标签:object cert 访问 ide day bfd 版本 pwc 相同
kubectl本身带有认证信息 认证信息文件存放在用户家目录下的/root/.kube/config
kubectl 可以远程访问 只需要把配置文件拷贝过去 k8s的输入输出都是以json格式来传递的
[root@k8s-master ~]# kubectl proxy --port=8080
Starting to serve on 127.0.0.1:8080
[root@k8s-master .kube]# curl http://localhost:8080/api/v1/namespaces
k8s中每个资源都有一个唯一对应的资源路径url 可以通过此url对资源进行操作
创建资源的时候需要填充一个body参数 其它操作直接调用url指定action即可
快速生成资源清单文件模板
1.只要支持create命令的资源都可以使用此方式
kubectl create serviceaccount mysa -o yaml --dry-run > s.yaml

1.创建私钥 [pki]# (umask 077; openssl genrsa -out yxh.key 2048) [pki]# ls apiserver.key front-proxy-ca.crt yxh.key 2.生成证书签署请求 CN就是用户账号名称 [pki]# openssl req -new -key yxh.key -out yxh.csr -subj "/CN=yxh" 3.签署证书 [root@k8s-master pki]# openssl x509 -req -in yxh.csr -CA ca.crt -CAkey ca.key -CAcreateserial -out yxh.crt -days 365 Signature ok subject=/CN=yxh Getting CA Private Key 4.查看证书信息 [root@k8s-master pki]# openssl x509 -in yxh.crt -text -noout Certificate: Data: Version: 1 (0x0) Serial Number: 8a:59:4a:8d:64:e9:3b:1c Signature Algorithm: sha256WithRSAEncryption Issuer: CN=kubernetes Validity Not Before: Jun 22 10:30:26 2019 GMT Not After : Jun 21 10:30:26 2020 GMT Subject: CN=yxh 5.添加用户到k8s集群 [root@k8s-master pki]# kubectl config set-credentials yxh --client-certificate=./yxh.crt --client-key=./yxh.key --embed-certs=true User "yxh" set. [root@k8s-master pki]# kubectl config set-context yxh@kubernetes --cluster=kubernetes --user=yxh Context "yxh@kubernetes" created. [root@k8s-master pki]# kubectl config use-context yxh@kubernetes Switched to context "yxh@kubernetes". [root@k8s-master pki]# kubectl get pods No resources found. Error from server (Forbidden): pods is forbidden: User "yxh" cannot list pods in the namespace "default"
定义角色Role和clusterRole
1.operations 操作
2.objects 资源
两种用户类型
User Account
Service Account 用户充当客户端的pod 比如运行dashboard的pod
角色绑定 RoleBinding
集群角色绑定 ClusterRoleBinding
Role和RoleBinding 主要针对RoleBinding所属名称空间下进行授权
ClusterRole和ClusterRoleBinding 针对集群级别授权
ClusterRole和RoleBinding 针对所属名称空间授权
解决多个名称空间中角色名和权限完全相同的情况
Role和ClusterRoleBinding不能相互绑定
不管是Role还是ClusterRole
只要是和RoleBinding 那么权限就只限定在RoleBinding所属的名称空间中
只要是和ClusterRoleBinding 那么就是针对整个集群来授权

# kubectl config use-context kubernetes-admin@kubernetes # kubectl apply -f role_demo.yaml role.rbac.authorization.k8s.io/pods-reader created [root@k8s-master role]# kubectl create rolebinding yxh-read-pods --role=pods-reader --user=yxh rolebinding.rbac.authorization.k8s.io/yxh-read-pods created [root@k8s-master role]# kubectl describe rolebinding yxh-read-pods Name: yxh-read-pods Labels: <none> Annotations: <none> Role: Kind: Role Name: pods-reader Subjects: Kind Name Namespace ---- ---- --------- User yxh [root@k8s-master role]# kubectl config use-context yxh@kubernetes Switched to context "yxh@kubernetes". [root@k8s-master role]# kubectl get svc No resources found. Error from server (Forbidden): services is forbidden: User "yxh" cannot list services in the namespace "default" [root@k8s-master role]# kubectl get pods NAME READY STATUS RESTARTS AGE myapp-deploy-67f6f6b4dc-2986w 1/1 Running 0 6d myapp-deploy-67f6f6b4dc-czvq4 1/1 Running [root@k8s-master role]# kubectl get pods -n kube-system No resources found. Error from server (Forbidden): pods is forbidden: User "yxh" cannot list pods in the namespace "kube-system"

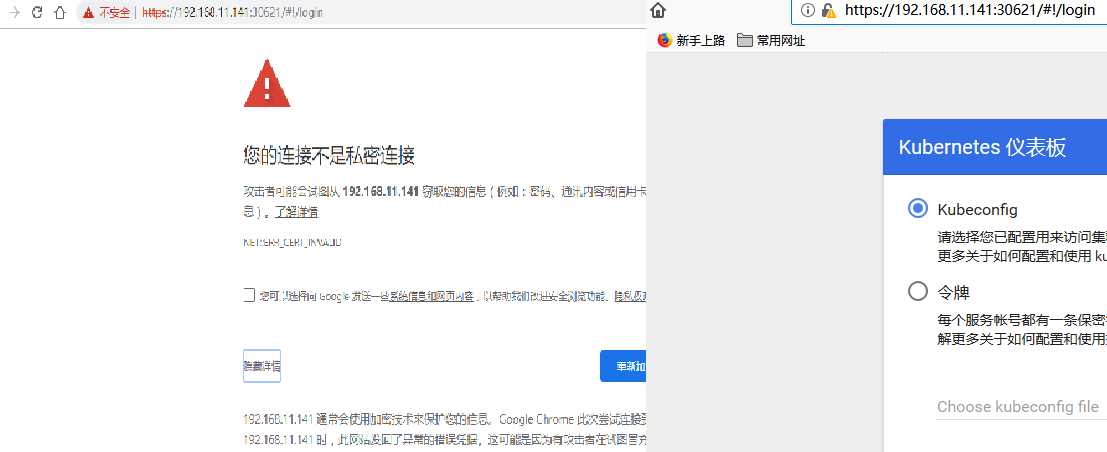
1.上传镜像 默认访问谷歌仓库 无法访问 每个节点都需要传递 docker load < kubernetes-dashboard-amd64.tar 2.修改image的版本 containers: - name: kubernetes-dashboard image: k8s.gcr.io/kubernetes-dashboard-amd64:v1.8.3 3.查看dashboard的pod运行状态 # kubectl get pods -n kube-system NAME READY STATUS RESTARTS AGE kubernetes-dashboard-6948bdb78-h6z25 1/1 Running 0 37s 4.# kubectl get svc -n kube-system NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE kube-dns ClusterIP 10.96.0.10 <none> 53/UDP,53/TCP 260d kubernetes-dashboard ClusterIP 10.109.157.47 <none> 443/TCP 1m 5.# kubectl patch svc kubernetes-dashboard -p ‘{"spec":{"type":"NodePort"}}‘ -n kube-system service/kubernetes-dashboard patched
说明: 因为是自签名证书,很多浏览器不让访问,可以使用FireFox,选择添加安全例外(Exceptions)即可.

root@k8s-master ~]# kubectl create serviceaccount dashboard-admin -n kube-system serviceaccount/dashboard-admin created [root@k8s-master ~]# kubectl get sa -n kube-system NAME SECRETS AGE attachdetach-controller 1 261d bootstrap-signer 1 261d certificate-controller 1 261d clusterrole-aggregation-controller 1 261d coredns 1 261d cronjob-controller 1 261d daemon-set-controller 1 261d dashboard-admin 1 9s default 1 261d deployment-controller 1 261d disruption-controller 1 261d endpoint-controller 1 261d expand-controller 1 261d flannel 1 261d generic-garbage-collector 1 261d horizontal-pod-autoscaler 1 261d job-controller 1 261d kube-proxy 1 261d kubernetes-dashboard 1 20h namespace-controller 1 261d node-controller 1 261d persistent-volume-binder 1 261d pod-garbage-collector 1 261d pv-protection-controller 1 261d pvc-protection-controller 1 261d replicaset-controller 1 261d replication-controller 1 261d resourcequota-controller 1 261d service-account-controller 1 261d service-controller 1 261d statefulset-controller 1 261d token-cleaner 1 261d ttl-controller 1 261d [root@k8s-master ~]# kubectl create clusterrolebinding dashboard-cluster-admin --clusterrole=cluster-admin --serviceaccount=kube-system:dashboard-admin clusterrolebinding.rbac.authorization.k8s.io/dashboard-cluster-admin created [root@k8s-master ~]# kubectl get secret -n kube-system NAME TYPE DATA AGE attachdetach-controller-token-59k84 kubernetes.io/service-account-token 3 261d clusterrole-aggregation-controller-token-tnqvr kubernetes.io/service-account-token 3 261d coredns-token-nstwr kubernetes.io/service-account-token 3 261d cronjob-controller-token-cqmsp kubernetes.io/service-account-token 3 261d daemon-set-controller-token-mlp6k kubernetes.io/service-account-token 3 261d dashboard-admin-token-lr9j6 kubernetes.io/service-account-token 3 4m default-token-czx5p kubernetes.io/service-account-token 3 261d deployment-controller-token-nr9lf kubernetes.io/service-account-token 3 261d job-controller-token-s9j82 kubernetes.io/service-account-token 3 261d kube-proxy-token-d58zg kubernetes.io/service-account-token 3 261d kubernetes-dashboard-certs Opaque 0 20h kubernetes-dashboard-key-holder Opaque 2 20h kubernetes-dashboard-token-zfb6z kubernetes.io/service-account-token 3 20h namespace-controller-token-fwkbc kubernetes.io/service-account-token 3 261d node-controller-token-nf2tk kubernetes.io/service-account-token 3 261d persistent-volume-binder-token-5xs9v token-cleaner-token-5xsxp kubernetes.io/service-account-token 3 261d ttl-controller-token-wv2gh kubernetes.io/service-account-token 3 261d [root@k8s-master ~]# kubectl describe secret dashboard-admin-token-lr9j6 Error from server (NotFound): secrets "dashboard-admin-token-lr9j6" not found [root@k8s-master ~]# kubectl describe secret dashboard-admin-token-lr9j6 -n kube-system Name: dashboard-admin-token-lr9j6 Namespace: kube-system Labels: <none> Annotations: kubernetes.io/service-account.name=dashboard-admin kubernetes.io/service-account.uid=da8cef11-95ab-11e9-9e10-000c2927f194 Type: kubernetes.io/service-account-token Data ==== namespace: 11 bytes token: eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJrdWJlLXN5c3RlbSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VjcmV0Lm5hbWUiOiJkYXNoYm9hcmQtYWRtaW4tdG9rZW4tbHI5ajYiLCJrdWJlcm5ldGVzLmlvL3NlcnZpY2VhY2NvdW50L3NlcnZpY2UtYWNjb3VudC5uYW1lIjoiZGFzaGJvYXJkLWFkbWluIiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9zZXJ2aWNlLWFjY291bnQudWlkIjoiZGE4Y2VmMTEtOTVhYi0xMWU5LTllMTAtMDAwYzI5MjdmMTk0Iiwic3ViIjoic3lzdGVtOnNlcnZpY2VhY2NvdW50Omt1YmUtc3lzdGVtOmRhc2hib2FyZC1hZG1pbiJ9.DRxgWYbKCHRbRnQ8ZmNMkFaE6gWaedmOtz9GQg_E0RSKPa2xaauMhtgZxr_Fv2dyWmMWo1a0-1rHn2eVkU8n0JgtwGB-ttqmZPMa-WFBgsaUihzltSCU3ghmJogg6yz5Tav2Els4HOlVL2c_q0K3WCrOFefl_M-to9n4dd61444es2nY7pWC8b1X6udFASTtYNBqGwVbc6MgctN4iwamtzRe0j-qhtoj4wEFU6SnLNH4Po7XMz_U7TgcBM_3VunJx6ZbE9nRTbL-VEijlN5Si-Qwx0f3G2YUxPE2HP_0ZVp7n8E5nQnePn3sUTJRm3DHTz4AxWuSOw2CV7lFiBjDbQ ca.crt: 1025 bytes #操作步骤说明 1.创建serviceaccount [root@k8s-master ~]# kubectl create serviceaccount dashboard-admin -n kube-system serviceaccount/dashboard-admin created [root@k8s-master ~]# kubectl get sa -n kube-system 2.把sa绑定到clusterRoleBinding [root@k8s-master ~]# kubectl create clusterrolebinding dashboard-cluster-admin --clusterrole=cluster-admin --serviceaccount=kube-system:dashboard-admin clusterrolebinding.rbac.authorization.k8s.io/dashboard-cluster-admin created 3.查看sa的token信息 [root@k8s-master ~]# kubectl get secret -n kube-system [root@k8s-master ~]# kubectl describe secret dashboard-admin-token-lr9j6 -n kube-system

标签:object cert 访问 ide day bfd 版本 pwc 相同
原文地址:https://www.cnblogs.com/yxh168/p/11072125.html