标签:persist utils 支持 dir ogg upload firewalld epo dock
一、环境介绍centos7.4 系统机器两台:
| 机器 | 主机名 |
|---|---|
| 10.1.31.36 | kubernetes master |
| 10.1.31.24 | kubernetes node1 |
以下步骤在两台台主机上都要操作。
需要pull docker镜像,请先安装docker。
[`https://github.com/kubernetes/kubernetes`]()从CentOS OS存储库中使用docker,则docker版本可能较旧,无法与Kubernetes v1.13.0及更高版本一起使用。
这里我们安装18.06.3版本
yum install -y -q yum-utils device-mapper-persistent-data lvm2 > /dev/null 2>&1
yum-config-manager --add-repo https://download.docker.com/linux/centos/docker-ce.repo > /dev/null 2>&1
yum install -y -q docker-ce-18.06.3.ce >/dev/null 2>&1启动docker
systemctl enable docker && systemctl start docker
docker version如果系统开启了防火墙则按如下步骤关闭防火墙
[root@localhost]# systemctl stop firewalld
[root@localhost]# systemctl disable firewalld[root@localhost]# setenforce 0
[root@localhost]# sed -i ‘/^SELINUX=/cSELINUX=disabled‘ /etc/sysconfig/selinux或者编辑/etc/selinux/config
root@localhost]# vi /etc/selinux/config
将SELINUX=enforcing改为SELINUX=disabled,重启后生效
查看状态
[root@localhost]# sestatus
SELinux status: disabledkubeadm不支持swap
执行
[root@localhost yum.repos.d]# swapoff -a
#或者编辑/etc/fstab注释掉swap
[root@localhost yum.repos.d]# cat /etc/fstab
# /etc/fstab
# Created by anaconda on Fri Oct 18 00:03:01 2019
#
# Accessible filesystems, by reference, are maintained under ‘/dev/disk‘
# See man pages fstab(5), findfs(8), mount(8) and/or blkid(8) for more info
#
UUID=1a73fb9d-095b-4302-aa87-4a49783c0133 / xfs defaults 0 0
UUID=e293a721-617e-4cdd-8cb9-d2e895427b03 /boot xfs defaults 0 0
#UUID=73e88a54-4574-4f0a-8a4f-d57d2bc2ee46 swap swap defaults 0 0三台主机分别设置master、node1
[root@localhost kubernetes]# cat >> /etc/sysconfig/network << EOF
hostname=master
EOF
[root@localhost kubernetes]# cat /etc/sysconfig/network
# Created by anaconda
hostname=master或者
[root@localhost]#hostnamectl set-hostname master
[root@localhost]#hostnamectl set-hostname node1
[root@localhost]#hostnamectl set-hostname node2每台主机上都执行
[root@localhost]#echo "192.168.3.100 master" >> /etc/hosts
[root@localhost]#echo "192.168.3.101 node1" >> /etc/hosts
[root@localhost]#echo "192.168.3.102 node2" >> /etc/hosts将桥接的IPv4流量传递到iptables的链
[root@localhost]#cat <<EOF > /etc/sysctl.d/k8s.conf
net.bridge.bridge-nf-call-ip6tables = 1
net.bridge.bridge-nf-call-iptables = 1
----net.bridge.bridge-nf-call-arptables = 1
net.ipv4.ip_forward = 1
EOF使如上配置生效
[root@localhost]#sysctl --system//配置国内tencent yum源地址、epel源地址、Kubernetes源地址
[root@localhost]#mkdir -p /etc/yum.repos.d/repos.bak
[root@localhost]#mv /etc/yum.repos.d/*.repo /etc/yum.repos.d/repos.bak
[root@localhost]#wget -O /etc/yum.repos.d/CentOS-Base.repo http://mirrors.cloud.tencent.com/repo/centos7_base.repo
[root@localhost]#wget -O /etc/yum.repos.d/epel.repo http://mirrors.cloud.tencent.com/repo/epel-7.repo
[root@localhost]#yum clean all && yum makecache
//配置国内Kubernetes源地址
[root@localhost]#cat <<EOF > /etc/yum.repos.d/kubernetes.repo
[kubernetes]
name=Kubernetes
baseurl=https://mirrors.aliyun.com/kubernetes/yum/repos/kubernetes-el7-x86_64
enabled=1
gpgcheck=1
repo_gpgcheck=1
gpgkey=https://mirrors.aliyun.com/kubernetes/yum/doc/yum-key.gpg https://mirrors.aliyun.com/kubernetes/yum/doc/rpm-package-key.gpg
EOF指定版本号
[root@localhost]#yum install -y kubelet-1.16.0 kubeadm-1.16.0 kubectl-1.16.0 --disableexcludes=kubernetes不指定版本号
install -y kubelet kubeadm kubectl --disableexcludes=kubernetes说明:–disableexcludes=kubernetes #禁用除kubernetes之外的仓库,可以不带这个参数
启动工具
[root@localhost]#systemctl enable kubelet
[root@localhost]#systemctl start kubelet其他命令
systemctl status kubelet
systemctl stop kubelet
systemctl restart kubelet##3# 11、初始化获取要下载的镜像列表
[root@master ~]# cd /home
[root@master home]# ls
apache-zookeeper-3.5.6-bin jdk1.8.0_231 kafka_2.12-2.3.1
[root@master home]# kubeadm config images list
W1115 18:05:31.432259 17146 version.go:101] could not fetch a Kubernetes version from the internet: unable to get URL "https://dl.k8s.io/release/stable-1.txt": Get https://dl.k8s.io/release/stable-1.txt: net/http: request canceled while waiting for connection (Client.Timeout exceeded while awaiting headers)
W1115 18:05:31.436956 17146 version.go:102] falling back to the local client version: v1.16.3
k8s.gcr.io/kube-apiserver:v1.16.3
k8s.gcr.io/kube-controller-manager:v1.16.3
k8s.gcr.io/kube-scheduler:v1.16.3
k8s.gcr.io/kube-proxy:v1.16.3
k8s.gcr.io/pause:3.1
k8s.gcr.io/etcd:3.3.15-0
k8s.gcr.io/coredns:1.6.2执行下面命令,会在当前目录生成kubeadm.conf文件
[root@master home]#kubeadm config print init-defaults > kubeadm.confkubeadm.conf这个配置文件默认会从google的镜像仓库地址k8s.gcr.io下载镜像,国内下载不了。因此,我们通过下面的方法把地址改成国内的,比如用阿里的。
编辑kubeadm.conf文件,把imageRepository的value改成下面的
imageRepository: registry.aliyuncs.com/google_containers
kubeadm.conf文件里的kubeadm和k8s版本必须匹配,不能一高一低,如果不匹配,修改kubeadm.conf下面k8s的版本号即可
[root@master home]#vi kubeadm.conf在kubeadm.conf所在目录执行
[[root@master home]#kubeadm config images pull --config kubeadm.conf
[root@master home]# docker images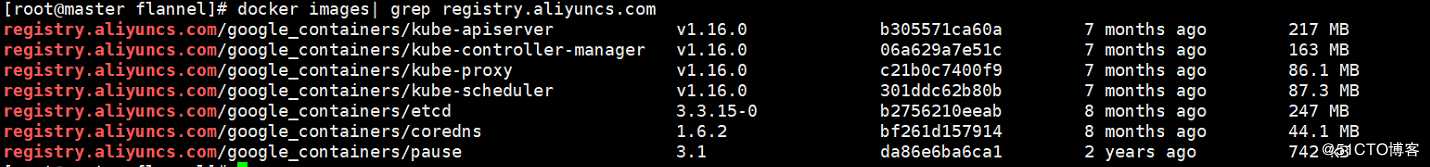
镜像下载好后,还需要tag下载好的镜像,让下载好的镜像都是带有 k8s.gcr.io 标识的,如果不打tag变成k8s.gcr.io,那么后面用kubeadm安装会出现问题,因为kubeadm里面只认 google自身的模式。打tag后删除带有 registry.aliyuncs.com 标识的镜像。
重新打tag
docker tag registry.aliyuncs.com/google_containers/kube-apiserver:v1.16.0 k8s.gcr.io/kube-apiserver:v1.16.0
docker tag registry.aliyuncs.com/google_containers/kube-proxy:v1.16.0 k8s.gcr.io/kube-proxy:v1.16.0
docker tag registry.aliyuncs.com/google_containers/kube-controller-manager:v1.16.0 k8s.gcr.io/kube-controller-manager:v1.16.0
docker tag registry.aliyuncs.com/google_containers/kube-scheduler:v1.16.0 k8s.gcr.io/kube-scheduler:v1.16.0
docker tag registry.aliyuncs.com/google_containers/etcd:3.3.15-0 k8s.gcr.io/etcd:3.3.15-0
docker tag registry.aliyuncs.com/google_containers/coredns:1.6.2 k8s.gcr.io/coredns:1.6.2
docker tag registry.aliyuncs.com/google_containers/pause:3.1 k8s.gcr.io/pause:3.1执行
[root@master ~]# kubeadm init --kubernetes-version=v1.16.0 --pod-network-cidr= 10.244.0.0/16 --apiserver-advertise-address=192.168.3.100执行成功结果
[init] Using Kubernetes version: v1.16.0
[preflight] Running pre-flight checks
[preflight] Pulling images required for setting up a Kubernetes cluster
[preflight] This might take a minute or two, depending on the speed of your internet connection
[preflight] You can also perform this action in beforehand using ‘kubeadm config images pull‘
[kubelet-start] Writing kubelet environment file with flags to file "/var/lib/kubelet/kubeadm-flags.env"
[kubelet-start] Writing kubelet configuration to file "/var/lib/kubelet/config.yaml"
[kubelet-start] Activating the kubelet service
[certs] Using certificateDir folder "/etc/kubernetes/pki"
[certs] Generating "ca" certificate and key
[certs] Generating "apiserver" certificate and key
[certs] apiserver serving cert is signed for DNS names [master kubernetes kubernetes.default kubernetes.default.svc kubernetes.default.svc.cluster.local] and IPs [10.96.0.1 192.168.3.100]
[certs] Generating "apiserver-kubelet-client" certificate and key
[certs] Generating "front-proxy-ca" certificate and key
[certs] Generating "front-proxy-client" certificate and key
[certs] Generating "etcd/ca" certificate and key
[certs] Generating "etcd/server" certificate and key
[certs] etcd/server serving cert is signed for DNS names [master localhost] and IPs [192.168.3.100 127.0.0.1 ::1]
[certs] Generating "etcd/peer" certificate and key
[certs] etcd/peer serving cert is signed for DNS names [master localhost] and IPs [192.168.3.100 127.0.0.1 ::1]
[certs] Generating "etcd/healthcheck-client" certificate and key
[certs] Generating "apiserver-etcd-client" certificate and key
[certs] Generating "sa" key and public key
[kubeconfig] Using kubeconfig folder "/etc/kubernetes"
[kubeconfig] Writing "admin.conf" kubeconfig file
[kubeconfig] Writing "kubelet.conf" kubeconfig file
[kubeconfig] Writing "controller-manager.conf" kubeconfig file
[kubeconfig] Writing "scheduler.conf" kubeconfig file
[control-plane] Using manifest folder "/etc/kubernetes/manifests"
[control-plane] Creating static Pod manifest for "kube-apiserver"
[control-plane] Creating static Pod manifest for "kube-controller-manager"
[control-plane] Creating static Pod manifest for "kube-scheduler"
[etcd] Creating static Pod manifest for local etcd in "/etc/kubernetes/manifests"
[wait-control-plane] Waiting for the kubelet to boot up the control plane as static Pods from directory "/etc/kubernetes/manifests". This can take up to 4m0s
[kubelet-check] Initial timeout of 40s passed.
[apiclient] All control plane components are healthy after 209.010947 seconds
[upload-config] Storing the configuration used in ConfigMap "kubeadm-config" in the "kube-system" Namespace
[kubelet] Creating a ConfigMap "kubelet-config-1.16" in namespace kube-system with the configuration for the kubelets in the cluster
[upload-certs] Skipping phase. Please see --upload-certs
[mark-control-plane] Marking the node master as control-plane by adding the label "node-role.kubernetes.io/master=‘‘"
[mark-control-plane] Marking the node master as control-plane by adding the taints [node-role.kubernetes.io/master:NoSchedule]
[bootstrap-token] Using token: vmuuvn.q7q14t5135zm9xk0
[bootstrap-token] Configuring bootstrap tokens, cluster-info ConfigMap, RBAC Roles
[bootstrap-token] configured RBAC rules to allow Node Bootstrap tokens to post CSRs in order for nodes to get long term certificate credentials
[bootstrap-token] configured RBAC rules to allow the csrapprover controller automatically approve CSRs from a Node Bootstrap Token
[bootstrap-token] configured RBAC rules to allow certificate rotation for all node client certificates in the cluster
[bootstrap-token] Creating the "cluster-info" ConfigMap in the "kube-public" namespace
[addons] Applied essential addon: CoreDNS
[addons] Applied essential addon: kube-proxy
Your Kubernetes control-plane has initialized successfully!
To start using your cluster, you need to run the following as a regular user:
mkdir -p $HOME/.kube
sudo cp -i /etc/kubernetes/admin.conf $HOME/.kube/config
sudo chown $(id -u):$(id -g) $HOME/.kube/config
You should now deploy a pod network to the cluster.
Run "kubectl apply -f [podnetwork].yaml" with one of the options listed at:
https://kubernetes.io/docs/concepts/cluster-administration/addons/
Then you can join any number of worker nodes by running the following on each as root:
kubeadm join 192.168.3.100:6443 --token vmuuvn.q7q14t5135zm9xk0 --discovery-token-ca-cert-hash sha256:c302e2c93d2fe86be7f817534828224469a19c5ccbbf9b246f3695127c3ea611记录最后的输出,node节点加入需要用到
kubeadm join 192.168.3.100:6443 --token vmuuvn.q7q14t5135zm9xk0
–discovery-token-ca-cert-hash sha256:c302e2c93d2fe86be7f817534828224469a19c5ccbbf9b246f3695127c3ea611如果init失败,重启kubeadm再执行init
[root@master ~]# kubeadm reset
初始化成功后会在/etc/kubernetes/成下面的文件,如果没有需要重新init[root@master home]# ll /etc/kubernetes/
total 36
-rw------- 1 root root 5453 Nov 15 17:42 admin.conf
-rw------- 1 root root 5485 Nov 15 17:42 controller-manager.conf
-rw------- 1 root root 5457 Nov 15 17:42 kubelet.conf
drwxr-xr-x. 2 root root 113 Nov 15 17:42 manifests
drwxr-xr-x 3 root root 4096 Nov 15 17:42 pki
-rw------- 1 root root 5437 Nov 15 17:42 scheduler.conf注意:kubeadm reset是清理环境,执行后,master要重新init。如果node已经加入集群,那么node也要reset重启kubelet并要重新join
[root@node1 home]#kubeadm reset
[root@node1 home]#systemctl daemon-reload && systemctl restart kubelet
[root@node1 home]# kubeadm join 192.168.3.100:6443 --token vmuuvn.q7q14t5135zm9xk0 --discovery-token-ca-cert-hash sha256:c302e2c93d2fe86be7f817534828224469a19c5ccbbf9b246f3695127c3ea611当前用户,执行以下步骤(系统由admin.conf文件启动kubernetes,如果不配置会起不来)
root@master home]# mkdir -p $HOME/.kube
[root@master home]# cp -i /etc/kubernetes/admin.conf $HOME/.kube/config
[root@master home]# chown $(id -u):$(id -g) $HOME/.kube/configk8s 支持很多种网络方案,在这里使用的是经典的 flannel 方案,还有Calico方式。
查看flannel版本
https://github.com/coreos/flannel
执行命令开始安装。注:下面这个地址是v0.11.0-amd6版本的
[root@master home]#kubectl apply -f https://raw.githubusercontent.com/coreos/flannel/62e44c867a2846fefb68bd5f178daf4da3095ccb/Documentation/kube-flannel.yml
安装结果
clusterrole.rbac.authorization.k8s.io/flannel created
clusterrolebinding.rbac.authorization.k8s.io/flannel created
serviceaccount/flannel created
configmap/kube-flannel-cfg created
unable to recognize "https://raw.githubusercontent.com/coreos/flannel/62e44c867a2846fefb68bd5f178daf4da3095ccb/Documentation/kube-flannel.yml": no matches for kind "PodSecurityPolicy" in version "extensions/v1beta1"
unable to recognize "https://raw.githubusercontent.com/coreos/flannel/62e44c867a2846fefb68bd5f178daf4da3095ccb/Documentation/kube-flannel.yml": no matches for kind "DaemonSet" in version "extensions/v1beta1"
unable to recognize "https://raw.githubusercontent.com/coreos/flannel/62e44c867a2846fefb68bd5f178daf4da3095ccb/Documentation/kube-flannel.yml": no matches for kind "DaemonSet" in version "extensions/v1beta1"
unable to recognize "https://raw.githubusercontent.com/coreos/flannel/62e44c867a2846fefb68bd5f178daf4da3095ccb/Documentation/kube-flannel.yml": no matches for kind "DaemonSet" in version "extensions/v1beta1"
unable to recognize "https://raw.githubusercontent.com/coreos/flannel/62e44c867a2846fefb68bd5f178daf4da3095ccb/Documentation/kube-flannel.yml": no matches for kind "DaemonSet" in version "extensions/v1beta1"
unable to recognize "https://raw.githubusercontent.com/coreos/flannel/62e44c867a2846fefb68bd5f178daf4da3095ccb/Documentation/kube-flannel.yml": no matches for kind "DaemonSet" in version "extensions/v1beta1"如果一直pull不下来,默认的flannel配置文件拉取镜像在国外,国内拉取失败,很多网上文章没注意这一步,导致flannel部署失败,如下解决
访问:https://blog.51cto.com/14040759/2492764
[root@master home]# mkdir flannel
#把内容粘贴到下面的文本后保存
[root@master home]# vim kube-flannel.yml
[root@master home]# kubectl apply -f flannel/kube-flannel.yml
[root@master home]#执行获取pods列表命令,查看相关状态
[root@master home]# kubectl get pods --all-namespaces
NAMESPACE NAME READY STATUS RESTARTS AGE
kube-system coredns-5644d7b6d9-5zsbb 0/1 Pending 0 6h17m
kube-system coredns-5644d7b6d9-pvsm9 0/1 Pending 1 6h17m
kube-system etcd-master 1/1 Running 0 6h16m
kube-system kube-apiserver-master 1/1 Running 0 6h16m
kube-system kube-controller-manager-master 1/1 Running 0 6h16m
kube-system kube-flannel-ds-amd64-7x9fv 1/1 Running 0 6h16m
kube-system kube-flannel-ds-amd64-n6kpw 1/1 Running 0 6h14m
kube-system kube-proxy-8zl82 1/1 Running 0 6h14m
kube-system kube-proxy-gqmxx 1/1 Running 0 6h17m
kube-system kube-scheduler-master 1/1 Running 0 6h16m查看主节点情况
[root@master ~]# kubectl get nodes
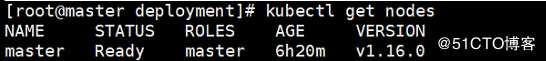
使用kubeadm初始化的集群,出于安全考虑Pod不会被调度到Master Node上,也就是说Master Node不参与工作负载,这样Master的资源就浪费了。在Master节点上,可以运行以下命令使其作为一个工作节点
[root@master ~]#kubectl taint nodes --all node-role.kubernetes.io/master-禁止master部署pod
[root@master ~]#kubectl taint nodes k8s node-role.kubernetes.io/master=true:NoSchedule关于污点,网上资料参考:
使用kubeadm搭建的集群默认就给 master 节点添加了一个污点标记,所以我们看到我们平时的 pod 都没有被调度到 master 上去。
[root@master ~]#kubectl describe node master | grep Taints(注:master node name)有一条关于 Taints 的信息:node-role.kubernetes.io/master:NoSchedule,就表示给 master 节点打了一个污点的标记,其中影响的参数是NoSchedule,表示 pod 不会被调度到标记为 taints 的节点,除了 NoSchedule 外,还有另外两个选项:
PreferNoSchedule:NoSchedule 的软策略版本,表示尽量不调度到污点节点上去
NoExecute:该选项意味着一旦 Taint 生效,如该节点内正在运行的 pod 没有对应 Tolerate 设置,会直接被逐出
jion集群
[root@node1 ~]# kubeadm join 10.1.31.36:6443 --token vmuuvn.q7q14t5135zm9xk0 --discovery-token-ca-cert-hash sha256:c302e2c93d2fe86be7f817534828224469a19c5ccbbf9b246f3695127c3ea611
如果在master初始化的时候没有记下jion命令,在master上使用kubeadm token create --print-join-command查询
$ kubectl delete node --all
$ for service in kube-apiserver kube-controller-manager kubectl kubelet kube-proxy kube-scheduler; do
systemctl stop $service
done
$ yum -y remove kubernetes #if it‘s registered as a serviceyum remove -y kubelet kubectl
rm -rf ~/.kube/
rm -rf /etc/kubernetes/
rm -rf /etc/systemd/system/kubelet.service.d
rm -rf /etc/systemd/system/kubelet.service
rm -rf /usr/bin/kube*
rm -rf /etc/cni
rm -rf /opt/cni
rm -rf /var/lib/etcd
rm -rf /var/etcd
rm -rf /var/lib/cni/flannel/* && rm -rf /var/lib/cni/networks/cbr0/* && ip link delete cni0
rm -rf /var/lib/cni/networks/cni0/*docker rm -f $(docker ps -qa)
#删除所有的数据卷
docker volume rm $(docker volume ls -q)
#再次显示所有的容器和数据卷,确保没有残留
docker ps -a
docker volume ls[root@master ~]# kubectl get nodes -o wide
https://blog.51cto.com/blogger/success/2492786
标签:persist utils 支持 dir ogg upload firewalld epo dock
原文地址:https://blog.51cto.com/14040759/2492789