标签:des android c style class blog
The goal of this section is to introduce, discuss, and provide language specific mitigation techniques for HttpOnly.
According to a daily blog article by Jordan Wiens, “No cookie for you!,” HttpOnly cookies were first implemented in 2002 by Microsoft Internet Explorer developers for Internet Explorer 6 SP1. Wiens, [1]
According to the Microsoft Developer Network, HttpOnly is an additional flag included in a Set-Cookie HTTP response header. Using the HttpOnly flag when generating a cookie helps mitigate the risk of client side script accessing the protected cookie (if the browser supports it).
Set-Cookie: <name>=<value>[; <Max-Age>=<age>] [; expires=<date>][; domain=<domain_name>] [; path=<some_path>][; secure][; HttpOnly]
If the HttpOnly flag (optional) is included in the HTTP response header, the cookie cannot be accessed through client side script (again if the browser supports this flag). As a result, even if a cross-site scripting (XSS) flaw exists, and a user accidentally accesses a link that exploits this flaw, the browser (primarily Internet Explorer) will not reveal the cookie to a third party.
If a browser does not support HttpOnly and a website attempts to set an HttpOnly cookie, the HttpOnly flag will be ignored by the browser, thus creating a traditional, script accessible cookie. As a result, the cookie (typically your session cookie) becomes vulnerable to theft of modification by malicious script. Mitigating, [2]
According to Michael Howard, Senior Security Program Manager in the Secure Windows Initiative group at Microsoft, the majority of XSS attacks target theft of session cookies. A server could help mitigate this issue by setting the HTTPOnly flag on a cookie it creates, indicating the cookie should not be accessible on the client.
If a browser that supports HttpOnly detects a cookie containing the HttpOnly flag, and client side script code attempts to read the cookie, the browser returns an empty string as the result. This causes the attack to fail by preventing the malicious (usually XSS) code from sending the data to an attacker‘s website. Howard, [3]
Since Sun Java Enterprise Edition 6 (JEE 6), that adopted Java Servlet 3.0 technology, it‘s programmatically easy setting HttpOnly flag in a cookie.
In fact setHttpOnly and isHttpOnly
methods are available in the Cookie interface [4], and also for session cookies (JSESSIONID) [5]:
Cookie cookie = getMyCookie("myCookieName");
cookie.setHttpOnly(true);
Moreover since JEE 6 it‘s also declaratively easy setting
HttpOnly flag in session cookie, by applying the
following configuration in the deployment descriptor
WEB-INF/web.xml:
<session-config> <cookie-config> <http-only>true</http-only> </cookie-config> </session-config>
For Java Enterprise Edition versions prior to JEE 6 a
common workaround is to overwrite the
SET-COOKIE http response header with a session cookie
value that explicitly appends the HttpOnly flag:
String sessionid = request.getSession().getId();
// be careful overwriting: JSESSIONID may have been set with other flags
response.setHeader("SET-COOKIE", "JSESSIONID=" + sessionid + "; HttpOnly");
In this context overwriting, despite appropriate for the
HttpOnly flag, is discouraged because JSESSIONID may
have been set with other flags. So a better workaround is taking
care of the previously set flags or using the ESAPI#Java_EE
library: in fact the addCookie method of the
SecurityWrapperResponse [6] takes care of previously set falgs for us. So
we could write a servlet filter as the following one:
public void doFilter(ServletRequest request, ServletResponse response, FilterChain filterChain) throws IOException, ServletException {
HttpServletRequest httpServletRequest = (HttpServletRequest) request;
HttpServletResponse httpServletResponse = (HttpServletResponse) response;
// if errors exist then create a sanitized cookie header and continue
SecurityWrapperResponse securityWrapperResponse = new SecurityWrapperResponse(httpServletResponse, "sanitize");
Cookie[] cookies = httpServletRequest.getCookies();
if (cookies != null) {
for (int i = 0; i < cookies.length; i++) {
Cookie cookie = cookies[i];
if (cookie != null) {
// ESAPI.securityConfiguration().getHttpSessionIdName() returns JSESSIONID by default configuration
if (ESAPI.securityConfiguration().getHttpSessionIdName().equals(cookie.getName())) {
securityWrapperResponse.addCookie(cookie);
}
}
}
}
filterChain.doFilter(request, response);
}
Some web application servers, that implements JEE 5, and servlet container that implements Java Servlet 2.5 (part of the JEE 5), also allow creating HttpOnly session cookies:
context.xml set the
context tag‘s attribute useHttpOnly [7] as follow:<?xml version="1.0" encoding="UTF-8"?> <Context path="/myWebApplicationPath" useHttpOnly="true">
\server\<myJBossServerInstance>\deploy\jbossweb.sar\context.xml
set the SessionCookie tag [8]
as follow:<Context cookies="true" crossContext="true"> <SessionCookie secure="true" httpOnly="true" />
In .NET 2.0, HttpOnly can also be set via the HttpCookie
object for all custom application cookies
<httpCookies httpOnlyCookies="true" …>
C# Code:
HttpCookie myCookie = new HttpCookie("myCookie");
myCookie.HttpOnly = true;
Response.AppendCookie(myCookie);
VB.NET Code:
Dim myCookie As HttpCookie = new HttpCookie("myCookie")
myCookie.HttpOnly = True
Response.AppendCookie(myCookie)
Response.Cookies[cookie].Path += ";HttpOnly";
Python Code (cherryPy):
To use HTTP-Only cookies with Cherrypy
sessions just add the following line in your configuration file:
tools.sessions.httponly = True
If you use SLL you can also make your cookies secure (encrypted)
to avoid "man in the middle" cookies reading with:
tools.sessions.secure = True
PHP supports setting the HttpOnly flag since version 5.2.0 (November 2006).
For session cookies managed by PHP, the flag is set either permanently in php.iniPHP manual on HttpOnly through the parameter:
session.cookie_httponly = True
or in and during a script via the function[9]:
void session_set_cookie_params ( int $lifetime [, string $path [, string $domain
[, bool $secure= false [, bool $httponly= false ]]]] )
For application cookies last parameter in setcookie() sets HttpOnly flag[10]:
bool setcookie ( string $name [, string $value [, int $expire= 0 [, string $path
[, string $domain [, bool $secure= false [, bool $httponly= false ]]]]]] )
If code changes are infeasible, web application firewalls can be used to add HttpOnly to session cookies:
Using WebGoat‘s HttpOnly lesson, the following web browsers have been tested for HttpOnly support. If the browsers enforces HttpOnly, a client side script will be unable to read or write the session cookie. However, there is currently no prevention of reading or writing the session cookie via a XMLHTTPRequest.
Note: These results may be out of date as this page is not well maintained. A great site that is focused on keeping up with the status of browsers is at: http://www.browserscope.org/. For the most recent security status of various browsers, including many details beyond just HttpOnly, go to the browserscope site, and then click on the Security Tab on the table at the bottom of the page. The Browserscope site does not provide as much detail on HttpOnly as this page, but provides lots of other details this page does not.
Our results as of Feb 2009 are listed below in table 1.
| Browser | Version | Prevents Reads | Prevents Writes | Prevents Read within XMLHTTPResponse* |
|---|---|---|---|---|
| Microsoft Internet Explorer | 8 Beta 2 | Yes | Yes | Partially (set-cookie is protected, but not set-cookie2, see [14]). Fully patched IE8 passes http://ha.ckers.org/httponly.cgi |
| Microsoft Internet Explorer | 7 | Yes | Yes | Partially (set-cookie is protected, but not set-cookie2, see [15]). Fully patched IE7 passes http://ha.ckers.org/httponly.cgi |
| Microsoft Internet Explorer | 6 (SP1) | Yes | No | No (Possible that ms08-069 fixed IE 6 too, please verify with http://ha.ckers.org/httponly.cgi and update this page!) |
| Microsoft Internet Explorer | 6 (fully patched) | Yes | Unknown | Yes |
| Mozilla Firefox | 3.0.0.6+ | Yes | Yes | Yes (see [16]) |
| Netscape Navigator | 9.0b3 | Yes | Yes | No |
| Opera | 9.23 | No | No | No |
| Opera | 9.50 | Yes | No | No |
| Opera | 11 | Yes | Unknown | Yes |
| Safari | 3.0 | No | No | No (almost yes, see [17]) |
| Safari | 5 | Yes | Yes | Yes |
| iPhone (Safari) | iOS 4 | Yes | Yes | Yes |
| Google‘s Chrome | Beta (initial public release) | Yes | No | No (almost yes, see [18]) |
| Google‘s Chrome | 12 | Yes | Yes | Yes |
| Android | Android 2.3 | Unknown | Unknown | No |
* An attacker could still read the session cookie in a response to an XmlHttpRequest.
As of 2011, 99% of browsers and most web application frameworks do support httpOnly<ref>Misunderstandings on HttpOnly Cookie</ref>.
The goal of this section is to provide a step-by-step example of testing your browser for HttpOnly support.
The OWASP WEBGOAT HttpOnly lab is broken and does not show IE 8 Beta 2 with ms08-069 as complete in terms of HttpOnly XMLHTTPRequest header leakage protection. This error is being tracked via http://code.google.com/p/webgoat/issues/detail?id=18.
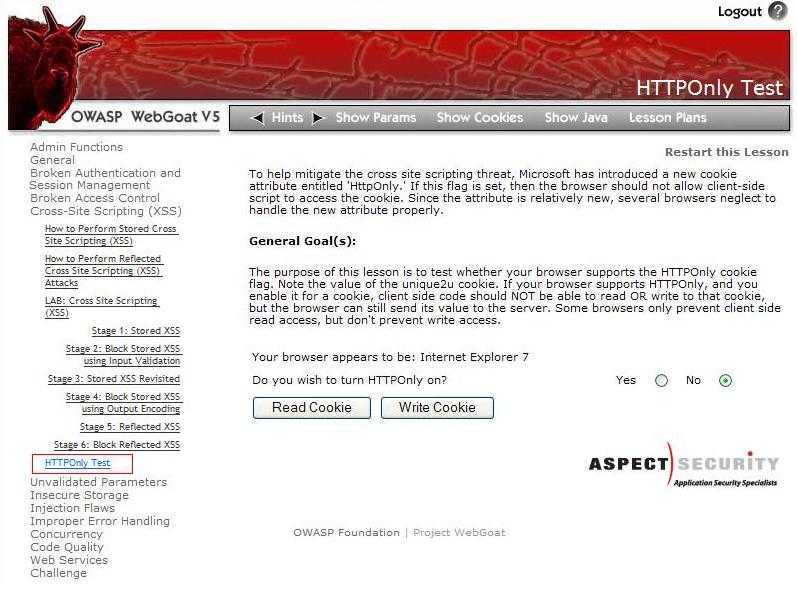
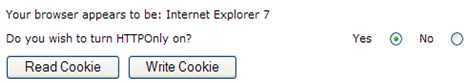
Assuming you have installed and launched WebGoat, begin by navigating to the ‘HttpOnly Test’ lesson located within the Cross-Site Scripting (XSS) category. After loading the ‘HttpOnly Test’ lesson, as shown in figure 1, you are now able to begin testing web browsers supporting HTTPOnly.
If the HttpOnly flag is set, then your browser should not allow a client-side script to access the session cookie. Unfortunately, since the attribute is relatively new, several browsers may neglect to handle the new attribute properly.
The purpose of this lesson is to test whether your browser supports the HttpOnly cookie flag. Note the value of the unique2u cookie. If your browser supports HTTPOnly, and you enable it for a cookie, a client-side script should NOT be able to read OR write to that cookie, but the browser can still send its value to the server. However, some browsers only prevent client side read access, but do not prevent write access.
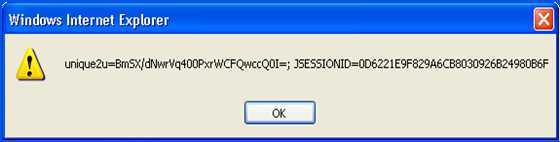
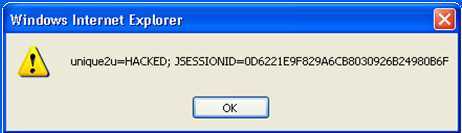
The following test was performed on two browsers, Internet Explorer 7 and Opera 9.22, to demonstrate the results when the HttpOnly flag is enforced properly. As you will see, IE7 properly enforces the HttpOnly flag, whereas Opera does not properly enforce the HttpOnly flag.
1) Select the option to turn HttpOnly off as shown below in figure 2.
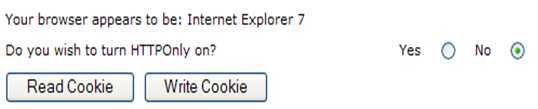
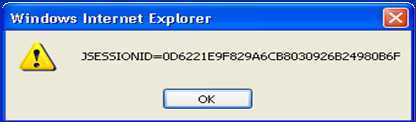
2) After turning HttpOnly off, select the “Read Cookie” button.
3) With HttpOnly remaining disabled, select the “Write Cookie” button.
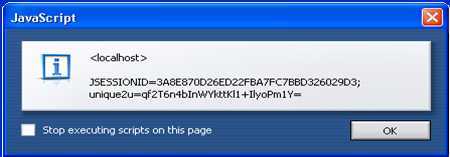
4) Select the radio button to enable HttpOnly as shown below in figure 5.
5) After enabling HttpOnly, select the "Read Cookie" button.
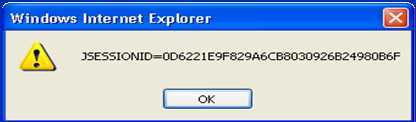
6) Select the "Write Cookie" button.

[1] Wiens, Jordan. No cookie for you!"
[2] Mitigating Cross-site Scripting with HTTP-Only Cookies
[3] Howard, Michael. Some Bad News and Some Good News
[4] MSDN. Setting the HttpOnly propery in .NET
[5] XSS: Gaining access to HttpOnly Cookie in 2012
标签:des android c style class blog
原文地址:http://www.cnblogs.com/milantgh/p/3766587.html