一.测试拓扑: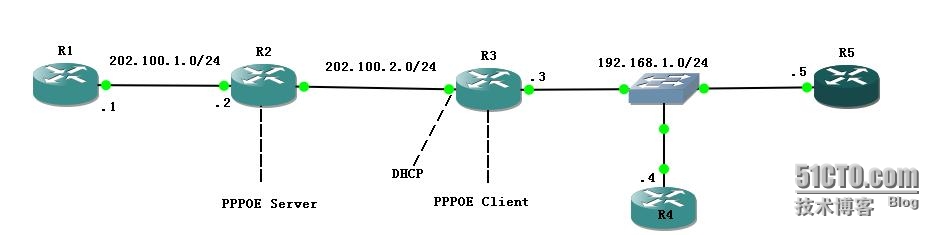
二.测试思路:
A.通过不设置方向的ip nat enable解决
---这种方式可以直接用公网IP地址访问,也可以用域名方式访问
---不幸的是思科不同的IOS,有的虽然有ip nat enable,但是实现不了同样的功能
---在有的版本中接口下干脆就不能输入ip nat enable
B.通过设置DNS域名为内网实际地址解决
---这种方式只适用于使用域名访问的方式
---如果是ASA防火墙可以通过NAT添加DNS参数,让修改DNS回包为内网地址解决
---如果客户端DNS为内部服务器,可以直接修改内部服务器DNS记录
---如果没有内部DNS服务器,可以让路由器同时作为DNS代理服务器,同时在它上面配置记录,将域名指向内部服务器的实际地址
三.基本配置:
A.R1:
interface Ethernet0/0
ip address 202.100.1.1 255.255.255.0
no shutdown
ip route 0.0.0.0 0.0.0.0 202.100.1.2
B.R2:
1.接口配置:
interface Ethernet0/0
ip address 202.100.1.2 255.255.255.0
no shutdown
interface Ethernet0/1
no ip address
no shutdown
2.DNS 服务器:
ip dns server
ip host R4.yuntian.cn 202.100.2.4
ip host R1.yuntian.cn 202.100.1.1
2.PPPOE Server配置:
aaa new-model
aaa authentication ppp default local
username cisco password 0 cisco
ip dhcp excluded-address 202.100.2.2
ip dhcp pool ppoe
network 202.100.2.0 255.255.255.0
default-router 202.100.2.2
bba-group pppoe TEST
virtual-template 1
interface Virtual-Template1
ip address 202.100.2.2 255.255.255.0
peer default ip address dhcp-pool ppoe
ppp authentication chap callin
ppp ipcp dns 202.100.2.2
interface Ethernet0/1
pppoe enable group TEST
C.R3:
1.接口配置:
interface Ethernet0/0
no ip address
no shutdown
interface Ethernet0/1
ip address 192.168.1.3 255.255.255.0
no shutdown
2.PPPOE Client配置:
interface e0/0
pppoe enable group global
pppoe-client dial-pool-number 1
interface Dialer0
mtu 1492
ip address negotiated
encapsulation ppp
dialer pool 1
ppp chap hostname cisco
ppp chap password 0 cisco
2.DHCP服务器:
ip dhcp excluded-address 192.168.1.3
ip dhcp excluded-address 192.168.1.4
ip dhcp pool client
network 192.168.1.0 255.255.255.0
dns-server 202.100.2.2
D.R4:
interface Ethernet0/0
ip address 192.168.1.4 255.255.255.0
no shutdown
ip route 0.0.0.0 0.0.0.0 192.168.1.3
E.R5:
interface Ethernet0/0
ip address DHCP
no shutdown
---接口IP,默认网关,DNS都由DHCP分配
四.解决地址回流
---都是在R3上面配置
A.方法一:NVI
1.动态PAT配置:
ip access-list extended PAT
permit ip 192.168.1.0 0.0.0.255 any
ip nat source list PAT interface Dialer0 overload
interface Ethernet0/1
ip nat enable
interface Dialer0
ip nat enable
2.静态NAT配置:
ip nat source static 192.168.1.4 202.100.2.4 extendable
3.测试:
---R5能通过R4映射后的公网地址访问R4
R5#telnet 202.100.2.4
Trying 202.100.2.4 ... Open
User Access Verification
Password:
R4>show users
Line User Host(s) Idle Location
0 con 0 UNKNOWN 00:00:16
*130 vty 0 idle 00:00:00 202.100.2.3
Interface User Mode Idle Peer Address
R4>
---R4也能通过R4映射后的公网地址访问R4
R4#telnet 202.100.2.4
Trying 202.100.2.4 ... Open
User Access Verification
Password:
R4>show users
Line User Host(s) Idle Location
0 con 0 202.100.2.4 00:00:00
*131 vty 1 idle 00:00:00 202.100.2.4
Interface User Mode Idle Peer Address
R4>
---通过域名访问时会自动修改DNS记录回包(类似ASA的dns rewrite)
R2(config)#ip dns server
R2(config)#ip host R4.yuntian.cn 202.100.2.4
R5(config)#ip domain-lookup
R5(config)#ip name-server 202.100.2.2
R5#ping R4.yuntian.cn
Translating "R4.yuntian.cn"...domain server (202.100.2.2) [OK]
Translating "R4.yuntian.cn"...domain server (202.100.2.2) [OK]
Translating "R4.yuntian.cn"...domain server (202.100.2.2) [OK]
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.1.4, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 8/32/52 ms
R5#
*Mar 1 02:13:40.991: ICMP: echo reply rcvd, src 192.168.1.4, dst 192.168.1.5
*Mar 1 02:13:41.047: ICMP: echo reply rcvd, src 192.168.1.4, dst 192.168.1.5
*Mar 1 02:13:41.087: ICMP: echo reply rcvd, src 192.168.1.4, dst 192.168.1.5
*Mar 1 02:13:41.095: ICMP: echo reply rcvd, src 192.168.1.4, dst 192.168.1.5
*Mar 1 02:13:41.139: ICMP: echo reply rcvd, src 192.168.1.4, dst 192.168.1.5
R5#
通过不同位置的抓包可以看出,路由器R3修改了DNS的回包,把公网地址修改为内网地址:
--在R2连接R3的接口抓包,可以看到DNS回复的是公网地址
--但是在R3内网接口抓包,可以看到公网地址已经被修改为内网地址
B.方法二:手工修改DNS记录
A.配置R3为DNS代理,并指定客户端DNS为自己
R3(config)#ip dns server
R3(config)#ip name-server 202.100.2.2
R3(config)#ip host R4.yuntian.cn 192.168.1.4
R3(config)#ip dhcp pool client
R3(dhcp-config)#dns-server 192.168.1.3
B.测试:
---R5关闭接口重新获取地址,再ping R4.yuntian.cn
R5#ping R4.yuntian.cn
Translating "R4.yuntian.cn"...domain server (192.168.1.3) [OK]
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.1.4, timeout is 2 seconds:
.!!!!
Success rate is 80 percent (4/5), round-trip min/avg/max = 8/30/44 ms
R5#
*Mar 1 03:40:58.335: ICMP: echo reply rcvd, src 192.168.1.4, dst 192.168.1.6
*Mar 1 03:40:58.383: ICMP: echo reply rcvd, src 192.168.1.4, dst 192.168.1.6
*Mar 1 03:40:58.395: ICMP: echo reply rcvd, src 192.168.1.4, dst 192.168.1.6
*Mar 1 03:40:58.423: ICMP: echo reply rcvd, src 192.168.1.4, dst 192.168.1.6
R5#
这时在R3内网接口上面抓包,可以看到DNS的回包:
这时因为路由器上面有该条记录,所以直接回复客户端,在外部dns抓包看不到DNS请求包
但是这时如果请求其他域名,外部DNS为有回包
R5#ping R1.yuntian.cn
Translating "R1.yuntian.cn"...domain server (192.168.1.3) [OK]
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 202.100.1.1, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 52/84/152 ms
R5#
*Mar 1 03:46:26.579: ICMP: echo reply rcvd, src 202.100.1.1, dst 192.168.1.6
*Mar 1 03:46:26.647: ICMP: echo reply rcvd, src 202.100.1.1, dst 192.168.1.6
*Mar 1 03:46:26.731: ICMP: echo reply rcvd, src 202.100.1.1, dst 192.168.1.6
*Mar 1 03:46:26.795: ICMP: echo reply rcvd, src 202.100.1.1, dst 192.168.1.6
*Mar 1 03:46:26.851: ICMP: echo reply rcvd, src 202.100.1.1, dst 192.168.1.6
R5#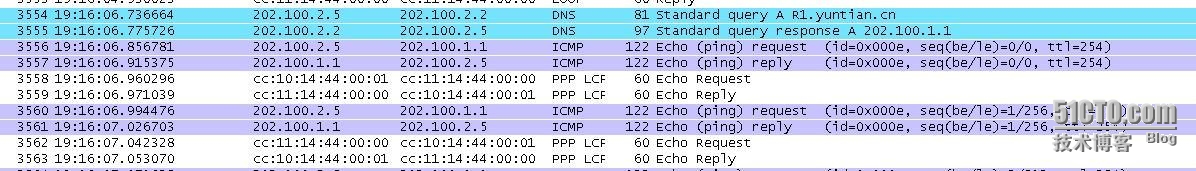
本文出自 “httpyuntianjxxll.spac..” 博客,请务必保留此出处http://333234.blog.51cto.com/323234/1664196
思科路由器PPOE client+NAT解决地址回流问题测试
原文地址:http://333234.blog.51cto.com/323234/1664196