标签:community exec recover replace 配置文件 item 入参 error lib
yum install -y net-snmp net-snmp-utils
vim /usr/lib/systemd/system/snmptrapd.service
ExecStart=/usr/sbin/snmptrapd $OPTIONS -f -O n
vim /etc/snmp/snmptrapd.conf
authCommunity execute public
traphandle default /sbin/snmptthandler
systemctl enable snmptrapd
systemctl start snmptrapd
netstat -unpl |grep 162# rpm -ivh http://dl.fedoraproject.org/pub/epel
yum install snmptt perl-Sys-Syslog
vim /etc/snmp/snmptt.ini
date_time_format= %Y/%m/%d %H:%M:%S
mode = daemon
~~~
snmptt_conf_files = <<END
/etc/snmp/snmptt.conf #默认的格式化日志配置文件
/etc/snmp/nbu.conf # 在这里可以指定其他的格式化trap日志的配置文件
END
~~~
vim /etc/snmp/nbu.conf #snmptrapd接受设备打过来的日志信息,传输到snmptt进行格式化,
~~~
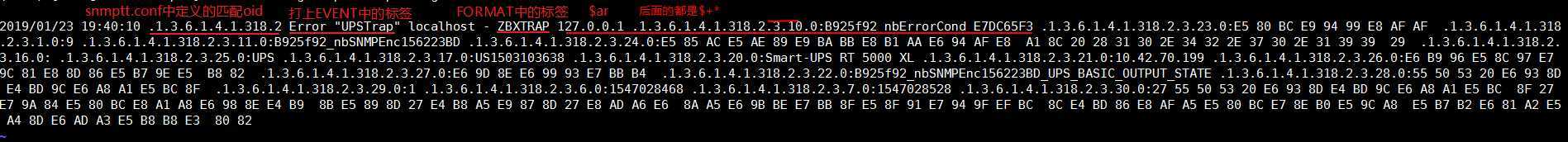
EVENT general .1.3.6.1.4.1.318.* "UPSTrap" Error #EVENT general 固定格式 .1.3.6......匹配日志信息中的oid,后面的.*支持统配,将收到的日志添加 "UPSTrap" Error
FORMAT ZBXTRAP $ar $+* # 格式化数据,都打上ZABTRAP 头,$ar $+* $ar一般是ip,$+*就是后面的oid信息
EXEC /etc/snmp/xxxx.py "$+*" #执行指定的py脚本,传入format中匹配的参数,
~~~
xxxx.py中的处理 #在EXEC中指定执行的脚本
def handle(param):
param = """127.0.0.1 .1.3.6.1.4.1.318.2.3.10.0:B925f92_nbErrorCond_E7DC65F3 .1.3.6.1.4.1.318.2.3.23.0:E5 80 BC E9 94 99 E8 AF AF .1.3.6.1.4.1.318.2.3.1.0:9 .1.3.6.1.4.1.318.2.3.11.0:B925f92_nbSNMPEnc156223BD .1.3.6.1.4.1.318.2.3.24.0:E5 85 AC E5 AE 89 E9 BA BB E8 B1 AA E6 94 AF E8 A1 8C 20 28 31 30 2E 34 32 2E 37 30 2E 31 39 39 29 .1.3.6.1.4.1.318.2.3.16.0: .1.3.6.1.4.1.318.2.3.25.0:UPS .1.3.6.1.4.1.318.2.3.17.0:US1503103638 .1.3.6.1.4.1.318.2.3.20.0:Smart-UPS RT 5000 XL .1.3.6.1.4.1.318.2.3.21.0:10.42.70.199 .1.3.6.1.4.1.318.2.3.26.0:E6 B9 96 E5 8C 97 E7 9C 81 E8 8D 86 E5 B7 9E E5 B8 82 .1.3.6.1.4.1.318.2.3.27.0:E6 9D 8E E6 99 93 E7 BB B4 .1.3.6.1.4.1.318.2.3.22.0:B925f92_nbSNMPEnc156223BD_UPS_BASIC_OUTPUT_STATE .1.3.6.1.4.1.318.2.3.28.0:55 50 53 20 E6 93 8D E4 BD 9C E6 A8 A1 E5 BC 8F .1.3.6.1.4.1.318.2.3.29.0:1 .1.3.6.1.4.1.318.2.3.6.0:1547028468 .1.3.6.1.4.1.318.2.3.7.0:1547028528 .1.3.6.1.4.1.318.2.3.30.0:27 55 50 53 20 E6 93 8D E4 BD 9C E6 A8 A1 E5 BC 8F 27 E7 9A 84 E5 80 BC E8 A1 A8 E6 98 8E E4 B9 8B E5 89 8D 27 E4 B8 A5 E9 87 8D 27 E8 AD A6 E6 8A A5 E6 9B BE E7 BB 8F E5 8F 91 E7 94 9F EF BC 8C E4 BD 86 E8 AF A5 E5 80 BC E7 8E B0 E5 9C A8 E5 B7 B2 E6 81 A2 E5 A4 8D E6 AD A3 E5 B8 B8 E3 80 82
"""
data = {}
param_list = param.split('.1.3.6.1.4.1.318.2.3.')[1:] #使用1.3.6.1.4.1.318.2.3来切割字符串,得到.1.3.6.1.4.1.318.2.3.后面的值 >'10.0:B925f92_nbErrorCond_E7DC65F3 ',
for item in param_list:
key, value = item.split(':') #用:来切割,得到所有的oid及其对应的值 key > .1.3.6.1.4.1.318.2.3.6.0 value >1547028468
key = key.split('.')[0] #
data[key] = value
if key in ['23', '24', '26', '27', '28', '30']:
value = binascii.a2b_hex(value.replace(' ', '')).decode('utf8')
else:
value = value.strip()
data[key] = value
host = data['24'].split(' ')[0].strip()
ip = data['21'].strip()
end = int(data['7'])
if end:
value = 0
else:
value = 1
if value:
key, value = check_alert_key(data)
else:
key, value = check_recover_key(data)
start = int(data['6'])
end = int(data['7'])
msg = data['30']
#logging.info(data['29'], data['30'])
return host, ip, key, value, start, end, msg
if __name__ == '__main__':
if len(sys.argv) > 1:
arg = sys.argv[1]
ret = handle(arg) #接受传入参数,这里是匹配的$+*,就是匹配的所有的oid信息
sender = ZabbixSender() #使用了zabbixsender来给server端发送数据
sender.add(ret[1], ret[2], ret[3]) #指定了ip key value
sender.send() #发送
item = '[{4} - {5}] host: {0} ip: {1} key: {2} value: {3} message: {6}\n'.format(*ret)
logging.info(item)systemctl enable snmptt
systemctl start snmpttvi zabbix_server.conf
vi zabbix_proxy.conf
SNMPTrapperFile=/var/log/snmptt/snmptt.log
StartSNMPTrapper=1
systemctl retart zabbix-server
# 测试命令
snmptrap -v 2c -c public 127.0.0.1 "" 1.3.6.1.4.1.2345 1.3.6.1.4.1.2345 s "test v2"
发送的 ip 要与主机的 SNMP接口 ip 一致。authCommunity execute public traphandle default /sbin/snmptthandler标签:community exec recover replace 配置文件 item 入参 error lib
原文地址:https://www.cnblogs.com/0916m/p/11544440.html