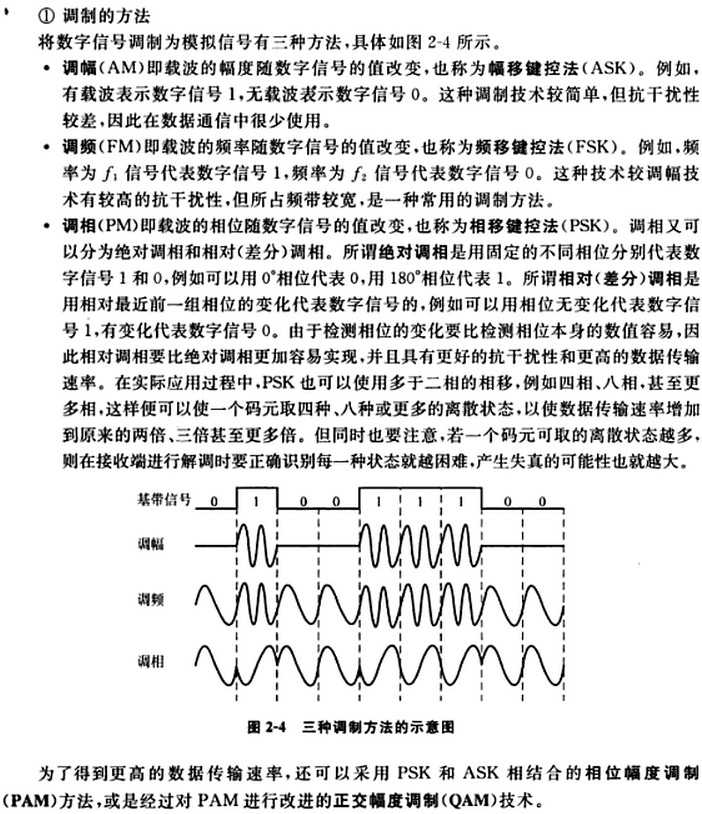
标签:

不同频段的RFID产品会有不同的特性,本文详细介绍了无源的感应器在不同工作频率产品的特性以及主要的应用。
目前定义RFID产品的工作频率有低频、高频和甚高频的频率范围内的符合不同标准的不同的产品,而且不同频段的RFID产品会有不同的特性。
其中感应器有无源和有源两种方式,下面详细介绍无源的感应器在不同工作频率产品的特性以及主要的应用。
1. 低频(从125KHz到134KHz)
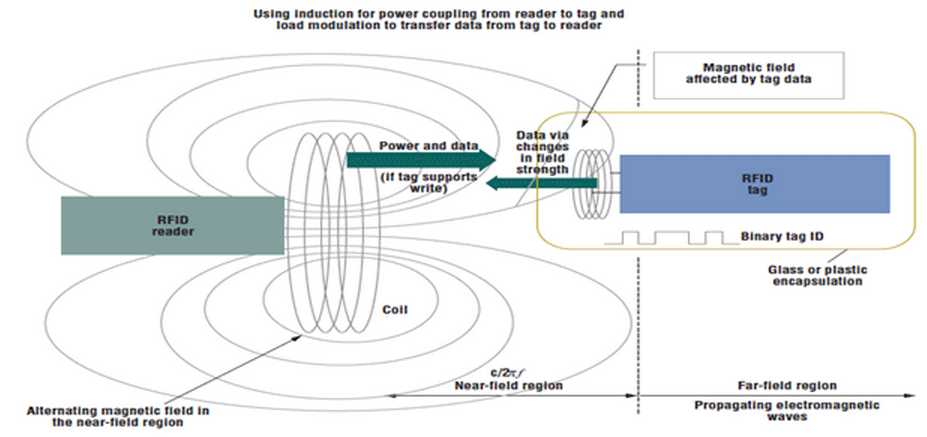
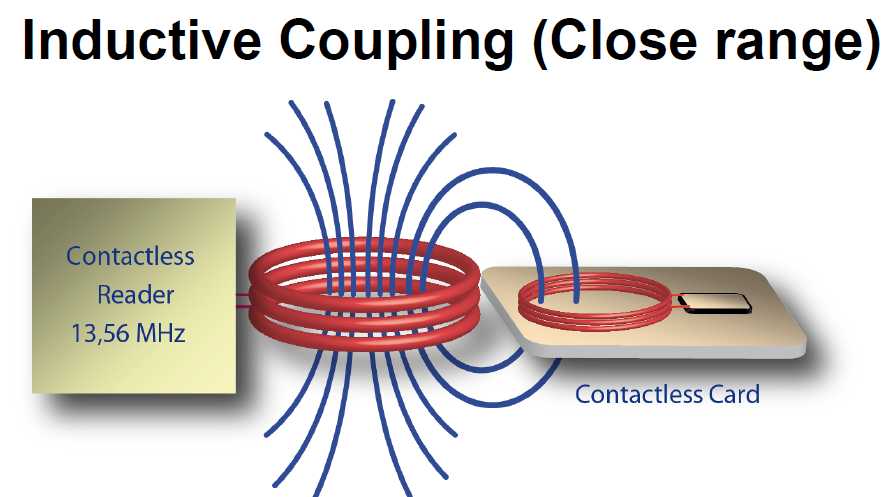
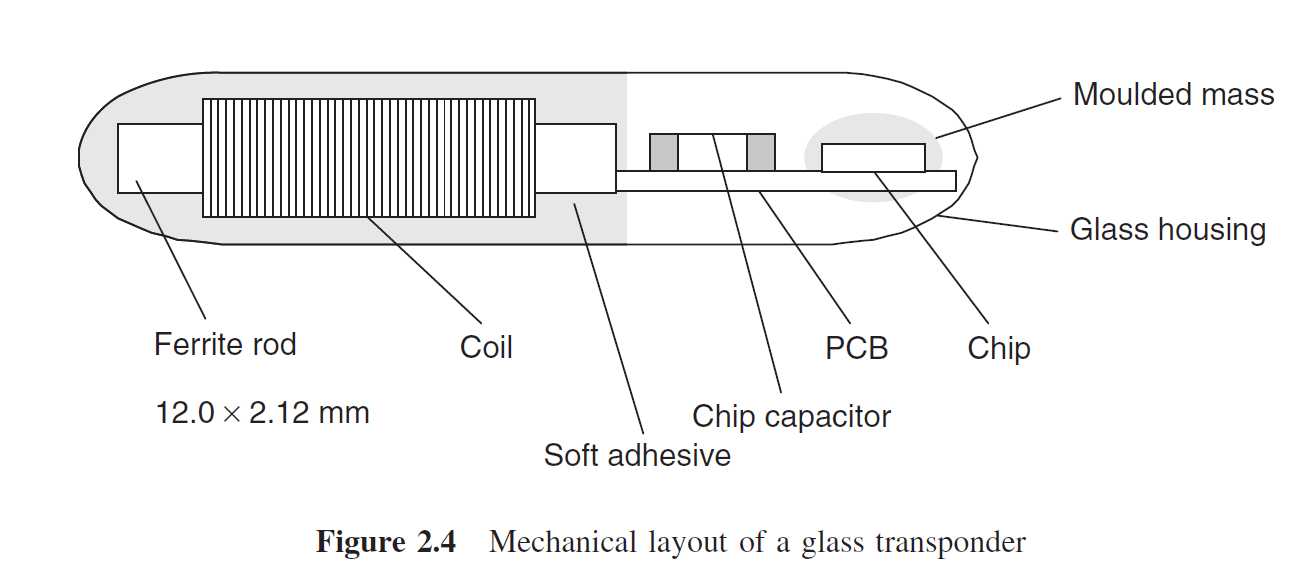
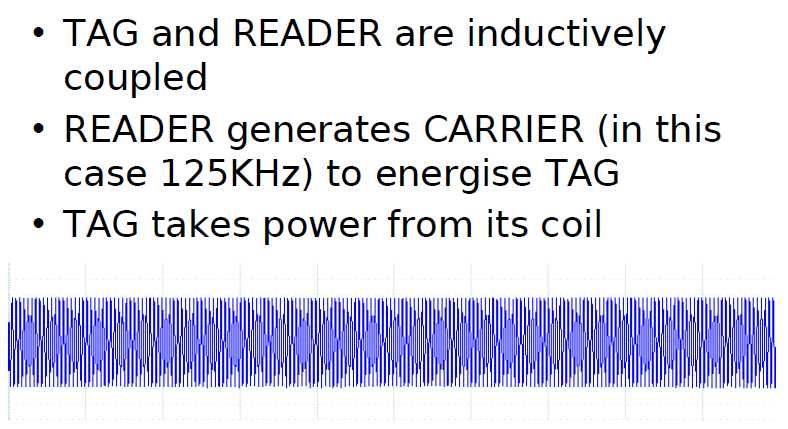
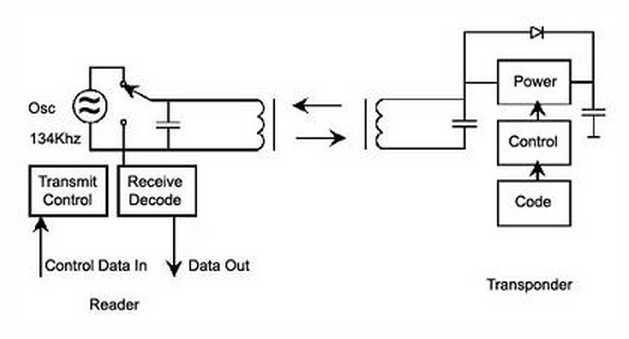
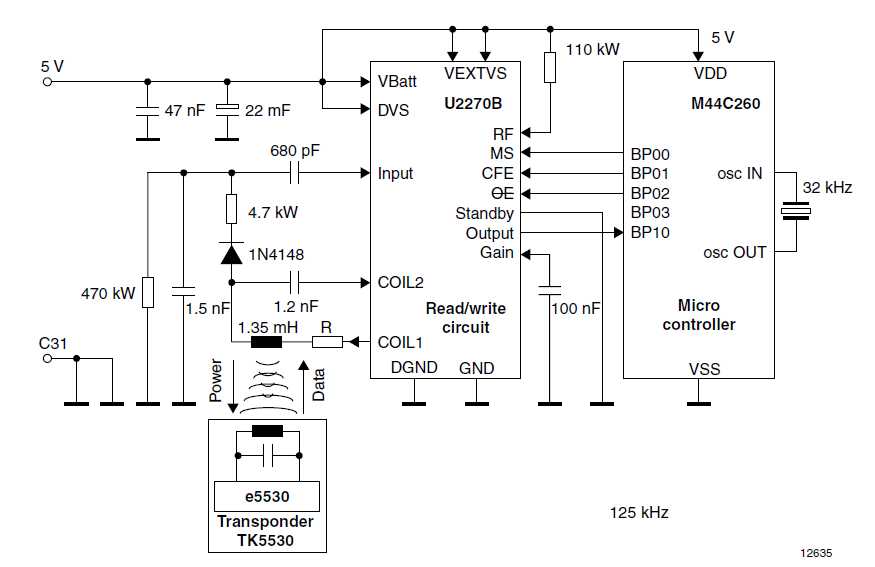
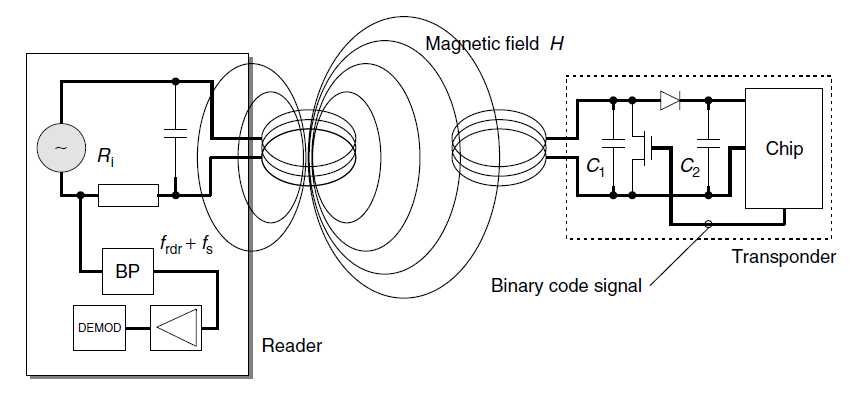
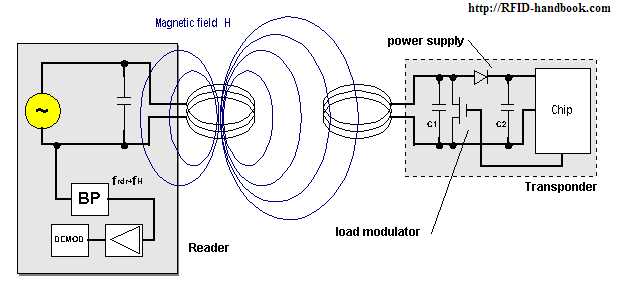
其实RFID技术首先在低频得到广泛的应用和推广。该频率主要是通过电感耦合的方式进行工作,
也就是在读写器线圈和感应器线圈间存在着变压器耦合作用.通过读写器交变场的作用在感应器天线中
感应的电压被整流,可作供电电压使用. 磁场区域能够很好的被定义,但是场强下降的太快。
特性:
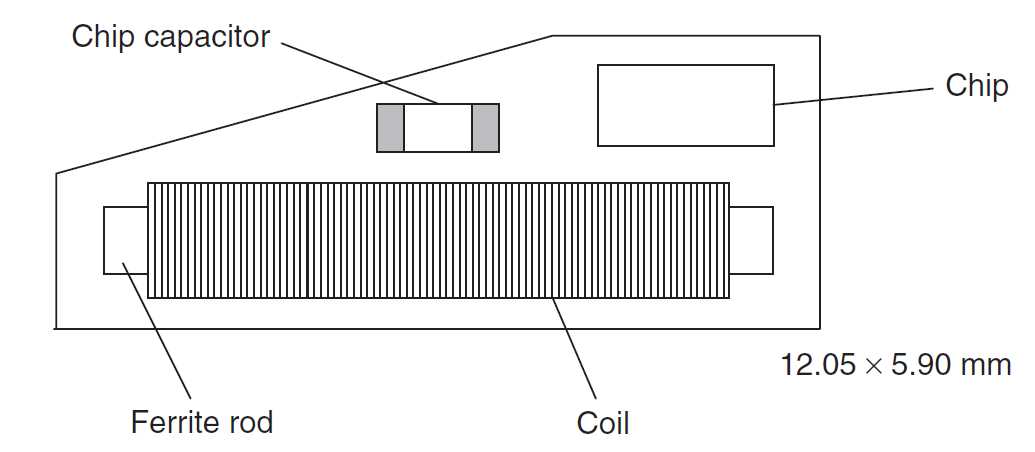
1. 工作在低频的感应器的一般工作频率从120KHz到134KHz, TI 的工作频率为134.2KHz。该频段的波长大约为2500m.
2. 除了金属材料影响外,一般低频能够穿过任意材料的物品而不降低它的读取距离。
3. 工作在低频的读写器在全球没有任何特殊的许可限制。
4.低频产品有不同的封装形式。好的封装形式就是价格太贵,但是有10年以上的使用寿命。
5.虽然该频率的磁场区域下降很快,但是能够产生相对均匀的读写区域。
6.相对于其他频段的RFID产品,该频段数据传输速率比较慢。
7.感应器的价格相对与其他频段来说要贵。
主要应用:
1. 畜牧业的管理系统
2. 汽车防盗和无钥匙开门系统的应用
3. 马拉松赛跑系统的应用
4. 自动停车场收费和车辆管理系统
5. 自动加油系统的应用
6. 酒店门锁系统的应用
7. 门禁和安全管理系统
符合的国际标准:
a) ISO 11784 RFID畜牧业的应用-编码结构
b) ISO 11785 RFID畜牧业的应用-技术理论
c) ISO 14223-1 RFID畜牧业的应用-空气接口
d) ISO 14223-2 RFID畜牧业的应用-协议定义
e) ISO 18000-2 定义低频的物理层、防冲撞和通讯协议
f) DIN 30745 主要是欧洲对垃圾管理应用定义的标准
2. 高频(工作频率为13.56MHz)
在该频率的感应器不再需要线圈进行绕制,可以通过腐蚀活着印刷的方式制作天线。
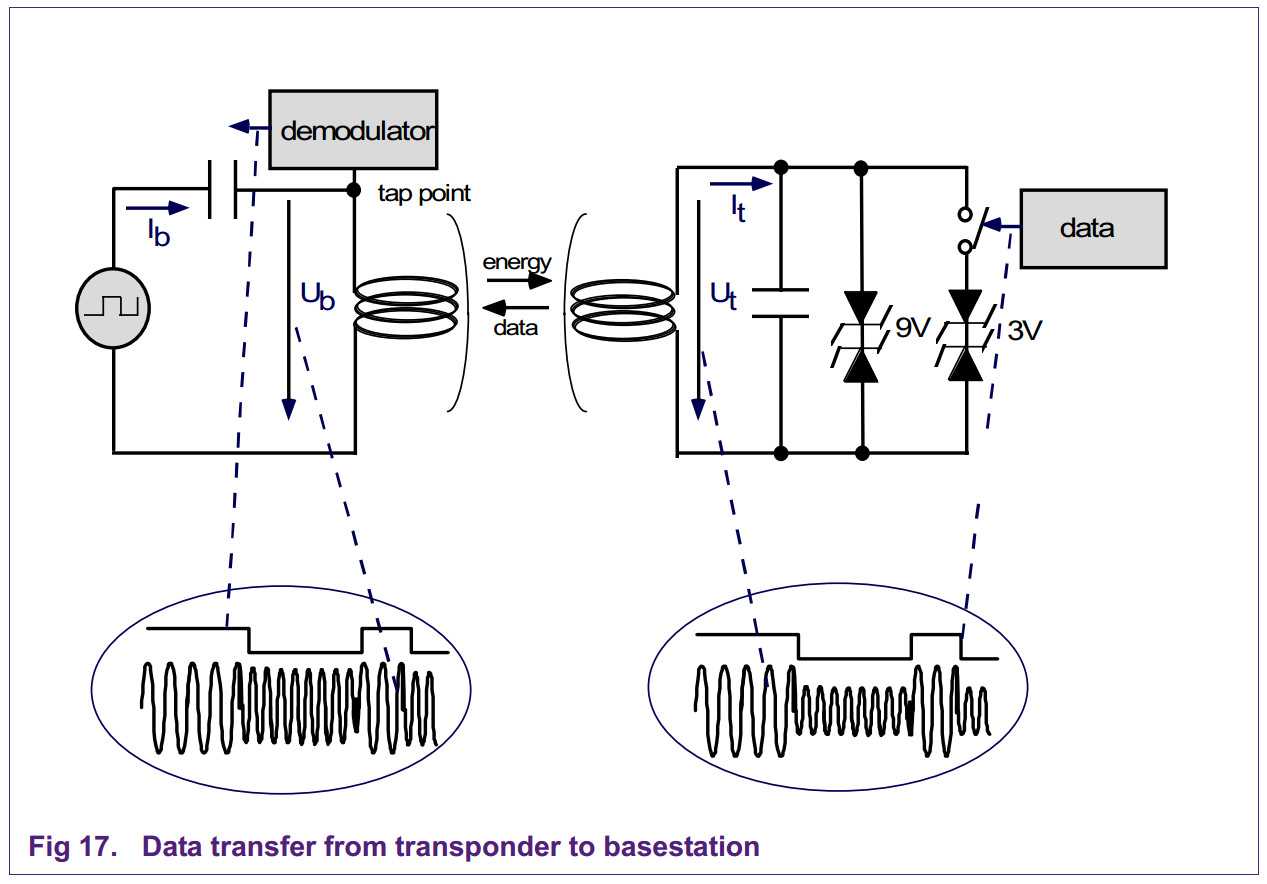
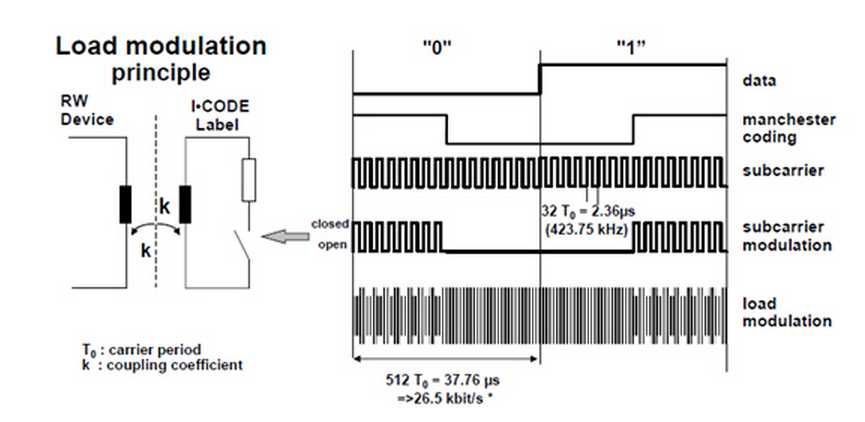
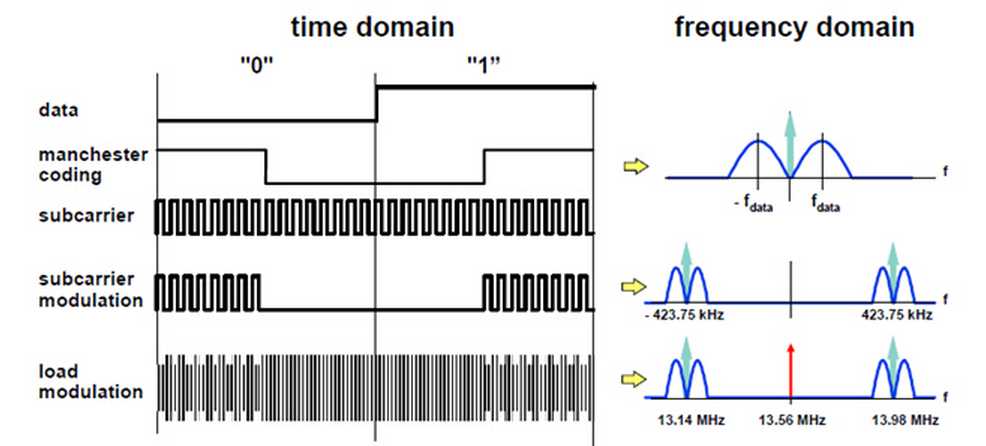
感应器一般通过负载调制的方式 的方式进行工作。
也就是通过感应器上的负载电阻的接通和断开促使读写器天线上的电压发生变化,实现用远距离感应器对天线电压进行振幅调制。
如果人们通过数 据控制负载电压的接通和断开,那么这些数据就能够从感应器传输到读写器
特性:
1. 工作频率为13.56MHz,该频率的波长大概为22m。
2. 除了金属材料外,该频率的波长可以穿过大多数的材料,但是往往会降低读取距离。感应器需要离开金属一段距离。
3. 该频段在全球都得到认可并没有特殊的限制。
4. 感应器一般以电子标签的形式。
5. 虽然该频率的磁场区域下降很快,但是能够产生相对均匀的读写区域。
6. 该系统具有防冲撞特性,可以同时读取多个电子标签。
7. 可以把某些数据信息写入标签中。
8. 数据传输速率比低频要快,价格不是很贵。
主要应用:
1. 图书管理系统的应用
2. 瓦斯钢瓶的管理应用
3. 服装生产线和物流系统的管理和应用
4. 三表预收费系统
5. 酒店门锁的管理和应用
6. 大型会议人员通道系统
7. 固定资产的管理系统
8. 医药物流系统的管理和应用
9. 智能货架的管理
符合的国际标准:
a) ISO/IEC 14443 近耦合IC卡,最大的读取距离为10cm.
b) ISO/IEC 15693 疏耦合IC卡,最大的读取距离为1m.
c) ISO/IEC 18000-3 该标准定义了13.56MHz系统的物理层,防冲撞算法和通讯协议。
d) 13.56MHz ISM Band Class 1 定义13.56MHz符合EPC的接口定义。
3. 超高频(工作频率为860MHz到960MHz之间)
甚高频系统通过电场来传输能量。电场的能量下降的不是很快,但是读取的区域不是很好进行定义。
该频段读取距离比较远,无源可达10m左右。主要是通过电容耦合的方式进行实现。
特性:
主要应用:
符合的国际标准:
a) ISO/IEC 18000-6 定义了甚高频的物理层和通讯协议;空气接口定义了Type A和Type B两部分;支持可读和可写操作。
b) EPCglobal 定义了电子物品编码的结构和甚高频的空气接口以及通讯的协议。例如:Class 0, Class 1, UHF Gen2。
c) Ubiquitous ID 日本的组织,定义了UID编码结构和通信管理协议。
我们毫无怀疑,在将来,甚高频的产品会得到大量的应用。例如WalMart, Tesco, 美国国防部和麦德龙超市都会在它们的供应链上应用RFID技术。
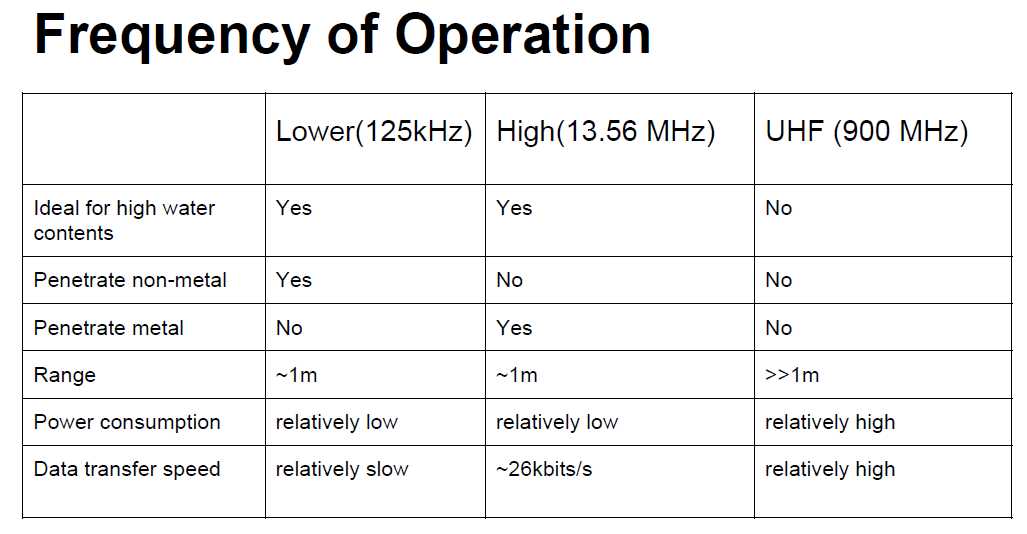
Frequency refers to the size of the radio waves used to communicate between RFID system components.
RFID systems throughout the world operate in low frequency (LF), high frequency (HF) and ultra-high frequency (UHF) bands.
Radio waves behave differently at each of these frequencies with advantages and disadvantages associated with using each frequency band.
If an RFID system operates at a lower frequency, it has a shorter read range and slower data read rate,
but increased capabilities for reading near or on metal or liquid surfaces.
If a system operates at a higher frequency, it generally has faster data transfer rates and longer read ranges than lower frequency systems,
but more sensitivity to radio wave interference caused by liquids and metals in the environment.
The LF band covers frequencies from 30 KHz to 300 KHz.
Typically LF RFID systems operate at 125 KHz, although there are some that operate at 134 KHz.
This frequency band provides a short read range of 10 cm, and has slower read speed than the higher frequencies,
but is not very sensitive to radio wave interference.
LF RFID applications include access control and livestock tracking.
Standards for LF animal-tracking systems are defined in ISO 14223, and ISO/IEC 18000-2.
The LF spectrum is not considered a truly global application because of slight differences in frequency and power levels throughout the world.
The HF band ranges from 3 to 30 MHz. Most HF RFID systems operate at 13.56 MHz with read ranges between 10 cm and 1 m.
HF systems experience moderate sensitivity to interference.
HF RFID is commonly used for ticketing, payment, and data transfer applications.
There are several HF RFID standards in place, such as the ISO 15693 standard for tracking items,
and the ECMA-340 and ISO/IEC 18092 standards for Near Field Communication (NFC),
a shortrange technology that is commonly used for data exchange between devices.
Other HF standards include the ISO/IEC 14443 A and ISO/IEC 14443 standards for MIFARE technology,
which used in smart cards and proximity cards,
and the JIS X 6319-4 for FeliCa, which is a smart card system commonly used in electronic money cards.
The UHF frequency band covers the range from 300 MHz to 3 GHz.
Systems complying with the UHF Gen2 standard for RFID use the 860 to 960 MHz band.
While there is some variance in frequency from region to region,
UHF Gen2 RFID systems in most countries operate between 900 and 915 MHz.
The read range of passive UHF systems can be as long as 12 m, and UHF RFID has a faster data transfer rate than LF or HF.
UHF RFID is the most sensitive to interference, but many UHF product manufacturers have found ways of designing tags,
antennas, and readers to keep performance high even in difficult environments.
Passive UHF tags are easier and cheaper to manufacture than LF and HF tags.
UHF RFID is used in a wide variety of applications, ranging from retail inventory management,
to pharmaceutical anti-counterfeiting, to wireless device configuration.
The bulk of new RFID projects are using UHF opposed to LF or HF, making UHF the fastest growing segment of the RFID market.
The UHF frequency band is regulated by a single global standard called the ECPglobal Gen2 (ISO 18000-6C) UHF standard.
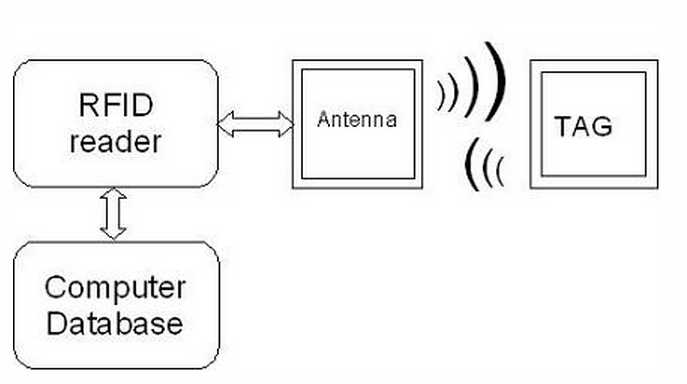
RFID is so called Radio Frequency Identification system which consists of two main parts:
transmitter and receiver.
The labels, access cards and even passports in some countries they have RFID transponders integrated.
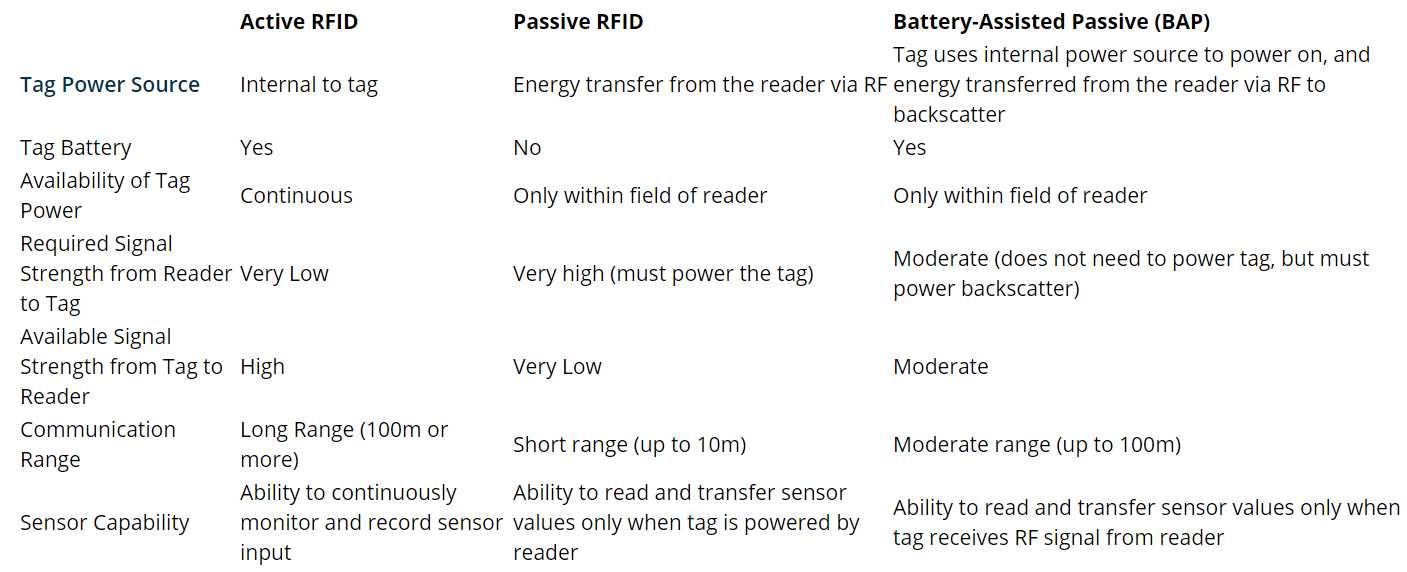
There can be three types of RFID transponders:
Passive, Active and semi-passive.
Tags are grouped into three basic types:
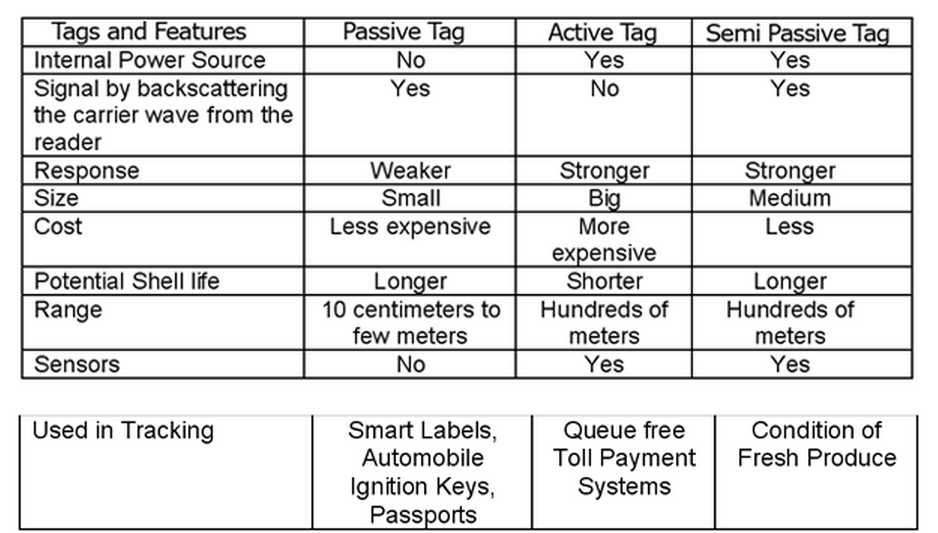
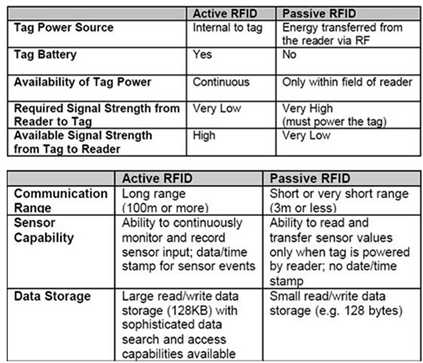
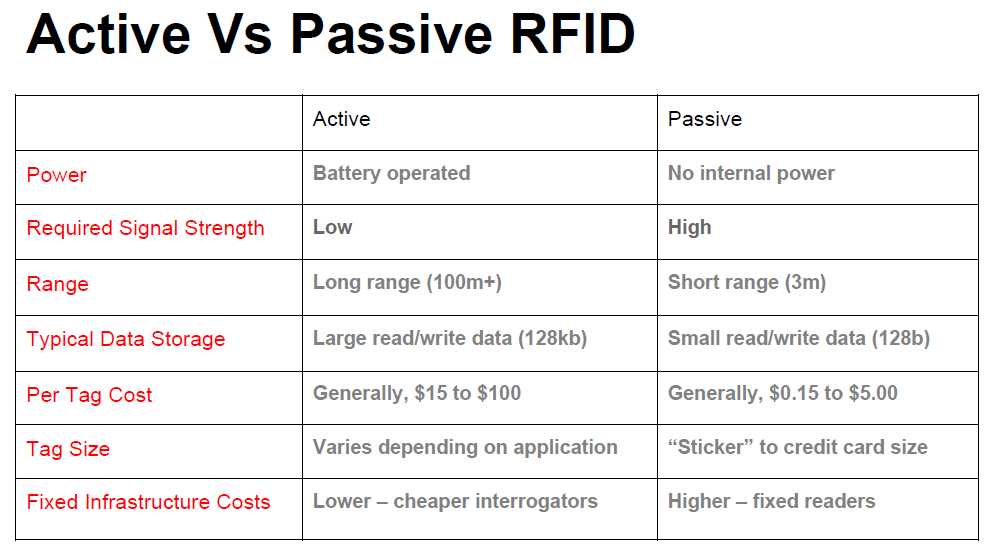
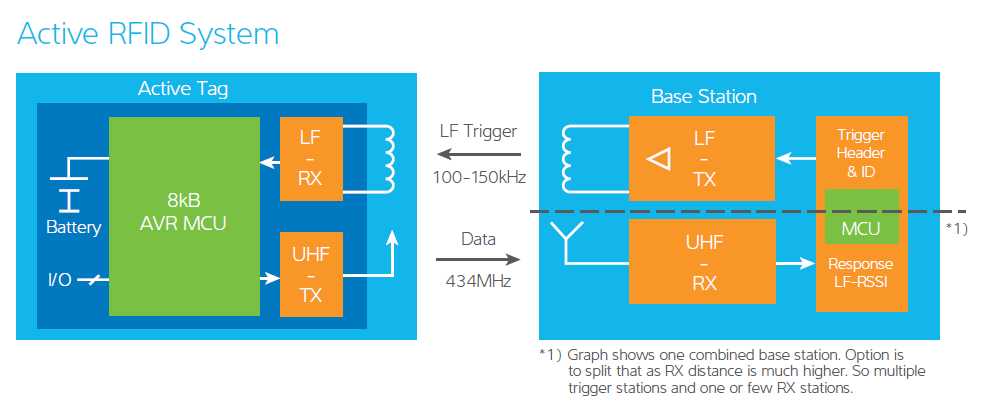
In active RFID systems, tags have their own transmitter and power source.
Usually, the power source is a battery.
Active tags broadcast their own signal to transmit the information stored on their microchips.
Active RFID systems typically operate in the ultra-high frequency (UHF) band and offer a range of up to 100 m.
In general, active tags are used on large objects, such as rail cars, big reusable containers,
and other assets that need to be tracked over long distances.
There are two main types of active tags: transponders and beacons.
Transponders are “woken up” when they receive a radio signal from a reader,
and then power on and respond by transmitting a signal back.
Because transponders do not actively radiate radio waves until they receive a reader signal, they conserve battery life.
Beacons are used in most real-time locating systems (RTLS), in order to track the precise location of an asset continuously.
Unlike transponders, beacons are not powered on by the reader’s signal.
Instead, they emit signals at pre-set intervals. Depending on the level of locating accuracy required,
beacons can be set to emit signals every few seconds, or once a day.
Each beacon’s signal is received by reader antennas that are positioned around the perimeter of the area being monitored,
and communicates the tag’s ID information and position.
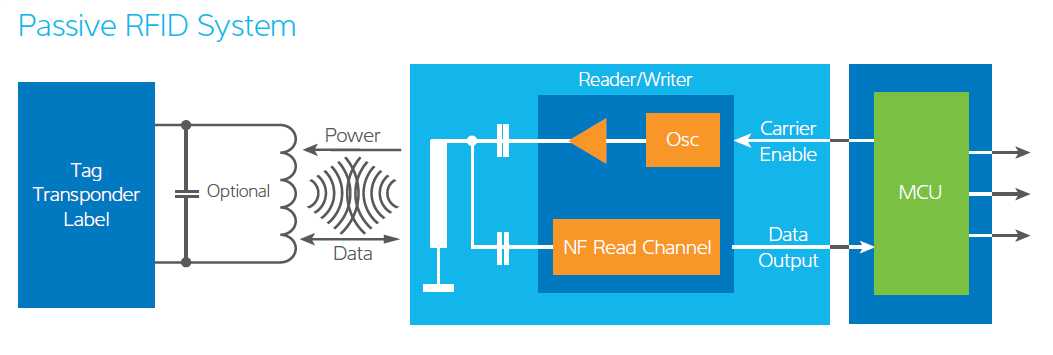
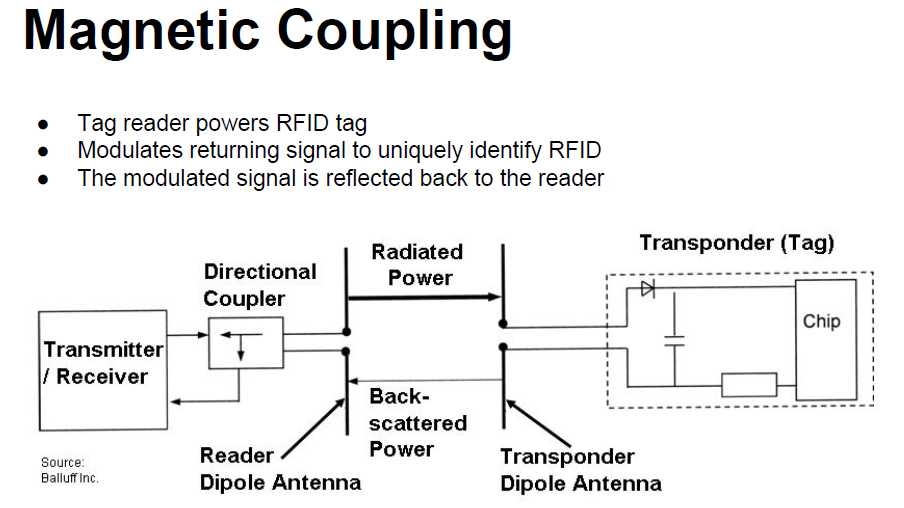
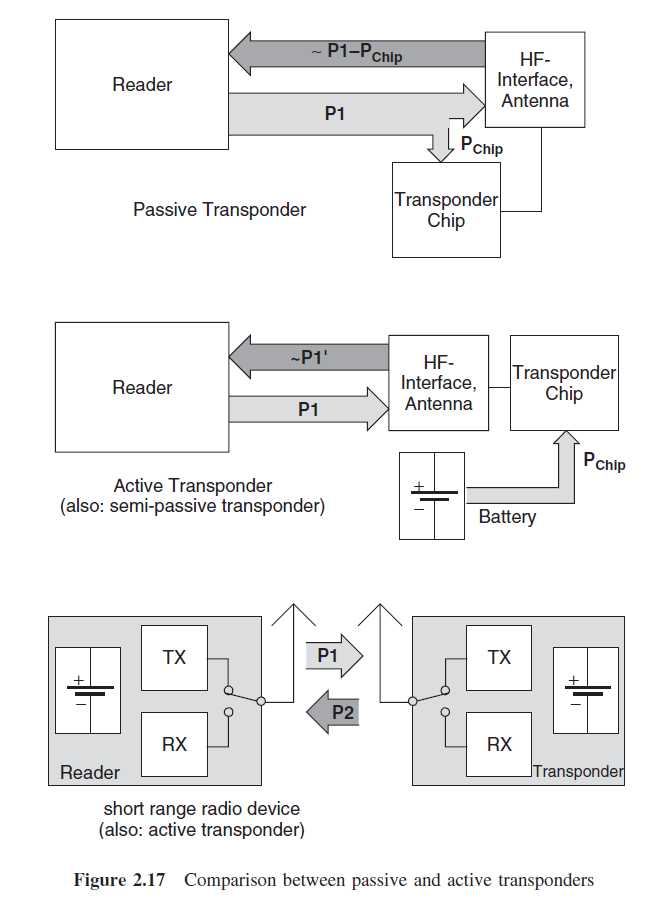
In passive RFID systems, the reader and reader antenna send a radio signal to the tag.
The RFID tag then uses the transmitted signal to power on, and reflect energy back to the reader.
Passive RFID systems can operate in the low frequency (LF), high frequency (HF) or ultra-high frequency (UHF) radio bands.
As passive system ranges are limited by the power of the tag’s backscatter
(the radio signal reflected from the tag back to the reader),they are typically less than 10 m.
Because passive tags do not require a power source or transmitter, and only require a tag chip and antenna,
they are cheaper, smaller, and easier to manufacture than active tags.
Passive tags can be packaged in many different ways, depending on the specific RFID application requirements.
For instance, they may be mounted on a substrate, or sandwiched between an adhesive layer and a paper label to create smart RFID labels.
Passive tags may also be embedded in a variety of devices or packages to make the tag resistant to extreme temperatures or harsh chemicals.
Passive RFID solutions are useful for many applications, and are commonly deployed to track goods in the supply chain,
to inventory assets in the retail industry, to authenticate products such as pharmaceuticals, and to embed RFID capability in a variety of devices.
Passive RFID can even be used in warehouses and distribution centers,
in spite of its shorter range, by setting up readers at choke points to monitor asset movement.
A Battery-Assisted Passive RFID tag is a type of passive tag which incorporates a crucial active tag feature.
While most passive RFID tags use the energy from the RFID reader’s signal to power on the tag’s chip and backscatter to the reader,
BAP tags use an integrated power source (usually a battery) to power on the chip,
so all of the captured energy from the reader can be used for backscatter.
Unlike transponders, BAP tags do not have their own transmitters.

Transponders (tags) of passive RFID system don’t have power supply.
This is why they are called passive.
Passive tags are powered from electromagnetic field generated by reader antenna.
Reader antenna has to transmit enough power to provide enough energy to tag so it could to transmit back data.
Because of this reading distance is very limited – up to several centimeters.
Passive RFID tags do not have internal power supply.
Instead, they are powered by energy induced in the antenna by the RF signal.
Most passive tags transmit by backscattering the carrier signal from the reader.
The engineering challenge is to design an antenna that can collect power from the incoming signal
and transmit it to the outbound backscatter signal.
The response of a passive RFID tag is not necessarily just an ID number;
the tag chip can contain non-volatile EEPROM for storing data.
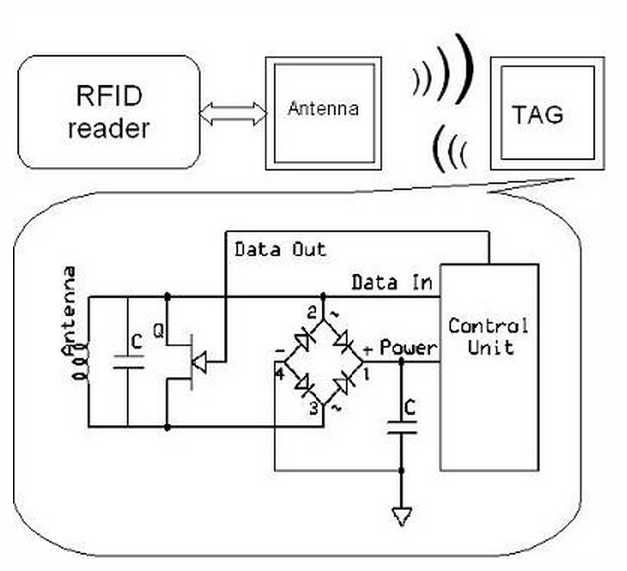
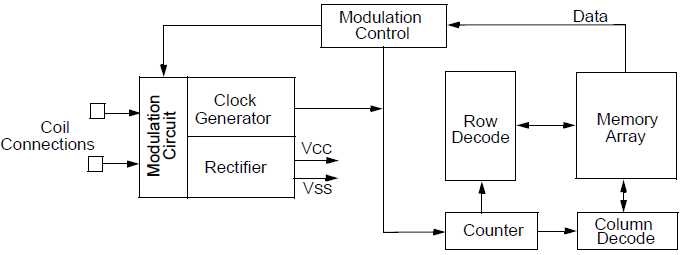
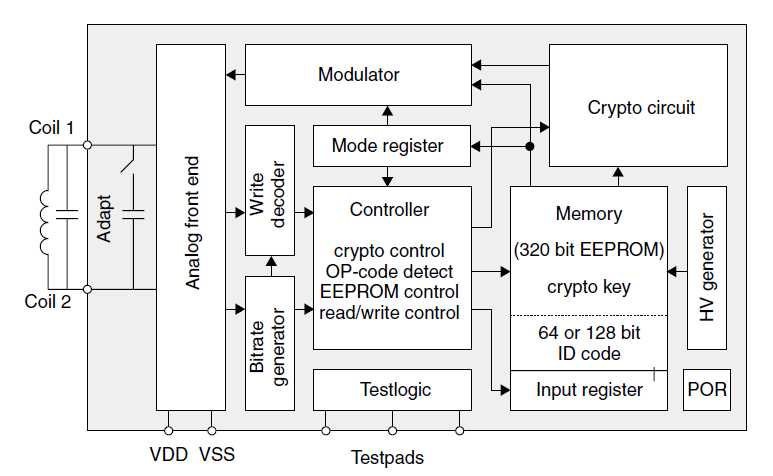
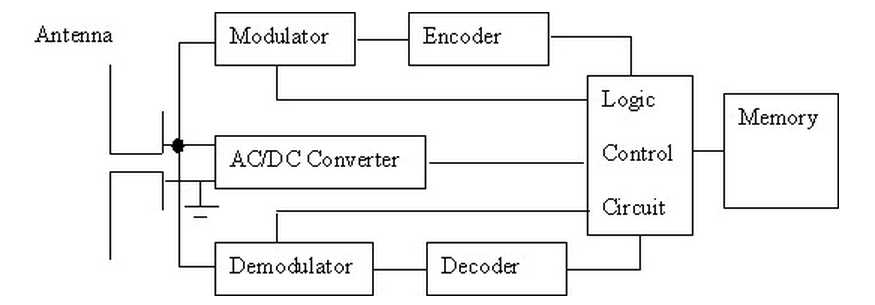
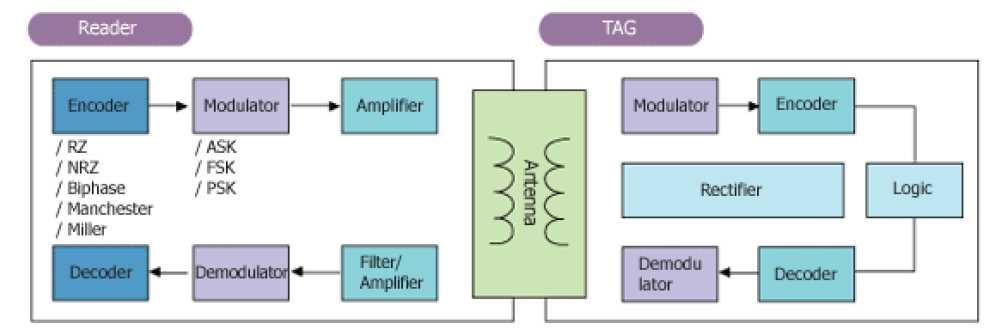
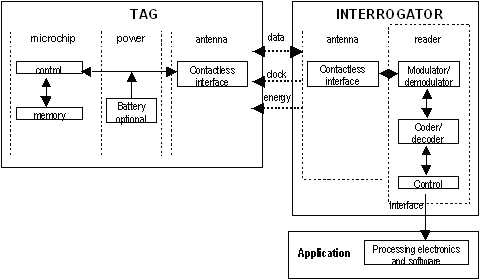
A simplified block schematic of an RFID tag (also called transponder) is shown in the diagram below.
Various components of the tag are as shown.
Normally, the antenna is external to the tag chip, and large in size.
The operation of the RFID tag is described below:
Handshaking with the Reader (interrogator):
Well some of implementations may reach several meters.
Passive tags are most common used because they are cheap,
can last indefinitely long as there is no need for power supply,
and they are small size what allows them easy to integrate almost
in every environment starting wrists, necklaces, cards, stickers.
Passive tags simply consist of single IC and antena coil which is usually flat.
Passive tags are operating below 100MHz frequencies
(most common frequencies are 125kHz – 134.2kHz and 13.56MHz)
and main transfer energy is carried by magnetic field.
Magnetic field generated voltage in the coil which is used as power supply also as data signal.
There are also HF passive tags that operate at 900MHz and 2.45GHz.
These tags have dipole antena (1/8 wave length)construction.
With these tags distance may reach more than 3 meters.
But high frequency tags require more expensive manufacturing processing with more precise electronics,
but they can support up to 2Mb/s data stream.
Active RFID tags may provide all advantages of RFID system because tags are fully powered transmitters.
They don’t have to be activated by antenna reader.
Active RFID topic may be very wide because there are many areas where an how they can be used.
In some cases tags may not need a reader antena because tags in some particular cases can be configured to interact with each other.
Active transponders can communicate in very long ranges up to several hundred kilometers.
Main disadvantages of active tags may be relatively big size and production price compared to passive ones.


Semi-Passive tags are more similar to passive transponders than active.
These tags are powered from battery or so called battery assisted tags,
but radio transmission depends on antena activity.
As data processor had it own power, so all received power can be used for transmitting back the signal
which is stronger than passive transducer.
This allows to increase communication distance with quit cheap solution.

Semi passive RFID tags augment the energy from reader antenna,
but they are not constantly beaming signals as active tags does.
Semi-passive RFID tags use a process to generate a tag response similar to that of passive tags.
Semi-passive tags differ from passive in that semi passive tags possess an internal battery
for the tag’s circuitry which allows the tag to complete other functions such as monitoring
of environmental conditions (temperature, shock) and which may extend the tag signal range.
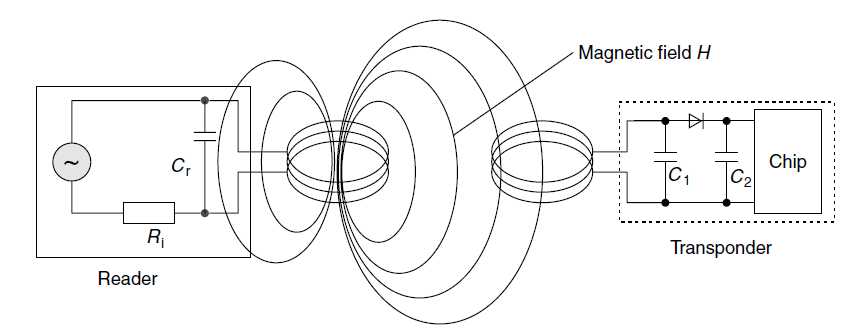
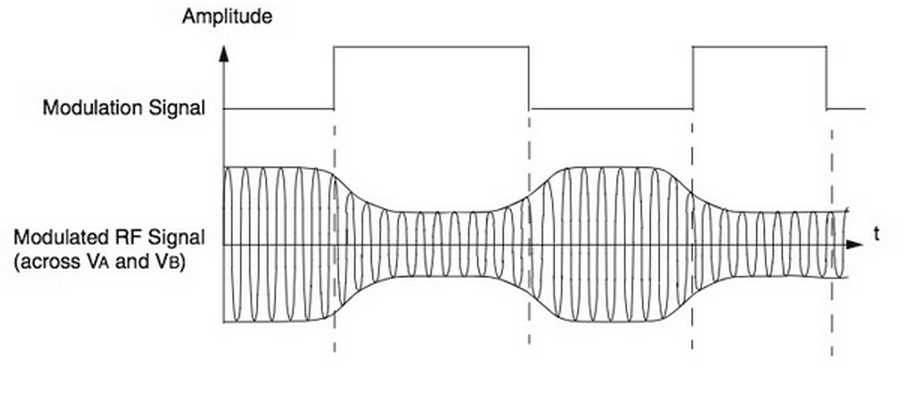
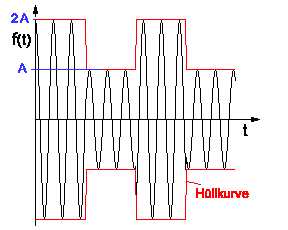
Power supply to an inductively coupled transponder from the energy of the magnetic alternating field generated by the reader
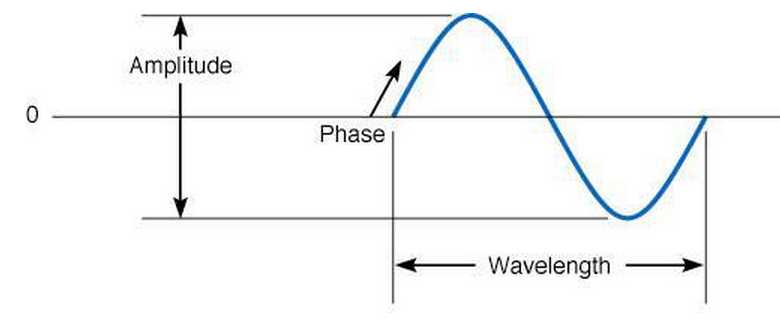
Sound is converted into electricity by a telephone and then transmitted as an analog signal.
These waves have 3 fundamental characteristics:
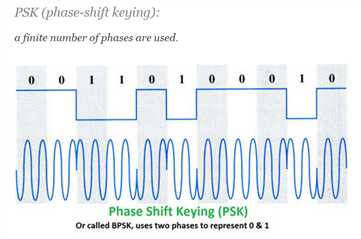
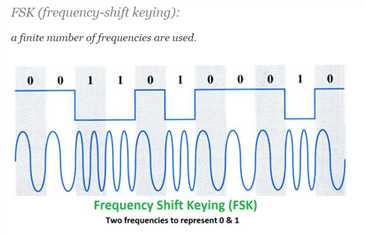
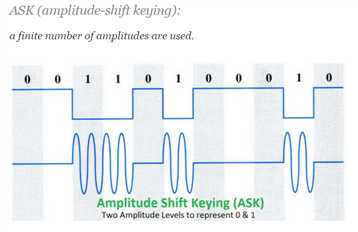
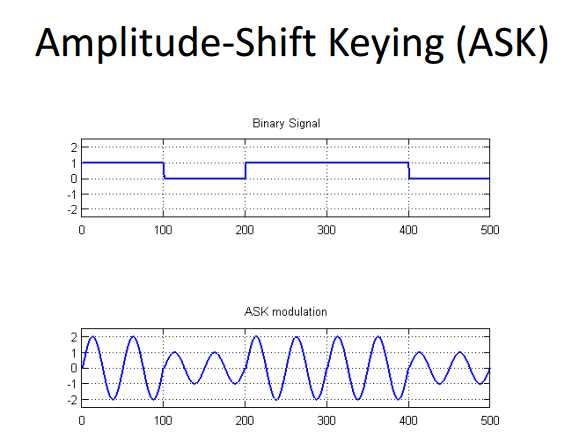
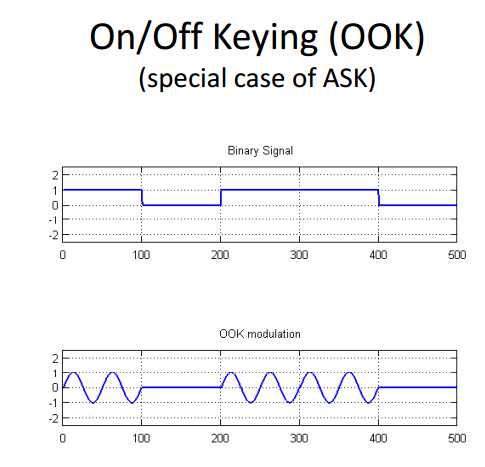
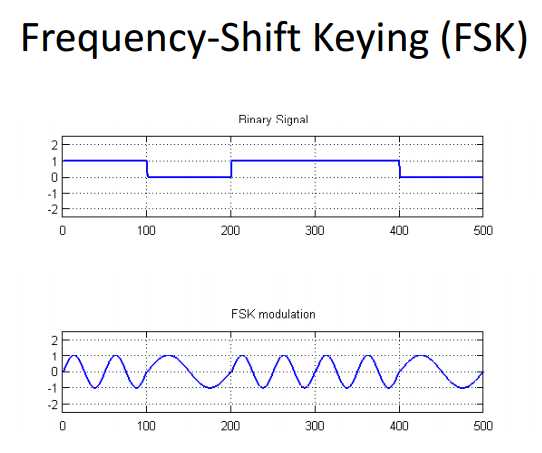
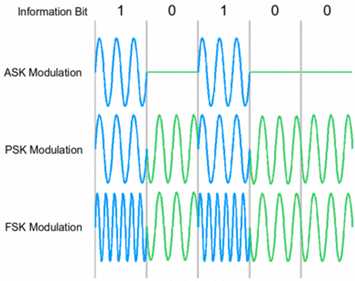
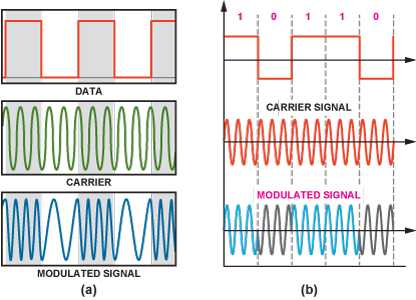
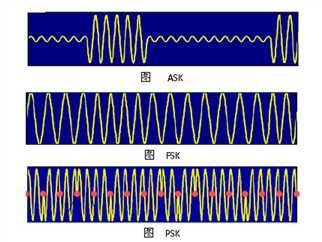
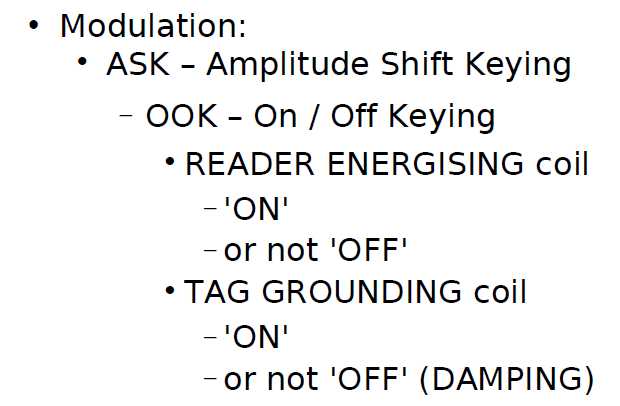
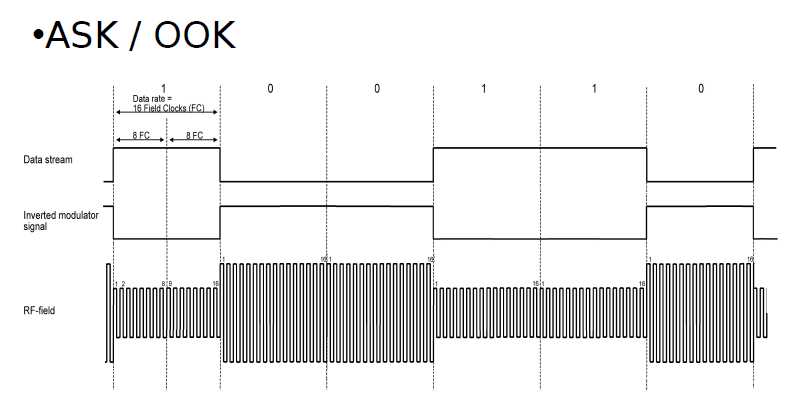
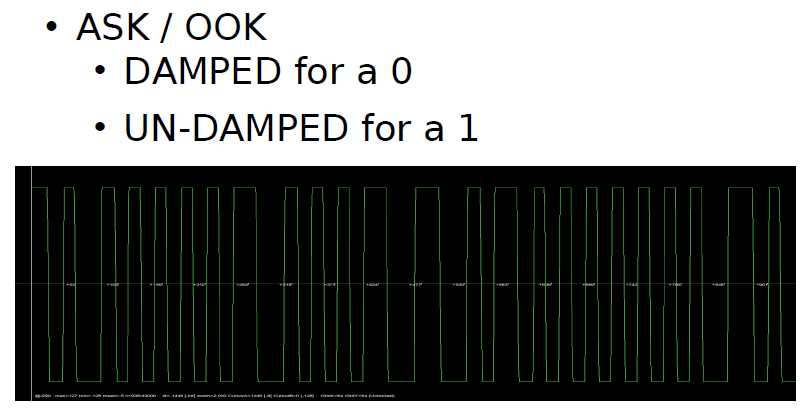
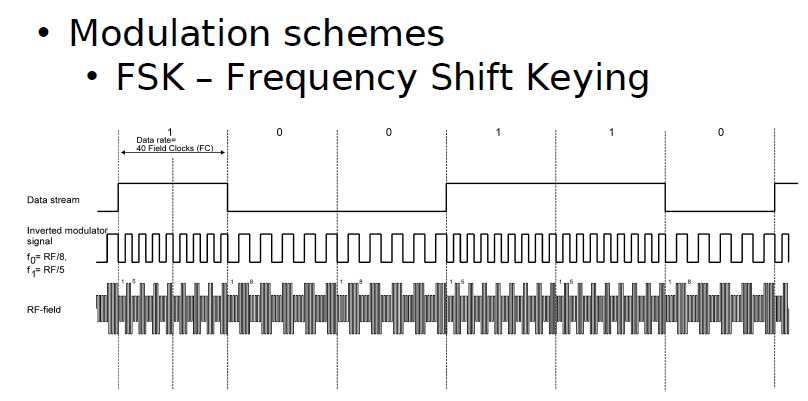
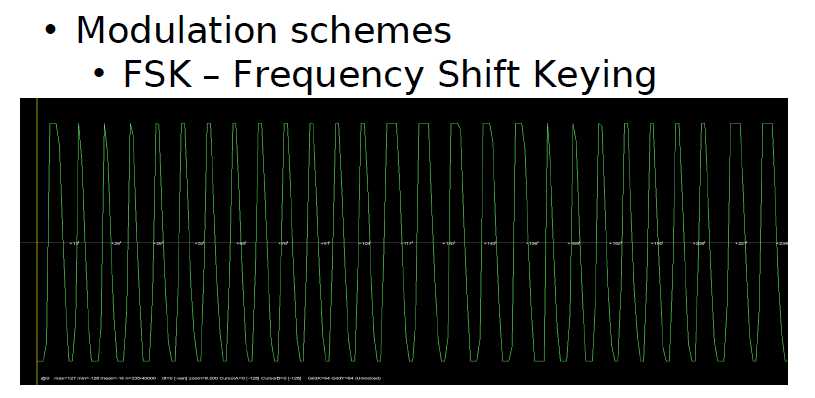
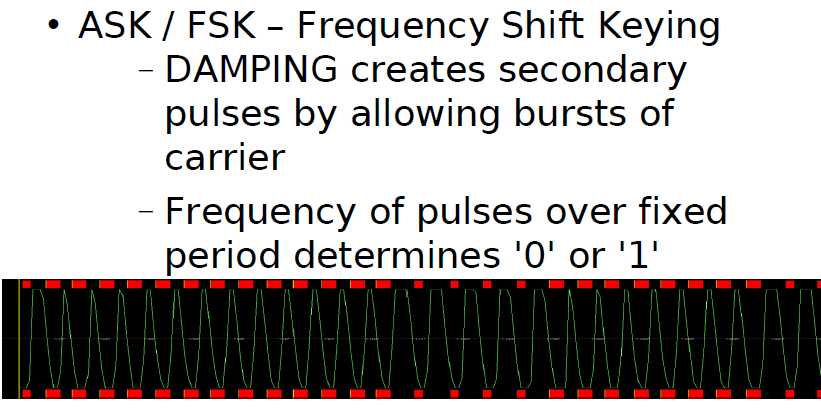
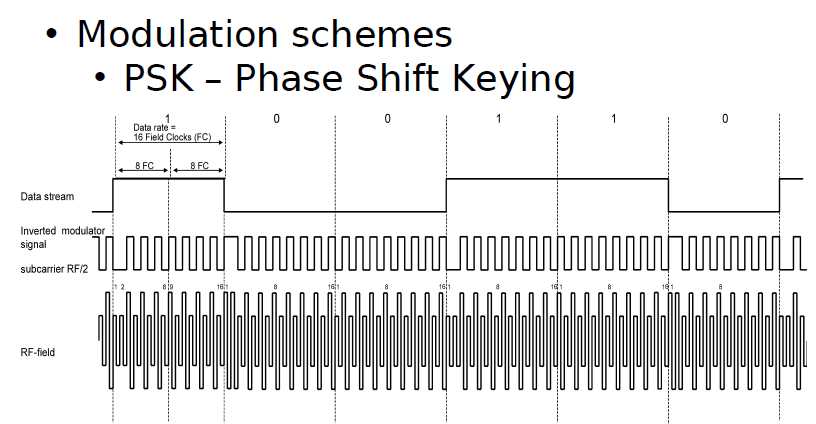
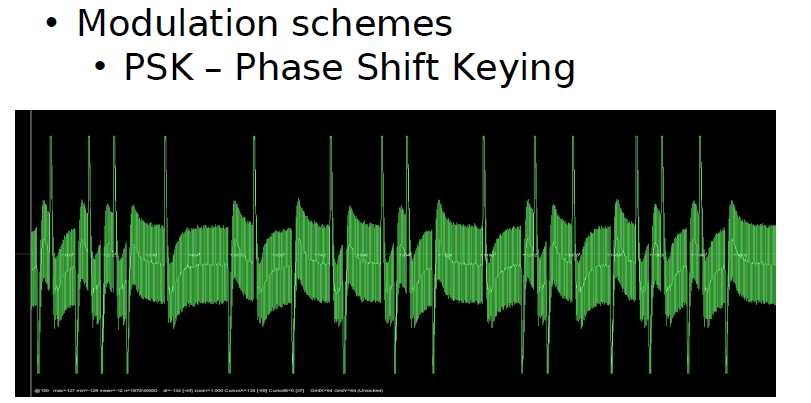
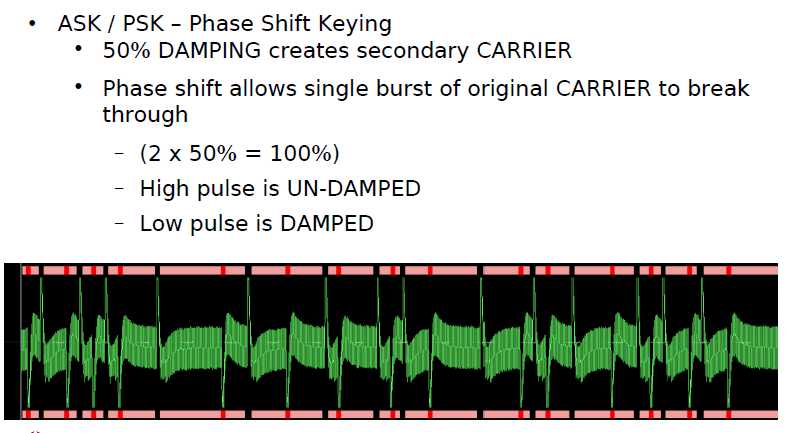
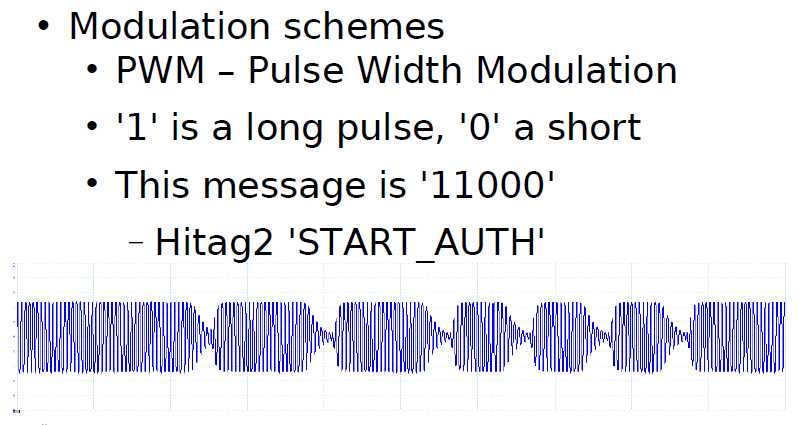
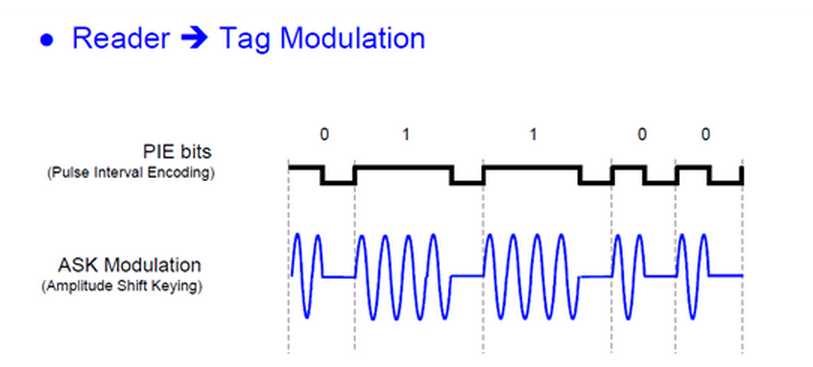
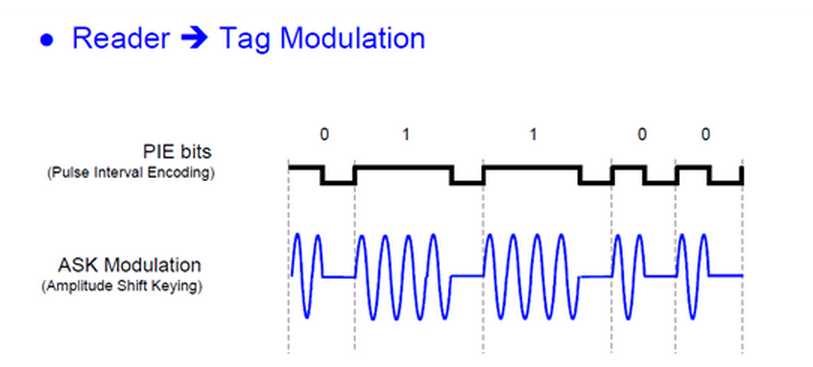
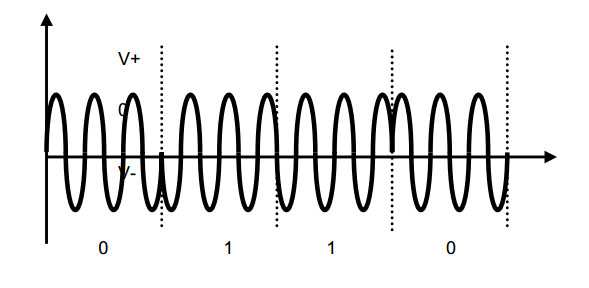
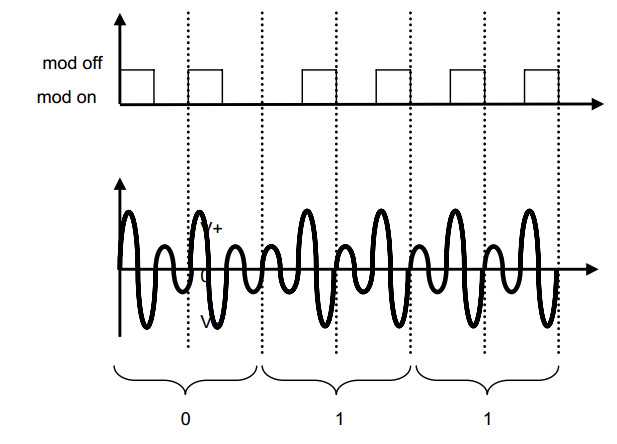
Most RFID tags were using ASK (Amplitude Shift Keying), FSK (Frequency Shift Keying) and PSK (Phase Shift Keying) for its analog modulation.
All known digital modulation procedures are used in data transfer from the reader to the transponder
in full and half duplex systems, irrespective of the operating frequency or the coupling procedure.
There are three basic procedures:
Because of the simplicity of demodulation, the majority of systems use ASK modulation
Modulation is the process process of modifying modifying the characteristics of a signal,
called a carrier wave, to convey information information.
The characteristics of a signal to modify include amplitude, frequency frequency, and phase.
http://electronicdesign.com/communications/understanding-modern-digital-modulation-techniques
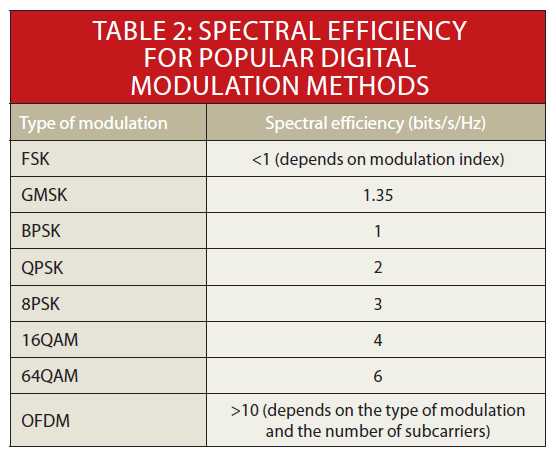
Fundamental to all wireless communications is modulation, the process of impressing the data to be transmitted on the radio carrier. Most wireless transmissions today are digital, and with the limited spectrum available, the type of modulation is more critical than it has ever been.
The main goal of modulation today is to squeeze as much data into the least amount of spectrum possible. That objective, known as spectral efficiency, measures how quickly data can be transmitted in an assigned bandwidth. The unit of measurement is bits per second per Hz (b/s/Hz). Multiple techniques have emerged to achieve and improve spectral efficiency.
Table of Contents
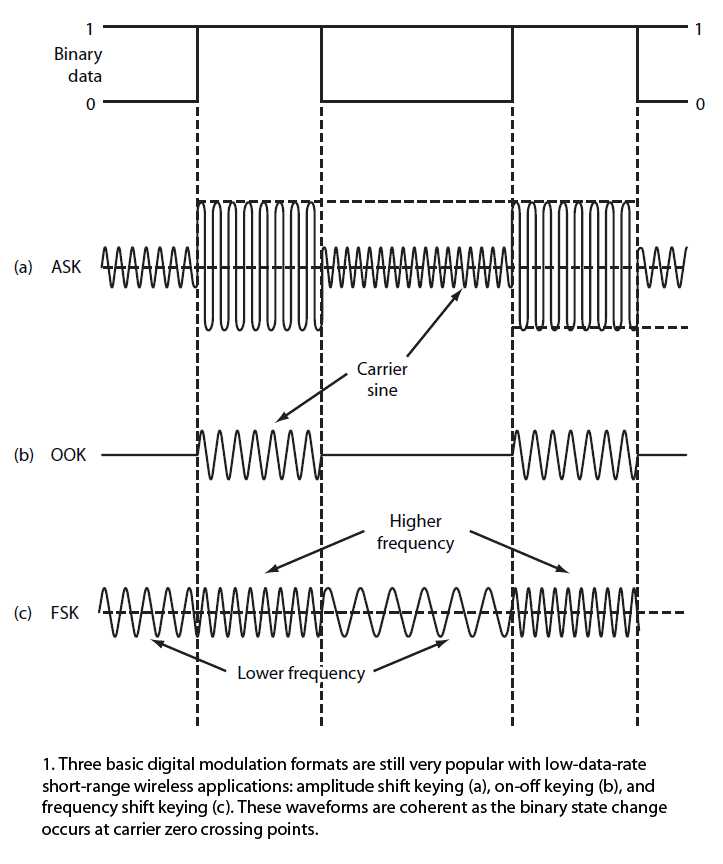
Amplitude Shift Keying (ASK) and Frequency Shift Keying (FSK)
There are three basic ways to modulate a sine wave radio carrier:
modifying the amplitude, frequency, or phase.
More sophisticated methods combine two or more of these variations to improve spectral efficiency.
These basic modulation forms are still used today with digital signals.
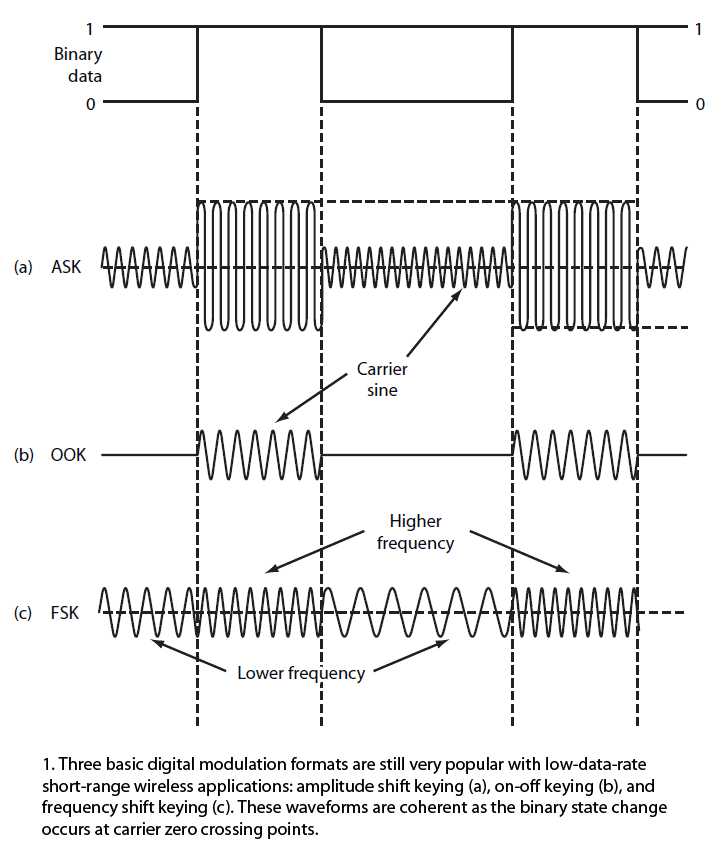
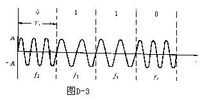
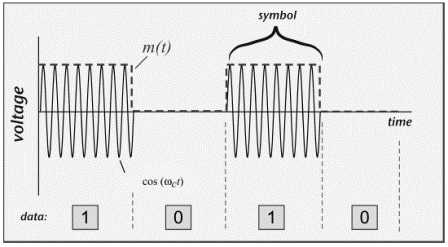
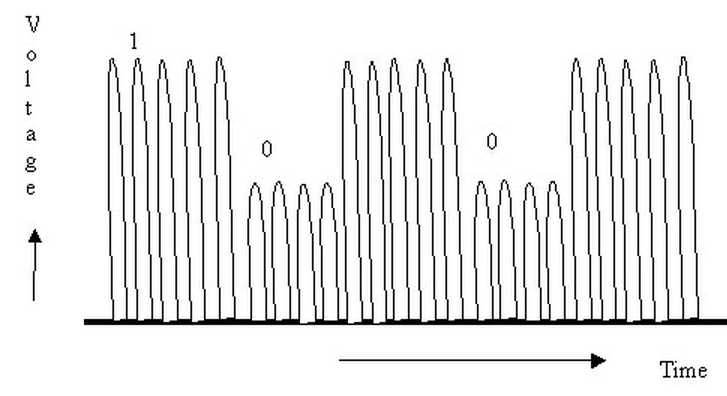
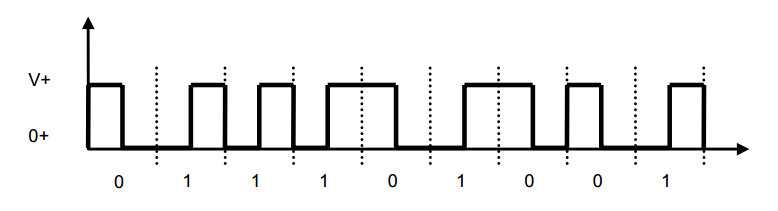
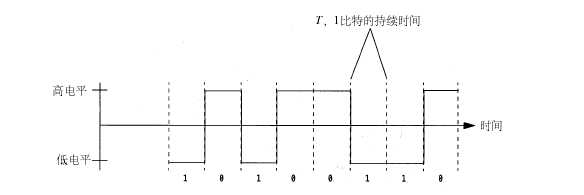
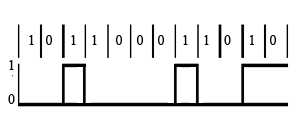
Figure 1 shows a basic serial digital signal of binary zeros and ones to be transmitted and the corresponding AM and FM signals resulting from modulation.
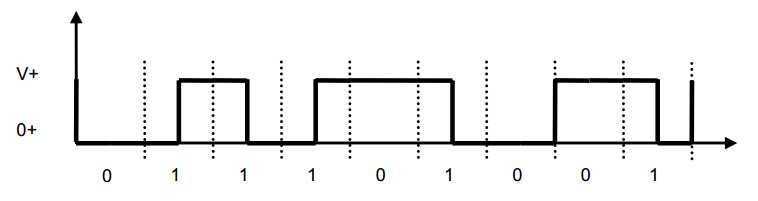
There are two types of AM signals: on-off keying (OOK) and amplitude shift keying (ASK).
In Figure 1a, the carrier amplitude is shifted between two amplitude levels to produce ASK.
InFigure 1b, the binary signal turns the carrier off and on to create OOK.
AM produces sidebands above and below the carrier equal to the highest frequency content of the modulating signal.
The bandwidth required is two times the highest frequency content including any harmonics for binary pulse modulating signals.
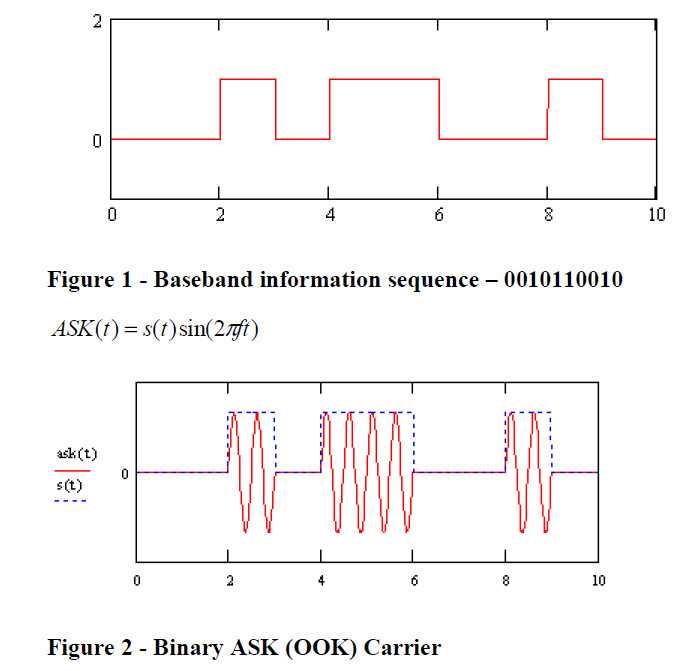
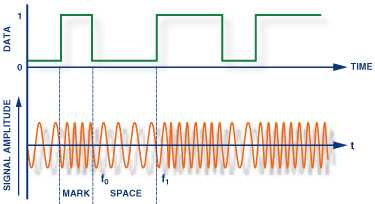
Frequency shift keying (FSK) shifts the carrier between two different frequencies called the mark and space frequencies, or fm and fs(Fig. 1c).
FM produces multiple sideband frequencies above and below the carrier frequency.
The bandwidth produced is a function of the highest modulating frequency including harmonics and the modulation index, which is:
m = Δf(T)
Δf is the frequency deviation or shift between the mark and space frequencies, or:
Δf = fs – fm
T is the bit time interval of the data or the reciprocal of the data rate (1/bit/s).
Smaller values of m produce fewer sidebands.
A popular version of FSK called minimum shift keying (MSK) specifies m = 0.5. Smaller values are also used such as m = 0.3.
Here are two ways to further improve the spectral efficiency for both ASK and FSK.
First, select data rates, carrier frequencies, and shift frequencies so there are no discontinuities in the sine carrier when changing from one binary state to another.
These discontinuities produce glitches that increase the harmonic content and the bandwidth.
The idea is to synchronize the stop and start times of the binary data with when the sine carrier is transitioning in amplitude or frequency at the zero crossing points.
This is called continuous phase or coherent operation. Both coherent ASK/OOK and coherent FSK have fewer harmonics and a narrower bandwidth than non-coherent signals.
A second technique is to filter the binary data prior to modulation. This rounds the signal off, lengthening the rise and fall times and reducing the harmonic content.
Special Gaussian and raised cosine low pass filters are used for this purpose. GSM cell phones widely use a popular combination, Gaussian filtered MSK (GMSK),
which allows a data rate of 270 kbits/s in a 200-kHz channel.
Binary Phase Shift Keying (BPSK) And Quadrature Phase Shift Keying (QPSK)
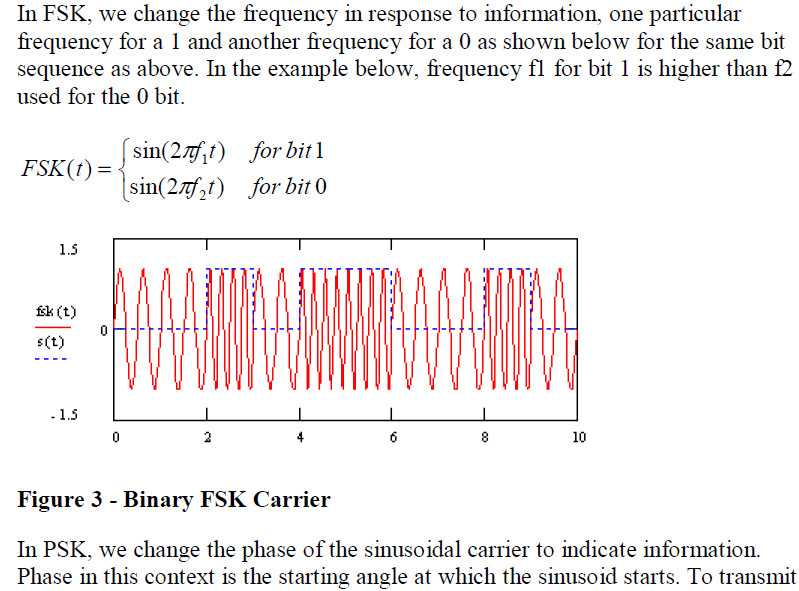
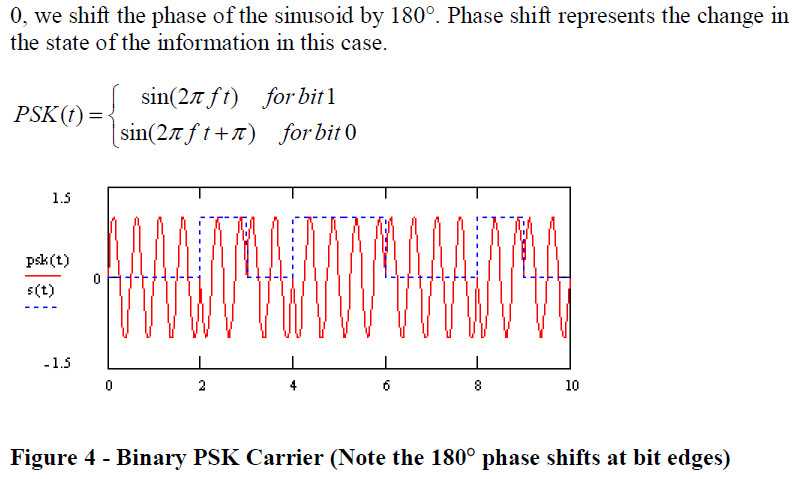
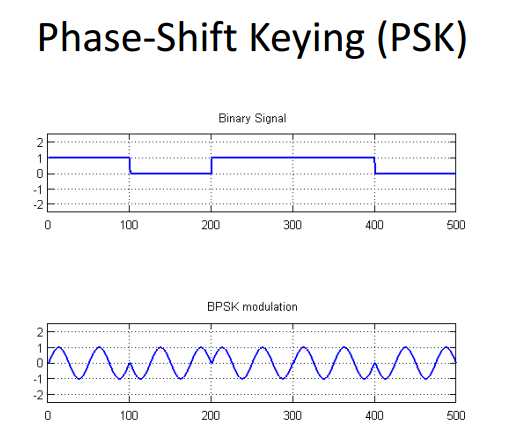
A very popular digital modulation scheme, binary phase shift keying (BPSK), shifts the carrier sine wave 180° for each change in binary state (Fig. 2).
BPSK is coherent as the phase transitions occur at the zero crossing points.
The proper demodulation of BPSK requires the signal to be compared to a sine carrier of the same phase. This involves carrier recovery and other complex circuitry.
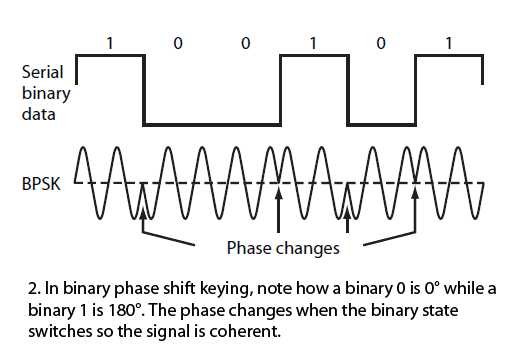
2. In binary phase shift keying, note how a binary 0 is 0° while a binary 1 is 180°.
The phase changes when the binary state switches so the signal is coherent.
A simpler version is differential BPSK or DPSK, where the received bit phase is compared to the phase of the previous bit signal.
BPSK is very spectrally efficient in that you can transmit at a data rate equal to the bandwidth or 1 bit/Hz.
In a popular variation of BPSK, quadrature PSK (QPSK), the modulator produces two sine carriers 90° apart.
The binary data modulates each phase, producing four unique sine signals shifted by 45° from one another.
The two phases are added together to produce the final signal. Each unique pair of bits generates a carrier with a different phase (Table 1).
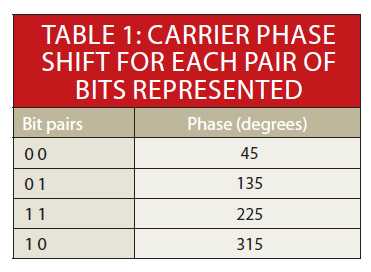
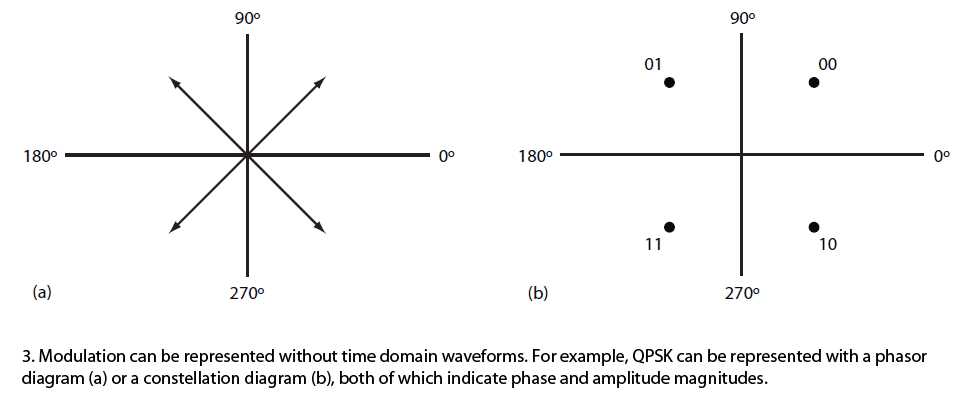
Figure 3a illustrates QPSK with a phasor diagram where the phasor represents the carrier sine amplitude peak and its position indicates the phase.
A constellation diagram in Figure 3b shows the same information.
QPSK is very spectrally efficient since each carrier phase represents two bits of data.
The spectral efficiency is 2 bits/Hz, meaning twice the data rate can be achieved in the same bandwidth as BPSK.
Data Rate And Baud Rate
The maximum theoretical data rate or channel capacity (C) in bits/s is a function of the channel bandwidth (B) channel in Hz and the signal-to-noise ratio (SNR):
C = B log2 (1 + SNR)
This is called the Shannon-Hartley law. The maximum data rate is directly proportional to the bandwidth and logarithmically proportional the SNR.
Noise greatly diminishes the data rate for a given bit error rate (BER).
Another key factor is the baud rate, or the number of modulation symbols transmitted per second.
The term symbol in modulation refers to one specific state of a sine carrier signal.
It can be an amplitude, a frequency, a phase, or some combination of them. Basic binary transmission uses one bit per symbol.
In ASK, a binary 0 is one amplitude and a binary 1 is another amplitude.
In FSK, a binary 0 is one carrier frequency and a binary 1 is another frequency.
BPSK uses a 0° shift for a binary 0 and a 180° shift for a binary 1.
In each of these cases there is one bit per symbol.
Data rate in bits/s is calculated as the reciprocal of the bit time (tb):
bits/s = 1/tb
With one symbol per bit, the baud rate is the same as the bit rate.
However, if you transmit more bits per symbol, the baud rate is slower than the bit rate by a factor equal to the number of bits per symbol.
For example, if 2 bits per symbol are transmitted, the baud rate is the bit rate divided by 2.
For instance, with QPSK a 70 Mb/s data stream is transmitted at a baud rate of 35 symbols/second.
Multiple Phase Shift Keying (M-PSK)
QPSK produces two bits per symbol, making it very spectrally efficient. QPSK can be referred to as 4-PSK because there are four amplitude-phase combinations. By using smaller phase shifts, more bits can be transmitted per symbol. Some popular variations are 8-PSK and 16-PSK.
8-PSK uses eight symbols with constant carrier amplitude 45° shifts between them, enabling three bits to be transmitted for each symbol. 16-PSK uses 22.5° shifts of constant amplitude carrier signals. This arrangement results in a transmission of 4 bits per symbol.
While Multiple Phase Shift Keying (M-PSK) is much more spectrally efficient, the greater the number of smaller phase shifts, the more difficult the signal is to demodulate in the presence of noise. The benefit of M-PSK is that the constant carrier amplitude means that more efficient nonlinear power amplification can be used.
Quadrature Amplitude Modulation (QAM)
The creation of symbols that are some combination of amplitude and phase can carry the concept of transmitting more bits per symbol further.
This method is called quadrature amplitude modulation (QAM).
For example, 8QAM uses four carrier phases plus two amplitude levels to transmit 3 bits per symbol.
Other popular variations are 16QAM, 64QAM, and 256QAM, which transmit 4, 6, and 8 bits per symbol respectively(Fig. 4).
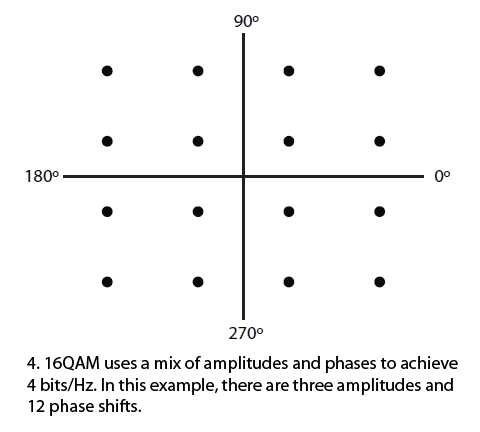
While QAM is enormously efficient of spectrum, it is more difficult to demodulate in the presence of noise, which is mostly random amplitude variations.
Linear power amplification is also required. QAM is very widely used in cable TV, Wi-Fi wireless local-area networks (LANs), satellites, and cellular telephone systems
to produce maximum data rate in limited bandwidths.
Amplitude Phase Shift Keying (APSK)
Amplitude phase shift keying (APSK), a variation of both M-PSK and QAM, was created in response to the need for an improved QAM.
Higher levels of QAM such as 16QAM and above have many different amplitude levels as well as phase shifts. These amplitude levels are more susceptible to noise.
Furthermore, these multiple levels require linear power amplifiers (PAs) that are less efficient than nonlinear (e.g., class C).
The fewer the number of amplitude levels or the smaller the difference between the amplitude levels, the greater the chance to operate in the nonlinear region of the PA to boost power level.
APSK uses fewer amplitude levels. It essentially arranges the symbols into two or more concentric rings with a constant phase offset θ.
For example, 16APSK uses a double-ring PSK format (Fig. 5). This is called 4-12 16APSK with four symbols in the center ring and 12 in the outer ring.
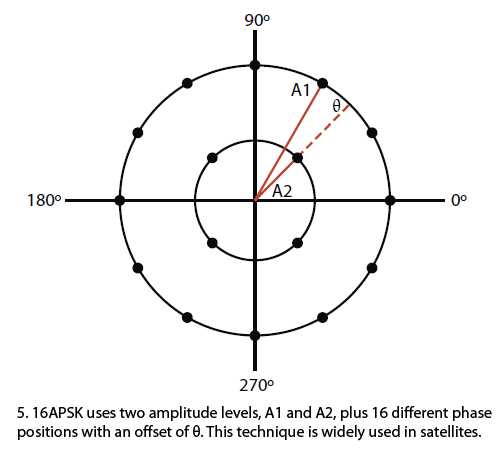
Two close amplitude levels allow the amplifier to operate closer to the nonlinear region, improving efficiency as well as power output.
APSK is used primarily in satellites since it is a good fit with the popular traveling wave tube (TWT) PAs.
Orthogonal Frequency Division Multiplexing (OFDM)
Orthogonal frequency division multiplexing (OFDM) combines modulation and multiplexing techniques to improve spectral efficiency.
A transmission channel is divided into many smaller subchannels or subcarriers. The subcarrier frequencies and spacings are chosen so they’re orthogonal to one another.
Their spectra won’t interfere with one another, then, so no guard bands are required (Fig. 6).
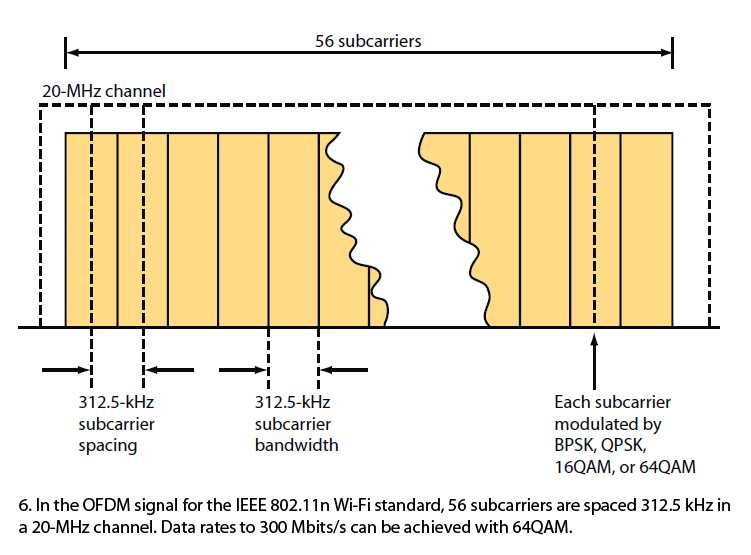
The serial digital data to be transmitted is subdivided into parallel slower data rate channels. These lower data rate signals are then used to modulate each subcarrier.
The most common forms of modulation are BPSK, QPSK, and several levels of QAM. BPSK, QPSK, 16QAM, and 64QAM are defined with 802.11n.
Data rates up to about 300 Mbits/s are possible with 64QAM.
The complex modulation process is only produced by digital signal processing (DSP) techniques.
An inverse fast Fourier transform (IFFT) generates the signal to be transmitted. An FFT process recovers the signal at the receiver.
OFDM is very spectrally efficient. That efficiency level depends on the number of subcarriers and the type of modulation, but it can be as high as 30 bits/s/Hz.
Because of the wide bandwidth it usually occupies and the large number of subcarriers, it also is less prone to signal loss due to fading, multipath reflections,
and similar effects common in UHF and microwave radio signal propagation.
Currently, OFDM is the most popular form of digital modulation.
It is used in Wi-Fi LANs, WiMAX broadband wireless, Long Term Evolution (LTE) 4G cellular systems, digital subscriber line (DSL) systems,
and in most power-line communications (PLC) applications. For more, see “Orthogonal Frequency-Division Multiplexing (OFDM): FAQ Tutorial.”
Determining Spectral Efficiency
Again, spectral efficiency is a measure of how quickly data can be transmitted in an assigned bandwidth, and the unit of measurement is bits/s/Hz (b/s/Hz).
Each type of modulation has a maximum theoretical spectral efficiency measure (Table 2).
ASK是幅移键控调制的简写,例如二进制的,把二进制符号0和1分别用不同的幅度来表示,就是ASK了。 而
OOK则是ASK调制的一个特例,把一个幅度取为0,另一个幅度为非0,就是OOK了。例如二进制符号0用不发射载波表示,二进制1用发射1表示。
ASK跟OOK的频谱都比较宽。
FSK是频移键控调制的简写,即用不同的频率来表示不同的符号。例如2KHz表示符号0,3KHz表示符号1。
GFSK是高斯频移键控的简写,在调制之前通过一个高斯低通滤波器来限制信号的频谱宽度。
FSK(Frequency-shift keying):频移键控。就是用数字信号去调制载波的频率。是信息传输中使用得较早的一种调制方式,它的主要优点是:
实现起来较容易,抗噪声与抗衰减的性能较好。在中低速数据传输中得到了广泛的应用。
ASK: 幅移键控ASK (Amplitude Shift Keying)
ASK指的是振幅键控方式。这种调制方式是根据信号的不同,调节正弦波的幅度。
幅度键控可以通过乘法器和开关电路来实现。载波在数字信号1或0的控制下通或断,在信号为1的状态载波接通,此时传输信道上有载波出现;
在信号为0的状态下,载波被关断,此时传输信道上无载波传送。那么在接收端我们就可以根据载波的有无还原出数字信号的1和0。
对于二进制幅度键控信号的频带宽度为二进制基带信号宽度的两倍。
幅移键控法(ASK)的载波幅度是随着调制信号而变化的, 其最简单的形式是,载波在二进制调制信号控制下通断, 此时又可称作开关键控法(OOK)。
多电平MASK调制方式是一种比较高效的传输方式,但由于它的抗噪声能力较差,尤其是抗衰落的能力不强,因而一般只适宜在恒参信道下采用。
ASK定义
“移幅键控”又称为“振幅键控”(Amplitude Shift Keying),记为ASK,是调制技术的一种常用方式。
如果数字调制信号的可能状态与二进制信息符号或它的相应基带信号状态一一对应,则称其已调信号为二进制数字调制信号。
用二进制信息符号进行键控,称为二进制振幅键控,用2ASK表示。
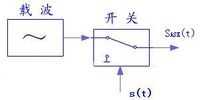
图1:移幅键控原理图
在“移幅键控”方式中,当“1”出现时接通振幅为A的载波,“0”出现时关断载波,这相当于将原基带信号(脉冲列)频谱搬到了载波的两侧。
移幅键控(ASK)相当于模拟信号中的调幅,只不过与载频信号相乘的是二进制数码而已。
移幅就是把频率、相位作为常量,而把振幅作为变量,信息比特是通过载波的幅度来传递的。
二进制振幅键控(2ASK),由于调制信号只有0或1两个电平,相乘的结果相当于将载频或者关断,或者接通,
它的实际意义是当调制的数字信号为“1”时,传输载波;当调制的数字信号为“0”时,不传输载波。
原理如图1所示,其中s(t)为基带矩形脉冲。一般载波信号用余弦信号,而调制信号是把数字序列转换成单极性的基带矩形脉冲序列,
而这个通断键控的作用就是把这个输出与载波相乘,就可以把频谱搬移到载波频率附近,实现2ASK。实现后的2ASK波形如图2所示。
图2:输出后的2ASK波形
移幅键控这种调制技术工作的最简单和最常用的形式是开关,载波存在用“1”代表,载波不存在用“0”代表。
这种类型的调制称为开关键控(OOK),是最节省能量的调制方式,因为只有在发送“1”时辐射能量。
幅移键控需要很高的信噪比才能解调信号,因为根据其本身特性,大部分信号都是以很低的功率进行发射的。
ASK调制射频系统的优点是发射和接收设备的结构简单,并且功耗比较低。
但不幸的是,ASK/OOK调制系统所占用的带宽低于500kHz或着峰值密度根本不会落入“数字调制系统”要求的范围。
这表明ASK/OOK调制系统的发射功率被限制在50mV/m,或者必须采用一些FHSS技术以满足FCC的15.247条款的要求。
OOK On-Off Keying
OOK是ASK调制的一个特例,把一个幅度取为0,另一个幅度为非0,就是OOK。
二进制启闭键控(OOK:On-Off Keying)又名二进制振幅键控(2ASK),它是以单极性不归零码序列来控制正弦载波的开启与关闭。
该调制方式的出现比模拟调制方式还早,Morse码的无线电传输就是使用该调制方式。
由于OOK的抗噪声性能不如其他调制方式,所以该调制方式在目前的卫星通信、数字微波通信中没有被采用,
但是由于该调制方式的实现简单,在光纤通信系统中,振幅键控方式却获得广泛应用。
该调制方式的分析方法是基本的,因而可从OOK调制方式入门来研究数字调制的基本理论。
FSK频移键控
中文名称:频移键控
英文名称:frequency-shift keying;
正弦振荡的频率在一组离散值间改变的角度调制,其中每一离散值表示时间离散调制信号的一种特征状态。
应用学科:通信科技(一级学科);通信原理与基本技术(二级学科)
频移键控,英文缩写FSK
频移键控是利用两个不同频率F1和F2的振荡源来代表信号1和0。
用数字信号的1和0去控制两个独立的振荡源交替输出。
对二进制的频移键控调制方式,其有效带宽为B=2xF+2Fb,xF是二进制基带信号的带宽也是FSK信号的最大频偏,
由于数字信号的带宽即Fb值大,所以二进制频移键控的信号带宽比较大,频带利用率小。
Binary Keying
Binary Keying definition:
The bits in a message stream switch the modulation parameters (amplitude, freque ncy and phase) from one state to another.
This process is called binary keying.
Binary keying is a process that makes the values of amplitude, phase or frequency of the carrier signal change
in sympathy with the values of the bits in the binary signal tream.
Basic actions can be classified as:
– ASK – Amplitude Shift Keying
– PSK – Phase Shift Keying
– FSK – Frequency Shift Keying
- OOK - On-Off Keying is also known as Amplitude Shift Keying (ASK)
- BPSK - Binary or Bi-Phase Shift Keying
- QPSK - Quadrature Phase Shift Keying
- MSK - Minimum Shift Keying
- DPSK - Differential PSK
- 8PSK - 8 Phase Shift Keying
http://www.cse.iitk.ac.in/users/dheeraj/cs425/lec03.html
A modem (modulator-demodulator) converts digital data to analog signal. There are 3 ways to modulate a digital signal on an analog carrier signal.
Amplitude shift keying (ASK):
is a form of modulation which represents digital data as variations in the amplitude of a carrier wave.
Two different amplitudes of carrier frequency represent ‘0‘ , ‘1‘.
Frequency shift keying (FSK):
In Frequency Shift Keying, the change in frequency define different digits. Two different frequencies near carrier frequency represent ‘0‘ ,‘‘1‘.
Phase shift keying (PSK):
The phase of the carrier is discretely varied in relation either to a reference phase or to the phase of the immediately preceding signal element,
in accordance with data being transmitted. Phase of carrier signal is shifted to represent ‘0‘ , ‘1‘.
The origin of all radio modulation techniques stem back to the AM and FM basic modulation. AM modulation changes the carrier frequency according to the data signal while the FM changes the carrier frequency according to the data signal. The information signal varies with time such as it could increase, decrease, or vanish to zero. The following signal represents a temperature increase as function of time. The temperature starts from zero at the bottom left and increases as time goes by. This analog temperature signal is converted to a voltage signal voltage(t) where the voltage tracks temperature as function of time:
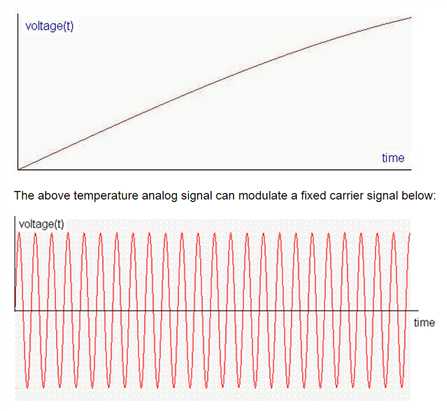
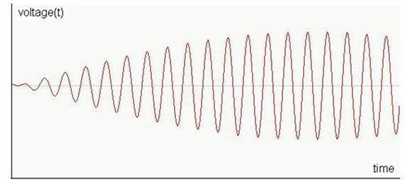
In AM modulation the carrier frequency is kept the same but the amplitude of the carrier is changed according to the temperature signal as follow:
In FM modulation the amplitude of the carrier is kept the same but the carrier frequency is changed according to the temperature signal as follow:
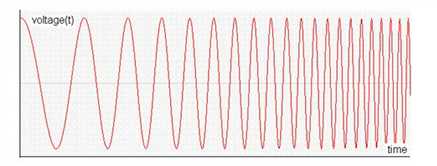
The temperature reading is then transmitted in form of radio signal and picked by the radio receiver. The receiver then extracts the information from the radio signal (AM or FM) by analyzing the variation in amplitude or frequency. The same rules of amplitude and frequency variations are followed when transmitting or receiving the data signal.
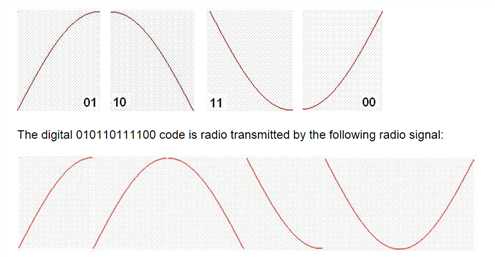
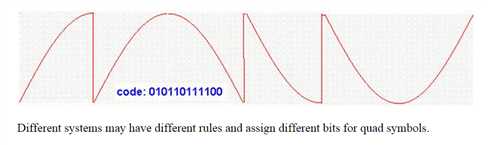
From the above methods of AM and FM modulations different forms of radio modulations are derived. The ON-OFF Keying (OOK) technique described above is a derived form of AM modulation. Frequency Hopping Spread Spectrum (FHSS) is an advanced form of FM modulation. Other modulation techniques such as Frequency Shift Keying (FSK), Phase Shift Keying (PSK), and In phase – Out of phase (IQ) modulation, Quadrate Phase Shift Keying (QPSK) modulation are also derived forms of FM modulation. The key is that the sine wave is divided into equal number of sections (4, 8, 16, 32) and the correct section is used to associate the data symbol to. Phase modulation and frequency modulation are related to one another and many rules equally apply to both of them. The sine wave can be divided into 4 quarters (Quad Modulation) each of the quad having 90 degrees. Here is how the sine wave is divided into 4 equal sections
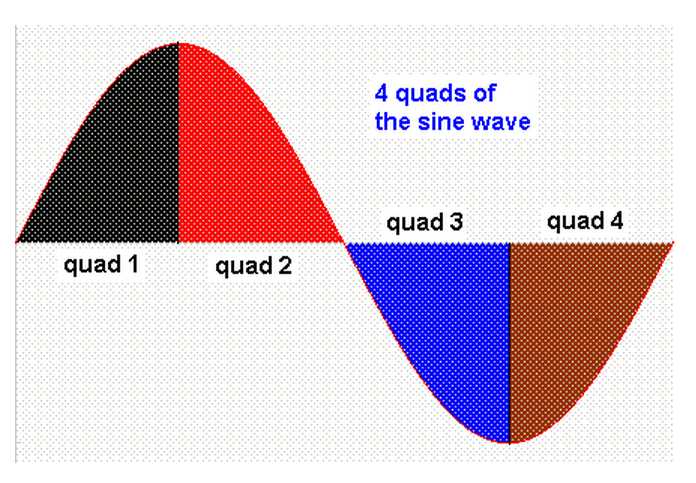
Details of the sine wave quads are used to carry useful information in the radio waves. These quads are transmitted wirelessly in series from the transmitter to the receiver.The IQ modulation could be use for very high speed communication. Each quad is assigned for example two digital bits as follow:
By doing so the power consumptions is minimized, communication speed is multiplied, but the possibility of transmit error is increased.
Here is how the above radio signal may look like using the oscilloscope:
Most current optical transmission systems encode the signal as a sequence of light pulses in a binary form.
This is called “on-off keying” (OOK).
Sometimes this is described as amplitude modulation, comparing it to AM radio.
In fact, the technique is nothing like AM radio.
An AM radio carries an analogue signal.
The amplitude of the carrier is continuously varied (modulated) in accordance with variations in the signal.
The receiver recovers the signal from the variations of the carrier.
But in an optical system, it is much more like a very simple form of digital baseband transmission in the electronic world.
The signal is there or it isn’t; beyond this the amplitude of the signal doesn’t matter.
In fairness, you can call OOK a special case of amplitude shift keying (ASK)
in which a number of discrete signal amplitude levels are used to carry a digital signal.
The signal power is kept large (m = 1) to indicate a binary ‘1‘
and small or zero (m = 0) to represent a binary ‘0‘.
An example is shown in Figure 3.6. In OOK, each symbol is a period of fixed duration
in which the signal power is either high or low.
Each OOK symbol represents one binary bit, though other types of symbols can convey more than one bit each.
Any circuit that can change the output power, such as a simple switch,can be used to create an OOK signal,
and any circuit that can detect power levels can demodulate (extract the data from) the signal.
For example, a diode (an electrical component that passes electrical current only in one direction
and blocks current flow in the opposite direction) can rectify a high-frequency signal, turning it into pulses of DC.
These pulses can be smoothed with a storage capacitor to produce an output signal that looks very much like the baseband signal m(t).
If the diode responds rapidly, it can be used at very high frequencies.
Modern diodes can operate up to over 1 GHz, allowing passive RFID tags to demodulate a reader signal using only a diode and capacitor.
Unmodified OOK is admirably simple and seems promising as a method of modulating a reader signal.
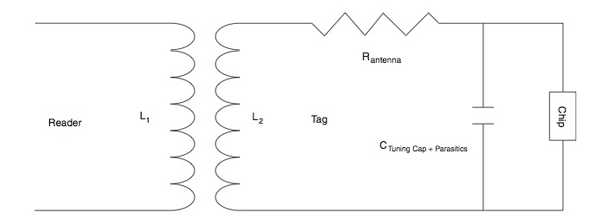
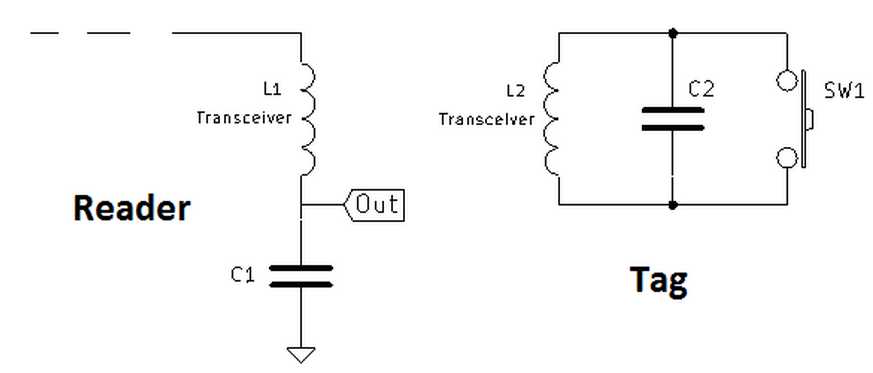
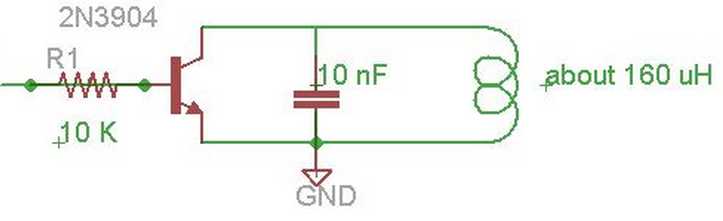
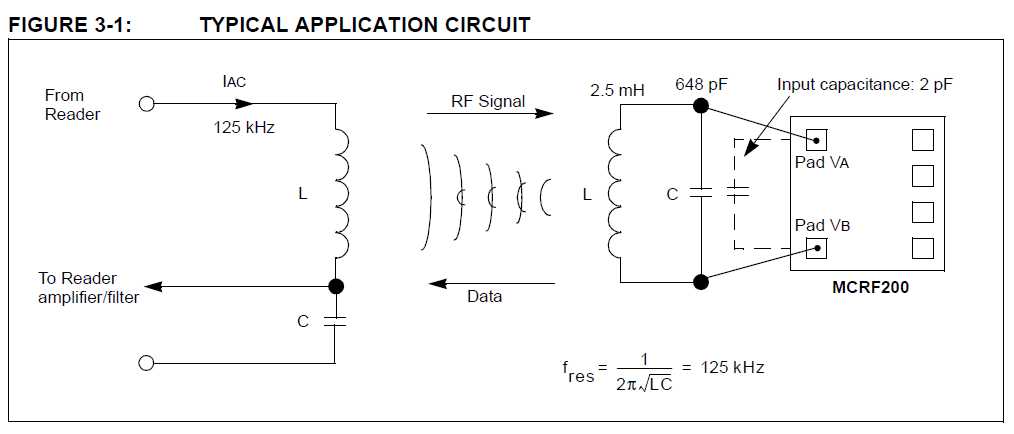
Because communications, power, communications, and synchronization flow through the antenna, antenna design is critical for successful RFID applications.
The typical parallel resonant circuit of a tag antenna comprises the inductance, resistance, and capacitance of the antenna loop (see Fig. 2)
with resonant frequency fres = 1/(2π√(L_2 C)).
In this equivalent circuit, the loop capacitance is the sum of the tuning capacitance and parasitic capacitances of the antenna coil and tag materials.
Antenna designers work to keep coil resistance to a minimum to increase the Q of the antenna and so maximize the energy available to the tag.
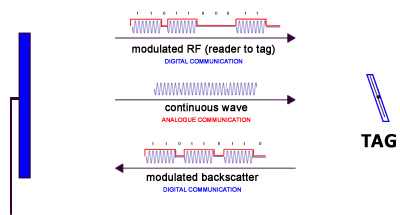
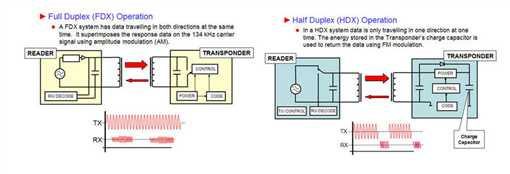
In passive RFID, the reader and tag antennas form a transformer,
so the RF signal transmitted by the reader energizes the parallel resonant circuit formed by the antenna coil and tag capacitance.
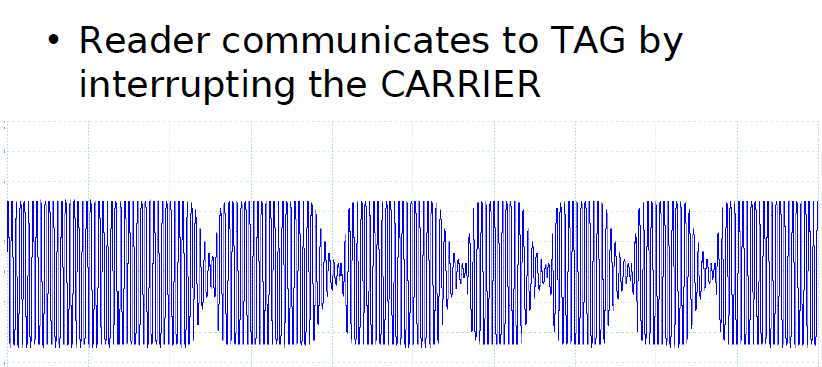
In passive RFID systems, readers communicate with tags by modulating the amplitude, phase, or frequency of the carrier,
according to the specific design of the RFID system.
Tags respond using methods that depend on whether the tag is operating in the near field or far field of the reader.
Near-field communications takes advantage of the inductive coupling of the reader and tag antennas.
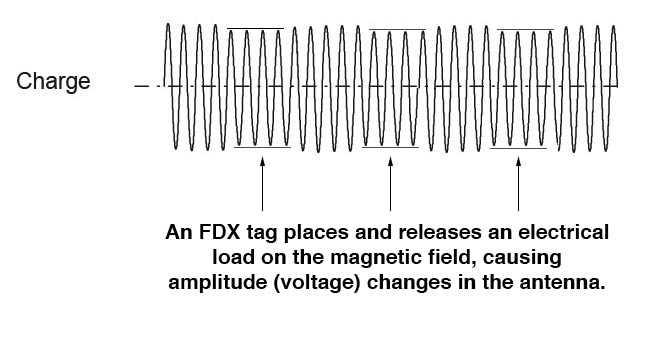
Here, the tag communicates its data by varying the load on its antenna coil,
which affects the voltage on the antenna — and signal seen by the reader.
By switching the coil load on and off rapidly, the tag can communicate its response as a modulation of the RF carrier (see Fig. 3).
Diverse tag designs implement widely different variations of this basic amplitude shift keying (ASK)
approach to support communications using other modulation methods including frequency shift keying (FSK),
phase shift keying (PSK), pulse position modulation (PPM),
pulse duration modulation (PDM), and phase jitter modulation (PJM), among others.
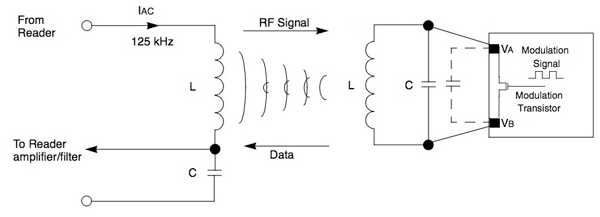
By driving a transistor with a modulating signal, a tag can vary the load on the antenna resonant circuit (a)
to transmit data as a modulated RF signal back to a reader.
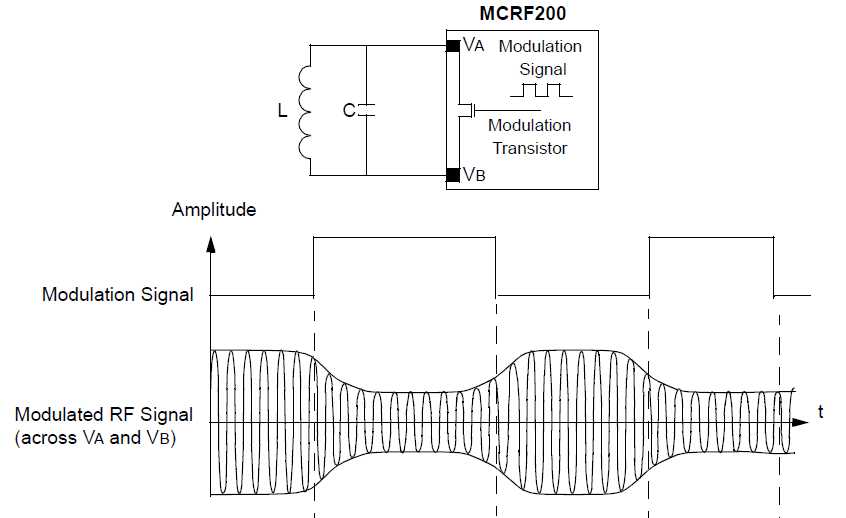
In this example, a tag with a 2.5-mH loop antenna connected to its antenna pads (VA and VB)
would require a 648-pF capacitor (assuming 2-pF parasitic capacitance illustrated by a dashed line)
to resonant at the 125-kHz operating frequency.
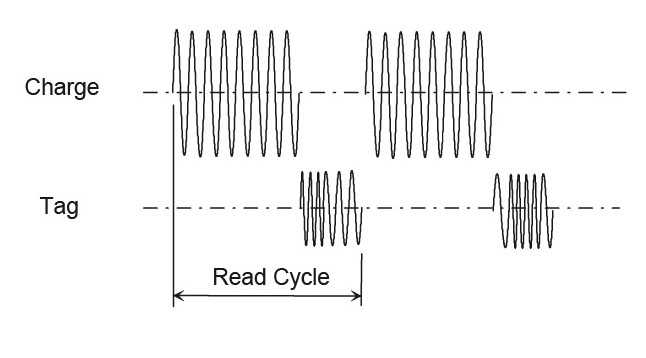
Often, tag communication methods require peak power beyond that acquired through inductive coupling.
In these cases, the tag design typically includes an additional capacitor.
During a power phase of the communications protocol, the reader carrier energizes the resonant circuit in the tag as usual,
but now this induced voltage is rectified by the tag chip to charge the capacitor.
At the end of the power phase, the tag transmits its data using the energy stored in the capacitor.
RFID systems operate according to one of two basic procedures:
full-duplex (FDX)/half-duplex (HDX) systems, and sequential systems (SEQ).
In full-duplex and half-duplex systems the transponder’s response is broadcast when the reader’s RF field is switched on.
Because the transponder’s signal to the receiver antenna can be extremely weak in comparison with the signal from the reader itself,
appropriate transmission procedures must be employed to differentiate the transponder’s signal from that of the reader.
In practice, data transfer from transponder to reader takes place using load modulation, load modulation using a subcarrier,
and also (sub)harmonics of the reader’s transmission frequency.
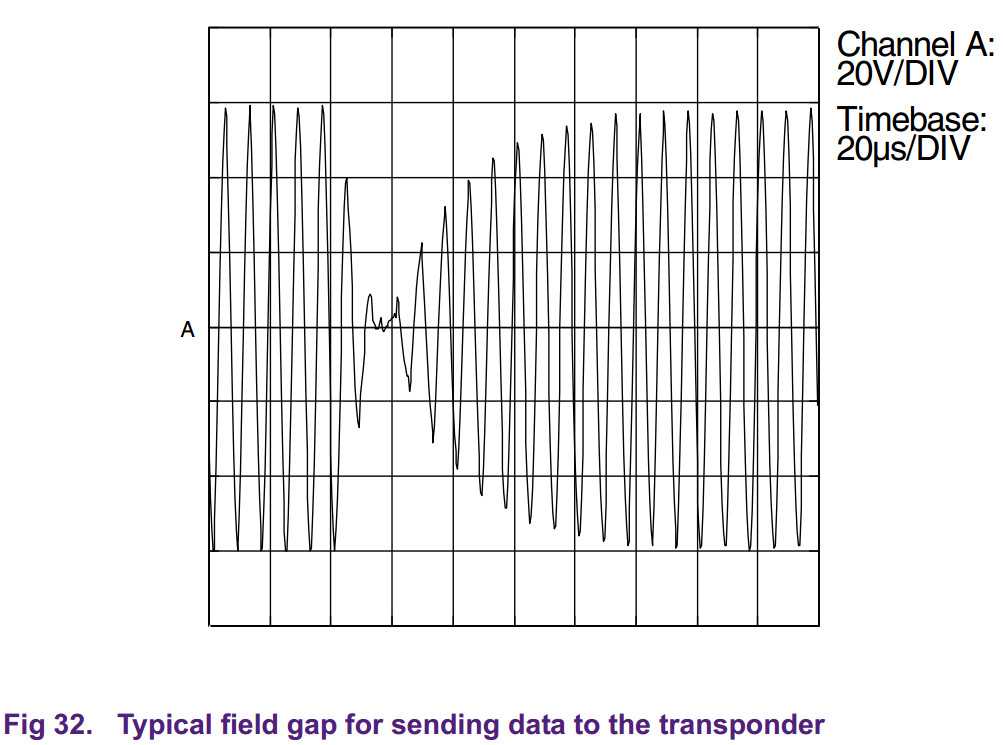
In contrast, sequential procedures employ a system whereby the field from the reader is switched off briefly at regular intervals.
These gaps are recognised by the transponder and used for sending data from the transponder to the reader.
The disadvantage of the sequential procedure is the loss of power to the transponder during the break in transmission,
which must be smoothed out by the provision of sufficient auxiliary capacitors or batteries.
This kind of sequential communications protocol contrasts with full-duplex and half-duplex communications,
which transmit the energy-providing carrier continuously while exchanging information simultaneously (full-duplex)
or in alternating periods (half-duplex) (see Fig. 4).
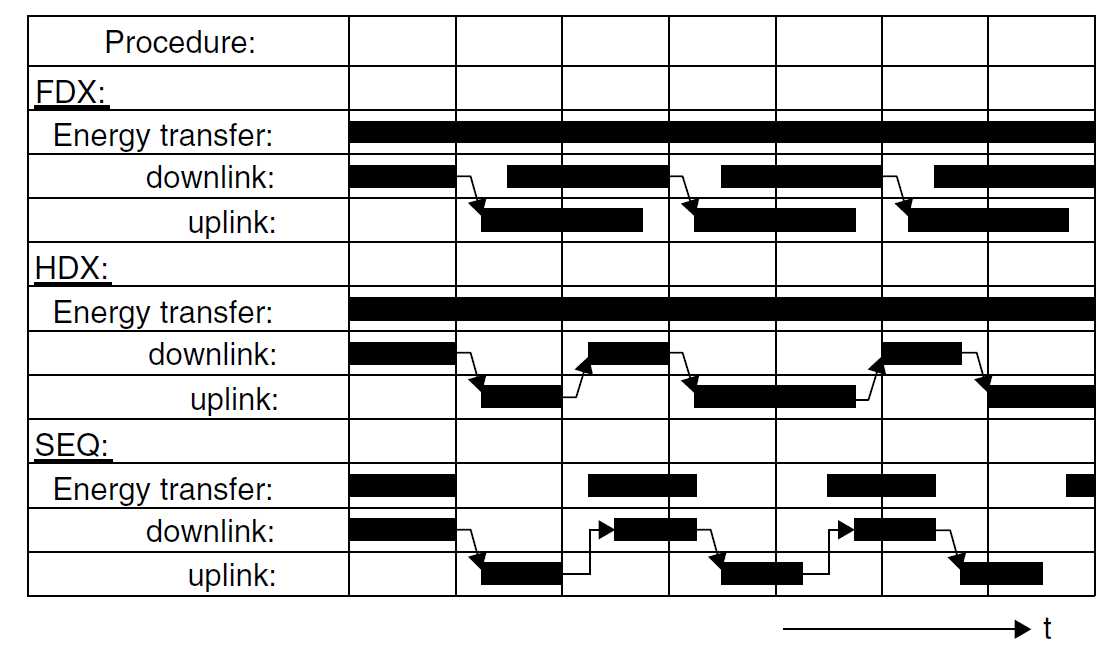
Representation of full duplex, half duplex and sequential systems over time.
Data transfer from the reader to the transponder is termed downlink,
while data transfer from the transponder to the reader is termed uplink
Fig. 4: Energy transfer through RF signal transmission occurs continuously in full-duplex (FDX) and half-duplex (HDX) communications,
but bursts in sequential (SEQ) systems such as RFID tags that use such power cycles to charge a capacitor for peak power demand.
Data transfer from the reader (down link) or from the tag (up link) occurs simultaneously
with FDX or in alternating periods with HDX and SEQ methods. (Source: Tektronix.)
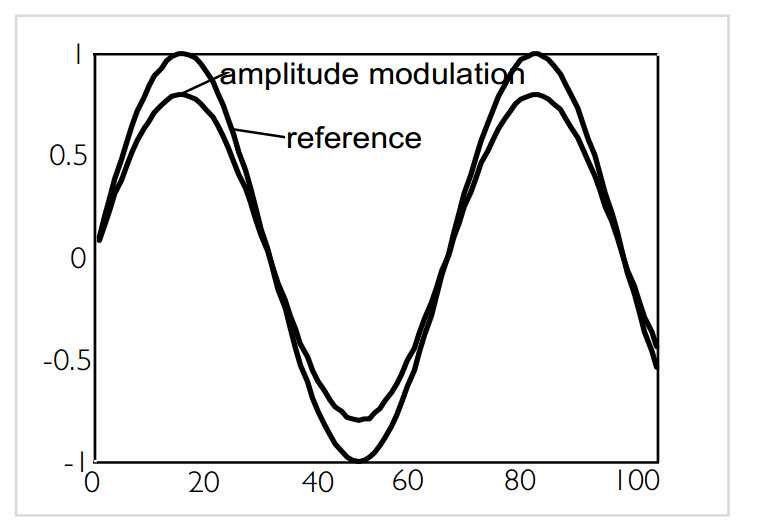
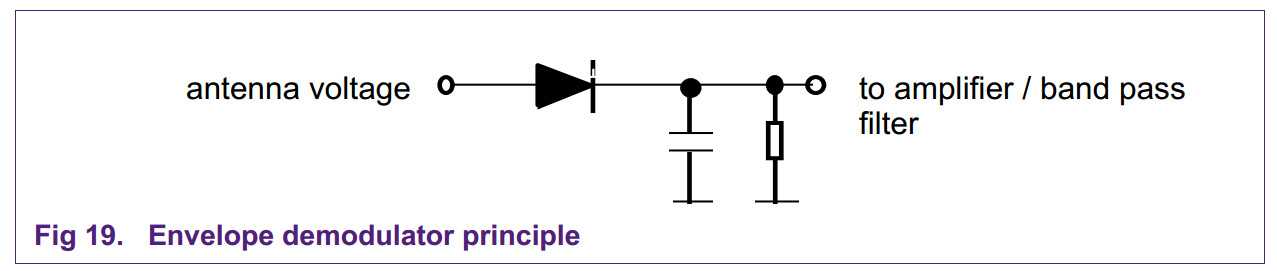
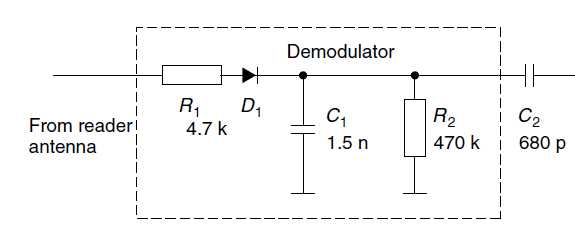
This amplitude modulation can be detected by a very basic and simple kind of demodulator, the so called envelope demodulator:
A backscatter tag communicates by modulating the scattered electromagnetic wave incident from the reader.
The scattered wave is modulated by changing the electrical impedance presented to the tag antenna.
A passive backscatter tag receives the power needed to operate from the wave incident from the reader.
Generation of load modulation in the transponder by switching the drain-source resistance of an FET on the chip.
The reader illustrated is designed for the detection of a subcarrier.
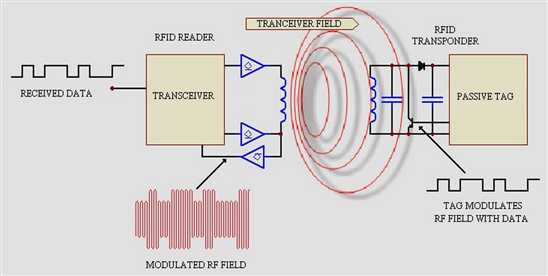
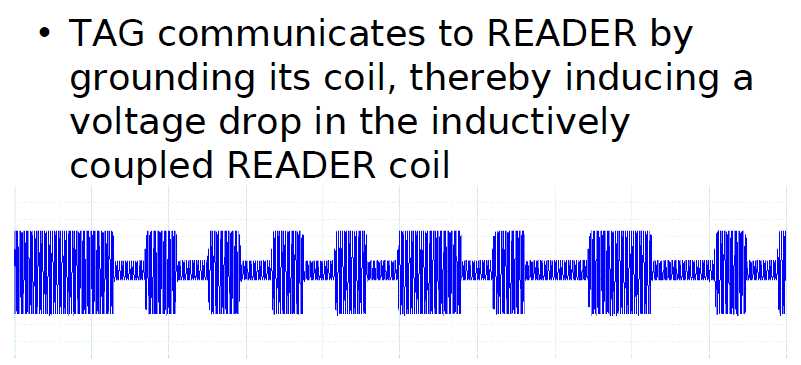
Shown is a RFID transceiver that communicates with a passive Tag.
Passive tags have no power source of their own and instead derive power from the incident electromagnetic field.
Commonly the heart of each tag is a microchip.
When the Tag enters the generated RF field it is able to draw enough power from the field
to access its internal memory and transmit its stored information.
When the transponder Tag draws power in this way the resultant interaction of the RF fields
causes the voltage at the transceiver antenna to drop in value.
This effect is utilized by the Tag to communicate its information to the reader.
The Tag is able to control the amount of power drawn from the field and by doing
so it can modulate the voltage sensed at the Transceiver according to the bit pattern it wishes to transmit.
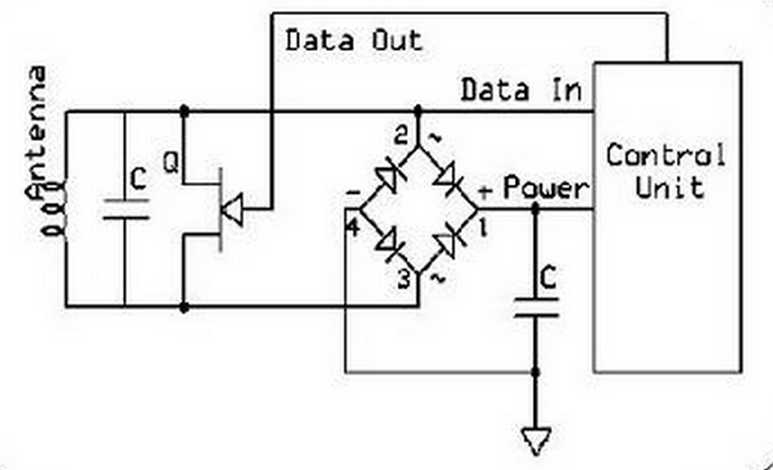
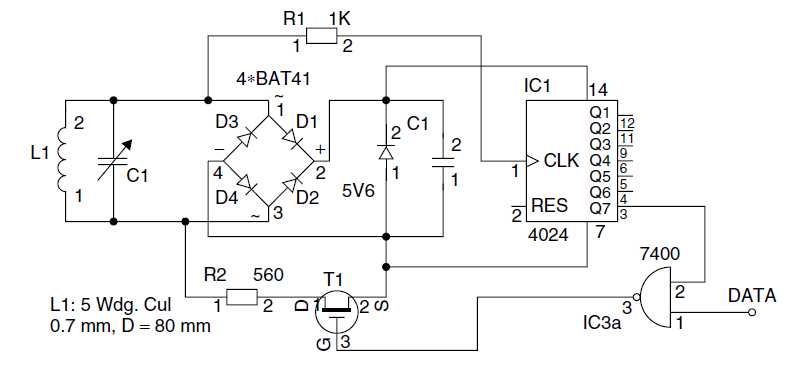
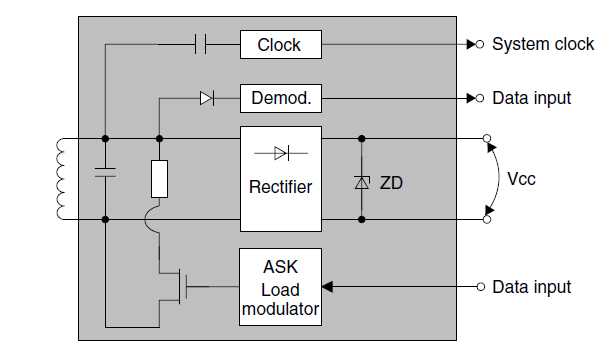
Sample circuit of the power supply and load modulator in a transponder
The voltage induced at the antenna coil L1 by the magnetic alternating field of the reader
is rectified using the bridge rectifier (D1–D4) and after additional smoothing (C1)
is available to the circuit as supply voltage. The parallel regulator (ZD 5V6) prevents
the supply voltage from being subject to an uncontrolled increase when the transponder approaches the reader antenna.
If the additional load resistor in the transponder is switched on and off at a very high elementary frequency fH,
then two spectral lines are created at a distance of ±fH around the transmission frequency of the reader,
and these can be easily detected (however fH must be less than fREADER).
In the terminology of radio technology the new elementary frequency is called a subcarrier.
Data transfer is by the ASK, FSK or PSK modulation of the subcarrier in time with the data flow.
This represents an amplitude modulation of the subcarrier.
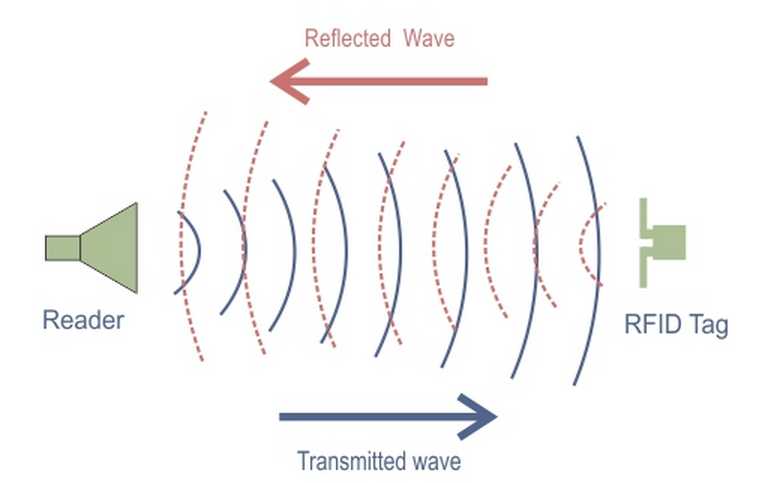
We know from the field of RADAR technology that electromagnetic waves
are reflected by objects with dimensions greater than around half the wave length of the wave.
The efficiency with which an object reflects electromagnetic waves is described by its reflection cross-section.
Objects that are in resonance with the wave front that hits them,
as is the case for antenna at the appropriate frequency for example, have a particularly large reflection cross-section.
Operating principle of a backscatter transponder.
The impedance of the chip is ‘modulated’ by switching the chip’s FET (Integrated Silicon Design, 1996)
BACKSCATTER MODULATION
This terminology refers to the communication method used by a passive RFID tag to send data to the reader using the same reader’s carrier signal.
The incoming RF carrier signal to the tag is transmitted back to the reader with tag’s data.
The RF voltage induced in the tag’s antenna is amplitude-modulated by the modulation signal (data) of tag device.
This amplitude-modulation can be achieved by using a modulation transistor across the LC resonant circuit or partially across the resonant circuit.
The changes in the voltage amplitude of tag’s antenna can affect on the voltage of the reader antenna.
By monitoring the changes in the reader antenna voltage (due to the tag’s modulation data), the data in the tag can be reconstructed.
The RF voltage link between reader and tag antennas are often compared to a weakly coupled transformer coils;
as the secondary winding (tag coil) is momentarily shunted, the primary winding (reader coil) experiences a momentary voltage drop.
Backscatter is one of the most widely used modulation schemes for modulating data on to rf carrier.
In this method of modulation, the tag coil (load) is shunted depending on the bit sequence received.
This in turn modulates the rf carrier amplitude as shown in the diagram below.
The reader detects the changes in the modulated carrier and recovers the data.
The above diagram provides a simplified modulated carrier signals from the RFID tag.
As seen in the diagram, the encoded binary digits modulate rf carrier.
A 1 is represented with high carrier level, and a 0 is represented by a low carrier level (tag coil shunted).
The reader demodulates the signals to recover the data, and note that this data is still encoded.
The reader decodes the data using suitable decoder,
and forwards it for further processing to a computer (or any backend server).
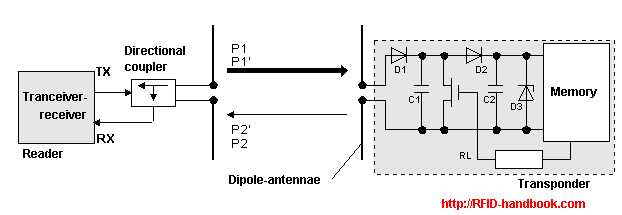
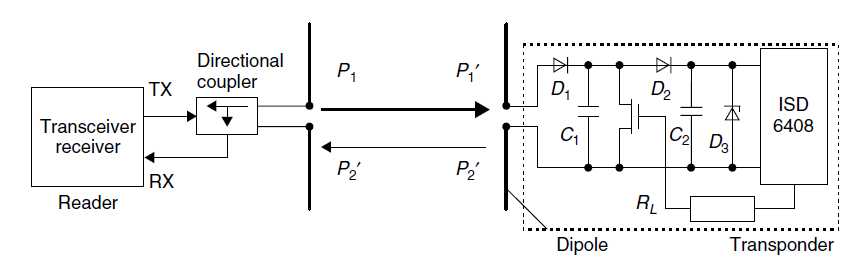
Power P1 is emitted from the reader‘s antenna, a small proportion of which (free space attenuation) reaches the transponder‘s antenna.
The power P1‘ is supplied to the antenna connections as HF voltage and after rectification by the diodes D1 and D2
this can be used as turn on voltage for the deactivation or activation of the power saving "power-down" mode.
The diodes used here are low barrier Schottky diodes, which have a particularly low threshold voltage.
The voltage obtained may also be sufficient to serve as a power supply for short ranges.
A proportion of the incoming power P1‘ is reflected by the antenna and returned as power P2.
The reflection characteristics (= reflection cross-section) of the antenna can be influenced by altering the load connected to the antenna.
In order to transmit data from the transponder to the reader,
a load resistor RL connected in parallel with the antenna is switched on and off in time with the data stream to be transmitted.
The amplitude of the power P2 reflected from the transponder can thus be modulated (modulated backscatter).
The power P2 reflected from the transponder is radiated into free space.
A small proportion of this (free space attenuation) is picked up by the reader‘s antenna.
The reflected signal therefore travels into the antenna connection of the reader in the "backwards direction"
and can be decoupled using a directional coupler and transferred to the receiver input of a reader.
The "forward" signal of the transmitter, which is stronger by powers of ten, is to a large degree suppressed by the directional coupler.
The ratio of power transmitted by the reader and power returning from the transponder (P1 / P2) can be estimated using the radar equation
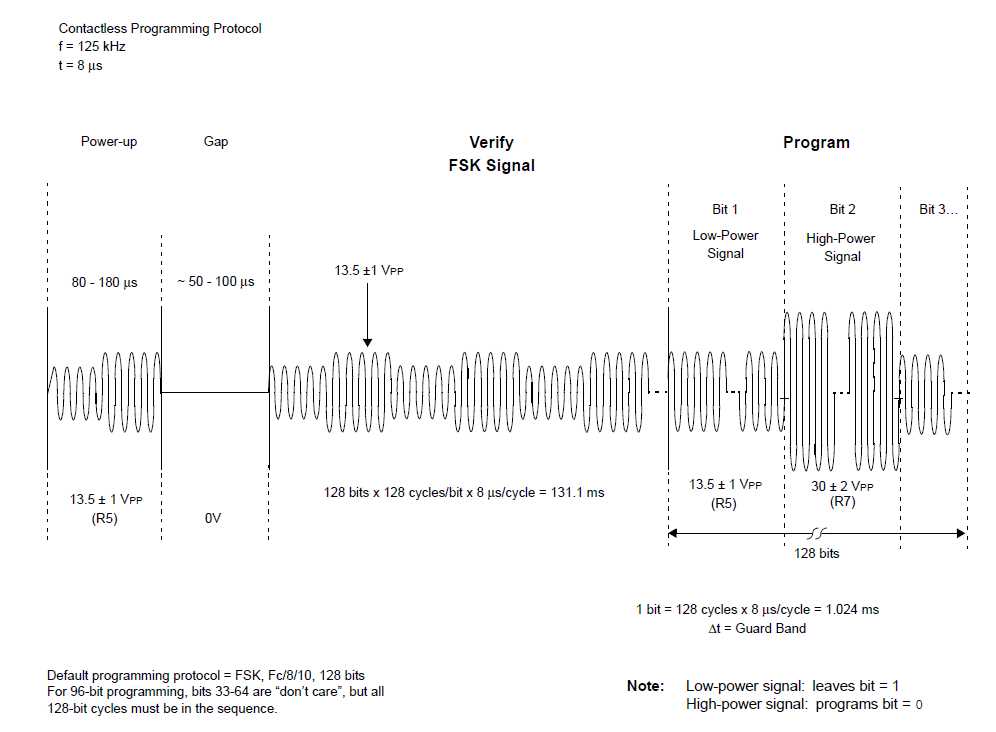
Lets take an example of passive transponder data transmission which sends out data at frequency of 134.2kHz.
Reader or so called interrogator sends out 134.2kHz pulse which lasts for 50ms which is used
to power passive tag and start up the transponder controller.
Received energy is stored in cap pacitor inside transponder.
After this 50ms pulse ends, transponder transmits data back over period 20ms.
After tag transmitting is over, capacitor discharges and resets for next readings.
Passive Tag transmission is usually performed by switching low resistance across the antenna coil.
The change of voltage across antenna generates radio frequency which is referred as backscattering.
Data is read from tags ROM memory and transmitted serially by switching coil load switch.
Coil switch is driven by carrier clock source which is modulated with data from serial ROM memory data.
In other end the reader removes(demodulates) the carrier signal, filters and cleans up the signal with Schmitt trigger.
Then signal enters digital section, where CRC code is checked and decoded.
Passive RFID tags vary in how they communicate data to RFID readers and
how they receive power from the RFID reader‘s inductive or electromagnetic field.
This is commonly performed via two basic methods:
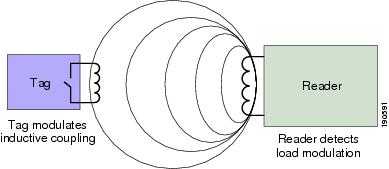
Passive Tag Load Modulation
Load modulation and inductive coupling in the near field—In this approach,
the RFID reader provides a short-range alternating current magnetic field
that the passive RFID tag uses for both power and as a communication medium.
Via a technique known as inductive (or near-field) coupling ,
this magnetic field induces a voltage in the antenna coil of the RFID tag,
which in turn powers the tag.
The tag transmits its information to the RFID reader by taking advantage of the fact
that each time the tag draws energy from the RFID reader‘s magnetic field,
the RFID reader itself can detect a corresponding voltage drop across its antenna leads.
Capitalizing on this phenomenon, the tag can communicate binary information to the reader
by switching ON and OFF a load resistor to perform load modulation.
When the tag performs load modulation, the RFID reader detects this action
as amplitude modulation of the signal voltage at the reader‘s antenna.
Load modulation and inductive coupling can be found among passive RFID tags
using frequencies from 125 to 135 kHz and 13.56 MHz.
Limitations that exist with regard to the use of such low frequencies include the necessity to use larger antennas,
low data rate and bandwidth and a rather dramatic decay in the strength of the electromagnetic field (1/r6),
where r represents the distance between a low frequency interrogator and a passive RFID tag.
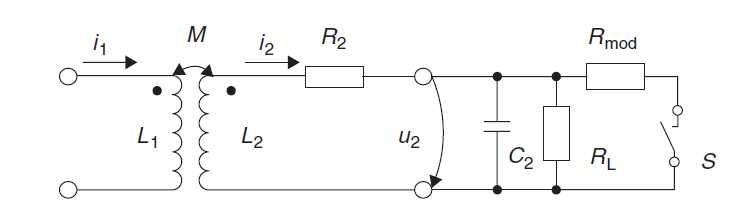
Ohmic Load Modulation
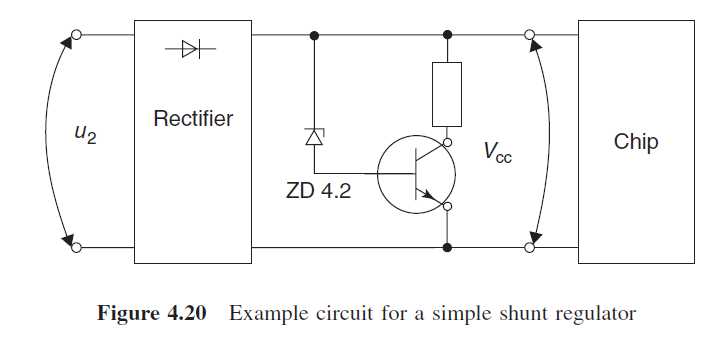
Equivalent circuit diagram for a transponder with load modulator.
Switch S is closed in time with the data stream – or a modulated subcarrier signal – for the transmission of data
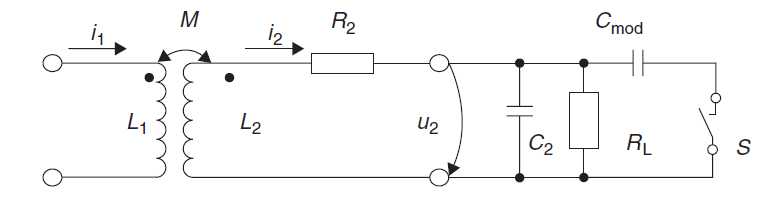
Capacitive Load Modulation
Equivalent circuit diagram for a transponder with capacitive load modulator.
To transmit data the switch S is closed in time with the data stream – or a modulated subcarrier signal
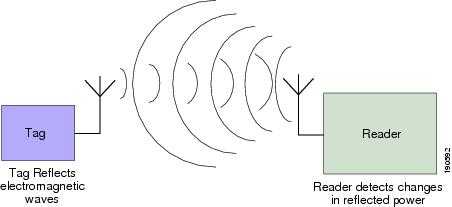
Passive Tag Backscatter Modulation
Backscatter modulation and electromagnetic coupling in the far field—In this approach),
the RFID reader provides a medium-range electromagnetic field that the passive RFID tag
uses for both power and a communication medium.
Via a technique known as electromagnetic (or far-field) coupling,
the passive RFID tag draws energy from the electromagnetic field of the RFID reader.
However, the energy contained in the incoming electromagnetic field
is partially reflected back to the RFID reader by the passive tag antenna.
The precise characteristics of this reflection depend on the load (resistance)connected to the antenna.
The tag varies the size of the load that is placed in parallel with the antenna
in order to apply amplitude modulation to the reflected electromagnetic waves,
thereby enabling it to communicate information payloads back to the RFID reader via backscatter modulation.
Tags using backscatter modulation and electromagnetic coupling typically
provide longer range than inductively coupled tags, and can be found most commonly among
passive RFID tags operating at 868 MHz and higher frequencies.
Far field coupled tags typically provide significantly longer range than inductively coupled tags,
principally due to the much slower rate of attenuation (1/r2) associated with the electromagnetic far-field.
Antennas used for tag employing far field coupling are typically smaller than their inductively coupled counterparts.
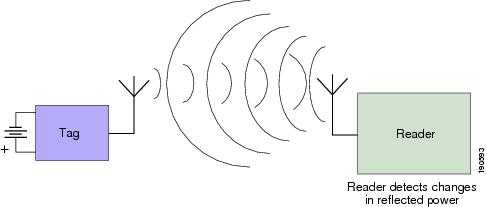
Backscatter Modulation in Semi-Passive RFID Tags
Semi-passive RFID tags overcome two key disadvantages of pure passive RFID tag designs:
•![]() The lack of a continuous source of power for onboard telemetry and sensor asset monitoring circuits.
The lack of a continuous source of power for onboard telemetry and sensor asset monitoring circuits.
•![]() Short range.
Short range.
Semi-passive tags differ from passive tags in that they use an onboard battery
to provide power to communication and ancillary support circuits,
such as temperature and shock monitoring.
It is interesting to note that although they employ an onboard power source,
semi-passive RFID tags do not use it to directly generate RF electromagnetic energy.
Rather, these tags typically make use of backscatter modulation and
reflect electromagnetic energy from the RFID reader to generate a tag response
similar to that of standard passive tags.
The onboard battery is used only to provide power for telemetry
and backscatter enabling circuits on the tag, not to generate RF energy directly.
A digitally modulated signal is a stream of distinct symbols.
A simple example with substantial relevance for RFID is on/off keying (OOK).
Most current optical transmission systems encode the signal as a sequence of light pulses in a binary form.
This is called “on-off keying” (OOK).
Sometimes this is described as amplitude modulation, comparing it to AM radio.
In fact, the technique is nothing like AM radio.
An AM radio carries an analogue signal.
The amplitude of the carrier is continuously varied (modulated) in accordance with variations in the signal.
The receiver recovers the signal from the variations of the carrier.
But in an optical system, it is much more like a very simple form of digital baseband transmission in the electronic world.
The signal is there or it isn’t; beyond this the amplitude of the signal doesn’t matter.
In fairness, you can call OOK a special case of amplitude shift keying (ASK)
in which a number of discrete signal amplitude levels are used to carry a digital signal.
The signal power is kept large (m = 1) to indicate a binary ‘1‘
and small or zero (m = 0) to represent a binary ‘0‘.
An example is shown in Figure 3.6. In OOK, each symbol is a period of fixed duration
in which the signal power is either high or low.
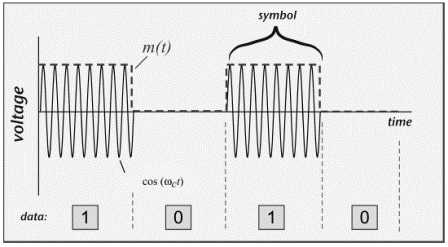
Each OOK symbol represents one binary bit, though other types of symbols can convey more than one bit each.
Any circuit that can change the output power, such as a simple switch,can be used to create an OOK signal,
and any circuit that can detect power levels can demodulate (extract the data from) the signal.
For example, a diode (an electrical component that passes electrical current only in one direction
and blocks current flow in the opposite direction) can rectify a high-frequency signal, turning it into pulses of DC.
These pulses can be smoothed with a storage capacitor to produce an output signal that looks very much like the baseband signal m(t).
If the diode responds rapidly, it can be used at very high frequencies.
Modern diodes can operate up to over 1 GHz, allowing passive RFID tags to demodulate a reader signal using only a diode and capacitor.
Unmodified OOK is admirably simple and seems promising as a method of modulating a reader signal.
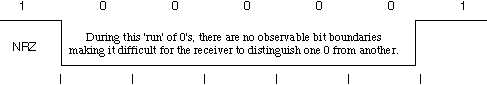
However, there is a problem with OOK for passive RFID.
A passive RFID tag depends on power obtained from the reader to run its circuitry.
If that power is interrupted, the tag cannot operate.
However, imagine the case of an OOK signal containing a long string of binary 0s:
in this case, m = 0 for as long as the data remains 0.
The tag will receive no power during this time.
If the data remains ‘0‘ for too long, the tag will power off and need to be restarted,
a situation not likely to be conducive to reliable operation.
Even when some binary 1s are present, the power level delivered to the tag is strongly data dependent, an undesirable trait.
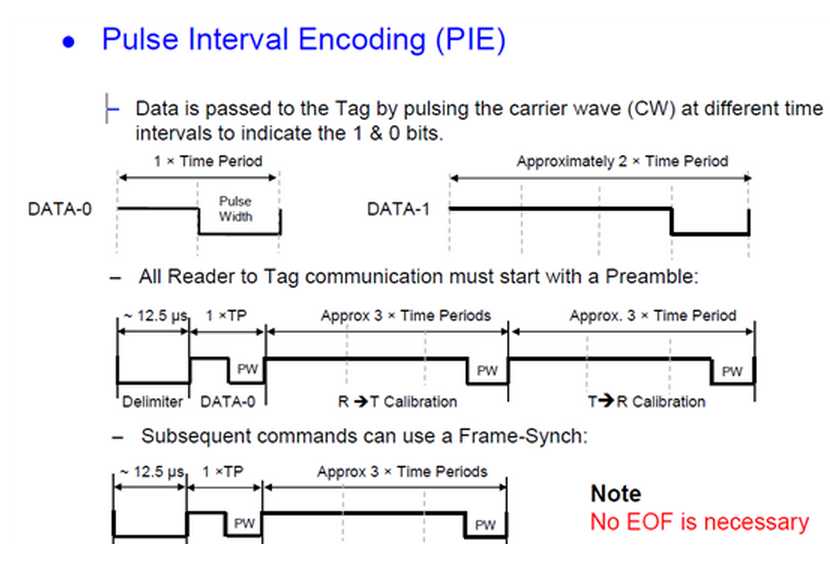
(Figure 3.7) Pulse-interval Coding Baseband Symbols (the function m(t))
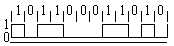
A common solution to the power problem is to code the binary data prior to modulation.
One RFID coding approach is known as pulse-interval encoding (PIE).
A binary ‘1‘ is coded as a short power-off pulse following a long full-power interval,
and a binary ‘0‘ is coded as a shorter full-power interval with the same power-off pulse (Figure 3.7).
The resulting coded baseband signal m(t) is then used to modulate the carrier (Figure 3.8).
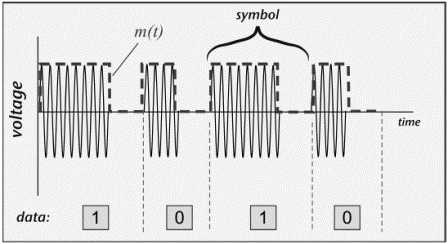
Figure 3.8 Pulse-interval Coding with OOK Modulation of a Carrier Wave
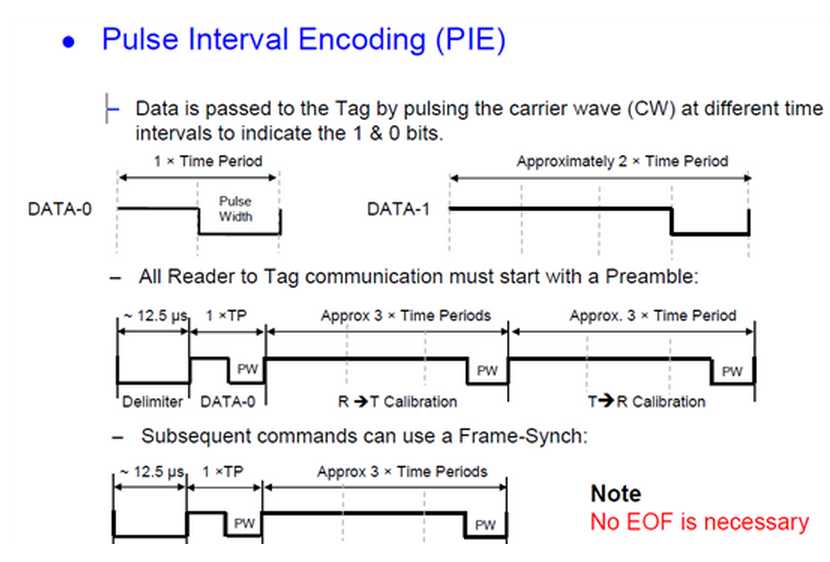
PIE using equal low and high pulses for a ‘0‘ ensures that at least 50% of the maximum power
is delivered to the tag even when the data being transmitted contains long strings of zeros,
and if the high is three times as long for a ‘1‘, a random stream of equally mixed binary data
will provide about 63% of peak power. Note that in this case, the data rate becomes dependent on the data:
a stream of binary 0s will be transmitted more rapidly than a stream of binary 1s.
A single symbol has two features—the off-time and on-time—but still conveys only one binary bit.
(This scheme is used in EPCglobal Class 1 Generation 2 readers.
Other passive RFID standards use slightly different coding schemes,
all generally characterized by the desire to have the reader power on as much as possible to power the tag.)
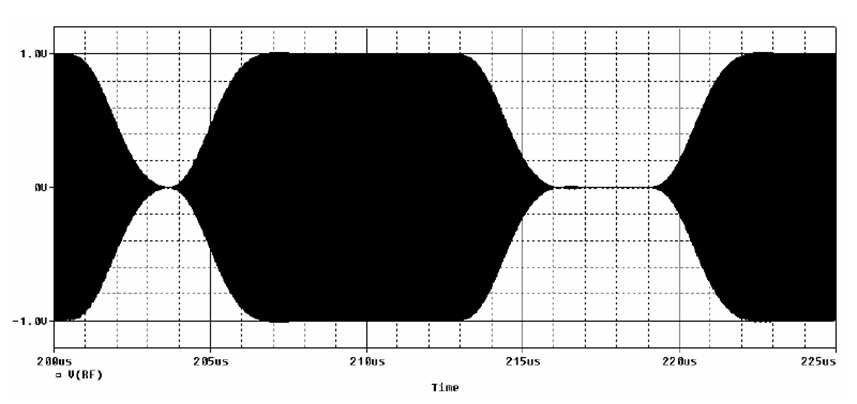
Reader RF signal, 100% modulation
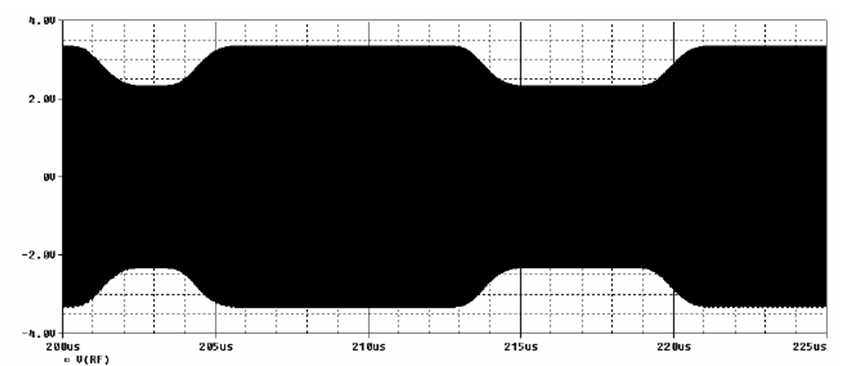
Reader RF signal, 20% modulation
Data transfer reader → transponder
Data is sent in driection from basestation to transponder by modulatating the magnetic field ("On/Off Keying, 100% modulation)
respectively switching off the field for short periods of time.
During that time, the transponder energy and clock supply is provided by transponder resonant circuitry.
The data is coded into the postion and/or distance of these field gaps.
A field gap is started by switching off the antenna drivers.
After this, the energy stored in the basestation antenna resonant circuitry is cut down by clipping diodes in driver stages.
Therefore the field strength decays rapidly to zero.
After switching the drivers on again, the resonance circuitry energy has to be build up again.
The time needed for that depends on the quality factor of the antenna.
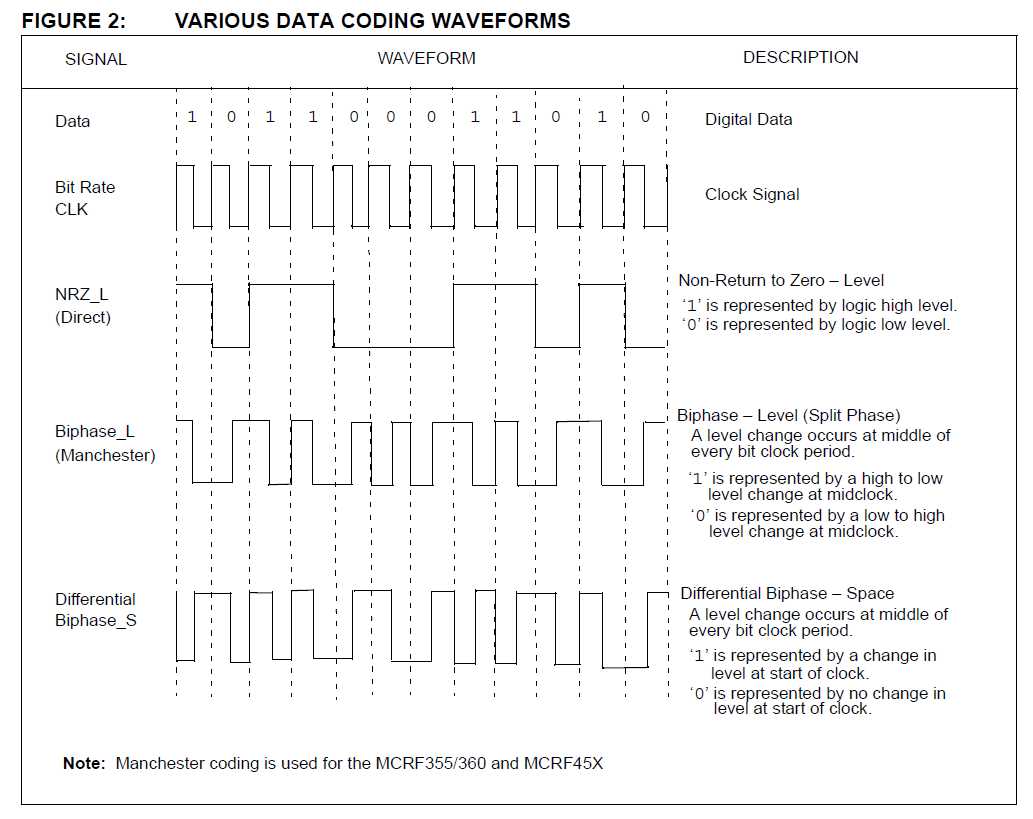
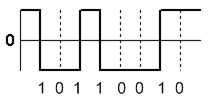
DATA MODULATION FOR 125 kHz DEVICES
Although all the data is transferred to the host by amplitude-modulating the carrier (backscatter modulation),
the actual modulation of 1’s and 0’s is accomplished with three additional modulation methods:
1. Direct.
In direct modulation, the Amplitude Modulation of the backscatter approach is the only modulation used.
A high in the envelope is a ‘1’ and a low is a ‘0’. Direct modulation can provide a high data rate but low noise immunity.
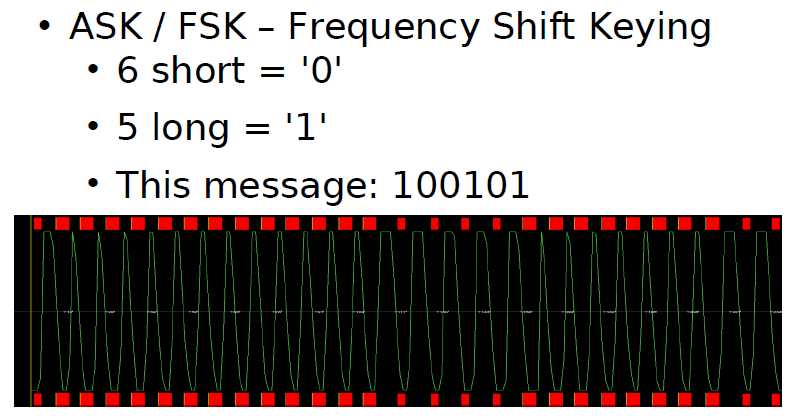
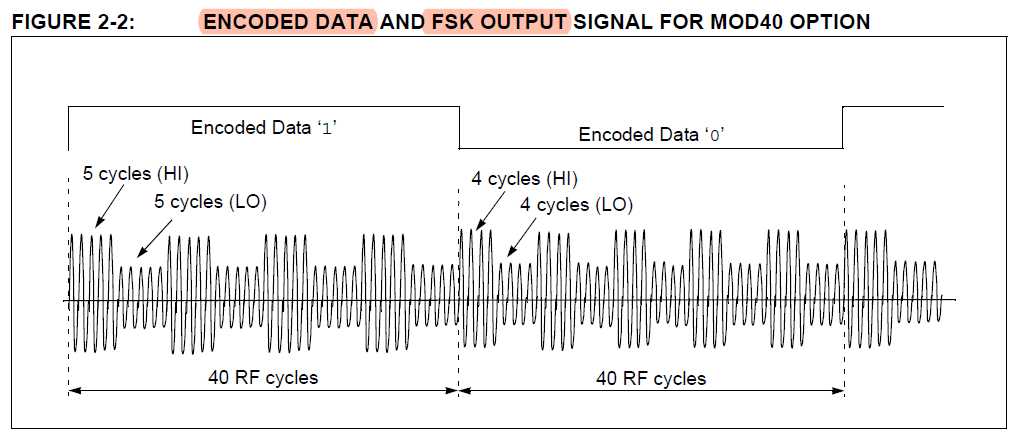
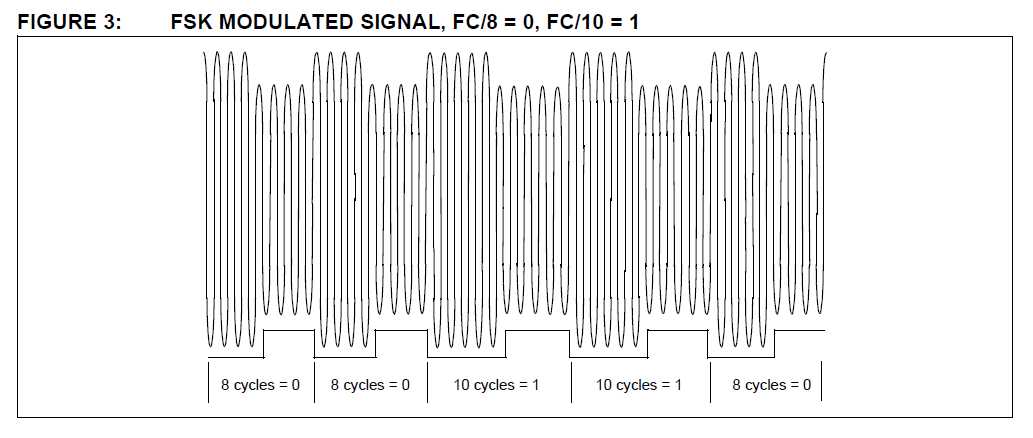
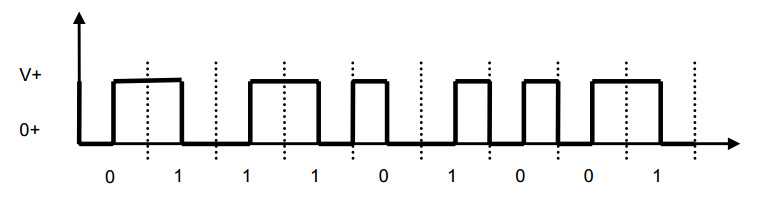
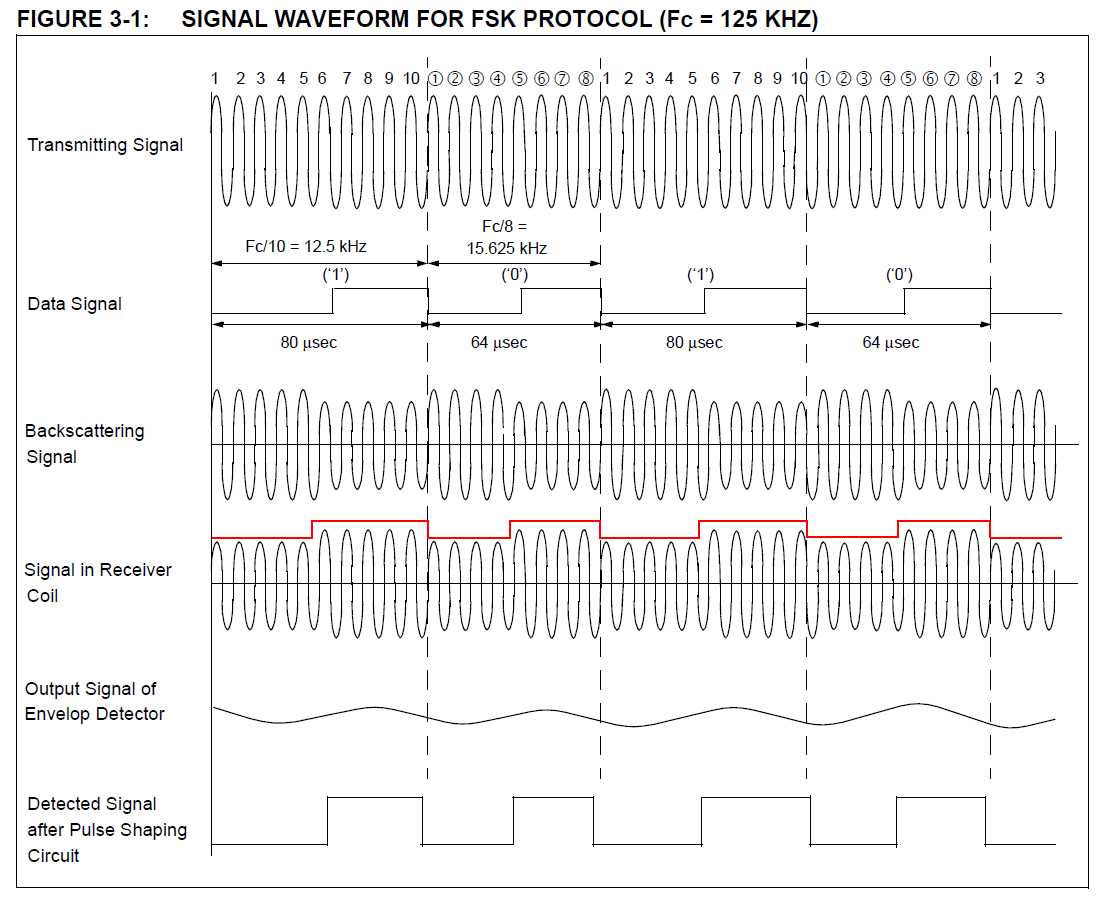
2. FSK (Frequency Shift Keying).
This form of modulation uses two different frequencies for data transfer; the most common FSK mode is FC/8/10.
In other words, a ‘0’ is transmitted as an amplitude-modulated clock cycle with period corresponding to the carrier frequency divided by 8,
and a ‘1’ is transmitted as an amplitude-modulated clock cycle period corresponding to the carrier frequency divided by 10.
The amplitude modulation of the carrier thus switches from FC/8 to FC/10 corresponding to 0’s and 1’s in the bitstream,
and the reader has only to count cycles between the peak-detected clock edges to decode the data.
FSK allows for a simple reader design, provides very strong noise immunity,
but suffers from a lower data rate than some other forms of data modulation.
In Figure 3, FSK data modulation is used with NRZ encoding.
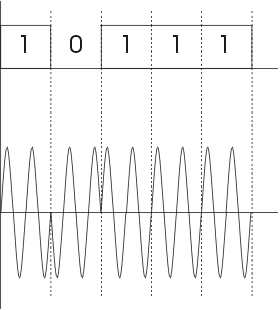
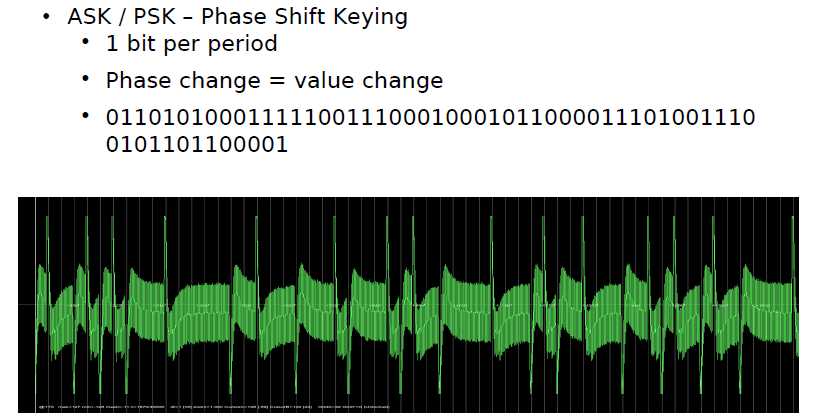
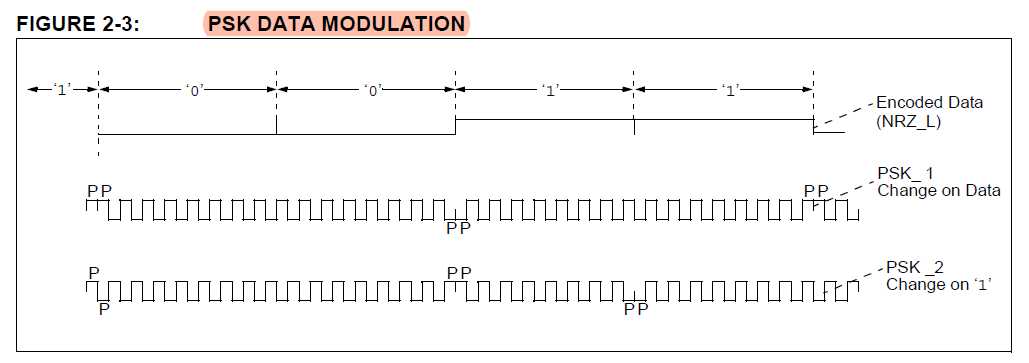
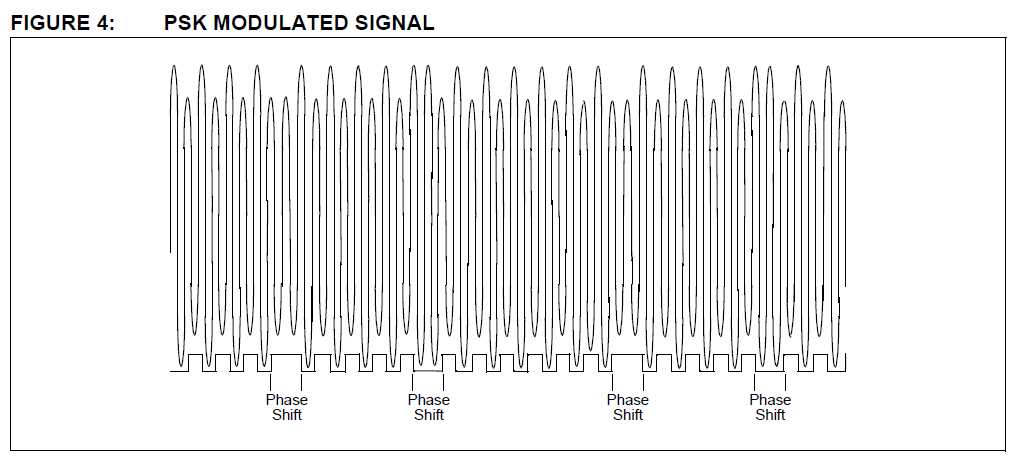
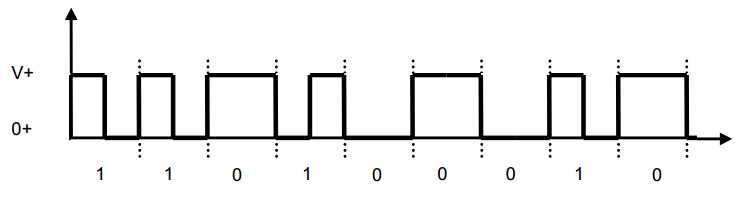
3. PSK (Phase Shift Keying).
This method of data modulation is similar to FSK, except only one frequency is used,
and the shift between 1’s and 0’s is accomplished by shifting the phase of the backscatter clock by 180 degrees.
Two common types of PSK are:
• Change phase at any ‘0’, or
• Change phase at any data change (0 to 1 or 1 to 0).
PSK provides fairly good noise immunity, a moderately simple reader design, and a faster data rate than FSK.
Typical applications utilize a backscatter clock of FC/2, as shown in Figure 4.
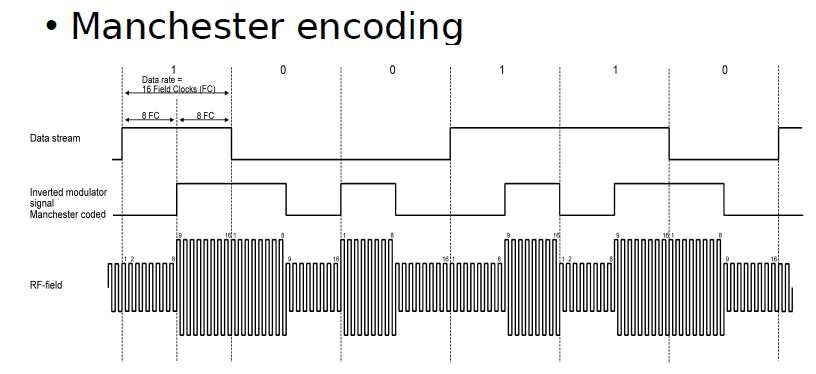
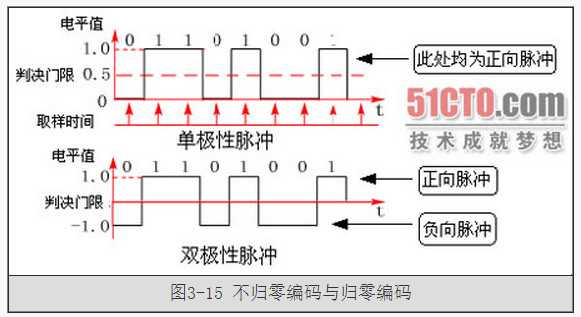
这个实例是ISO/IEC 15693-2中的内容是关于标签向reader的通讯的调制过程。
如图所示,标签需要发送的信号为“0”和“1”,其数字波形如图上的data;
通过曼彻斯特编码后为图上所示的manchester coding的数字波形;
subcarrier为副载波,其目的也是以提高信息传输的可靠性;
最终要发出去的数字信号就变成了subcarrier modulation的数字波形;
而最终发给Reader端的数据是一个射频信号,标签通过负载调制发射出的最终信号为13.56MHz载波的信号load modulation的信号。
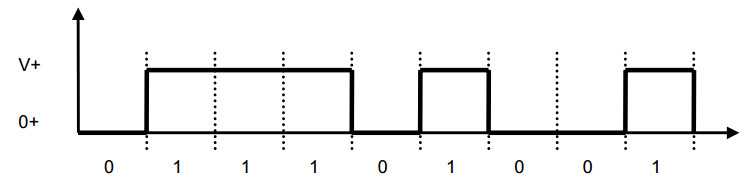
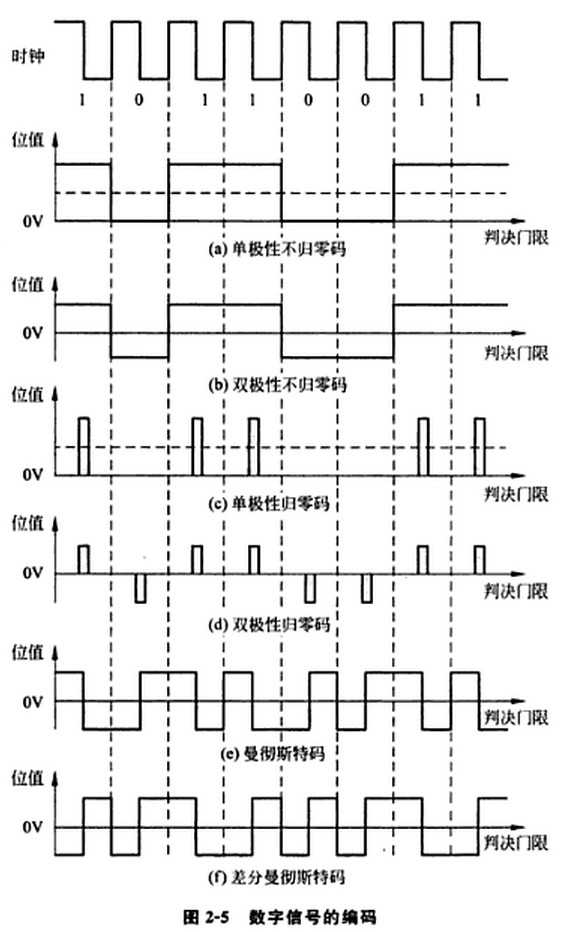
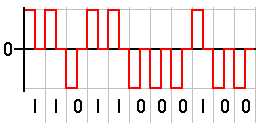
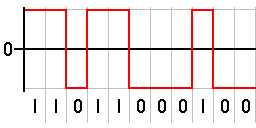
Low level = 0V
High level = +V
For each bit, there are n clocks (data rate).
Requires time co-ordination:
Longs strings of ‘0’ and ‘1’ do not produce any transitions which may create problems in error detection and recovery.
High DC level ( average of ½ Volts ).
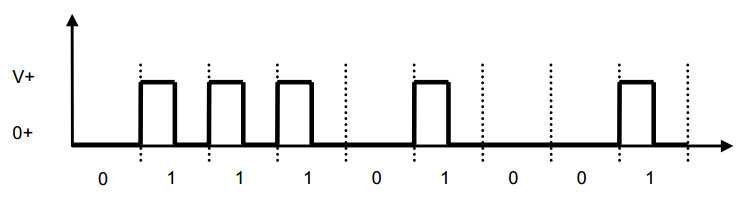
Low level = 0V
High level = +V during the first half of the bit and 0 during the second half.
DC average is only ¼ Volts.
Requires time co-ordination
This code is self-clocking
There is a transition at the start of the bit period, if the bit ‘0‘ is followed by a ‘0‘ bit or the bit ‘1‘ is followed by a ‘1‘ bit
There is no transition at the start of the bit period, if the bit is ‘0‘, followed by a ‘1‘ bit or the bit ‘1‘ is followed by a ‘0‘ bit
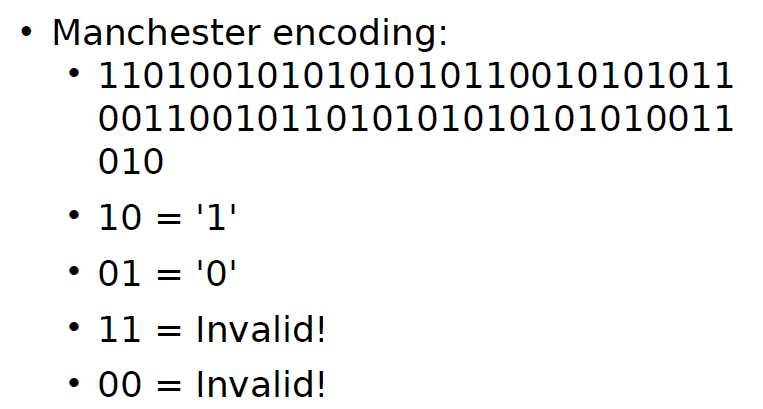
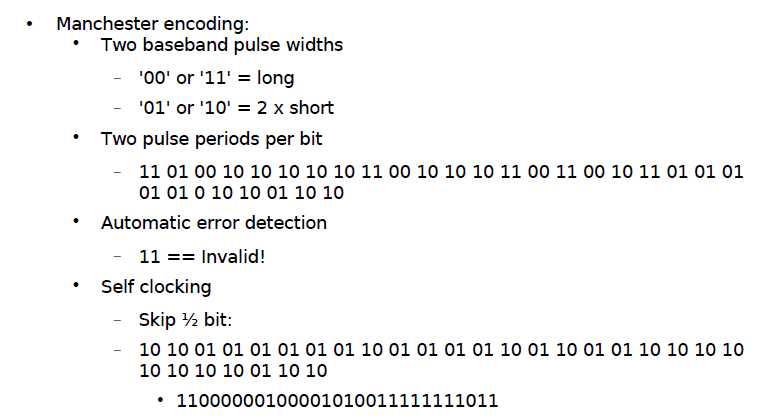
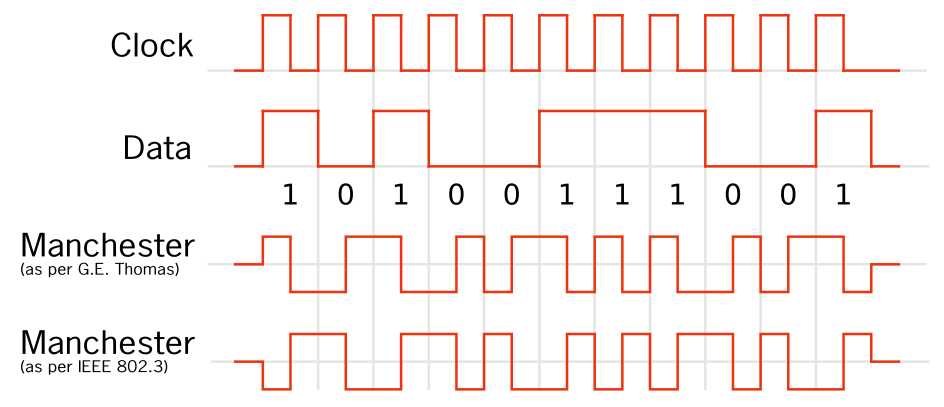
There is a transition in the middle of each bit period
A 1 to 0 transition represents a ‘0‘ bit
A 0 to 1 transition represents a ‘1‘ bit
The mid-bit transition is used as clock as well as data.
The residual DC value is eliminated by having both polarities for every bit
The bandwidth required could be twice the bit rate (Efficiency of this code can be as low as 50%)
This code is self-clocking
A transition at the start of the bit period represents a ‘0‘ bit
No transition at the start of the bit period represents a ‘1‘ bit
There is a transition in the middle of each bit period
The mid-bit transition is used only to provide clocking.
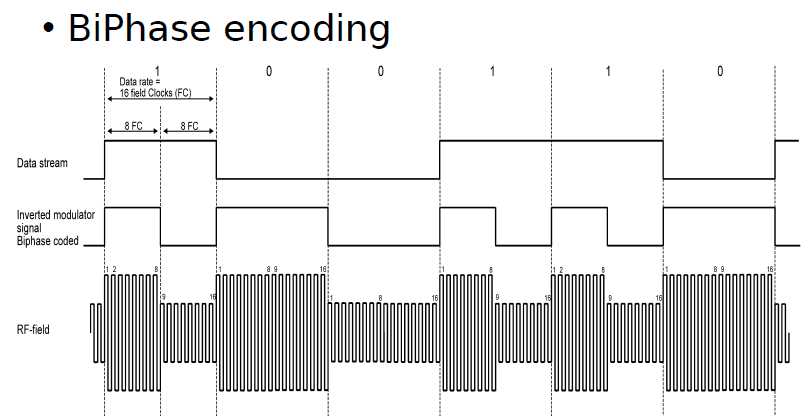
Biphased data streams have generally a signal change in the middle of each bit, independent of the value.
Therefore the signal does not necessarily return to zero.
The advantages of the biphase method are:
Synchronisation : Since there is a predictable transition for each bit, the beceiver can synchronise on this edge.
These codes are also known as self-clocking
Error immunity : To cause an error, the noise must invert both, the signal before and after the transition
There is a transition at the start of each bit period
A ‘0‘ has no transition in the middle of the bit period
A ‘1‘ bit has generally a transition in the middle of the bit period (pos. or neg.)
There is a transition at the start of each bit period
A ‘0‘ bit has generally a transition in the middle of the bit period (pos. or neg.)
A ‘1‘ has no transition in the middle of the bit period
There is a transition at the start of the bit period, if the bit ‘0‘ is followed by a ‘0‘ bit
There is no transition at the start of the bit period, if the bit is ‘0‘, followed by a ‘1‘ bit
There is a transition in the middle of a bit period, if it is a bit ‘1‘
This code is very efficient, regarding the desired bandwidth (half of the desired bandwidth of Manchester Coding).
Phaseshift keyed data is only decodable with angle sensitive demodulators. The data information can be found in the phase of the signal.
AM demodulators will show no results.
A bit ‘1‘ has a signal phase of π or 180°
A bit ‘0‘ has a signal phase of 0°
The interpretation of the digital value can as well be interpreted inverse (‘1‘ → π, ‘0‘ → 180°).
The conventional understanding of PSK is shown in the following figure, where the carrier is modulated by the transmitter (reader).
PSK modulation is also possible if the carrier is quasi-amplitude-modulated by the transponder as principally shouwn in the following figure.
The above example shows a PSK modulation with two periods per bit of data information.
The upper trace is the control of the transponder modulator.
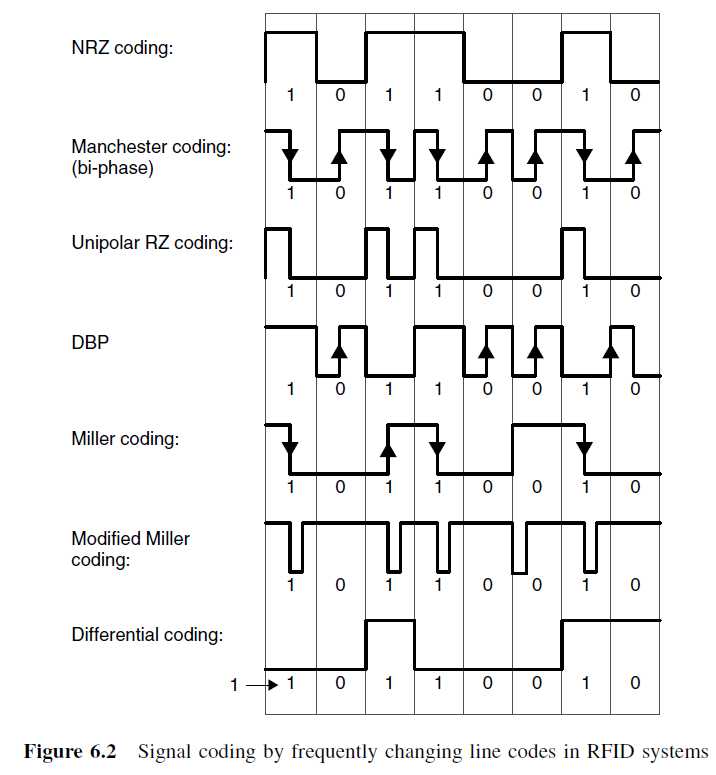
DATA ENCODING
Data encoding refers to processing or altering the data bitstream in-between the time it is retrieved
from the RFID chip’s data array and its transmission back to the reader.
The various encoding algorithms affect error recovery, cost of implementation, bandwidth,
synchronization capability and other aspects of the system design. Entire textbooks are written on the subject, but
there are several popular methods used in RFID tagging today:
1. NRZ (Non-Return to Zero) Direct.
In this method no data encoding is done at all; the 1’s and 0’s are clocked from the data array directly to the output transistor.
A low in the peak-detected modulation is a ‘0’ and a high is a ‘1’.
2. Differential Biphase.
Several different forms of differential biphase are used, but in general the bitstream being clocked out of the data array is modified
so that a transition always occurs on every clock edge, and 1’s and 0’s are distinguished by the transitions within the middle of the clock period.
This method is used to embed clocking information to help synchronize the reader to the bitstream.
Because it always has a transition at a clock edge, it inherently provides some error correction capability.
Any clock edge that does not contain a transition in the data stream is in error and can be used to reconstruct the data.
3. Biphase_L (Manchester).
This is a variation of biphase encoding in which there is not always a transition at the clock edge.
The MCRF355/360 and MCRF45X devices use this encoding method.
http://en.wikipedia.org/wiki/Return-to-zero
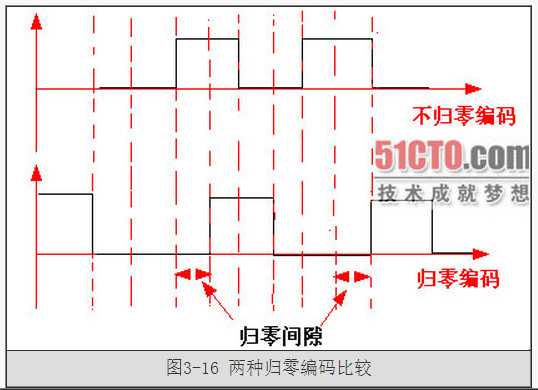
RZ 编码(Return-to-zero Code),即归零编码。
在 RZ 编码中,正电平代表逻辑 1,负电平代表逻辑 0,并且,每传输完一位数据,信号返回到零电平,
也就是说,信号线上会出现 3 种电平:正电平、负电平、零电平:
从图上就可以看出来,因为每位传输之后都要归零,所以接受者只要在信号归零后采样即可,这样就不在需要单独的时钟信号。
实际上,RZ 编码就是相当于把时钟信号用归零编码在了数据之内。这样的信号也叫做自同步(self-clocking)信号。
这样虽然省了时钟数据线,但是还是有缺点的,因为在 RZ 编码中,大部分的数据带宽,都用来传输“归零”而浪费掉了。
Return-to-zero (RZ) describes a line code used in telecommunications signals in which the signal drops (returns) to zero between each pulse.
This takes place even if a number of consecutive 0s or 1s occur in the signal.
The signal is self-clocking. This means that a separate clock does not need to be sent alongside the signal,
but suffers from using twice the bandwidth to achieve the same data-rate as compared to non-return-to-zero format.
The "zero" between each bit is a neutral or rest condition, such as
a zero amplitude in pulse amplitude modulation (PAM),
zero phase shift in phase-shift keying (PSK), or
mid-frequency in frequency-shift keying(FSK).
That "zero" condition is typically halfway between the significant condition representing a 1 bit and the other significant condition representing a 0 bit.
Although return-to-zero (RZ) contains a provision for synchronization, it still has a DC component resulting in “baseline wander”
during long strings of 0 or 1 bits, just like the line code non-return-to-zero.
Return-to-zero, inverted (RZI) is a method of mapping for transmission.
The two-level RZI signal has a pulse (shorter than a clock cycle) if the binary signal is 0, and no pulse if the binary signal is 1.
It is used (with a pulse 3/16 of a bit long) by the IrDA serial infrared (SIR) physical layer specification.
Required bandwidth for this kind of modulation is: BW = R(data rate)
http://en.wikipedia.org/wiki/Non-return-to-zero
http://zh.wikipedia.org/wiki/%E4%B8%8D%E6%AD%B8%E9%9B%B6
NRZ 编码(Non-return-to-zero Code),不归零编码。
我们去掉这个归零步骤,NRZ 编码(Non-return-to-zero Code)就出现了,和 RZ 的区别就是 NRZ 是不需要归零的:
http://baike.baidu.com/view/491480.htm
NRZ指的是在一个比特位的传送时间内,电压是保持不变的(比如说,不回到零点)。
In telecommunication, a non-return-to-zero (NRZ) line code is a binary code in which
1s are represented by one significant condition (usually a positive voltage) and
0s are represented by some other significant condition (usually a negative voltage), with no other neutral or rest condition.
The pulses have more energy than a return-to-zero (RZ) code.
Unlike RZ, NRZ does not have a rest state.
NRZ is not inherently a self-clocking signal, thus some additional synchronization technique
(for example a run length limited constraint, or a parallel synchronization signal) must be used for avoiding bit slip.
For a given data signaling rate, i.e., bit rate, the NRZ code requires only half the baseband bandwidth required
by the Manchester code (the passband bandwidth is the same).
When used to represent data in an asynchronous communication scheme,
the absence of a neutral state requires other mechanisms for bit synchronization
when a separate clock signal is not available.
NRZ-Level itself is not a synchronous system but rather an encoding that can be used
in either a synchronous or asynchronous transmission environment,
that is, with or without an explicit clock signal involved.
Because of this, it is not strictly necessary to discuss how the NRZ-Level encoding acts "on a clock edge" or "during a clock cycle"
since all transitions happen in the given amount of time representing the actual or implied integral clock cycle.
The real question is that of sampling—the high or low state will be received correctly provided the transmission line has stabilized for that bit
when the physical line level is sampled at the receiving end.
However, it is helpful to see NRZ transitions as happening on the trailing (falling) clock edge in order to compare NRZ-Level to other encoding methods,
such as the mentioned Manchester code, which requires clock edge information (is the XOR of the clock and NRZ, actually)
see the difference between NRZ-Mark and NRZ-Inverted.
在电信学中,不归零编码 (non-return-to-zero line code, NRZ) 指的是一种二进制的讯号代码,
在这种传输方式中,1 和 0 都个别由不同的电子显著状态来表现,除此之外,没有中性状态、亦没有其他种状态。
这种脉冲的能量比归零代码要来得密集,但它传输时是不停歇的,这代表同步信号必须在此代码之外独自传输。
在给定一个信号频率的情况下(比如说位元率),NRZ 代码只需要曼彻斯特代码 (Manchester code) 的一半带宽。
当用于异步传输时,由于缺少中性状态,必须依靠其他种机制,来达成在同步传输中使用时钟侦测错误的资料回复工作。
NRZ-Level 本身并非一种同步系统,而更是一种编码方式,因为它可用于同步环境、或异步环境中,也就是不管有没有明确的时钟讯号,都可以运作。
所以,讨论 NRZ-Level 编码是否在时钟“跳动 (clock-edge)”或“跳动之间 (between clock-edge)”并非必要的,
因为每一个讯号一定都是以给定的时脉来传输的,这就暗示了讯号内在的时脉。
真正的问题是,能否在接收端以当初取样时的同样频率重绘该讯号。
然而,由于 NRZ 讯号的脉冲与时钟是一致的,这就很容易看出 NRZ-Level 和其他编码方式的不同,
例如前面提到的曼彻斯特代码,它需要明确的时脉资讯(即 NRZ 和时钟的 XOR 值),
还能看出与 NRZ-Mark 和 NRZ-Inverted 等编码的不同。
不归零法编码 不归零法(Nonreturn to Zero, NRZ)可能是最简单的一种编码方案。
它传送一个0时把电压升高,而传送一个1时则使用低电平。
这样,通过在高低电平之间作相应的变换来传送0和1的任何序列。
NRZ指的是在一个比特位的传送时间内,电压是保持不变的(比如说,不回到零点)。
下图描述了二进制串1 0 1 0 0 11 0的NRZ传输过程。
NRZ编码虽然简单,但却存在一个问题。研究一下下图中的传输。它正在传送什么呢?
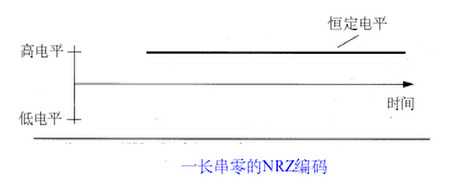
你可以回答说是“一个0的序列”。是的,但到底有多少个0呢?
对于这个问题,你会回答说这取决于一个比特位的持续时间。
现在假设我们告诉你1毫米线段对应于一个周期。那么你所要做的就是量出图中线段的长度,并转换为毫米。
这一计算将告诉你线段中有多少个1毫米的分段,也就是0的个数。理论上这个方法是行得通的,但实际上却不然。
假设有个人用尺子画出了一条包含1 0 0 0个1毫米分段的线段。那么总共有多长呢?
答案是1米,但由于在测量和实际绘制时出现的误差,线段可能只是接近而不是刚刚好一米长。
因此,当第二个人来测量这条线段时,他将得出一个比1 0 0 0个分段稍微多点或少点的答案。
即使第一个人很幸运,他的测量准确无误,但第二个人度量时的不精确也将导致误差。
这会给数据传输带来什么影响呢?
当一台设备传送一个比特的数字信号时,它将在一定的周期内,假定为T,产生一个持续的信号。
一个内置的时钟负责定时。接收设备必须知道信号的周期,这样它才能在每个T时间单元内对信号进行采样。
它也有一个负责定时的内置时钟。剩下的就是确保两个时钟使用同样的T。
下一个问题是:所有的时钟总是保持一致的吗?任何物理设备都存在着设计上的局限性和缺陷。
几乎可以肯定任何两个时钟都存在着微小的差别,这使得设备无法对传输信号作十分精确的采样。
就好象我们在新年的第一天校正了两个时钟,但到了年底却发现它们已经有了轻微的差别。
同样地,管弦乐队的音乐家们以同样的速度同时开始演奏,但如果他们不看指挥,
也不注意听别人的拍子的话,他们的节奏将开始混乱。
稍微的不和谐就将毁掉整个演奏,使它听起来就象作者和他的同事们正在表演一样。
就象指挥家确保演奏者的同步一样,通信设备也需要某种机制以使它们的定时保持一致。
不变的信号不具备同步机制。但如果信号改变的话,这种改变就可以用来保持设备的同步。
有些强制信号改变的编码方案就是基于这个原因。
Non return to zero(NRZ)
NRZ codes share the property that voltage level is constant during a bit interval.
High level voltage = bit 1 and Low level voltage = bit 0.
A problem arises when there is a long sequence of 0s or 1s and the volatage level
is maintained at the same value for a long time.
This creates a problem on the recieving end because now, the clock synchronization is lost due to lack of any transitions and hence,
it is difficult to determine the exact number of 0s or 1s in this sequence.
The two variations are as follows:
NRZ-I has an advantage over NRZ-L.
Consider the situation when two data wires are wrongly connected in each other‘s place.
In NRZ-L all bit sequences will get reversed (B‘coz voltage levels get swapped).
Whereas in NAZ-I since bits are recognized by transition the bits will be correctly interpreted.
A disadvantage in NRZ codes is that a string of 0‘s or 1‘s will prevent synchronization of transmitter clock
with receiver clock and a separate clock line need to be provided.
"One" is represented by one physical level (such as a DC bias on the transmission line).
"Zero" is represented by another level (usually a negative voltage).
1”由一种物理电平表现,例如传输线上的直流偏移 (DC bias)。
“0”由另一种电平表现(通常是负电压)。
在时脉术语中,通常“1”沿着上一个位元的时脉边缘,维持或改变到一个较低的位置;
而“0”则沿着上一个位元的时脉边缘,维持或改变到一个较高的位置,或者两者反过来。
这可能会造成一长串不改变的电平,让同步工作变得困难。
一个解决办法是只传送有着许多变化的讯号,见限制游长 (Run Length Limited)。
图表显示最低一条线代表真正的零电平,而其上是代表“0”的逻辑电平,电压代表“1”,这种配置较稀少。
"One" is represented by one physical level (usually a positive voltage).
"Zero" is represented by another level (usually a negative voltage).
In clock language, in bipolar NRZ-Level the voltage
"swings" from positive to negative on the trailing edge of the previous bit clock cycle.
An example of this is RS-232, where "one" is −12 V to −5 V and "zero" is +5 V to +12 V.
1”由一物理电平表现(通常是正电压)。负电压 ?
“0”由另一电平表现(通常是负电压)。正电压 ?
在时脉术语中,两极的 NRZ-Level 电压沿着上一个位元的时脉边缘,从正转向负。
这种讯号的例子是 RS-232,它的“1”是 -5v 至 -12V 之间、“0”是 +5V 至 +12V 之间。
“1”由物理电平的改变来表示。
“0”由物理电平的没有改变来表示。
在时脉术语中,沿着上一个位元的时脉边缘作出改变的代表“1”,没有改变的代表“0”。
观看图表来理解以改变为基础的编码时,必须理解到如果第一个位元之前的初始状态被判断为相反的,
则整个讯号会是反相的、或部份反相的。
在其他文件中,这个编码很常只用“NRZ”单名来称呼[1];
FIPS 1037 也把“不归零改变为一 (non-return-to-zero change-on-ones)
”和“不归零一 (non-return-to-zero one)”定义为与此相同的东西。
"One" is represented by no change in physical level.
"Zero" is represented by a change in physical level.
In clock language, the level transitions on the trailing clock edge of the previous bit to represent a "zero."
This "change-on-zero" is used by High-Level Data Link Control and USB.
They both avoid long periods of no transitions (even when the data contains long sequences of 1 bits) by using zero-bit insertion.
HDLC transmitters insert a 0 bit after five contiguous 1 bits (except when transmitting the frame delimiter ‘01111110‘).
USB transmitters insert a 0 bit after six consecutive 1 bits.
The receiver at the far end uses every transition —
both from 0 bits in the data and these extra non-data 0 bits — to maintain clock synchronization.
The receiver otherwise ignores these non-data 0 bits.
1”由物理电平的没有改变来表现。
“0”由电平的改变来表现。
在时脉术语中,沿着前一个位元的时脉边缘改变的电平代表的是“0”。
这个“改变为零”的应用例子是 High-Level Data Link Control 和 USB。
它们利用插入零位元来避免长串的未改变位元(即使资料中包含了大量的 1 位元序列)。
HDLC 传输器会在连续的五个 1 位元后面,自动插入一个 0 位元(一个例外是区块定义符 "01111110")。
USB 传输器会在六个连续的 1 位元后,插入一个 0 位元。
接收端将使用每一个电平的转换(不管是资料本身还是自动插入位元)来维持时脉的同步性,若不为同步,则这些插入 0 位元会被忽略。
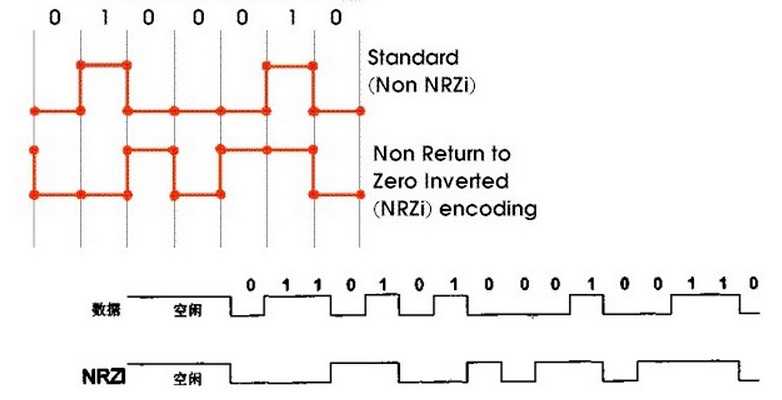
Non return to zero, inverted (NRZI) is a method of mapping a binary signal to a physical signal
for transmissionover some transmission media.
The two level NRZI signal has a transition at a clock boundary if the bit being transmitted is a logical 1,
and does not have a transition if the bit being transmitted is a logical 0.
"One" is represented by a transition of the physical level.
"Zero" has no transition.
Also, NRZI might take the opposite convention, as in Universal Serial Bus (USB) signalling,
when in Mode 1, in which a transition occurs when signaling zero, and a steady level when signaling a one.
The transition occurs on the leading edge of the clock for the given bit.
This distinguishes NRZI from NRZ-Mark.
However, even NRZI can have long series of zeros (or ones if transitioning on "zero"),
and thus clock recovery can be difficult unless some form of run length limited (RLL) coding is used in addition to NRZI.
Magnetic disk and tape storage devices generally use fixed-rate RLL codes,
while USB uses bit stuffing, which inserts an additional 0 bit after 6 consecutive 1 bits.
While bit stuffing is efficient, it results in a variable data rate
because it takes slightly longer to send a long string of 1 bits than it does to send a long string of 0 bits.
一改变:“1”为物理电平上的改变。“0”为没有改变。
零改变:“0”为物理电平上的改变。“1”为没有改变。
改变发生在当下位元的时钟脉冲前缘。
但是,NRZI 会有长串的 0或1 位元出现,导致时脉回复有困难,可以使用一些编码技巧(例如游长限制)来解决。
曼彻斯特代码永远有时脉信号,但传输效率比 NRZI 低。
NRZI 编码被用于磁带的录音、CD的刻录和标准 USB 的传讯。
信号电平的一次反转代表1,电平不变化表示0,并且在表示完一个码元后,电压不需回到0
不归零制编码是效率最高的编码
缺点是存在发送方和接收方的同步问题
单极性不归零码,无电压(也就是元电流)用来表示"0",而恒定的正电压用来表示"1"。
每一个码元时间的中间点是采样时间,判决门限为半幅度电平(即0.5)。
也就是说接收信号的值在0.5与1.0之间,就判为"1"码,如果在O与0.5之间就判为"0"码。
每秒钟发送的二进制码元数称为"码速"。
双极性不归零码,"1"码和"0"码都有电流,但是"1"码是正电流,"0"码是负电流,正和负的幅度相等,故称为双极性码。
此时的判决门限为零电平,接收端使用零判决器或正负判决器,接收信号的值若在零电平以上为正,判为"1"码;若在零电平以下为负,判为"0"码。
以上两种编码,都是在一个码元的全部时间内发出或不发出电流(单极性),以及发出正电流或负电流(双极性)。
每一位编码占用了全部码元的宽度,故这两种编码都属于全宽码,也称作不归零码NRZ (Non Return Zero)。
如果重复发送"1"码,势必要连续发送正电流;如果重复发送"0"码,势必要连续不送电流或连续发送负电流,
这样使某一位码元与其下一位码元之间没有间隙,不易区分识别。归零码可以改善这种状况。
NRZI 编码(Non-Return-to-Zero Inverted Code)和 NRZ 的区别就是
NRZI 用信号的翻转代表一个逻辑,信号保持不变代表另外一个逻辑。
USB 传输的编码就是 NRZI 格式,在 USB 中,电平翻转代表逻辑 0,电平不变代表逻辑1(NRZI 遇 0 翻转,遇 1 不变):
翻转的信号本身可以作为一种通知机制,而且可以看到,即使把 NRZI 的波形完全翻转,
所代表的数据序列还是一样的,对于像 USB 这种通过差分线来传输的信号尤其方便.
现在再回到那个同步问题:的确,NRZ 和 NRZI 都没有自同步特性,但是可以用一些特殊的技巧解决。
比如,先发送一个同步头,内容是 0101010 的方波,让接受者通过这个同步头计算出发送者的频率,
然后再用这个频率来采样之后的数据信号,就可以了。
在 USB 中,每个 USB 数据包,最开始都有个同步域(SYNC),这个域固定为 0000 0001,
这个域通过 NRZI 编码之后,就是一串方波(复习下前面:NRZI 遇 0 翻转遇 1 不变),
接受者可以用这个 SYNC 域来同步之后的数据信号。
此外,因为在 USB 的 NRZI 编码下,逻辑 0 会造成电平翻转,所以接受者在接受数据的同时,
根据接收到的翻转信号不断调整同步频率,保证数据传输正确.
但是,这样还是会有一个问题,就是虽然接受者可以主动和发送者的频率匹配,但是两者之间总会有误差。
假如数据信号是 1000 个逻辑1,经过 USB 的 NRZI 编码之后,就是很长一段没有变化的电平,
在这种情况下,即使接受者的频率和发送者相差千分之一,就会造成把数据采样成 1001 个或者 999 个 1了。
USB 对这个问题的解决办法,就是强制插 0,也就是传说中的 bit-stuffing,
如果要传输的数据中有 7 个连续的 1,发送前就会在第 6 个 1 后面强制插入一个 0,
让发送的信号强制出现翻转,从而强制接受者进行频率调整。
接受者只要删除 6 个连续 1 之后的 0,就可以恢复原始的数据了。
曼彻斯特编码(Manchester Code)用信号的变化来保持发送设备和接收设备之间的同步。
也有人称之为自同步码( Self-Synchronizing Code)。
为了避免上面 不变的信号不具备同步机制 情况,它用电压的变化来分辨0和1。
它明确规定,从高电平到低电平的跳变代表0,而从低电平到高电平的跳变代表1。
下图给出了比特串0 1 0 11 0 0 1的曼彻斯特编码。如图所示,信号的保持不会超过一个比特位的时间间隔。
即使是0或1的序列,信号也将在每个时间间隔的中间发生跳变。
这种跳变将允许接收设备的时钟与发送设备的时钟保持一致。
曼彻斯特编码的一个缺点是需要双倍的带宽。也就是说,信号跳变的频率是NRZ编码的两倍。
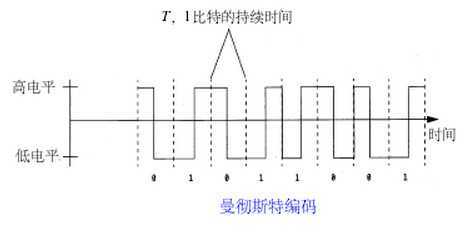
曼彻斯特编码(Manchester Encoding),也叫做相位编码( Phase Encode,简写PE),
是一个同步时钟编码技术,被物理层使用来编码一个同步位流的时钟和数据。
它在以太网媒介系统中的应用属于数据通信中的两种位同步方法[1]里的自同步法(另一种是外同步法),
即接收方利用包含有同步信号的特殊编码从信号自身提取同步信号来锁定自己的时钟脉冲频率,达到同步目的。
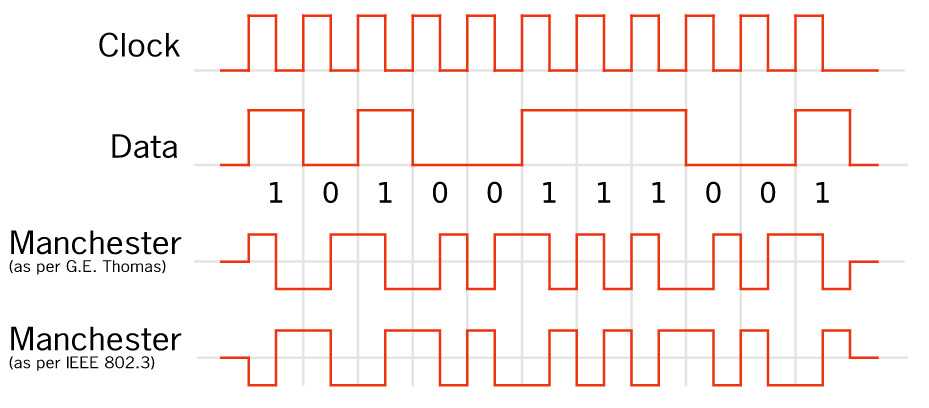
和曼彻斯特编码一样,在每个比特时间间隔的中间,信号都会发生跳变。
区别在于每个时间间隔的开始处。
0将使信号在时间间隔的开始处发生跳变。而1将使信号保持它在前一个时间间隔尾部的取值。( 不变 )
因此,根据信号初始值的不同, 0将使信号从高电平跳到低电平,或从低电平跳到高电平。
下图给出了比特串1 0 1 0 0 11 0的差分曼彻斯特编码。
在这里,我们通过检查每个时间间隔开始处信号有无跳变来区分0和1。
检测跳变通常更加可靠,特别是线路上有噪音干扰的时候。
如果有人把连接的导线颠倒了,也就是把高低电平颠倒了,这种编码仍然是有效的
(现在,你也许会问哪个神志清醒的人会把两根连接的导线颠倒呢。
有几种可能的原因。其一是某人过于匆忙,其二是某人不小心搞错了。这种事情常有发生!)。
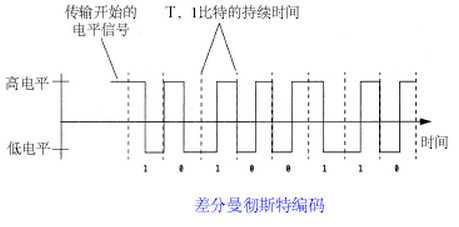
差分曼彻斯特编码:
在信号位开始时不改变信号极性,表示辑"1"
在信号位开始时改变信号极性,表示逻辑"0" ;
【注意】:如果在最初信号的时候,即第一个信号时:
如果中间位电平从低到高,则表示0;如果中间位电平从高到低,则表示1;
后面的(从第二个开始)就看每个信号位开始时有没有跳变来决定:
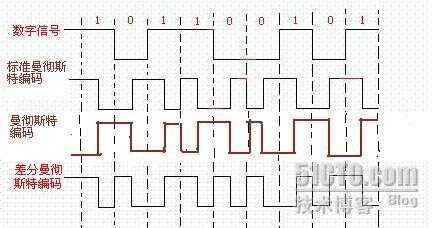
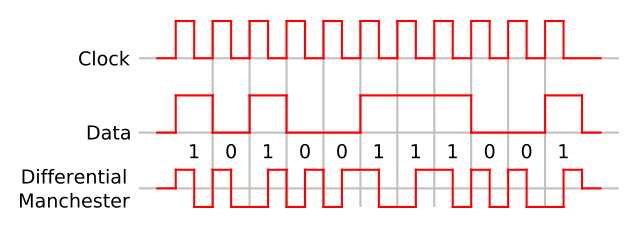
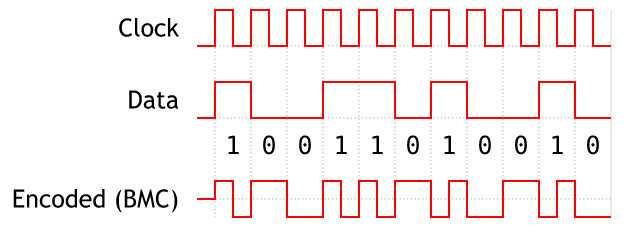
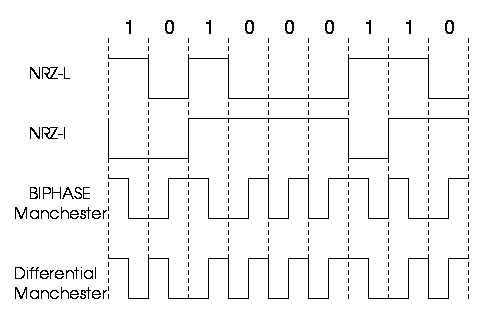
标签:
原文地址:http://www.cnblogs.com/shangdawei/p/4834182.html