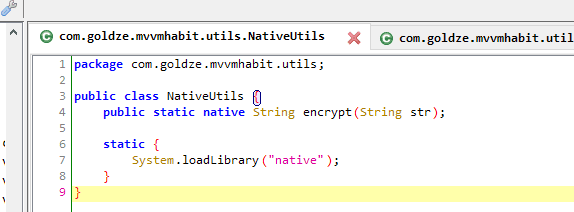
经过定位确定在这儿
jadx
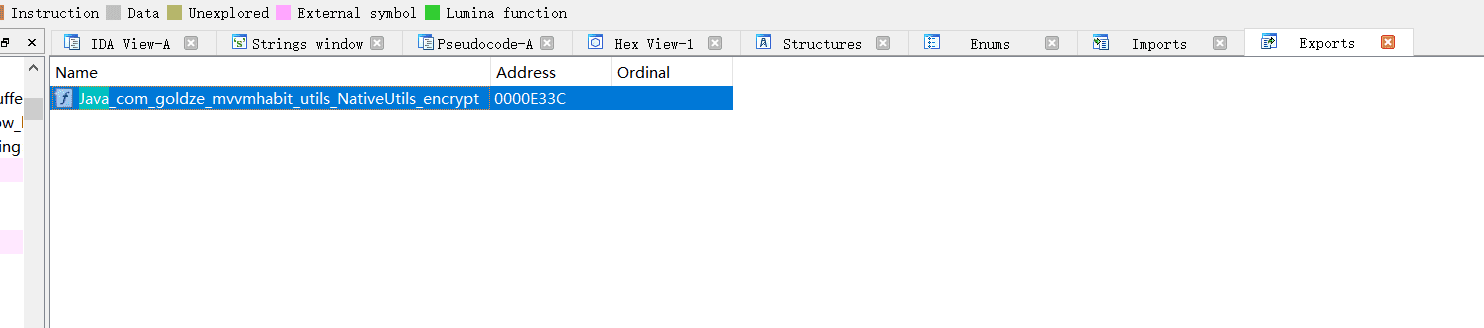
ida中直接有导出函数
jstring __fastcall Java_com_goldze_mvvmhabit_utils_NativeUtils_encrypt(JNIEnv *a1, int a2, int a3)
{
char *v4; // r0
int v5; // r0
const char *v6; // r1
jstring v7; // r4
char v9[12]; // [sp+4h] [bp-74h] BYREF
unsigned __int8 v10; // [sp+10h] [bp-68h] BYREF
_BYTE v11[11]; // [sp+11h] [bp-67h] BYREF
char v12[12]; // [sp+1Ch] [bp-5Ch] BYREF
_DWORD v13[3]; // [sp+28h] [bp-50h] BYREF
char v14[12]; // [sp+34h] [bp-44h] BYREF
char v15[12]; // [sp+40h] [bp-38h] BYREF
char v16[12]; // [sp+4Ch] [bp-2Ch] BYREF
_DWORD v17[3]; // [sp+58h] [bp-20h] BYREF
v17[2] = 0;
v17[0] = 0;
v17[1] = 0;
v4 = (*a1)->GetStringUTFChars(a1, a3, 0);
std::string::basic_string<decltype(nullptr)>(v16, v4);
sub_E490(v17);
std::string::~string(v16);
v5 = time(0); // 时间戳
std::to_string(v16, v5);
sub_E4A0(v17);
join(v14, v17, 44);
sha1(v15, v14); // 初步看sha1加密
std::string::~string(v14);
v13[2] = 0;
v13[0] = 0;
v13[1] = 0;
sub_E4A0(v13);
sub_E4A0(v13);
join(v12, v13, 44);
std::string::basic_string(v9, v12);
b64encode(&v10, v9); //重点特征
std::string::~string(v9);
v6 = *&v11[7];
if ( !(v10 << 31) )
v6 = v11;
v7 = (*a1)->NewStringUTF(a1, v6);
std::string::~string(&v10);
std::string::~string(v12);
std::__vector_base<std::string>::~__vector_base(v13);
std::string::~string(v15);
std::string::~string(v16);
std::__vector_base<std::string>::~__vector_base(v17);
return v7;
}
只需要知道一点点sha1加密
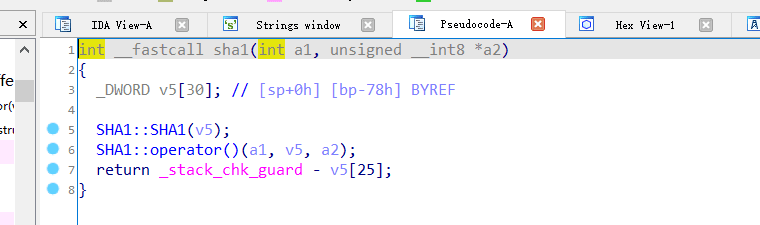
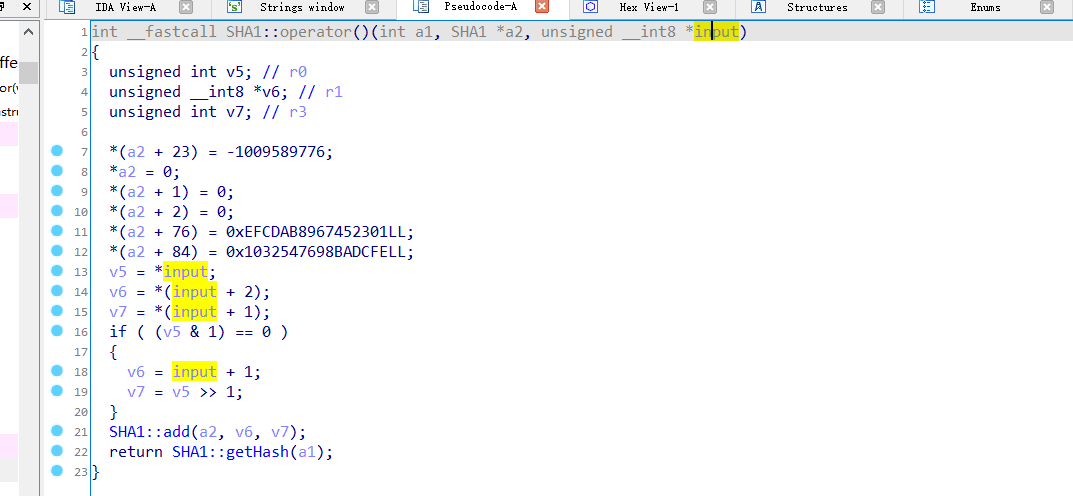
// sha1原型参考, 核心就是和md5差不多, hash算法,没有key。 多余的信息自行查看 https://en.wikipedia.org/wiki/SHA-1
int SHA1_Update(SHA_CTX *c, const void *data,
unsigned long len);
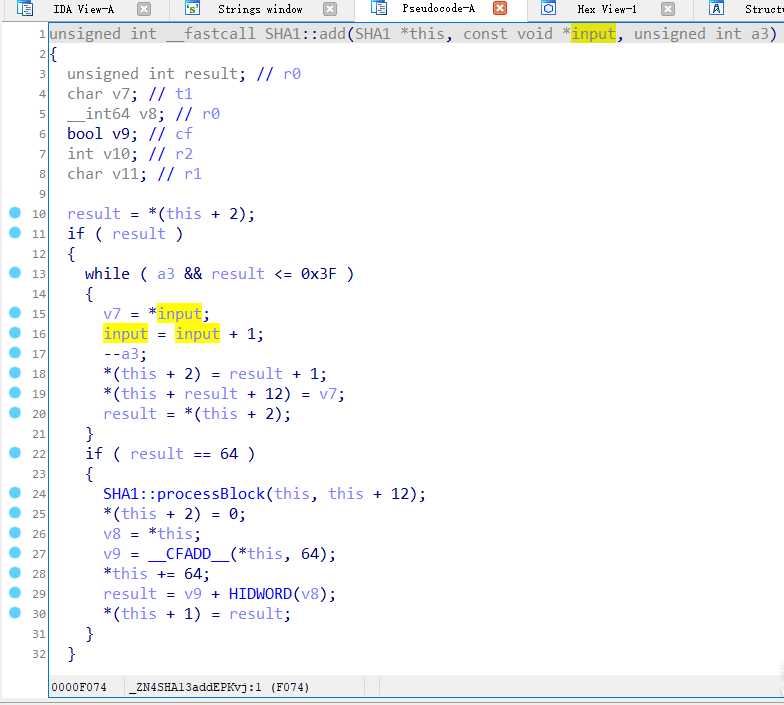
// 猜测对应位置 SHA1::add(a2, v6, v7);
上frida脚本测试下看看
// 这是一个写好的完整脚本, 需要会frida姿势哟。
function hookjava(){
Java.perform(function(){
var encrypt = Java.use("com.goldze.mvvmhabit.utils.NativeUtils").encrypt;
encrypt.implementation = function(str){
console.log("java input:" + str)
var ret = this.encrypt(str);
console.log("java output:" + ret);
return ret;
}
})
}
function hook(){
var base = Module.findBaseAddress(lib_so);
// SHA1::add
var offset = base.add(0xF075);
Interceptor.attach(offset, {
onEnter:function(args){
console.log("native:"+ Memory.readCString(args[1]))
}
}
)
}
var lib_so = "libnative.so"
var is_hook_libart = false;
function main(){
Interceptor.attach(Module.findExportByName(null, "dlopen"), {
onEnter: function (args) {
var pathptr = args[0];
if (pathptr !== undefined && pathptr != null) {
var path = ptr(pathptr).readCString();
// console.log("dlopen:", path);
if (!this.path){
return
}
if (path.indexOf(lib_so) >= 0) {
this.can_hook_libart = true;
console.log("[dlopen:]", path);
}
}
},
onLeave: function (retval) {
if (this.can_hook_libart && !is_hook_libart) {
hook();
is_hook_libart = true;
}
}
})
Interceptor.attach(Module.findExportByName(null, "android_dlopen_ext"), {
onEnter: function (args) {
var pathptr = args[0];
if (pathptr !== undefined && pathptr != null) {
var path = ptr(pathptr).readCString();
// console.log("android_dlopen_ext:", path);
if (path.indexOf(lib_so) >= 0) {
this.can_hook_libart = true;
console.log("[android_dlopen_ext:]", path);
}
}
},
onLeave: function (retval) {
if (this.can_hook_libart && !is_hook_libart) {
hook();
is_hook_libart = true;
}
}
});
}
setImmediate(hookjava)
setImmediate(main)
前面分析过的, 返回是个base64, 重新解码看下
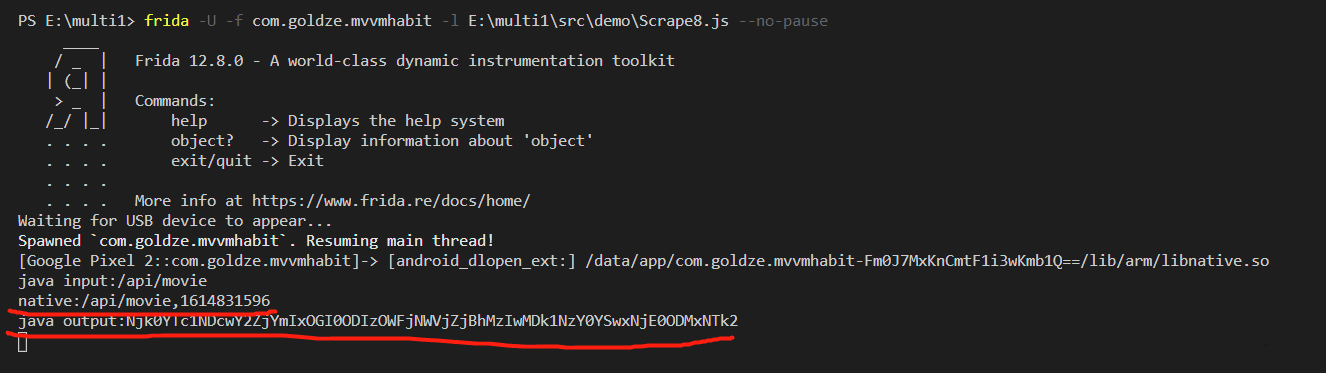
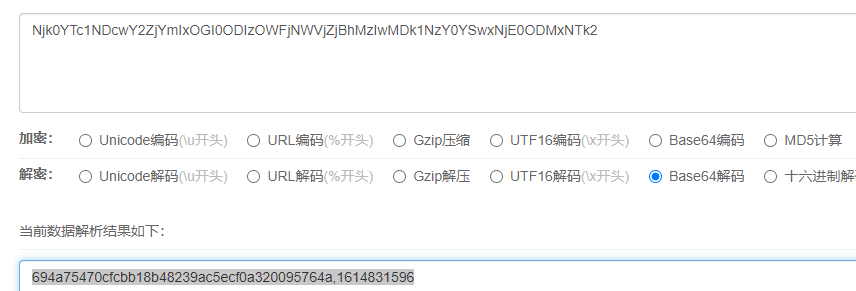

native:/api/movie,1614831596 重新sha1后结果与base64解开一样。
分析过程结束~~~
python脚本 完结傻花~~~
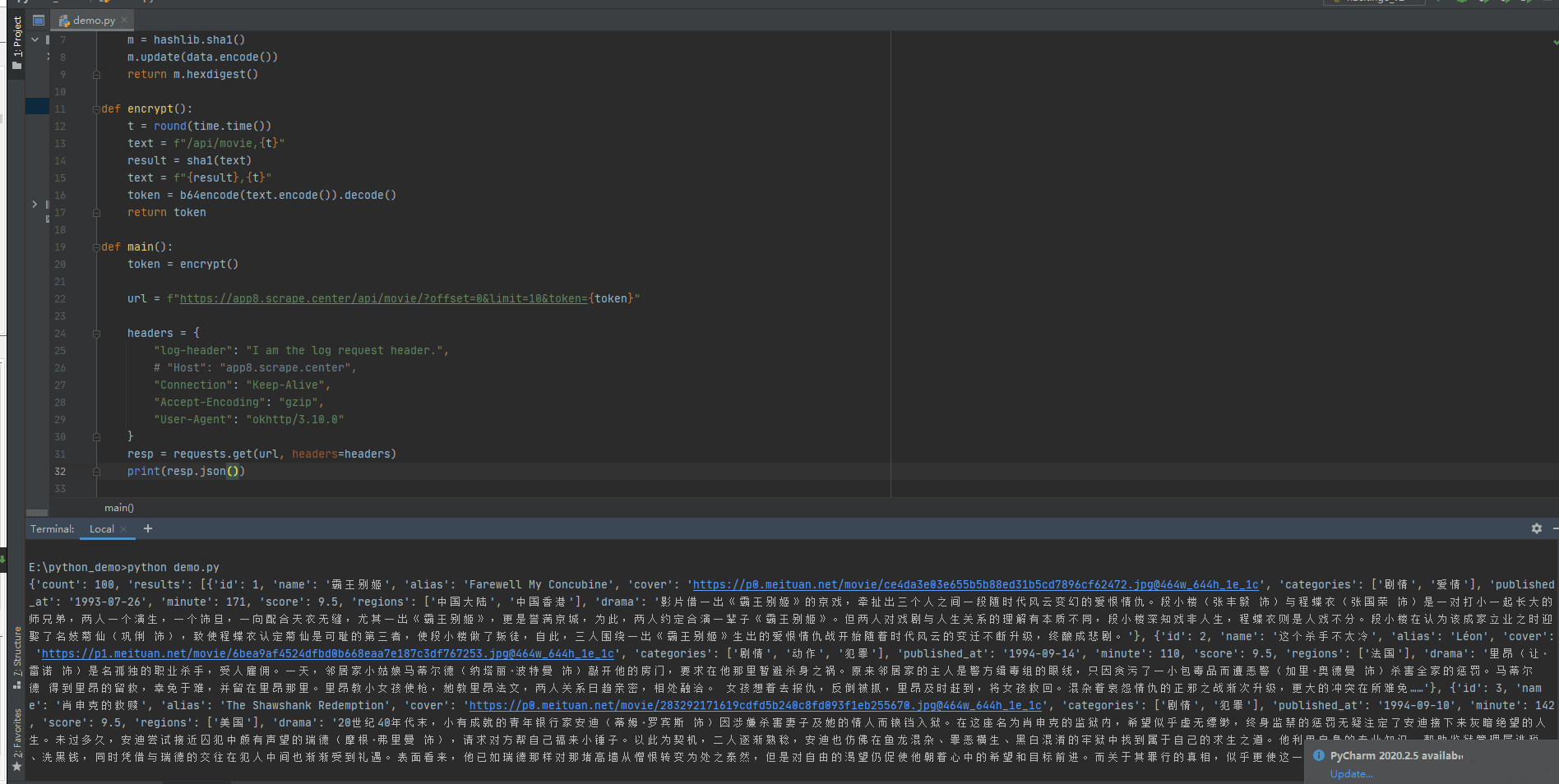
from base64 import b64encode
import hashlib
import time
import requests
def sha1(data):
m = hashlib.sha1()
m.update(data.encode())
return m.hexdigest()
def encrypt():
t = round(time.time())
text = f"/api/movie,{t}"
result = sha1(text)
text = f"{result},{t}"
token = b64encode(text.encode()).decode()
return token
def main():
token = encrypt()
url = f"https://app8.scrape.center/api/movie/?offset=0&limit=10&token={token}"
headers = {
"log-header": "I am the log request header.",
# "Host": "app8.scrape.center",
"Connection": "Keep-Alive",
"Accept-Encoding": "gzip",
"User-Agent": "okhttp/3.10.0"
}
resp = requests.get(url, headers=headers)
print(resp.json())
if __name__ == ‘__main__‘:
main()
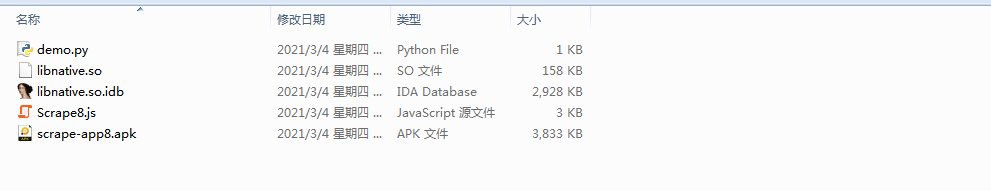
app和分析文件打包都在附件链接中 https://www.dslt.tech/article-96-1.html,欢迎下载交流学习,哈哈~~,更多逆向学习资料,可访问 大神论坛
版权声明:本文由 ogli324 原创,欢迎分享本文,转载请保留出处
标签:tst console wstring define 哈哈 time() jnienv indexof unsigned
原文地址:https://www.cnblogs.com/dslt/p/14491101.html