针对性扫描是指寻找目标网络中存在的已知可利用漏洞或能够轻松获取后门的特定操作系统、服务、软件以及配置缺陷。举例来说,在目标网络中快速地扫描存在MS08-067漏洞的主机是非常普遍的活动,因为MS08-067(仍然)是一个普遍存在的安全漏洞,并且能够让你很快地取得System的访问权限,比起扫描整个网络中所有漏洞后再攻击要容易的多。
1.服务器消息块协议扫描
Metasploit可以利用他的smb_version模块来遍历一个网络,并获取Windows系统的版本号
执行模块、列出参数并对RHOSTS参数进行设定后开始扫描:
msf > use scanner/smb/smb_version msf auxiliary(smb_version) > show options Module options (auxiliary/scanner/smb/smb_version): Name Current Setting Required Description ---- --------------- -------- ----------- RHOSTS yes The target address range or CIDR identifier SMBDomain WORKGROUP no The Windows domain to use for authentication SMBPass no The password for the specified username SMBUser no The username to authenticate as THREADS 1 yes The number of concurrent threads msf auxiliary(smb_version) > set RHOSTS 192.168.119.132 RHOSTS => 192.168.119.132 msf auxiliary(smb_version) > run [*] 192.168.119.132:139 is running Windows XP Service Pack 3 (language: Chinese - Traditional) (name:PC-201403241103) (domain:WORKGROUP) [*] Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed
2.搜索配置不当的Microsoft SQL Server
配置不当的Microsoft SQL Server(MS SQL)通常是竟如目标系统的第一个后门
MS SQL安装后,它默认监听在TCP端口1433上或使用随机的动态TCP端口。如果在随机的TCP端口上进行MS SQL监听,只需要简单的对UDP端口1434进行查询,便能或缺这个随机的TCP端口号。Metasploit有一个模块mssql_ping可以实现该操作
msf > use scanner/mssql/mssql_ping msf auxiliary(mssql_ping) > show options Module options (auxiliary/scanner/mssql/mssql_ping): Name Current Setting Required Description ---- --------------- -------- ----------- PASSWORD no The password for the specified username RHOSTS yes The target address range or CIDR identifier THREADS 1 yes The number of concurrent threads USERNAME sa no The username to authenticate as USE_WINDOWS_AUTHENT false yes Use windows authentification (requires DOMAIN option set) msf auxiliary(mssql_ping) > set RHOSTS 192.168.119.132 RHOSTS => 192.168.119.132 msf auxiliary(mssql_ping) > set THREADS 255 THREADS => 255 msf auxiliary(mssql_ping) > run [*] Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed
我安装的是SQL Server版本如下: Microsoft SQL Server Management Studio 9.00.1399.00 Microsoft Analysis Services 客户端工具 2005.090.1399.00 Microsoft 数据访问组件 (MDAC) 2000.085.1132.00 (xpsp.080413-0852) Microsoft MSXML 2.6 3.0 5.0 6.0 Microsoft Internet Explorer 8.0.6001.18702 Microsoft .NET Framework 2.0.50727.42 操作系统 5.1.2600
3.SSH服务器扫描
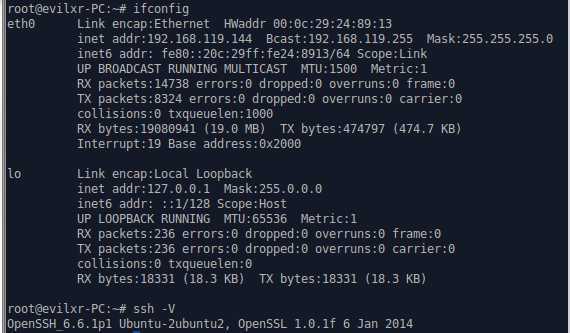
如果在扫描过程中遇到一些主机运行着SSH(安全 Shell),你应该对SSH的版本进行识别SSH是一种安全的协议,但是这里的安全仅数据传输的加密,很多SSH的实现版本中均被发现了安全漏洞。不要认为你永远不会遇到一台没哟安装补丁的老机器,这种幸运的事很哟可能就会落在你的头上。可以用Metasploit框架的ssh_version模块来识别目标服务器上运行的SSH版本。
msf > use scanner/ssh/ssh_version msf auxiliary(ssh_version) > show options Module options (auxiliary/scanner/ssh/ssh_version): Name Current Setting Required Description ---- --------------- -------- ----------- RHOSTS yes The target address range or CIDR identifier RPORT 22 yes The target port THREADS 1 yes The number of concurrent threads TIMEOUT 30 yes Timeout for the SSH probe msf auxiliary(ssh_version) > set RHOSTS 192.168.119.144 RHOSTS => 192.168.119.144 msf auxiliary(ssh_version) > run [*] 192.168.119.144:22, SSH server version: SSH-2.0-OpenSSH_6.6.1p1 Ubuntu-2ubuntu2 [*] Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed msf auxiliary(ssh_version) >
4.FTP扫描
FTP是一种复杂且缺乏安全性的应用层协议,FTP服务器经常是进入一个目标网络最便捷的途径
msf auxiliary(anonymous) > use scanner/ftp/ftp_version msf auxiliary(ftp_version) > show options Module options (auxiliary/scanner/ftp/ftp_version): Name Current Setting Required Description ---- --------------- -------- ----------- FTPPASS mozilla@example.com no The password for the specified username FTPUSER anonymous no The username to authenticate as RHOSTS 192.168.119.141 yes The target address range or CIDR identifier RPORT 21 yes The target port THREADS 1 yes The number of concurrent threads msf auxiliary(ftp_version) > set RHOSTS 192.126.119.48 RHOSTS => 192.126.119.48 msf auxiliary(ftp_version) > run [*] 192.126.119.48:21 FTP Banner: ‘220 Microsoft FTP Service\x0d\x0a‘ [*] Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed
原文地址:http://www.cnblogs.com/evilxr/p/3840891.html